Daily Drop (746): France: Poss. Anonymous Sudan, CHAVECLOAK, US IC: Foreign AI, RU: Arrested Won-soon, Open Source Grok, CISA hit, SVR: U.S. Interference, BianLian, Pentagon: UFO , Iran Sanctions
03-12-24
Tuesday, Mar 12 2024 // (IG): BB // ShadowNews // Coffee for Bob // Proxies
*Started adding the Proof Of Concepts (PoC) if available for mentioned CVE’s :
A Proof of Concept (PoC) is a small exercise to test a certain hypothesis or demonstrate that a potential project can be viable. It's primarily used to verify that certain concepts or theories have the potential for real-world application. The purpose of a PoC is to showcase the feasibility, functionality, and potential of a concept before proceeding to the development of the full-scale project. *
Unprecedented Cyberattacks Strike French Government Services
Bottom Line Up Front (BLUF): French government agencies, including the Prime Minister's office, reported a series of intense cyberattacks of unprecedented scale beginning Sunday night. The attackers, whose identities remain unconfirmed, targeted multiple ministerial services with techniques familiar to cybersecurity experts but with previously unseen intensity. Although a group named Anonymous Sudan claimed responsibility, French officials have not directly attributed the attack to any specific entity. Measures have been promptly taken to mitigate the impact, ensuring most services and state websites were restored swiftly.
Analyst Comments: The recent cyber onslaught against French state entities underscores the escalating cyber warfare landscape, where state and non-state actors leverage digital means to disrupt governmental operations. This incident not only reflects the growing sophistication of cyber threats but also highlights the strategic significance of cyber resilience for national security. The timing and targets suggest a calculated attempt to undermine France's governmental functions, potentially in retaliation for its geopolitical stances or to cause general destabilization. While direct attribution is challenging in the cyber realm, the involvement of groups like Anonymous Sudan, known for their pro-Russian stance, aligns with the broader context of geopolitical tensions, especially concerning Russia's activities in cyberspace.
FROM THE MEDIA: French state bodies were hit by cyberattacks described as "unprecedented intensity," affecting several ministerial services since Sunday. Prime Minister Gabriel Attal's office confirmed the containment of these attacks, although specifics about the perpetrators or the exact nature of the attacks remain undisclosed. Security sources indicated that these attacks were not attributable to Russia directly, despite speculation . A crisis cell was activated to deploy countermeasures, significantly reducing the impact and restoring access to affected state websites.
READ THE STORY: Le Monde // Security Affairs // La Prensa Latina
New Banking Trojan "CHAVECLOAK" Targets Brazilian Users Through Sophisticated Phishing Tactics
Bottom Line Up Front (BLUF): FortiGuard Labs has identified a new banking Trojan, dubbed CHAVECLOAK, targeting Brazilian users via phishing emails with malicious PDF attachments. This high-severity threat leverages DLL side-loading to execute and control victims' devices, collecting sensitive financial information. The malware exhibits a high level of sophistication, employing tactics similar to other well-known banking Trojans in the South American cyberthreat landscape, posing a significant risk to individuals engaged in online banking and financial transactions in Brazil.
Analyst Comments: CHAVECLOAK represents a significant evolution in the banking Trojan landscape, specifically tailored to exploit Brazilian users' online financial activities. Its deployment through a malicious PDF, masquerading as a DocuSign document, indicates a nuanced understanding of social engineering tactics to bait users into initiating the malware's download and execution process. The malware's ability to side-load DLLs underlines the increasing complexity of threats facing users in regions with high digital banking penetration. CHAVECLOAK's focus on Brazil, a country with a robust online banking user base, underscores the continuous targeting by cybercriminals of regions perceived as lucrative due to their high transaction volumes and potentially lax cybersecurity measures.
