QUICKLOOK: FSB and GRU Cyber Operations in the Russian-Ukrainian Conflict
PDF debrief: Unraveling the Digital Frontlines: Espionage, Disruption, and Warfare Tactics
Digital Shadows: The Role of FSB and GRU in Cyber Operations Amidst the Russian-Ukrainian Conflict”:
The FSB and GRU are not just remnants of the once-feared KGB but have evolved into dynamic entities adept at navigating the digital age. Their cyber strategies highlight Russia's intent to merge traditional espionage with the capabilities of modern technology.
The FSB, historically involved in counterintelligence and internal security, has been flexing its muscles in the cyber domain. One notable method involves deploying Advanced Persistent Threats (APTs) that can lurk silently within the systems, gathering information over long periods. Their sophisticated malware campaigns, sometimes in conjunction with criminal hacker groups, offer a dual advantage – not only do they collect data but also potentially compromise infrastructure.
GRU, on the other hand, leans more toward aggressive cyber warfare. They are often credited with high-profile attacks on foreign soil. A case in point is their suspected involvement in attacks on critical Ukrainian infrastructure in the past, leading to blackouts and disruption of services. While the FSB prefers subterfuge, GRU's approach is more direct, aiming to cripple adversaries.
Documents in review
Background:
The FSB (Federal Security Service) and GRU (Main Directorate of the General Staff) stand as two of Russia's foremost intelligence agencies, deeply rooted in the nation's intelligence and espionage endeavors, both within its borders and on the international stage. Their significance is further accentuated within the framework of the Russian-Ukrainian conflict. This conflict, characterized by territorial contentions, political discord, and a wider battle for dominion in the region, has witnessed an evolution in the art of warfare. A notable manifestation of this evolution is the rise of cyber operations as a pivotal component of the conflict's dynamics.
Throughout the duration of this conflict, both the FSB and GRU have been at the forefront of cyber activities. Their operational spectrum has spanned from spear-phishing attacks, meticulously crafted to extract critical information, to broad disinformation campaigns, orchestrated with the intent to mold public sentiment. Yet, in the midst of their expansive capabilities and clear objectives, there emerges a discernible gap in the coordination between their cyber-centric operations and Russia's traditional military maneuvers. This disjointed approach has, at times, led to missed opportunities that could have strategically amplified the impact of their cyber initiatives.
Compounding the challenges is the fluid nature of cyber warfare. The digital battleground is in a state of perpetual flux, demanding adaptability and innovation. Both the FSB and GRU, in response to this dynamic environment, have found themselves recalibrating their strategies and tactics, underscoring the imperative to remain agile in the face of the shifting contours of digital warfare.
Introduction:
In the intricate tapestry of global intelligence and espionage, Russia's FSB (Federal Security Service) and GRU (Main Directorate of the General Staff) emerge as pivotal threads. These agencies, deeply entrenched in Russia's domestic and international intelligence endeavors, have found their roles magnified against the backdrop of the Russian-Ukrainian conflict. This conflict, with its layers of territorial disputes, political tensions, and overarching power struggles, has also been a crucible for the evolution of modern warfare. A testament to this evolution is the ascendance of cyber operations, which have become central to the conflict's dynamics.
As the conflict has unfolded, the FSB and GRU have been at the vanguard of cyber warfare. Their arsenal of tactics is vast, ranging from spear-phishing attacks, designed with precision to glean vital information, to expansive disinformation campaigns, strategically deployed to shape public opinion. However, despite their vast capabilities and well-defined goals, a glaring chasm has been evident in the synchronization of their cyber operations with Russia's conventional military strategies. This lack of cohesion has occasionally resulted in potential strategic advantages slipping through the cracks.
The realm of cyber warfare is akin to shifting sands, constantly changing and presenting new challenges. In this volatile environment, adaptability becomes paramount. Both the FSB and GRU, recognizing the mercurial nature of the digital battlefield, have been in a state of continuous adaptation, underlining the necessity to stay nimble and innovative amidst the ever-changing dynamics of cyber warfare.
Summary:
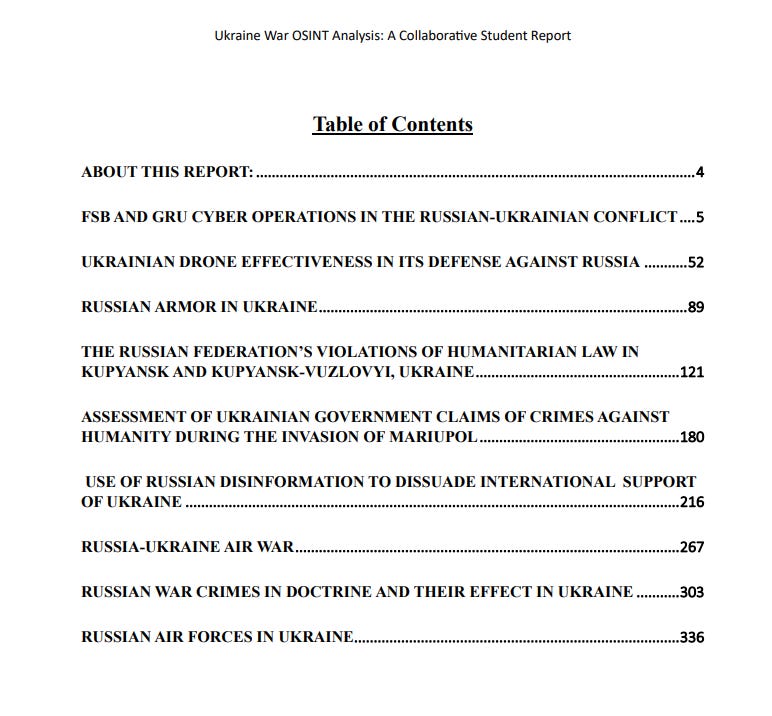
"Ukraine War OSINT Analysis: A Collaborative Student Report" is a product of nine undergraduate students from Virginia Tech's Department of Political Science and the International Studies Program. Under the guidance of Dr. Aaron Brantly, they utilized open-source materials to analyze the ongoing war in Ukraine, focusing on the cyber operations of Russia's primary intelligence agencies, the FSB (Federal Security Service) and GRU (Main Directorate of the General Staff).
