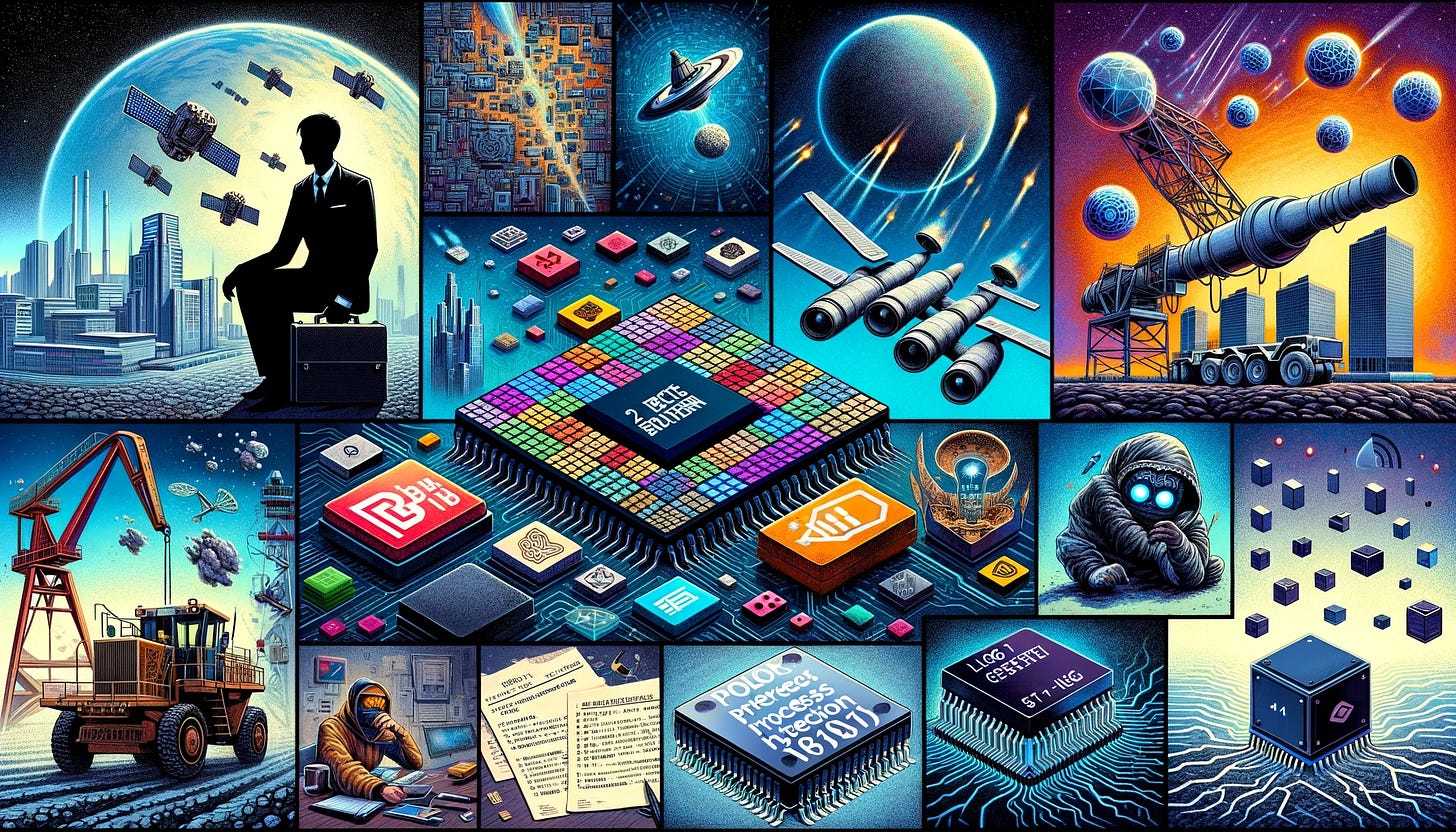
Daily Drop (681): SpyLoan Scandal, Space Debris Crisis, Mining Industry, 'Lego-Style' Semiconductor, Patent Litigation in China, PoolParty Process Injection, Bitcoin, Satoshi, Tencent, Qualcomm's 5G
12-11-23
Monday, Dec 11, 2023 // (IG): BB // ShadowNews // Coffee for Bob
SpyLoan Scandal: 18 Malicious Loan Apps on Android Defraud Millions
Bottom Line Up Front (BLUF): Eighteen malicious loan applications, collectively downloaded over 12 million times from the Google Play Store, have been unmasked for defrauding users. Operating under the guise of legitimate loan services, these apps, known as SpyLoan, exploited user trust to steal personal and financial information, resorting to blackmail and harassment.