FROM THE MEDIA: FortiGuard Labs' discovery of the CHAVECLOAK banking Trojan highlights a multifaceted attack strategy beginning with a phishing email containing a PDF file. Upon interaction, the file triggers the download of a ZIP file, which then employs DLL side-loading to activate the CHAVECLOAK malware. This banking Trojan is meticulously crafted to intercept and steal sensitive financial information from Brazilian users, employing techniques to ensure persistence on the infected device and communication with a Command and Control (C2) server. Its operational tactics mirror those of established banking Trojans in the region, like Casbaneiro and Grandoreiro, emphasizing the malware's potential impact on financial security in Brazil. CHAVECLOAK's mechanism involves monitoring the victim's activity and deploying deceptive pop-up windows to capture banking credentials and personal information. It demonstrates an advanced capability to manipulate users' interactions with financial portals, extending its reach to cryptocurrency platforms. The discovery of an older Delphi variant of CHAVECLOAK further illustrates the malware's evolving nature and the continuous threat landscape development in South America.
READ THE STORY: FORTINET // THN
U.S. Intelligence Agencies Raise Alarm on AI's Rapid Evolution and Security Threats
Bottom Line Up Front (BLUF): Top U.S. intelligence officials express increasing concern over the pace of artificial intelligence (AI) development and its potential to impact national security. The rapid advancement of machine learning models threatens to outpace governmental response capabilities, potentially leading to economic disparities, misinformation campaigns, AI-generated cyber threats, and unanticipated consequences in both the digital and physical realms.
Analyst Comments: The intelligence community's annual threat assessment underscores the multifaceted nature of the challenges posed by the swift evolution of AI technologies. Notably, the FBI's concern about the potential for U.S. AI models to be stolen and used by foreign adversaries, such as China, highlights the critical intersection of AI innovation and cybersecurity. The apprehension that enhanced AI capabilities could significantly augment the effectiveness of adversarial cyber operations reveals an urgent need for robust AI security measures and international cooperation to mitigate the risks associated with AI proliferation.
FROM THE MEDIA: During a Senate Intelligence Committee hearing, U.S. intelligence officials, including FBI Director Christopher Wray and CIA Director William Burns, detailed the complex web of threats emanating from the rapid innovation in AI technology. The arrest of a Chinese national for allegedly stealing AI-related material from Google serves as a stark reminder of the geopolitical stakes involved in securing AI advancements. Additionally, the report's emphasis on the dangers posed by the misuse of commercial spyware and the acquisition of sensitive data by intelligence agencies through commercially available means underscores the intricate balance between leveraging technological advancements for national security purposes and protecting civil liberties. The proliferation of AI technologies necessitates a reevaluation of existing regulatory frameworks and the development of new strategies to safeguard democratic institutions and critical infrastructure from the destabilizing effects of AI-enabled cyber operations and misinformation campaigns.
READ THE STORY: CYBERSCOOP
South Korean Citizen Detained in Russia on Cyber Espionage Charges
Bottom Line Up Front (BLUF): Russia has detained a South Korean national, Baek Won-soon, on charges of cyber espionage, marking a significant development amid escalating tensions between Russia and South Korea. Won-soon, arrested in Vladivostok and transferred to Moscow for further investigation, is accused of transmitting classified information to foreign intelligence services. His detention, extended until June 15, 2024, adds a new dimension to the complex geopolitical landscape influenced by cyber activities.
Analyst Comments: The arrest of Baek Won-soon represents a notable escalation in Russia's stance towards South Korea, a country it deems "unfriendly" due to its support for Western sanctions over the Ukraine conflict. This incident underscores the increasing role of cyber espionage in international relations, highlighting how digital spaces become battlegrounds for geopolitical rivalries. The choice of a South Korean national for such charges suggests a broadening spectrum of targets beyond the traditional West-Russia dichotomy, possibly signaling a more aggressive posture by Russia in cyberspace. Moreover, the timing coincides with growing Russian-North Korean military cooperation, indicating a complex web of alliances and enmities shaping the current geopolitical climate.
