Daily Drop (634): WebWyrm Exposé, OAuth Vul, Ukraine's Warfare, Chernihiv's Soul, Space Force: Delays, CVE-2023-5631, SpaceX: Canada, YoroTrooper, Parus-MGTU, Grammarly, IMAPLoader, CVE-2023-4320
10-26-23
Thursday, Oct 26, 2023 // (IG): BB // The Leek Sino-Satire // Coffee for Bob
The WebWyrm Exposé: Unmasking the China-Linked WhatsApp Job Fraud Network
Bottom Line Up Front (BLUF): Euronews Next's investigative dive uncovers a menacing global job scam operating through WhatsApp, intricately linked to cyber slavery rings and potentially orchestrated by Chinese entities. Thousands worldwide have fallen prey to this sophisticated operation, known as WebWyrm, with fraudulent job offers causing significant financial losses and psychological distress among victims. The scam's breadth and cyber enslavement angle highlight an alarming evolution in digital fraud.
Analyst Comments: The modus operandi of the WebWyrm network represents a nuanced evolution in cybercrime, where scammers exploit digital trust and communication platforms to orchestrate employment scams. By creating a mirage of legitimacy, these scammers deceive victims into participating in non-existent job opportunities, subsequently plunging them into financial losses through continuous investments, falsely portrayed as necessary for employment continuity. Furthermore, the global scale and adaptability of these scams signify a high level of organization, indicating the potential involvement of expansive cybercrime networks. These networks not only exploit individuals' desperation for employment but also exhibit traits of "cyber slavery" by trapping victims in exploitative pay-to-work cycles. The discovery of elements like Chinese coding in scam websites, and the adaptability in targeting based on regional factors like local currency, accentuates the complexity and extensive reach of this nefarious operation.
FROM THE MEDIA: The Euronews Next investigation illuminates a dark corner of the digital world, where a global job scam, potentially China-driven, exploits thousands via WhatsApp. This operation, known as WebWyrm, extends beyond financial deceit, hinting at a grim landscape of cyber slavery. The scam's elaborate nature, requiring extensive human interactions and sophisticated digital maneuvering, suggests victims are more than financially defrauded individuals; they might be the newest recruits in a burgeoning cyber slave trade. As global awareness grows, the necessity for coordinated international law enforcement action becomes paramount. However, the road to justice remains mired in geopolitical tensions, operational secrecy, and the ever-evolving face of cybercrime.
READ THE STORY: EuroNews
Critical OAuth Vulnerabilities Plague Popular Online Platforms: A Dive into the Security Loopholes
Bottom Line Up Front (BLUF): Critical security flaws were recently identified in the OAuth implementations of renowned online services, including Grammarly, Vidio, and Bukalapak. These vulnerabilities, which followed earlier discoveries in platforms like Booking.com and Expo, had the potential to enable cybercriminals to hijack user accounts by exploiting improperly handled access tokens. Though the issues have since been rectified, the incidents underscore the persistent risks associated with OAuth integrations and the imperative for rigorous security protocols.
Analyst Comments: The discovery of significant security shortcomings in the OAuth protocols of prominent online services brings to light the delicate balance in maintaining user security in the ecosystem of interconnected web applications. OAuth, while instrumental in enabling secure interactions between platforms, presents a high-stakes security challenge, primarily due to its widespread adoption across various services. The recent incidents involving Vidio and Bukalapak were characterized by a lack of rigorous token verification, a lapse that left room for attackers to deceive users into surrendering access tokens through fraudulent websites. These tokens could then be exploited, facilitating unauthorized intrusions into personal accounts.
FROM THE MEDIA: The revelation of critical OAuth vulnerabilities within Grammarly, Vidio, and Bukalapak amplifies ongoing concerns about the security of widespread authorization standards. While the immediate loopholes have been patched, the situation demands heightened industry vigilance. Companies must commit to continuous security evaluations and apply stringent authorization safeguards, acknowledging that even prevalent standards like OAuth are not immune to exploitation. This proactive mindset is paramount in fortifying user data against the ever-evolving landscape of cyber threats.