Analyst Comments: The discovery of the SpyLoan scandal highlights a worrying trend in the cybersecurity landscape, where seemingly legitimate mobile applications are weaponized to conduct large-scale fraud and espionage. This case underscores the evolving tactics of cybercriminals, leveraging the ubiquity of smartphones to access sensitive personal data. The targeting of users in Southeast Asia, Africa, and Latin America reveals a strategic focus on regions possibly perceived as more vulnerable due to less stringent app vetting processes.
FROM THE MEDIA: ESET's research identified 18 Android loan apps, part of the SpyLoan operation, targeting users in Southeast Asia, Africa, and Latin America. The apps, now removed from Google Play Store, utilized misleading descriptions and high interest rates to defraud users while collecting sensitive data for extortion. Common infection pathways included SMS messages, social media channels, and third-party app stores. These apps represent an ongoing trend of malicious applications exploiting financial desperation, often involving predatory loan contracts and unauthorized access to personal information. Users are advised to download apps only from official sources and to scrutinize app permissions and reviews before installation.
READ THE STORY: THN
Space Debris Crisis: The Challenges and Solutions in Satellite Refueling
Bottom Line Up Front (BLUF): The inability to refuel satellites in space results in them becoming debris once their fuel is depleted, contributing to the growing issue of space junk. Efforts are underway to develop technologies for in-space refueling and debris removal, with entities like NASA, Orbit Fab, and Astroscale at the forefront of these initiatives.
Analyst Comments: The space debris problem is a consequence of the evolving nature of space exploration and satellite technology. Historically, satellites were designed as non-refuelable, single-mission entities, leading to an accumulation of space junk. This poses risks for operational satellites and space missions. The innovative steps toward satellite refueling and debris removal mark a paradigm shift in space technology, moving towards sustainability and the long-term utility of space assets. However, these developments also present technical and economic challenges, as they require new satellite designs and the establishment of orbital refueling infrastructure.
FROM THE MEDIA: The pressing issue in space exploration currently revolves around the inability to refuel satellites, leading to them becoming debris. With about 36,500 objects larger than 10 centimeters in Earth's orbit, mostly defunct satellites, this debris increases collision risks and space operation hazards. Efforts to address this include NASA's pioneering work in satellite refueling and Astroscale's technology for debris removal. The European Space Agency (ESA) and Swiss start-up Clearspace SA are collaborating on a mission to capture defunct rocket parts. Colorado-based Orbit Fab is developing technology for orbital refueling, focusing on satellites yet to be launched. They propose standardized fueling ports for easier refueling operations. These initiatives aim to extend satellite lifespans, reduce space debris, and enhance the sustainability of space activities.
Mining Industry Embraces Satellite-Enabled IoT for Enhanced Sustainability
Bottom Line Up Front (BLUF): A study by Viasat, Inc. shows a significant trend in the mining industry toward adopting satellite-enabled IoT technology. 86% of mining businesses plan to increase IoT usage within a year to bolster sustainability initiatives. The industry views IoT as crucial for improving sustainability measures and overcoming challenges posed by limited terrestrial connectivity.
