Daily Drop (596): Winnti APT: ICS/OT, The AI Cold War, TSMC's Strategic Investments, Sophisticated Phishing, Microsoft: 59 patches, Charming Kitten: Backdoors, Mozilla Patches, Space Force
09-13-23
Wednesday, Sep 13, 2023 // (IG): BB // Financial Enabler PODCAST // Coffee for Bob
Space Force Needs More Cyber Operators for Weapons Systems
Analyst Comments: The Defense Department recently highlighted its cyber workforce needs and identified China and Russia as adversaries in its cyber strategy. The Pentagon's strategy aligns with the White House's national cyber strategy, emphasizing the importance of weapons security. Schiess stressed the importance of integrating cybersecurity during the development of new systems by the Space Systems Command. The command is also exploring the roles of space, intelligence, and cyber operators to determine if they can perform similar tasks.
FROM THE MEDIA: The U.S. Space Operations Command has expressed concerns about the security of its weapons systems due to the interconnected nature of these platforms. Maj. Gen. Douglas Schiess, the commander of U.S. Space Command’s Combined Force Space Component Command, emphasized the need for cyber systems to be ready and secure at all times. While the command has seen growth in intel and cyber since the inception of the Space Force in 2019, there is a need for more cyber operators, especially on protected satellite communications systems like Advanced HF, Milstar, and GPS. The Defense Department recently highlighted its cyber workforce needs and identified China and Russia as adversaries in its cyber strategy. Schiess stressed the importance of integrating cybersecurity during the development of new systems by the Space Systems Command. The command is also exploring the roles of space, intelligence, and cyber operators to determine if they can perform similar functions.
READ THE STORY: Defense One
Winnti APT Compromises National Grid of Neighboring Nation
Analyst Comments: During the breach, the ShadowPad Trojan disguised itself as VMware program files and directories. Once established, it deployed additional tools, including a keylogger and a tool that decrypted encrypted code payloads. Symantec identified a variant of ShadowPad in this attack, which had a direct connection to the previous attack on India. Both attacks used the same hardcoded remote command-and-control server. While Symantec hasn't definitively linked the two attacks, the shared infrastructure suggests a potential connection. Redfly, potentially the same group that targeted India, seems to prioritize state-level attacks, opting for targets with significant intelligence value over commercial entities. While the Redfly intrusion did not result in any disruptions, it's part of a growing trend of attacks on critical national infrastructure. China is not the only nation known for such activities; Russia and the US have also been implicated in past infrastructure attacks.
FROM THE MEDIA: China is once again under suspicion for cyber espionage activities, this time involving the power grid of a neighboring Asian nation. Espionage software believed to be developed by China was detected within the power grid of an undisclosed Asian country. The malware, known as the ShadowPad Trojan, was identified by Symantec's Threat Hunter Team. The team, named Redfly, reportedly infiltrated the national grid, stole credentials, installed additional malware, and moved across multiple systems on the infected network, maintaining access for six months. This isn't the first time the ShadowPad malware has been in the spotlight. It was previously used, presumably by a Beijing-backed group, to target the Indian power grid near the China-India border. In that instance, the attackers exploited vulnerable internet-connected devices, such as IP cameras and DVRs, to deploy the malware. The recent attack on the unnamed Asian nation's grid began with a single compromised computer.
READ THE STORY: DarkReading // The Register
Microsoft Addresses Actively Exploited Zero-Day Vulnerabilities
Analyst Comments: The release of these patches by Microsoft underscores the ever-present and evolving threats in the digital realm. It is imperative for both organizations and individual users to stay vigilant and prioritize such updates to fortify their systems against potential breaches. The proactive approach by tech giants like Microsoft, in identifying and addressing vulnerabilities, is commendable. However, the onus also lies on users to ensure they are leveraging these security measures by regularly updating their software.
FROM THE MEDIA: Microsoft has swiftly responded to the cybersecurity landscape's evolving threats by releasing patches for 59 vulnerabilities, two of which are critical zero-days that have been actively exploited. These vulnerabilities span across Microsoft's vast product portfolio. The most notable among these are CVE-2023-36761, an information disclosure vulnerability in Microsoft Word, and CVE-2023-36802, an elevation of privilege vulnerability in the Microsoft Streaming Service Proxy. The former can be exploited even by merely previewing a malicious Word document, leading to the potential disclosure of NTLM hashes. The latter provides attackers with SYSTEM privileges on the compromised system. While the specifics surrounding the exploitation and the threat actors remain undisclosed, the vulnerabilities serve as a stark reminder of the sophisticated techniques attackers employ.
READ THE STORY: THN
The AI Cold War: Alexandr Wang on the US, China, and the Future of Warfare
Analyst Comments: Wang's insights underscore the pivotal role AI is poised to play in future geopolitical dynamics. His concerns about the covert nature of AI in warfare are particularly alarming, suggesting a future where conflicts could escalate without clear attribution or understanding. The juxtaposition of the US and China in the AI race offers a sobering perspective on the challenges and opportunities both nations face. While the US boasts technological superiority, China's approach to data and its integration of AI into its military apparatus could tilt the balance. Wang's call for American technologists to rally behind the cause of ensuring US military and economic leadership is both a plea and a warning. The "tech cold war" he alludes to is not just about technological supremacy but also about preserving democratic values in the face of emerging global threats.