FROM THE MEDIA: A South Korean citizen, Baek Won-soon, was detained in Russia on cyber espionage charges, marking a rare occurrence of a South Korean national being arrested for such allegations in Russia. According to Russian news agency TASS, Won-soon was initially arrested in Vladivostok and later moved to Moscow's Lefortovo pretrial detention center, known for its stringent conditions. The charges involve the transmission of "top secret" information to unnamed foreign intelligence agencies. This incident occurs amidst deepening geopolitical connections between Russia and North Korea, with North Korean state-sponsored hacking groups targeting Russia for intelligence-gathering missions. The case draws parallels with other high-profile detentions in Russia, including American journalist Evan Gershkovich, and unfolds against a backdrop of increased cyber espionage activities globally .
READ THE STORY: The Diplomat // Nikkei Asia // VOA
Elon Musk to Open Source Grok, His ChatGPT Rival, Amid Legal Battle with OpenAI
Bottom Line Up Front (BLUF): Elon Musk's AI startup, xAI, announced plans to open source Grok, a chatbot rivaling ChatGPT. This decision follows Musk's recent lawsuit against OpenAI for deviating from its original open-source and non-profit mission. Grok, currently exclusive to subscribers of the social media platform X, aims to become more widely accessible, potentially democratizing innovations in AI but also raising concerns about misuse.
Analyst Comments: Elon Musk's move to open source Grok signifies a strategic pivot in the competitive landscape of generative AI technologies. By making Grok's code publicly available, Musk not only underscores his commitment to open-source principles but also challenges OpenAI's increasingly proprietary approach. This could catalyze a broader participation in AI development, fostering innovation and possibly accelerating advancements in the field. However, this openness comes with risks, notably the potential for exploitation by malicious actors. Musk's legal confrontation with OpenAI highlights a deeper ideological rift within the AI community regarding the balance between innovation, commercialization, and ethical governance of AI technologies.
FROM THE MEDIA: Elon Musk's xAI plans to make the Grok chatbot open source, a significant shift that promises to enhance collaborative innovation in AI while also posing potential security risks. The move is partly a response to Musk's dissatisfaction with OpenAI's partnership with Microsoft and departure from its non-profit, open-source roots. Grok, inspired by "The Hitchhiker's Guide to the Galaxy" and currently available to X's premium subscribers, aims to offer a less biased alternative to ChatGPT. This open-sourcing initiative may broaden Grok's user base and encourage community-driven improvements and applications.
READ THE STORY: Mashable // Wired // Forbes
CISA's Cybersecurity Breach: A Wake-Up Call for Critical Infrastructure Security
Bottom Line Up Front (BLUF): The U.S. Cybersecurity and Infrastructure Security Agency (CISA) recently suffered a breach due to vulnerabilities in Ivanti products, marking a significant cybersecurity event that underscores the ongoing threats to critical infrastructure and the necessity for robust vulnerability management and patch/configuration management practices.
Analyst Comments: This incident highlights a crucial aspect of cybersecurity: no organization is immune to cyber vulnerabilities, emphasizing the importance of an incident response plan. The exploitation of Ivanti's vulnerabilities by multiple threat groups, including espionage activities linked to China, points to the sophisticated nature of attackers targeting critical U.S. infrastructure. The breach of systems like the Infrastructure Protection (IP) Gateway and the Chemical Security Assessment Tool (CSAT) demonstrates the potential risks to national security and critical industry operations.
FROM THE MEDIA: The breach, facilitated through exploitation of high-severity vulnerabilities in Ivanti's Connect Secure, Policy Secure, and Neurons for Zero Trust Access products, underscores the strategic targeting by cybercriminals and state-sponsored groups of systems critical to national security and infrastructure. Despite the prompt response by CISA in taking the affected systems offline, the incident raises concerns about the potential for undetected breaches within organizations using Ivanti products, especially given the capability of threat actors to bypass the Integrity Checker Tool (ICT). The newly identified threat group, Magnet Goblin, exemplifies the adaptability and financial motivation behind exploiting such vulnerabilities, employing a range of sophisticated malware tools for data theft and persistent access to compromised networks. This breach serves as a critical reminder for organizations to reassess the security of their Ivanti deployments and consider the broader implications of such vulnerabilities on their operational resilience and cybersecurity posture.