Analyst Comments: The integration of IoT in the mining industry signals a transformative approach toward sustainability and operational efficiency. This shift is driven by the need for accurate, real-time data, which is essential for regulatory compliance and environmental stewardship. IoT, particularly satellite-enabled, offers a robust solution where terrestrial connectivity is lacking, providing a critical link in remote and challenging environments. This technological advancement not only aids in meeting sustainability goals but also aligns with the growing global emphasis on Environmental, Social, and Governance (ESG) criteria. However, the successful implementation of these technologies requires significant investment, training, and a strategic approach to data management and analysis.
FROM THE MEDIA: The study commissioned by Viasat and covering over 200 senior technology and ESG decision-makers in the mining industry reveals a substantial move towards IoT for sustainability. The report indicates 85% of respondents view their businesses as more sustainable than peers, though there's a perception gap regarding tangible sustainability metrics. A key finding is the reliance on satellite-enabled IoT solutions for improved sustainability, with many mining enterprises considering it a robust alternative for connectivity. The adoption of IoT has already yielded benefits, with 43% reporting reductions in CO2 emissions and biodiversity enhancements. The use of IoT data extends to engaging with local communities, industry peers, and customers on sustainability issues.
READ THE STORY: Global Mining Review
Innovative 'Lego-Style' Semiconductor Chip Developed by Sydney Researchers
Bottom Line Up Front (BLUF): Researchers from the University of Sydney Nano Institute have unveiled a new silicon semiconductor chip that integrates electronic and photonic components. This 'Lego-style' chip, less than 5 millimeters wide, offers enhanced radio-frequency bandwidth and precise information control, positioning Australia for sovereign chip manufacturing.
Analyst Comments: The development of this compact semiconductor chip represents a significant advancement in the field of integrated circuit technology. By combining electronics with photonics in a single chip, the researchers have created a platform that could revolutionize various applications, from telecommunications to radar systems. This innovation reflects a growing trend in semiconductor research towards more integrated, efficient, and versatile chip designs. It also underscores the importance of national capabilities in semiconductor production, especially in a global context where supply chains and technological sovereignty are increasingly critical.
FROM THE MEDIA: The University of Sydney's new chip, created with silicon photonics technology, is a result of a decade-long research effort. It integrates electronic 'chiplets' in a compact form, likened to assembling Lego blocks. This chip architecture enables Australia to potentially develop sovereign chip manufacturing capabilities. The innovation is aligned with the Australian government's focus on critical technologies, particularly semiconductors. The chip's impressive capabilities include a 15 gigahertz bandwidth of tunable frequencies and a spectral resolution of just 37 megahertz. Its potential applications are vast, spanning advanced radar, satellite systems, wireless networks, and future 6G and 7G telecommunications. This development aligns with the Semiconductor Sector Service Bureau (S3B) initiative and represents a significant stride in semiconductor innovation in Australia.
READ THE STORY: IE
The Rise of Patent Litigation in China: A New Arena for Multinationals
Bottom Line Up Front (BLUF): Multinational companies are increasingly engaging in patent litigation in China, a trend driven by the country's growing importance in the global market and the evolving legal landscape. Recent developments indicate a shift towards more robust patent enforcement, with Chinese courts frequently granting injunctions and enhanced damages, making it a strategic jurisdiction for intellectual property disputes.
Analyst Comments: The surge in patent litigation in China reflects the country's maturation as a key player in global intellectual property. The Chinese legal system's growing receptiveness to patent rights, seen in the increasing willingness to grant injunctions and enhanced damages, suggests a shift towards stronger IP enforcement. This is particularly significant for multinationals, for whom China's vast market is indispensable. The interplay of China's legal trends with global patent strategies underlines the importance of understanding and navigating the Chinese patent landscape. However, this also raises concerns about the balance between protecting patent rights and fostering innovation. Multinationals must carefully consider their legal strategies, balancing the benefits of stringent IP protection against potential challenges in a rapidly evolving jurisdiction.