FROM THE MEDIA: In a recent interview with the Financial Times, Alexandr Wang, co-founder of Scale AI, delved into the rapidly evolving landscape of artificial intelligence (AI) in warfare. Wang's 2018 visit to China exposed him to the burgeoning "tech cold war", prompting him to pivot his company's focus towards national security. Established in 2016, Scale AI initially aimed at labeling data for AI tools, primarily serving autonomous vehicle companies. However, by 2021, the company's valuation soared to $7.3bn, and its clientele expanded to include financial technology firms and other entities building AI models. Wang emphasized the paramount importance of AI in modern warfare, suggesting that its integration could redefine power dynamics on the global stage. He highlighted the covert nature of AI, contrasting it with the overt visibility of nuclear technology, and expressed concerns about its potential misuse, especially by nations with different governance structures like China and Russia.
READ THE STORY: FT
Suspected Iranian Hackers Target Brazil, Israel, and UAE with New Malware
Analyst Comments: The discovery of the "Sponsor" backdoor highlights the evolving sophistication of cyber threats and the continuous efforts by nation-state actors to exploit vulnerabilities for espionage or other malicious intents. The fact that the victims were "opportunistic" suggests a broader, more indiscriminate approach to targeting, which could mean a higher risk for organizations worldwide. The ongoing cyber tensions between countries like Israel and Iran further complicate the landscape. Organizations must remain vigilant, ensuring that their systems are regularly updated and patched, especially when vulnerabilities are publicly disclosed.
FROM THE MEDIA: Researchers have identified a new backdoor malware, named "Sponsor", being used by the hacker group Ballistic Bobcat, also known as Charming Kitten. This group, believed to be backed by Iran, has targeted organizations in Brazil, Israel, and the United Arab Emirates. The attacks occurred between March 2021 and June 2022, impacting at least 34 victims, predominantly in Israel. The victims ranged from a medical cooperative and health insurance operator in Brazil, an unidentified organization in the UAE, to various media, engineering, automotive, and financial companies in Israel. Interestingly, the compromised organizations were not meticulously chosen but were "opportunistic victims" that had an unpatched vulnerability in Microsoft Exchange, enabling remote code execution. This vulnerability had previously been flagged by cybersecurity agencies from Australia, the U.K., and the U.S., warning of its exploitation by Iranian state-sponsored actors.
READ THE STORY: The Record
TSMC Acquires Stake in Intel's IMS and Plans Investment in Arm's IPO
Analyst Comments: TSMC's recent investments underscore its strategic positioning in the semiconductor industry. By acquiring a stake in IMS, TSMC not only secures access to cutting-edge technology but also strengthens its ties with a key player in the chip manufacturing process. The investment in Arm's IPO further solidifies TSMC's commitment to Arm-based chip designs, which dominate various tech sectors, from mobile phones to servers. Intel's decision to divest from IMS and the introduction of Thunderbolt 5 indicates its efforts to diversify and enhance its product offerings.
FROM THE MEDIA: Taiwan Semiconductor Manufacturing Company (TSMC) has recently made significant financial moves in the semiconductor industry. The company acquired a 10% stake in Intel's IMS Nanofabrication for $430 million and has also announced intentions to invest $100 million in Arm's upcoming initial public offering (IPO). This acquisition comes shortly after Intel sold a 20% stake of IMS to Bain Capital, valuing IMS at around $4.3 billion. IMS, based in Vienna, specializes in the production of advanced semiconductors, particularly in the development of multi-beam mask writing tools essential for extreme ultraviolet lithography (EUV). Intel's association with IMS traces back to 2009, and its recent divestments aim to provide IMS with more autonomy, making it more appealing to potential clients. TSMC has been utilizing IMS's technology since 2012, and this investment is seen as a move to foster deeper industry collaboration.
READ THE STORY: The Register
Mozilla Patches Critical Zero-Day Exploit in Firefox and Thunderbird
Analyst Comments: The flaw has been patched in multiple versions of Firefox and Thunderbird. Google has also confirmed the existence of an exploit for CVE-2023-4863 in the wild. Last week, Apple updated its software to address two actively exploited vulnerabilities, which were reportedly used in a zero-click iMessage exploit chain named BLASTPASS to deploy the Pegasus spyware on fully patched iPhones running iOS 16.6. The exact details of the exploitation of these vulnerabilities remain undisclosed, but it's believed that they are being used to target high-risk individuals, including activists, dissidents, and journalists.
FROM THE MEDIA: Mozilla has released security updates to address a critical zero-day vulnerability in its Firefox and Thunderbird applications. This vulnerability, which has been actively exploited in the wild, was fixed by Google in its Chrome browser just a day prior. The vulnerability, identified as CVE-2023-4863, is a heap buffer overflow flaw in the WebP image format. If exploited, it can lead to arbitrary code execution when a maliciously crafted image is processed. Mozilla's advisory warns that opening such a malicious WebP image could lead to a heap buffer overflow. The National Vulnerability Database (NVD) further describes the flaw as allowing a remote attacker to perform an out-of-bounds memory write via a specially crafted HTML page. Apple Security Engineering and Architecture (SEAR) and the Citizen Lab at the University of Toronto's Munk School reported this security issue.