READ THE STORY: THN
Reengineering Survival: Ukraine's Unconventional Warfare Tactics
Bottom Line Up Front (BLUF): In the wake of dwindling Western support and resilient Russian opposition, Ukraine demonstrates remarkable ingenuity by salvaging and repurposing Russian electronic scrap into functional military drones. This move marks a strategic pivot, highlighting Ukraine's determination to sustain its defense capabilities despite external challenges and limited resources.
Analyst Comments: The Ukrainian conflict's dynamics have prompted a shift in strategic adaptations, primarily characterized by Ukraine's innovative approach to sustaining its military operations. With Western aid proving insufficient, Ukraine's turn to utilizing salvaged electronic components from Russian munitions underscores a deeper narrative of resourcefulness amid scarcity. This approach, particularly the assembly of drones using Russian technology, reflects not just a tactical improvisation but a symbolic act of resilience against a well-equipped adversary. The situation also casts a spotlight on the broader geopolitical undercurrents, where the inadequacy of international support intersects with Ukraine's on-ground realities. The repurposing of Russian technology is not merely a stop-gap measure but a calculated strategy within the larger framework of asymmetric warfare, where Ukraine is maximizing its available resources in the face of overwhelming odds.
FROM THE MEDIA: Ukraine's strategic shift to salvage and repurpose technology from adversarial forces underscores a significant turn in modern warfare dynamics, marked by ingenuity, resilience, and a pressing need for self-reliance. Faced with formidable challenges and inadequate external support, the country recalibrates its military strategy, adapting to technological possibilities while navigating complex geopolitical terrains. This move not only reflects the evolving nature of global conflict scenarios but also reiterates the significance of innovation and adaptability in contemporary defense narratives.
READ THE STORY: TFIGlobal
Resurrecting Heritage: How New Tech Saved Chernihiv's Soul
Bottom Line Up Front (BLUF): In the wake of the Russian invasion's destructive impact on Ukrainian cultural heritage, innovative technology has emerged as a saving grace. Tetiana Shyshova, a librarian deeply connected to Chernihiv's Youth Library, witnessed this first-hand. When Russian warplanes destroyed the library, a cornerstone of local culture and identity, it was Sergey Revenko's expertise in 3D scanning and photogrammetry that paved the way for accurate and efficient reconstruction, preserving the essence of Ukrainian identity against cultural erasure.
Analyst Comments: The devastation experienced by the people of Chernihiv, particularly Tetiana Shyshova, goes beyond physical destruction; it's an assault on their cultural identity. The Youth Library wasn't merely a repository of books but a symbol of community, history, and Ukrainian spirit. Its bombing is part of a broader strategy by Russian forces to undermine Ukrainian sovereignty by obliterating its unique cultural landmarks. This psychological warfare, intending to demoralize and erase national identity, has been combated with the unexpected weapon of technology. Sergey Revenko's arrival and his technological prowess marked a turning point. Utilizing photogrammetry and 3D scanning, he created a precise digital blueprint of the bombed library. This method isn't just about preservation; it's a defiance against cultural annihilation, ensuring that no act of destruction can completely erase what's fundamentally intrinsic to Ukrainian heritage.
FROM THE MEDIA: The story of Chernihiv's Youth Library is a testament to resilience in the face of cultural warfare. As Russian forces target symbols of Ukrainian identity, technology has emerged as an unexpected shield, safeguarding heritage and history. The efforts of individuals like Tetiana Shyshova and Sergey Revenko illuminate a crucial path forward: coupling cultural preservation with technological innovation. This synergy doesn't just offer a practical solution for restoration; it symbolizes a robust counterstrike in the defense of cultural identity, inspiring a nation under attack to hold steadfast to its roots. As this technology continues to evolve, it will undoubtedly serve as a beacon of hope and a tool of resistance for many other cultures facing similar threats around the world.
READ THE STORY: The Record
Space Force's Key Programs Face Delivery Delays Beyond 2023
Bottom Line Up Front (BLUF): Despite the U.S. Space Force's intensified efforts and acquisition reforms, three crucial programs — Next Generation Operational Control Segment (OCX), Advanced Extremely High Frequency (AEHF) system, and Military GPS User Equipment (MGUE) — are set to miss their 2023 delivery targets. Persistent technical and integration challenges have led to additional delays, pushing expected completion to mid-2024 or later.