READ THE STORY: SC Media
The Kremlin's foreign intelligence service, SVR, levels serious allegations against the Biden administration ahead of Russia's presidential election
Bottom Line Up Front (BLUF): Russia's Foreign Intelligence Service (SVR) accuses the US, specifically the Biden administration, of planning to interfere in the upcoming Russian presidential election. Allegations include a scheme to reduce voter turnout and launching a cyberattack on Russia's online voting system. The SVR, however, has not provided concrete evidence to support its claims. These accusations come amid historical tensions and accusations of election interference between the two nations.
Analyst Comments: The SVR's allegations against the US mark another chapter in the long-standing saga of geopolitical tension and accusations of electoral interference between Russia and the United States. Historically, both nations have accused each other of meddling in domestic electoral processes, with significant attention on the US indicting the Russian Internet Research Agency for its alleged role in the 2016 US election. The timing of these allegations, close to the Russian presidential election in which President Putin is widely expected to win, could be seen as preemptive deflection or as a means to consolidate domestic support by framing external threats. Furthermore, the lack of provided evidence and the historical context of Russia's own accusations of meddling abroad paint a complex picture of international relations where cyber capabilities and influence operations have become central to geopolitical strategies.
FROM THE MEDIA: The SVR's accusations against the US include plans to meddle in Russia's presidential election by decreasing voter turnout and attacking the online voting system through cyber means, specifically targeting the electronic counting of votes. These allegations were made without presenting direct evidence. Additionally, the SVR's statement coincides with President Putin's warnings against foreign interference in the election, framing such actions as aggression. Meanwhile, the Kremlin has denied any intentions of meddling in US elections, contrasting its claims of non-interference with its accusations against the US.
READ THE STORY: The Register // Reuters // Ground
BianLian's Strategic Pivot: Embracing Extortion-Only Cyber Tactics
Bottom Line Up Front (BLUF): The BianLian threat actor group has significantly shifted its operations towards extortion-only tactics, as observed by GuidePoint’s Research and Intelligence Team (GRIT). This adaptation follows the public release of a decryptor for BianLian's previous ransomware, compelling the group to evolve its approach by exploiting vulnerabilities in systems like TeamCity servers for initial access and control.
Analyst Comments: The evolution of BianLian's strategy underscores a larger trend within the cybersecurity threat landscape, where actors quickly adapt to countermeasures and seek new vulnerabilities. The group’s shift to extortion without deploying ransomware suggests a focus on minimizing efforts while maximizing returns, leveraging the threat of data exposure as their main leverage. This trend is indicative of the adaptability of cyber threat actors and the continuous arms race between cybersecurity defenses and offensive tactics.
FROM THE MEDIA: Recent investigations have unveiled a deeper insight into BianLian's refined modus operandi, exploiting specific vulnerabilities (CVE-2024-27198 and CVE-2023-42793) in TeamCity servers for unauthorized access. Once inside, the attackers deploy sophisticated PowerShell scripts to maintain persistence and control over the compromised systems, utilizing advanced obfuscation and communication techniques to evade detection. This shift in tactics highlights BianLian's technical sophistication and their ability to bypass conventional security measures. GuidePoint’s advisory emphasizes the importance of preparedness against such threats, advocating for rigorous patch management, incident response planning, penetration testing, and the strategic application of threat intelligence.
READ THE STORY: InfoSecMag
Unmasking the Unknown: The Pentagon's UFO Inquiry and the Lingering Mysteries
Bottom Line Up Front (BLUF): A recent Pentagon report on Unidentified Anomalous Phenomena (UAP) concludes there's no evidence of extraterrestrial contact or technology reverse-engineering, yet it leaves several key questions unanswered, prompting further speculation and investigation into the nature of unidentified sightings and the advanced technologies possibly being developed in secrecy.
Analyst Comments: The Pentagon's All-domain Anomaly Resolution Office (AARO) report, despite its extensive investigation, has not fully satisfied public curiosity or scientific inquiry regarding UAPs. The meticulous denial of alien encounters or technology reverse-engineering subtly shifts focus towards the possibilities of terrestrial advancements in technology and physics that might be mistaken for extraterrestrial. The report's ambiguity over specific programs and technologies hints at a complex intersection of defense secrecy, scientific innovation, and public speculation. Given the historical context of government secrecy surrounding advanced military technology, this report adds another layer to the enigmatic narrative of UAPs, emphasizing the blurred lines between national security, scientific advancement, and the human imagination's reach into the cosmos.
