Daily Drop (592): China: BRI, DARPA: POWER Program, China & US: CHIPS, EU: LNG imports from Russia, Apple: ARM Deal, Advance Installer: Malware, Japan's iSpace, TSMC, China: EMP, APT: Aerospace Focus
09-09-23
Saturday, Sep 09, 2023 // (IG): BB // Financial Enabler PODCAST // Coffee for Bob
The Belt and Road Initiative: China's Green Vision for Global Connectivity
Analyst Comments: China's BRI is undeniably a monumental endeavor with the potential to reshape global economic landscapes. Its emphasis on green development is commendable, especially in an era where environmental concerns are paramount. However, for the BRI to be a true harbinger of sustainable development, it is imperative that ecological sustainability is ingrained at its core. This involves clear action plans, transparent environmental assessments, incentives for clean energy, and the sharing of best environmental practices. Furthermore, the initiative should pivot from a purely human-centric development model to one that also prioritizes wildlife and the broader environment. While challenges abound, the BRI's potential to be a pioneering step in global environmental governance is undeniable.
FROM THE MEDIA: The Belt and Road Initiative (BRI), conceived in 2013 by Chinese President Xi Jinping, aspires to connect the dynamic East Asian and European economic hubs. This ambitious project encompasses land and maritime infrastructure undertakings, trade agreements, and a myriad of cooperative ventures, ranging from cyberspace to the blue economy. The World Bank's projections for the BRI are optimistic, forecasting reduced travel times, augmented trade, elevated incomes, and a significant reduction in extreme poverty. China's dedication to eco-friendly development within the BRI framework is evident. They have not only entered into environmental agreements with the United Nations Environment Programme (UNEP) but also with various nations and global organizations. The 2023 white paper, "China’s Green Development in the New Era," underscores China's efforts in bolstering environmental governance among BRI partners and their investments in renewable energy projects across BRI nations.
READ THE STORY: Modern Diplomacy
Wireless Energy Transmission: A Leap Forward with DARPA's POWER Program
Analyst Comments: DARPA's POWER program is a testament to the potential of wireless energy transmission, promising not only to reshape our relationship with energy but also to revolutionize aircraft design by reducing their dependency on fuel. The program's emphasis on relay technologies underscores their significance in creating an efficient and adaptable wireless energy network. These relays are designed to combat conversion losses and enable efficient high-altitude transmission, bypassing the challenges of the turbulent lower atmosphere. The diverse technical approaches proposed by the selected teams further highlight the program's balance between leveraging existing technologies and pioneering innovative solutions. As the first phase unfolds over the next 20 months, the world will keenly watch the progress, anticipating a future where energy can be beamed across vast distances, making Tesla's dream a reality.
FROM THE MEDIA: The United States Defense Advanced Research Projects Agency (DARPA) has initiated the first phase of its Persistent Optical Wireless Energy Relay (POWER) program, aiming to revolutionize global energy distribution through airborne power transfer. This ambitious project, inspired by Nikola Tesla's century-old vision, seeks to bring about the most transformative change in energy transfer since the dawn of electrification. Leading the charge in this phase are three teams from RTX Corporation, Draper Laboratory, and BEAM Company. They are tasked with designing optical power relays that are pivotal to the program's success. Dr. Paul Jaffe, the head of the POWER program at DARPA, envisions a future where a wireless energy web can tap into diverse power sources, even from space, and deliver it to regions in dire need of energy.
READ THE STORY: Interesting Engineering
U.S. Weaponizes Semiconductor Exports Against China: Implications and Risks
Analyst Comments: The U.S.'s evolving stance on export controls, transitioning from the Obama era through the Trump administration and into the Biden administration, underscores the nation's adaptive approach to global technological challenges. While the U.S. has effectively weaponized economic interdependence, it's imperative to transition from reactive measures to a well-defined strategy. The balance between national security and global economic stability is delicate, and the U.S. must tread carefully to ensure that its policies don't inadvertently destabilize the very global systems it seeks to protect.
FROM THE MEDIA: In a strategic move against China's military ambitions, the Biden administration, in October, imposed export controls on advanced semiconductors used for AI systems. This policy not only affects U.S. companies but also any manufacturer globally that employs specified U.S. software or technology. Kevin Wolf, who previously managed the U.S. export-control regime, highlighted that due to foreign reliance on U.S. equipment, every such chip globally is now under U.S. jurisdiction. This move has been perceived by China as an attempt by the U.S. to suppress and contain its growth, leading to speculations of a looming "Silicon Curtain." The semiconductor supply chain, once seen as a symbol of global economic interdependence, has been transformed into a tool of strategic leverage by the U.S. The long-term implications of this policy are still uncertain. While China has previously employed similar tactics, using access restrictions to its market as a diplomatic tool, the current scenario suggests a brewing tit-for-tat between the two superpowers. This could potentially escalate, jeopardizing both U.S. security and the global economy.