Analyst Comments: The Space Force's inability to adhere to its initial timelines for pivotal programs such as OCX, ATLAS, and MGUE underscores systemic issues in large-scale defense acquisition projects. The recurring pattern of delays reveals a complex interplay of technical setbacks, bureaucratic hurdles, and perhaps underestimations of project scope and challenges, all of which contribute to schedule slippages. These postponements, notably with OCX's next-gen control systems and ATLAS's essential space command-and-control functionality, not only impede the U.S. military's operational capabilities but also may affect strategic positioning in an increasingly competitive space domain.
FROM THE MEDIA: The U.S. Space Force confronts a critical juncture as it misses 2023 delivery targets for key space defense programs, each fraught with their unique complexities and historical baggage. The OCX, ATLAS, and MGUE programs epitomize the challenges of ambitious technological leaps meeting the reality of intricate development work. While current strategies involve intensified oversight and internal restructuring, the broader implications necessitate a paradigm shift in the acquisition, evident in the emerging preference for more manageable, compartmentalized projects. As the Space Force grapples with these delayed timelines, the balance between maintaining cutting-edge technological advancement and the pragmatic execution of contract deliverables will be pivotal in shaping its future operational readiness and strategic capability.
READ THE STORY: C4ISRNET
Zero Trust Compromised: Nation-State Hackers Target Email Systems via Roundcube Flaw
Bottom Line Up Front (BLUF): On October 11, 2023, cybersecurity circles identified a severe breach orchestrated by Winter Vivern, a group aligned with Belarusian and Russian interests, exploiting a fresh zero-day vulnerability in Roundcube's webmail software. This exploitation, officially recognized as CVE-2023-5631, involves a pernicious form of stored cross-site scripting (XSS) that permits the stealthy injection and execution of malicious JavaScript code, compromising email confidentiality across several nations.
Analyst Comments: Winter Vivern, recognized also by the tags TA473 and UAC-0114, is an adversarial group whose actions often align with Belarus and Russia. They've been tied to recent cyber-attacks against nations like Ukraine, Poland, India, and various government bodies across Europe. This group exploited another vulnerability in Roundcube just months ago in August and September. Their exploitation method begins with a phishing message that deploys a Base64-encoded payload, which then exploits the XSS flaw, allowing them to inject and execute a JavaScript code without the user's manual intervention. The end game for this code execution is to exfiltrate email messages to their control servers. Notably, their toolkit might seem less sophisticated, but their consistency in attacks, particularly via phishing campaigns, makes them a significant threat, especially to European governments.
FROM THE MEDIA: The revelation of Winter Vivern's exploitation of a zero-day vulnerability in Roundcube webmail software underscores the ever-evolving threat landscape in cybersecurity. These incidents highlight the urgent need for continuous vigilance, rapid response to identified vulnerabilities, and robust cybersecurity strategies, particularly for entities with internet-facing services vulnerable to such sophisticated attack vectors. This event also serves as a reminder for organizations to expedite the application of security patches and maintain updated systems to mitigate potential breaches. The incident calls for a unified approach to cybersecurity, reinforcing defenses across public and private sectors to thwart such transnational cyber threats effectively.
READ THE STORY: THN
SpaceX Secures Launch: Canada's MDA Charts Course for Advanced Earth Monitoring
Bottom Line Up Front (BLUF): MDA Ltd has chosen SpaceX for the launch of its CHORUS satellite constellation, aiming to enhance Earth observation capabilities. Set for the fourth quarter of 2025, the deployment from Florida signifies MDA's continued confidence in SpaceX, reflecting their successful past collaboration.
Analyst Comments: This development marks a significant step for MDA in cementing its position within the space technology sector, particularly in Earth observation. The decision to employ SpaceX's Falcon 9 rocket highlights the continued reliability and trust in SpaceX's technology and launch services. This collaboration isn't just a business transaction but a strategic alignment between two entities that have previously worked together, showcasing SpaceX's growing influence and reliability in the commercial spaceflight sector. MDA's move comes at a time when advancements in Earth observation satellites are more crucial than ever for a range of applications, from climate monitoring to national security. By pushing for the CHORUS satellite constellation, MDA is setting the stage for enhanced global monitoring capabilities.