FROM THE MEDIA: The Pentagon's latest UFO report, spearheaded by AARO, maintains a firm stance against the existence of alien technology or government cover-ups regarding extraterrestrial contact. This conclusion follows extensive interviews, research into classified and unclassified programs, and the scrutinization of claims made by individuals such as whistleblower David Grusch. The report, however, not only debunks the alien technology myth but inadvertently raises more questions than it answers about the nature of the undisclosed advancements and materials under examination. Speculations range from foreign technological recovery, advanced US technology, speculative basic research, and the outer edges of known physics, suggesting a vast field of unknowns still to be explored.
READ THE STORY: Wired // The Hill
Biden Faces Critical Decision On $10 Billion Iran Sanctions Waiver Amid Regional Unrest
Bottom Line Up Front (BLUF): US President Joe Biden is at a pivotal juncture with the impending decision on whether to renew a $10 billion sanctions waiver for Iran. This decision comes at a particularly sensitive time, given the ongoing war in Gaza and continuous attacks in the Red Sea by Iran-backed Houthis. The waiver, initially extended last year, allows Iraq to buy electricity from Iran and enables Tehran access to $10 billion in escrow accounts for humanitarian purposes, amidst bipartisan concerns over potential misuse of funds.
Analyst Comments: The timing of President Biden's decision on the sanctions waiver is critical, with the Middle East engulfed in heightened tensions. The waiver's extension last year was met with skepticism from both sides of the US political spectrum, reflecting fears that Iran could redirect the funds toward militaristic ends, under the guise of humanitarian aid. The recent unrest, marked by drone attacks and increased aggression in the Red Sea, underscores the complexity of this decision. The possibility that Tehran might use escrow funds to support its proxies, despite restrictions aimed at humanitarian aid, presents a significant policy dilemma for the Biden administration.
FROM THE MEDIA: This critical juncture arrives amid escalating violence in the Middle East, including the war in Gaza and Iran-backed Houthi attacks. Last year, the Biden administration allowed a four-month extension of the sanctions waiver, facilitating Iraq's purchase of Iranian electricity and granting Iran limited access to $10 billion in escrow funds for humanitarian goods. The decision faced immediate bipartisan criticism over concerns that Iran could divert these funds to support its military proxies. The utilization of these funds by Iran remains largely opaque, with US Treasury officials providing minimal public information. Recent events have intensified scrutiny of the US's approach to Iran, as attacks on US service members and increased Houthi aggression raise questions about the efficacy of sanctions waivers as a tool for regional stability. Critics argue that the waiver could inadvertently finance Iran's contentious activities in the region, highlighting a significant challenge for US policy in navigating the intricate dynamics of Middle Eastern geopolitics.
READ THE STORY: Iran International
Stratolaunch's Leap to Supersonic: A Milestone for Hypersonic Ambitions
Bottom Line Up Front (BLUF): Stratolaunch successfully completed its first powered flight of the Talon-A test vehicle (TA-1), achieving high supersonic speeds approaching Mach 5. Although the mission ended with a planned splashdown in the Pacific and did not reach hypersonic speed, it marks a significant step forward in the company's goal of developing a reusable hypersonic testbed.
Analyst Comments: Stratolaunch's recent test flight of TA-1 represents a pivotal moment in the evolution of hypersonic technology. Founded by the late Paul Allen, Stratolaunch has shifted its focus towards hypersonic flight testing, aiming to fill a critical gap in the aerospace industry's test capabilities. By achieving near Mach 5 speeds, Stratolaunch has edged closer to the hypersonic regime, defined as speeds greater than Mach 5. The successful demonstration of its air-launch system and controlled flight dynamics highlights the company's potential to offer unique opportunities for hypersonic research and development. As geopolitical interests intensify the race for hypersonic capabilities, Stratolaunch's advancements could play a crucial role in ensuring the U.S. remains at the forefront of aerospace technology.