FROM THE MEDIA: Ruixue Ran, Justin Wang, and Xiaoliang Chen from Covington & Burling highlight the evolving patent infringement litigation in China, noting the increasing involvement of foreign entities. In recent years, foreign-related cases have constituted over 10% of the caseload in China’s Intellectual Property Tribunal, with patent infringement disputes being a significant portion. The ease of obtaining injunctive relief in China, alongside the introduction of punitive damages in the 2020 amendment to Chinese patent law, makes China an attractive jurisdiction for resolving global patent disputes. The case of Sichuan Golden-Elephant Sincerity Chemical Co. v. Shandong Hualu-Hengsheng Chemical Co. demonstrates the Chinese Supreme People’s Court's (SPC) commitment to upholding patent rights, emphasizing intellectual property protection. Foreign entities often secure higher damages awards than domestic enterprises, with a notable percentage receiving substantial compensation. This trend underscores the strategic importance of Chinese courts for multinational corporations, not only for protecting interests within the Chinese market but also as a lever in global competition and dispute resolution.
READ THE STORY: Bloomberg Law
PoolParty Process Injection: A New Threat to Cybersecurity Evasion Techniques
Bottom Line Up Front (BLUF): PoolParty, a new set of eight process injection techniques, has emerged as a significant cybersecurity threat. It effectively evades top Endpoint Detection and Response (EDR) systems, posing challenges for Windows system security. Developed by SafeBreach researcher Alon Leviev, these methods demonstrate high flexibility and effectiveness in code execution, potentially impacting a broad range of processes.
Analyst Comments: The advent of PoolParty process injection techniques marks a notable development in cybersecurity threats. By exploiting the Windows user-mode thread pool, these methods showcase a sophisticated approach to bypassing modern EDR systems. This development reflects the ongoing arms race between cybersecurity defenses and offensive capabilities. The efficacy of PoolParty in evading detection from leading EDR solutions underscores the need for continuous innovation and vigilance in cybersecurity. It also highlights the complexities in securing systems against advanced threats, necessitating a multi-layered security approach that goes beyond traditional detection methods. As threat actors continually adapt and evolve, the cybersecurity community must proactively identify and mitigate such emerging threats.
FROM THE MEDIA: PoolParty, a collective name for eight new process injection techniques, can bypass EDR systems to execute code in Windows systems. Alon Leviev from SafeBreach discovered these methods, which he presented at the Black Hat Europe 2023 conference. These techniques leverage the Windows user-mode thread pool to insert work items into target processes, making them versatile and effective across various processes. The techniques involve manipulating worker factories, part of Windows thread management, to execute malicious shellcode. PoolParty's effectiveness is proven by its 100% success rate against major EDR solutions from companies like CrowdStrike, Cybereason, Microsoft, Palo Alto Networks, and SentinelOne. This revelation comes after the disclosure of another process injection technique, Mockingjay, which also highlighted vulnerabilities in security solutions. Leviev's research indicates that despite advancements in EDR technologies, there are still opportunities for developing undetectable and impactful process injection methods.
READ THE STORY: THN
Bitcoin Inscriptions Flagged as Cybersecurity Risk by US National Vulnerability Database
Bottom Line Up Front (BLUF): The US National Vulnerability Database (NVD) has classified Bitcoin inscriptions as a cybersecurity risk. This categorization is due to a vulnerability in certain versions of Bitcoin Core and Bitcoin Knots, exploited by the Ordinals Protocol, allowing for the bypassing of data carrier limits.
Analyst Comments: The inclusion of Bitcoin inscriptions in the NVD underscores the evolving nature of cybersecurity risks associated with blockchain technologies. The identified vulnerability, exploited by the Ordinals Protocol, highlights the challenges of maintaining blockchain security and integrity, especially in widely used platforms like Bitcoin. This development reflects the increasing scrutiny of blockchain technology by regulatory and oversight bodies, considering its growing impact on various sectors. While blockchain offers numerous benefits, this situation demonstrates the need for continuous vigilance and proactive measures to identify and mitigate potential vulnerabilities.