The Bottom Line Up Front (BLUF) highlights that the cyber operations of the GRU and FSB in the Russian-Ukrainian conflict have not been as publicly successful as initially anticipated by intelligence predictions. While Russia's approach to information warfare is comprehensive, encompassing both technological and psychological operations, there have been evident gaps in the coordination between their cyber activities and conventional military operations. This lack of synergy has occasionally resulted in missed strategic opportunities, potentially limiting the overall impact of their cyber campaigns.
Furthermore, key judgments emphasize that the GRU's cyber operations have remained relatively static throughout the conflict, whereas the FSB's operations have shown some evolution. It's also underscored that Russian cyber operations have not provided a significant tactical or strategic advantage in the conflict, attributing this to the lack of coordination, the unexpected duration of the conflict, and the infrequency of impactful cyber operations.
In essence, while the FSB and GRU have been actively involved in various cyber activities throughout the conflict, their efforts have not always translated into tangible strategic gains, highlighting the complexities and challenges of integrating cyber operations into broader military strategies.
Assessment:
Emerging from the lineage of the once-dreaded KGB, Russia's primary intelligence agencies, the FSB and GRU, have adeptly transitioned into the digital age, becoming formidable entities in the cyber realm. Within the complex tapestry of the ongoing Russian-Ukrainian conflict, these agencies have been actively leveraging cyber operations to further their geopolitical objectives. The FSB, with its historical roots in counterintelligence and internal security, demonstrates an affinity for subterfuge in the digital space. They employ tactics like Advanced Persistent Threats (APTs), which allow them to maintain a prolonged, silent presence within compromised systems, gathering invaluable data over extended periods. Further showcasing their adaptive nature, the FSB has been known to form strategic collaborations with cybercriminal groups, pooling resources and expertise to compromise critical infrastructure and extract sensitive information.
Contrastingly, the GRU exhibits a more aggressive stance in its cyber operations. Distinct from the FSB's more covert approach, the GRU often engages in high-profile cyber-attacks, targeting vital infrastructure in foreign territories. Past instances have implicated them in significant disruptions, particularly in Ukraine, revealing a strategy focused on direct confrontation and causing tangible damage to adversaries.
Yet, beyond these technical onslaughts, a more insidious tactic has gained global prominence: disinformation campaigns. Both the FSB and GRU have masterfully infiltrated social media platforms, deploying a barrage of fake news and manipulated narratives. These orchestrated campaigns serve a dual purpose: firstly, painting Russia in a favorable or victimized light, thereby deflecting international criticism, and secondly, destabilizing perceived adversaries from within by exacerbating socio-political divisions. This confluence of traditional espionage techniques with modern cyber warfare tools underscores the evolving nature of international conflicts in the digital age. As nations grapple with these blurred lines between warfare and information warfare, understanding the methodologies of agencies like the FSB and GRU becomes crucial in shaping responses and strategies for the future.
Conclusion:
The Russian-Ukrainian conflict has been a theater for various modes of warfare, with cyber operations emerging as a significant facet. Two of Russia's primary intelligence agencies, the FSB and GRU, have been actively involved in these cyber activities. However, their operations have not been as publicly successful as initially anticipated by intelligence predictions. While Russia's approach to information warfare is comprehensive, encompassing both technological and psychological facets, there have been evident gaps in their execution.
A notable observation is the evolution (or lack thereof) in the cyber operations of these agencies. The GRU's cyber activities have remained relatively consistent throughout the conflict, whereas the FSB has shown signs of adaptability and experimentation. Despite these efforts, Russia hasn't derived a significant tactical or strategic advantage from its state-sponsored cyber operations. This limitation can be attributed to several factors:
Lack of Coordination: There's a discernible disconnect between Russia's conventional military operations and its cyber-centric activities. This lack of synergy has occasionally resulted in missed strategic opportunities, potentially limiting the overall impact of their cyber campaigns.
Longevity of the Conflict: The protracted nature of the Russian-Ukrainian conflict seems to have impacted the effectiveness of Russia's cyber operations. The sustained duration might have led to operational fatigue or resource allocation challenges.
The Infrequency of Impactful Operations: While there have been cyber attacks, not all have had a significant or lasting impact on the conflict's dynamics. This infrequency has curtailed the potential advantages Russia could have derived from a more consistent and impactful cyber campaign.
In light of these observations, it's evident that while cyber warfare holds immense potential as a tool of statecraft and conflict, its effectiveness is contingent on strategic planning, coordination, and adaptability. The Russian-Ukrainian conflict serves as a case study, underscoring the complexities and challenges inherent in integrating cyber operations within the broader framework of warfare.