FROM THE MEDIA: MDA's engagement with SpaceX for the CHORUS satellite constellation's deployment is a testament to both companies' growth and reliability in the evolving space sector. The mission, scheduled for Q4 2025, marks a significant advancement in Earth observation technology and reaffirms the importance of commercial partnerships in pioneering space technology and exploration. With this initiative, MDA not only aims to expand its imprint in space technology but also to contribute significantly to global monitoring efforts, harnessing SpaceX's proven expertise in spacecraft launches.
READ THE STORY: Reuters
YoroTrooper: Emerging Cyber Threat from Kazakhstan
Bottom Line Up Front (BLUF): Hackers, suspected to be based in Kazakhstan, have been orchestrating a cyber-espionage campaign against various members of the Commonwealth of Independent States (CIS). Identified as YoroTrooper, the group has displayed a pattern of attacks, language use, and currency preferences leading experts to associate them with Kazakhstan.
Analyst Comments: YoroTrooper, first documented in March 2023 and active since at least June 2022, represents a calculated threat within cyber espionage, targeting various CIS countries. Their tactics include a blend of commodity and custom-programmed malware, designed for stealth and efficiency. By creating a facade of operating from Azerbaijan, they've further clouded their origins and intentions. Their primary strategy involves spear-phishing campaigns to implant malware or direct victims to malicious sites for credential harvesting. The group’s evasive maneuvers in response to public disclosures demonstrate adaptability. They've upgraded their arsenal from widely available malware to custom tools coded in Python, PowerShell, Golang, and Rust. This progression not only signifies a tactical evolution but also indicates the possibility of substantial backing, potentially from a state entity. YoroTrooper's activities extend beyond simple attacks. They monitor Kazakhstan's state-owned email service for vulnerabilities and convert local currency to Bitcoin for their operational expenses, pointing to a well-organized financial strategy.
FROM THE MEDIA: YoroTrooper represents a significant cybersecurity threat, particularly to CIS nations, given their successful espionage despite relatively unsophisticated cyber capabilities. Their operational adjustments in response to external disclosures demonstrate a commitment to their espionage objectives. The group's activities, especially their focus on government entities, suggest they may be driven by broader political or state-directed goals, making them a critical concern for both regional and international cybersecurity efforts.
READ THE STORY: The Record // THN
Russian Spacewalkers Deploy Innovative Student Satellite with Solar Sails
Bottom Line Up Front (BLUF): On October 26, 2023, Russian cosmonauts Oleg Kononenko and Nikolay Chub successfully launched the student-designed satellite "Parus-MGTU" from the International Space Station during a spacewalk. This significant event marks a step forward in experimental space technology, focusing on the motion of solar sails, a technique that could revolutionize space travel by using sunlight for propulsion.
Analyst Comments: The successful launch of the "Parus-MGTU" satellite is a monumental achievement, emblematic of the impactful collaboration between academia and the scientific community, particularly highlighting the role of Bauman Moscow State Technical University students. This initiative marks a significant stride in space technology, with the solar sails experiment poised to pioneer future space missions by minimizing dependence on conventional fuels and thereby revolutionizing space exploration economics. Furthermore, the cosmonauts' adept response to the emergent need for repairs, specifically within the “Nayka” module, illustrates the ongoing challenges and requisite versatility demanded in space station operations, ensuring both human safety and equipment functionality. The initiation of the “Napor-MiniRSA” radar experiment broadened the scope of space-based research, emphasizing the critical domains of environmental surveillance, disaster response, and resource management.
FROM THE MEDIA: The deployment of the “Parus-MGTU” satellite during a spacewalk by Russian cosmonauts marks a significant advancement in space technology experimentation, particularly in harnessing sunlight for propulsion. Beyond the successful launch, the mission involved critical repair work on the ISS and initiated the “Napor-MiniRSA” radar experiment, underlining the multifaceted nature of space missions. These developments collectively contribute to the broader goals of scientific progress, resource management, and sustainable practices in space exploration. As the cosmonauts continue their work, the mission's achievements reaffirm the importance of international collaboration and innovation in advancing our capabilities in space.