FROM THE MEDIA: The NVD's recognition of Bitcoin inscriptions as a cybersecurity risk stems from a vulnerability that allows data masking as code in some Bitcoin Core and Bitcoin Knots versions. This issue was notably exploited by inscriptions in 2022 and 2023. The vulnerability could lead to blockchain spamming with non-transactional data, potentially increasing network size and impacting performance and fees. The vulnerability is currently under analysis, and its resolution could impact Ordinals inscriptions on the network. Existing inscriptions, however, would remain due to the blockchain's immutability.
READ THE STORY: Cointelegraph
Satoshi Is Black: Perspectives from the Black Blockchain Summit
Bottom Line Up Front (BLUF): The Black Blockchain Summit, held at Howard University, continued to showcase optimism in the potential of cryptocurrency and blockchain technology for Black empowerment, despite the broader crypto market crisis exemplified by the FTX trial. Attendees remained hopeful about blockchain's role in economic liberation and social justice.
Analyst Comments: The Black Blockchain Summit represents a critical convergence of technology and social justice, particularly within the African-American community. The discussions at the summit reflect a nuanced understanding of cryptocurrency and blockchain as tools for economic empowerment and social change, rather than merely speculative investments. This aligns with the broader trend of marginalized communities exploring decentralized technologies as alternatives to traditional financial systems, which they often find exclusionary or discriminatory. However, the summit also echoes the complexities and risks involved in adopting such technologies, especially given the volatile nature of the crypto market and the technological and regulatory challenges involved.
FROM THE MEDIA: The Black Blockchain Summit at Howard University highlighted the ongoing belief in the transformative power of cryptocurrency and blockchain for Black communities, despite recent market downturns. The summit's agenda emphasized the potential of these technologies to address issues like poverty, the prison-industrial complex, and environmental injustice. Notably, the event featured discussions about the impact of Bitcoin and blockchain on global Black communities, envisioning a future where these technologies foster financial independence and disrupt traditional power structures. The summit also tackled critical issues, such as the risks and realities of investing in cryptocurrency, the need for greater technological literacy, and the creation of inclusive and equitable digital economies. The presence of influential figures in the Black crypto movement underscored the community's engagement and investment in these technologies as tools for empowerment and change.
READ THE STORY: Wired
Tencent's Futuristic Headquarters: A Glimpse into the Future of Corporate Spaces
Bottom Line Up Front (BLUF): Tencent's new headquarters, Tencent Helix, designed by German architect Ole Scheeren, is set to revolutionize corporate workspaces. Doubling the size of Apple’s headquarters, this innovative design promises a unique blend of functionality and community integration, reshaping the concept of a corporate office.
Analyst Comments: Tencent Helix represents a significant leap in corporate architecture, emphasizing both aesthetics and utility. This project reflects a growing trend in corporate space design that prioritizes employee well-being and environmental sustainability. By integrating communal spaces and focusing on natural ventilation, the design moves away from traditional office layouts and embraces a more holistic and environmentally conscious approach. Scheeren's design also signals a shift in corporate attitudes towards workspace design, moving beyond the conventional cubicle or playful, startup-style environments. This development aligns with broader corporate goals of fostering innovation and collaboration while being mindful of the environmental impact. However, corporations must balance such innovative designs with practical considerations of employee comfort and productivity.
FROM THE MEDIA: The Tencent Helix, conceived by Ole Scheeren, is a groundbreaking project destined to become Tencent's main headquarters by 2028, coinciding with the company's 30th anniversary. Encompassing 500,000 square meters, it's designed to house over 23,000 employees. The helix-inspired design features four spiraling towers around a central "Vortex Incubator," symbolizing a collaborative and interactive work environment. The design incorporates communal spaces and educational facilities, blurring the lines between public and private areas. Tencent Helix will be a key part of the "future city" vision in Shenzhen, emphasizing a car-free approach while maintaining accessibility through designated road bridges. The design reflects a conscious effort to integrate nature, with a focus on natural ventilation and a "sponge city" concept for sustainable water use. Scheeren’s vision challenges conventional corporate campus designs, advocating for a balanced approach that creates functional yet inviting workspaces.