FROM THE MEDIA: Stratolaunch, known for its gigantic Roc carrier aircraft, has made significant strides in the field of hypersonic testing with the successful flight of the Talon-A test vehicle (TA-1). The test achieved its primary objectives, including the demonstration of the air-launch release system and achieving high supersonic speeds. Despite the vehicle not being intended for reuse, its successor, TA-2, is slated for launch later in 2024, with TA-3 currently under construction. The company's discreet approach to sharing flight details, citing proprietary agreements, underscores the competitive and secretive nature of hypersonic technology development. Stratolaunch's efforts complement existing aerospace ventures like Virgin Galactic, yet its unique focus on hypersonic speeds and the impressive capabilities of the Roc set it apart as a pivotal player in the future of high-speed aerospace research.
READ THE STORY: The Register
Items of interest
GPT-4's Unique Approach to Playing DOOM: A Mix of Innovation and Limitation
Bottom Line Up Front (BLUF): Adrian de Wynter, a principal applied scientist at Microsoft and researcher, explores GPT-4's ability to interact with the classic game DOOM, revealing the model's limitations in direct game execution but showcasing a creative workaround that enables it to play the game without specific training.
Analyst Comments: The investigation into GPT-4's ability to run and play DOOM by Adrian de Wynter highlights a fascinating aspect of AI development: the creative application of AI tools to perform tasks beyond their direct capabilities. While GPT-4 cannot execute DOOM's source code due to its nature as a language model, the introduction of GPT-4V, its multimodal variant, along with a Vision component and an Agent model, offers an ingenious solution. This setup captures game states as screenshots and interprets them to generate actionable commands within the game environment. The experiment underlines the potential of AI to engage in complex problem-solving through unconventional means, albeit with notable limitations such as a lack of object permanence and poor reasoning capabilities.
FROM THE MEDIA: Adrian de Wynter's experiment with GPT-4 and DOOM underscores the model's inability to directly run the game but demonstrates its capacity to play through an innovative combination of AI models and additional code. By integrating GPT-4V with a Vision component to analyze screenshots and an Agent model for decision-making, the setup navigates the game environment, making decisions like opening doors and firing weapons. This approach, however, reveals critical weaknesses, including the AI's forgetfulness about off-screen threats and challenges in logical reasoning. De Wynter's exploration raises questions about the ethical implications of AI's capabilities and the potential for misuse, even as it showcases the model's adaptability and potential for innovation in unexpected applications.
READ THE STORY: The Register
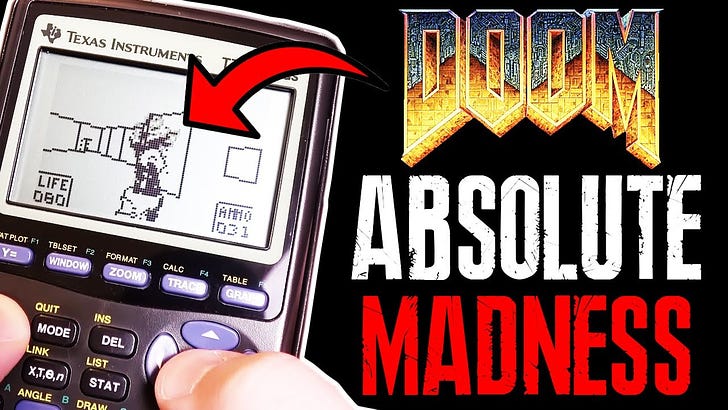
Why DOOM Runs On EVERYTHING (Video)
FROM THE MEDIA: In today's video, we are finally going to see why DOOM is able to run on basically any electronic device that exists in this world. I really hope you enjoy.
Can ChatGPT make a DOOM map? (Video)
FROM THE MEDIA: Yes it can.
These open-source products are reviewed by analysts at InfoDom Securities, providing possible context about current media trends related to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not endorse any third-party claims made in their original material or related links on their sites; the opinions expressed by third parties are theirs alone. For further questions, please contact InfoDom Securities at dominanceinformation@gmail.com.