READ THE STORY: Frontier India
Grammarly Strengthens User Security: Fixes Login Vulnerabilities
Bottom Line Up Front (BLUF): Grammarly has swiftly remedied security flaws in its social sign-in process after Salt Security identified and reported vulnerabilities. The prompt action prevented any account compromises, reaffirming Grammarly's commitment to user data protection and cybersecurity collaboration.
Analyst Comments: Upon receiving alerts from Salt Security, Grammarly immediately addressed vulnerabilities within its OAuth implementation for social sign-ins. These flaws, common in services using OAuth for platforms like Facebook or Google, could have enabled attackers to manipulate authentication tokens and access user accounts. Grammarly's engineering team's quick response highlights its effective incident readiness and robust security protocols. This issue, part of a broader concern with OAuth-dependent services, pinpoints the risks associated with complex authentication systems, especially when third-party platforms are involved. The 'Pass-The-Token' attack method exploited by these vulnerabilities emphasizes the need for rigorous token verification protocols.
FROM THE MEDIA: Grammarly's proactive approach in rectifying the sign-in vulnerabilities, before any exploitation could occur, sets a precedent in cybersecurity responsiveness. It also underscores the necessity for ongoing diligence among companies using OAuth, or similar protocols, for user sign-ins. Collaboration with cybersecurity researchers, as well as maintaining transparency with users, forms a crucial layer in defending against potential cyber threats and ensuring user data integrity. The incident illustrates the importance of not just robust initial system design, but also continuous monitoring and improvement of security measures, especially in an era where cyber threats are increasingly sophisticated.
READ THE STORY: The Record
Tortoiseshell Escalates Cyber Aggression with IMAPLoader Malware Attacks
Bottom Line Up Front (BLUF): The Iranian hacker group, Tortoiseshell, has intensified its cyber warfare tactics, launching a sophisticated malware strain, IMAPLoader, targeting various industries. This development, noted between 2022 and 2023, marks a concerning evolution in the threat actor's capabilities, necessitating heightened cybersecurity vigilance globally.
Analyst Comments: Tortoiseshell's activities have become increasingly aggressive and sophisticated, with the deployment of the IMAPLoader malware, a .NET-based malicious software capable of advanced system fingerprinting and payload downloads. It leverages compromised email functionality for command-and-control (C2) purposes, signifying a strategic shift in the group's modus operandi. The group, associated with the Islamic Revolutionary Guard Corps (IRGC), historically focused on strategic website compromises (watering hole attacks) and has recently expanded its targets, notably within maritime, shipping, logistics, and even the travel and hospitality sectors in the Mediterranean and Europe. Its connection with the IRGC highlights potential state-sponsored cyber warfare intentions, increasing the geopolitical sensitivity of these cyber attacks.
FROM THE MEDIA: The emergence of IMAPLoader malware underlines Tortoiseshell's growing cyber threat. The group's evolving tactics, techniques, and procedures (TTPs) show an increased risk level, particularly for industries and sectors within their focus areas. This situation calls for enhanced collaborative defense strategies, comprehensive threat intelligence sharing, and fortified cybersecurity protocols to mitigate the threats posed by such state-aligned actors. The international cybersecurity community must remain vigilant and proactive in countering the risks associated with Tortoiseshell and similar entities.
READ THE STORY: THN
Data Breach Alert: Seiko Reveals Impact of Ransomware Attack on Customer and Employee Information
Bottom Line Up Front (BLUF): Japanese watchmaker Seiko has disclosed that a ransomware attack it suffered earlier this year led to the compromise of approximately 60,000 pieces of personal data, affecting customers, employees, business partners, and job applicants. While Seiko has taken steps to respond to the breach and is notifying affected parties, this incident underscores the persistent threat of ransomware attacks targeting organizations globally.