READ THE STORY: IE
Critical Security Flaws Discovered in Qualcomm's 5G Chips
Bottom Line Up Front (BLUF): Security researchers at Singapore University of Technology and Design have identified high-severity vulnerabilities in Qualcomm’s 5G chips, potentially affecting a significant portion of the global smartphone market. These flaws could lead to a loss of 5G connection, requiring manual rebooting of affected devices.
Analyst Comments: The discovery of these vulnerabilities in Qualcomm's 5G chips is a crucial reminder of the ever-present cybersecurity risks in widely used technologies. The impact of these flaws is extensive, considering Qualcomm's chips are integral to numerous smartphone brands. This situation underscores the importance of continuous, rigorous security testing and timely patching of vulnerabilities in hardware components. It also highlights the collaborative nature of cybersecurity, where academic research plays a vital role in identifying potential threats. For users, the incident stresses the importance of regularly updating their device software to mitigate such risks.
FROM THE MEDIA: Dr. Matheus E. Garbelini and his team at the Singapore University of Technology and Design discovered vulnerabilities in Qualcomm’s 5G chips used in various smartphone models. These security flaws, identified as CVE-2023-33044, CVE-2023-33043, and CVE-2023-33042, could lead to a denial of service attack, causing a loss of 5G connection in approximately 714 smartphone models from 24 brands. The only remedy for affected devices is a manual reboot, sometimes requiring SIM card reinsertion. These findings were achieved through a method known as Wireless Fuzzing, highlighting the potential for malicious attacks from rogue 5G base stations. Qualcomm has acknowledged the issues and provided patches to Original Equipment Manufacturers (OEMs) in August 2023.
READ THE STORY: The Edge
Semiconductor Giants Compete to Develop Next-Generation '2 Nanometre' Chips
Bottom Line Up Front (BLUF): The world's leading semiconductor companies, including TSMC, Samsung, and Intel, are in a race to develop '2 nanometre' processor chips, a technological leap that will significantly impact the $500 billion industry. These advancements will power future smartphones, data centers, and AI technologies.
Analyst Comments: The pursuit of '2 nanometre' chips represents a pivotal moment in the semiconductor industry, highlighting the continuous drive for innovation in chip miniaturization. This race among industry giants like TSMC, Samsung, and Intel reflects the strategic importance of semiconductor technology in the global market. The development of smaller, more efficient chips is crucial for the advancement of various technologies, from consumer electronics to high-end computing and AI applications. The success of these companies in achieving this technological feat will not only influence their market position but also have broader implications for technological development and economic competitiveness.
FROM THE MEDIA: Taiwan Semiconductor Manufacturing Company (TSMC), Samsung Electronics, and Intel are focusing on developing '2 nanometre' chips, critical for the next wave of technological advancements. TSMC leads the race but faces stiff competition from Samsung, which offers cost-effective prototypes to attract major clients. Intel, once a market leader, is also making significant claims about its next-generation chips. The production of these advanced chips involves challenges, as smaller transistors mean lower energy consumption and higher speed, but also increased production complexity. Mass production is expected around 2025, with TSMC already showing test results to key clients like Apple and Nvidia. Samsung, despite being first to market with its 3nm chips, struggles with yield rates, whereas Intel aims to regain leadership with its ambitious production timelines.
READ THE STORY: FT
Two-Fifths of Log4j Apps Still Vulnerable to Critical Flaws
Bottom Line Up Front (BLUF): Despite efforts to patch critical vulnerabilities in Log4j, a popular utility in software applications, 38% of applications using Log4j remain vulnerable. These applications, spread across numerous organizations, are exposed to severe security risks, including the infamous Log4Shell vulnerability.