READ THE STORY: THN
Agent Tesla, OriginBotnet, and RedLine Clipper Deployed to Harvest Sensitive Information
Analyst Comments: This phishing campaign showcases the evolving sophistication of cyber threats. By bundling three distinct malware strains, attackers can extract a wide range of information from compromised systems, maximizing their potential gains. The use of a blurred image and counterfeit reCAPTCHA demonstrates the lengths to which cybercriminals will go to deceive their targets. The loader's technique of binary padding, which increases the file size to evade security software detection, further underscores the advanced nature of this attack. The introduction of OriginBotnet, a new malware with capabilities similar to the previously identified OriginLogger, suggests that the same threat actor might be behind both. This multi-stage attack, starting from a malicious Word document and culminating in the execution of multiple malware payloads, highlights the need for robust cybersecurity measures and user awareness.
FROM THE MEDIA: A new sophisticated phishing campaign has been identified, leveraging a Microsoft Word document to distribute three distinct threats: Agent Tesla, OriginBotnet, and RedLine Clipper. These threats aim to extract a broad spectrum of information from compromised Windows systems. The phishing email contains a Word document attachment, which displays a deliberately blurred image and a fake reCAPTCHA, enticing the recipient to click on it. Upon clicking, a loader is delivered from a remote server, which subsequently distributes the three malware strains. These strains are designed for various malicious activities, including keylogging, password recovery, cryptocurrency theft, and sensitive data harvesting.
READ THE STORY: THN
Items of interest
China's Exploitation Campaign Targets U.S. Military Personnel
Analyst Comments: China's strategic move to target U.S. military personnel, both current and former, underscores the nation's intent to bridge its military capability gaps by leveraging external expertise. This approach not only poses a direct threat to U.S. national security but also raises concerns about the potential dissemination of classified information and tactics. The fact that these recruitment efforts are often masked behind seemingly innocuous job offers from private companies, which are either controlled by or contract with the Chinese Communist Party, makes the situation even more alarming. It is crucial for U.S. officials and military personnel to remain vigilant and discerning about such offers, especially given the broader geopolitical tensions between the U.S. and China.
FROM THE MEDIA: China is actively targeting both current and former U.S. service members in an exploitation campaign aimed at enhancing its military capabilities, warns Gen. Charles Q. Brown Jr. This revelation was detailed in an Air Force memo, which highlighted China's push for international firms doing business with the People's Republic of China (PRC) to recruit "U.S. and NATO-trained military talent across various specialties and career fields." Gen. Brown emphasized the risks associated with such recruitment, stating that those who accept contracts with these foreign entities jeopardize national security and the safety of their fellow servicemembers. The memo also underscored the importance of safeguarding national defense information even post-retirement from the armed forces.
READ THE STORY: Fox News
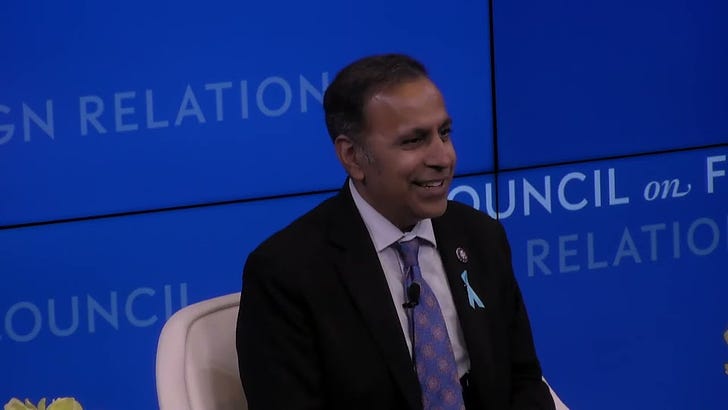
U.S. Strategic Competition With China (Video)
FROM THE MEDIA: Bipartisan leadership of the House Select Committee on the Strategic Competition Between the United States and the Chinese Communist Party, Chairman Mike Gallagher (R) and Ranking Member Raja Krishnamoorthi (D), discuss the work of the committee to ensure the United States is well positioned to counter growing competition with China, across the trade, technology, development, manufacturing, and military sectors.
US Lawmaker Says SMIC’s Huawei Chip May Violate Sanctions (Video)
FROM THE MEDIA: US Congressman Michael McCaul says China’s top chipmaker, Semiconductor Manufacturing International Corp., “warrants investigation” as the company appears to have violated US sanctions by supplying components to Huawei Technologies Co. Peter Elstrom reports on Bloomberg Television.
These open-source products are reviewed by analysts at InfoDom Securities, providing possible context about current media trends related to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not endorse any third-party claims made in their original material or related links on their sites; the opinions expressed by third parties are theirs alone. For further questions, please contact InfoDom Securities at dominanceinformation@gmail.com.