Analyst Comments: Seiko's revelation about the ransomware attack sheds light on the significant impact of such cyber incidents on businesses and individuals. The attack, attributed to the Black Cat cybercrime group (also known as AlphV), underscores the importance of robust cybersecurity measures to safeguard sensitive data. The compromised data includes customer information, although credit card details remain secure. Moreover, contact information of business counterparts involved in transactions with Seiko and job applicant details, including names, addresses, phone numbers, email addresses, and educational backgrounds, have been exposed. Current and former employees' information, such as names and email addresses, was also affected.
FROM THE MEDIA: The ransomware attack on Seiko resulted in the compromise of 60,000 personal data items belonging to customers, employees, partners, and job applicants. The incident serves as a reminder of the ongoing threat posed by cybercriminals, highlighting the importance of cybersecurity vigilance and readiness. Seiko's commitment to addressing the breach responsibly demonstrates the critical role of prompt incident response in mitigating the impact of such cyberattacks. Organizational preparedness, cybersecurity best practices, and collaborative efforts are essential in safeguarding sensitive data and protecting against ransomware threats.
READ THE STORY: The Record
Urgent Patch Required: Severe Flaw Discovered in NextGen's Mirth Connect
Bottom Line Up Front (BLUF): Users of NextGen Healthcare's Mirth Connect, widely utilized in the healthcare sector for data integration, face an urgent security threat due to a newly discovered unauthenticated remote code execution vulnerability, tracked as CVE-2023-43208. The flaw, addressed in the recently released version 4.4.1, requires immediate attention and patching, as it poses a severe risk of unauthorized access and potential compromise of sensitive healthcare data.
Analyst Comments: The vulnerability within Mirth Connect represents a critical security flaw, primarily because of its ease of exploitation and the sensitive nature of the data the platform handles. Dubbed the "Swiss Army knife of healthcare integration," Mirth Connect's widespread use makes this vulnerability particularly concerning, potentially impacting numerous healthcare systems and the confidentiality of patient data. This flaw is a patch bypass for the earlier CVE-2023-37679, which itself was a critical remote command execution vulnerability. It signals potential oversights in the cybersecurity approaches adopted during the software's development and patch management processes, highlighting a need for comprehensive vulnerability assessments and continuous monitoring of patches for effectiveness.
FROM THE MEDIA: The discovery of a severe security flaw in NextGen Healthcare's Mirth Connect underscores the persistent cybersecurity challenges in the healthcare industry. This critical vulnerability, CVE-2023-43208, allows potential unauthorized remote code execution, putting sensitive data at risk. Immediate updating to Mirth Connect version 4.4.1 is essential to safeguard healthcare data and system integrity. The situation calls for enhanced security protocols, including regular software updates and proactive cybersecurity measures, to protect against evolving cyber threats. The healthcare sector, given its sensitivity, must prioritize such actions to defend against potential data breaches and system compromises.
READ THE STORY: THN
Extended Cyber Intrusion in Philadelphia Government Emails Exposes Health Data
Bottom Line Up Front (BLUF): Hackers infiltrated the Philadelphia city government's email systems, sustaining unauthorized access for three months and potentially compromising residents' protected health information. The city, despite noticing suspicious activities, experienced delays in responding and has only recently begun notifying affected individuals, highlighting a critical lapse in its cybersecurity measures.
Analyst Comments: The cyber intrusion into Philadelphia's email systems underscores a growing trend of cyberattacks targeting governmental digital infrastructure, reflecting potential vulnerabilities within the city’s cybersecurity framework. The hackers' prolonged access from May 26 to July 28 raises significant concerns, primarily since the compromised emails contained protected health information, a category of data that requires utmost security due to its sensitive nature. This incident, unfortunately, is not isolated. It adds to the city's troubled cybersecurity history, evidenced by two significant breaches in 2020 affecting tens of thousands of residents. The recurrence of these issues suggests potential gaps in the city's cyber defenses, especially concerning timely detection, response, and public communication following the incidents.