Analyst Comments: The persistence of vulnerabilities in Log4j applications two years after the discovery of the Log4Shell bug is concerning. It reflects challenges in patch management and the complexities of maintaining security in widely-used open-source software. Log4j's ubiquity in various applications magnifies the impact of these vulnerabilities, making them attractive targets for cybercriminals. This situation underscores the need for organizations to prioritize software security, particularly in commonly used open-source components. Continuous monitoring, timely patching, and a proactive approach to software maintenance are essential to mitigate such risks.
FROM THE MEDIA: Veracode's analysis reveals that 38% of applications running Log4j versions 1.1 to 3.0.0-alpha1 remain vulnerable to critical flaws. This includes 32% of applications running Log4j2 1.2.x, exposed to three critical vulnerabilities: CVE-2022-23307, CVE-2022-23305, and CVE-2022-23302. An additional 3.8% use Log4j2 2.17.0, containing CVE-2021-44832, while 2.8% are still vulnerable to the Log4Shell vulnerabilities in Log4j2 2.0-beta9 to 2.15.0. The original Log4Shell vulnerability (CVE-2021-44228), discovered in November 2021, had significant implications due to the widespread use of Apache's Log4j system in various applications and open-source components. Despite the concerted effort to patch this vulnerability, the ongoing risk in many applications indicates a gap in open-source security practices.
READ THE STORY: InfoSecMag
Items of interest
China's Expanding Cybersecurity Threats and Strategic Shifts in Hacking
Bottom Line Up Front (BLUF): Recent reports and warnings indicate a significant shift in China’s cybersecurity strategy. While continuing its traditional economic espionage activities, China is increasingly focusing on hacking critical infrastructure in the U.S. and other countries. This shift represents a strategic evolution in China's approach to cyber warfare, expanding from intelligence gathering to potentially disrupting critical services in the event of a conflict.
Analyst Comments: China's cyber strategy appears to be evolving, reflecting a broader ambition in the digital domain. Historically, China’s hackers focused on economic espionage and intelligence gathering, but recent U.S. government analyses suggest a significant shift towards targeting critical infrastructure. This strategy aligns with China's broader geopolitical goals and mirrors its increasing assertiveness on the world stage. The implications are profound, indicating a potential shift from conventional cyber espionage to more aggressive, potentially destructive cyber operations. This evolution in China's cyber activities reflects the dynamic nature of cyber threats and underscores the need for robust cyber defense strategies by the U.S. and its allies.
FROM THE MEDIA: China's cybersecurity strategy is shifting from traditional economic espionage to increasingly targeting critical infrastructure in the U.S. and its allies. This strategic evolution is seen as a response to geopolitical ambitions, moving from intelligence gathering to potential disruption of critical services in conflict scenarios. The U.S. views China as a significant geostrategic challenge in cyberspace, with Chinese hackers engaging in complex operations against American government systems and infrastructure. Despite this shift, China continues its economic espionage activities and is also developing advanced disinformation campaigns using artificial intelligence. The U.S. response involves heightened vigilance and international collaboration, indicating the need for a comprehensive strategy to counteract these multifaceted cyber threats.
READ THE STORY: LAWFARE // VOA
The global battle over microchips (Video)
FROM THE MEDIA: Computers, cars, mobile phones, toasters: countless everyday objects contain microchips. They’re tiny, unremarkable, and cheap, but since the outbreak of the coronavirus pandemic, they’ve been at the center of a political and industrial tug-of-war.
This Is How Huawei Shocked America With a Smartphone (Video)
FROM THE MEDIA: President Xi Jinping’s November meeting with President Joe Biden at the APEC summit in San Francisco came amid simmering tensions between China and the US. Technology has been at the heart of those strains, particularly Washington’s efforts to restrict Chinese access to key semiconductor innovations.
hese open-source products are reviewed by analysts at InfoDom Securities, providing possible context about current media trends related to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not endorse any third-party claims made in their original material or related links on their sites; the opinions expressed by third parties are theirs alone. For further questions, please contact InfoDom Securities at dominanceinformation@gmail.com.