FROM THE MEDIA: The cyber breach in Philadelphia's government email system, leading to potential exposure of residents' health information, is a stark reminder of the escalating cyber threats facing public institutions. This event, amid previous incidents, signals the urgent need for strengthened cybersecurity protocols within public systems. The city's immediate corrective steps and future preventative strategies will be pivotal in restoring public trust and safeguarding sensitive resident information against the evolving landscape of cyber threats. Comprehensive approaches to tackle such issues should include timely public communication, robust protective measures, and an unwavering commitment to continuous cybersecurity improvements.
READ THE STORY: The Record
Items of interest
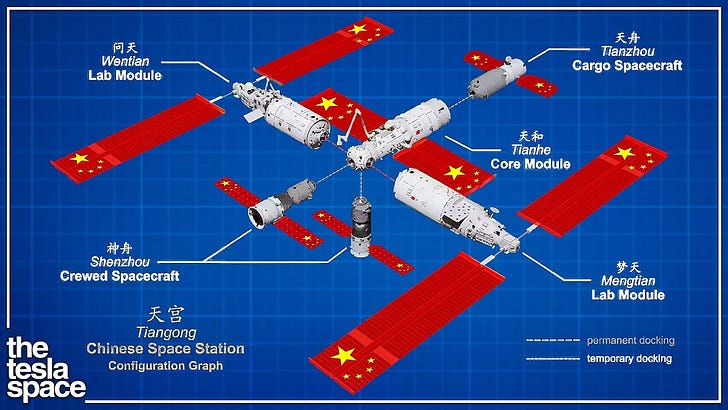
China's Latest Space Endeavor: Shenzhou-17 Blasts Off
Bottom Line Up Front (BLUF): In an ambitious step forward in its space program, China has launched Shenzhou-17, manned by its youngest crew ever, from the Jiuquan launch site. This mission, part of China's goal to establish a significant presence in space exploration, will involve maintenance, scientific experiments, and a handover from the previous crew, showcasing China's growing expertise and strategic advancements in extraterrestrial endeavors.
Analyst Comments: China's space program takes a monumental leap with the successful launch of Shenzhou-17, a mission that underscores the country's technological prowess and commitment to its long-term space objectives. The launch, characterized by national pride and witnessed by hundreds of supporters, propels a crew with the youngest average age, hinting at China's strategic investment in the next generation of astronauts. The mission's objectives are multifaceted, encompassing both maintenance and scientific exploration. Highlighting the pragmatic aspects of space habitation, the crew will address wear and tear on the Tiangong space station, specifically repairing minor damages caused by space debris, an inevitable challenge of space exploration. These practical operations are crucial for the sustainability of long-duration missions and the safety of crew members.
FROM THE MEDIA: The launch of Shenzhou-17 marks a significant milestone in China's burgeoning space efforts, emphasizing not just technological achievement but also a national commitment to cultivating a younger generation of astronauts. With a blend of maintenance tasks and scientific pursuits aboard the Tiangong space station, the mission reinforces China's capability for sustained space habitation and research. This step is one among many in China's ambitious trajectory toward becoming a leading force in space exploration, with objectives extending far into the upcoming decades, reflecting its strategic, long-term approach to space conquest.
READ THE STORY: Barrons
How China Reinvented The Space Station (Video)
FROM THE MEDIA: China's space exploration journey has taken a transformative turn with the continuous development and utilization of the Tiangong space station. Through innovative missions like the recent Shenzhou-17 launch, China is not just participating in the space race but reinventing space station norms, focusing on sustainable long-term habitation, comprehensive scientific research, and fostering a new generation of young astronauts, all wrapped up in a strategic agenda that could redefine global space dynamics.
Why China Will Win The Space Race (Video)
FROM THE MEDIA: China's strategic advancements in space exploration, exemplified by its recent Shenzhou-17 mission to the Tiangong space station, signify its trajectory toward leading the global space race. Through substantial financial investment, fostering youthful astronaut talent, prioritizing sustainable and long-term space missions, and integrating space ambitions into national identity, China is poised not only to challenge but potentially surpass traditional space powers in the coming decades.
These open-source products are reviewed by analysts at InfoDom Securities, providing possible context about current media trends related to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not endorse any third-party claims made in their original material or related links on their sites; the opinions expressed by third parties are theirs alone. For further questions, please contact InfoDom Securities at dominanceinformation@gmail.com.