READ THE STORY: WSJ
EU's Energy Conundrum: Rising LNG Imports from Russia and the Quest for Renewable Alternatives
Analyst Comments: The EU's energy landscape is at a crossroads. On one hand, there's the immediate need for energy security, leading to increased imports of Russian LNG. On the other, there's a clear vision for a sustainable future, pushing for innovations like solar-generated hydrogen. The challenge lies in balancing these short-term necessities with long-term goals. The EU's increasing reliance on Russian LNG, despite political tensions and past supply cuts, underscores the complexities of energy diplomacy and the intricacies of transitioning to a renewable energy future. The exploration of solar hydrogen production, while promising, is still in its nascent stages and highlights the importance of research and innovation in shaping the future of energy in Europe.
FROM THE MEDIA: The European Union (EU) is on track to import a record volume of liquefied natural gas (LNG) from Russia this year, despite its goal to reduce dependence on Russian fossil fuels by 2027. Between January and July, there was a 40% increase in EU imports of LNG compared to the same period in 2021. Belgium and Spain emerged as significant buyers, ranking second and third behind China. This surge contrasts with the global average increase in Russian LNG imports, which stood at 6%. The cost of the LNG imported during this period amounted to €5.29 billion. Most of the Russian LNG originates from the Yamal LNG joint venture, primarily owned by the Russian company Novatek. This increasing reliance on Russian LNG raises concerns, especially given Russia's past decisions to cut piped gas supplies. However, the EU's energy commissioner, Kadri Simson, emphasizes the need to eliminate Russian gas imports while ensuring energy security.
READ THE STORY: Modern Diplomacy
Apple and Arm Forge Ahead: A Chip Partnership Beyond 2040
Analyst Comments: The renewed partnership between Apple and Arm signifies a pivotal moment in the tech industry. Apple's decision to shift from Intel to Arm-based processors has already demonstrated the potential for increased performance and energy efficiency in their devices. The long-term agreement suggests a commitment to further innovation and development in chip technology. With Arm's impending IPO and its valuation, it's evident that the company plays a crucial role in the chip industry's future. This partnership not only solidifies Apple's position in the tech world but also showcases Arm's significance in shaping the future of chip technology.
FROM THE MEDIA: Apple has entered into a new long-term agreement with Arm for chip technology, a partnership that is projected to extend beyond the year 2040. This collaboration was revealed in documents Arm submitted for its initial public offering (IPO). The anticipated price range for Arm's IPO stands at a staggering $52 billion, marking it as the most significant IPO in the U.S. for 2023. SoftBank Group, Arm's parent company, plans to sell 95.5 million American depository shares of the London-based firm at a price range between $47 and $51 each. Apple's custom-made processors, known as Apple Silicon, are built on Arm's architecture. These processors are utilized in various Apple products, including Mac computers, iPhones, and iPads. Apple began its transition from Intel CPUs to its unique Arm-based processors in June 2020. This shift has allowed Apple to have more control over the integration of its hardware and software, resulting in enhanced performance and energy efficiency.
READ THE STORY: Interesting Engineering
Advanced Installer Tool: A Double-Edged Sword in Crypto-Mining Attacks
Analyst Comments: The exploitation of the Advanced Installer tool underscores the evolving sophistication of cybercriminal tactics. By leveraging a legitimate tool, attackers can bypass traditional security measures, making detection and mitigation more challenging. The strategic targeting of industries with high GPU power computers highlights the cybercriminals' intent to maximize their gains from cryptojacking. The geographical focus on French-speaking regions suggests a well-researched and targeted campaign. Organizations and individuals must remain vigilant and ensure that they download software from trusted sources.
FROM THE MEDIA: Cybercriminals have found a new method to exploit unsuspecting users by weaponizing a legitimate Windows tool, the Advanced Installer, to drop cryptocurrency-mining malware on infected systems. This malicious activity has been traced back to November 2021. Threat actors cleverly package legitimate software installers, such as Adobe Illustrator and Autodesk 3ds Max, with harmful scripts. They then leverage the Advanced Installer's Custom Actions feature to execute these scripts. The targeted applications suggest that industries like architecture, engineering, construction, manufacturing, and entertainment are at risk. Notably, the software installers primarily use the French language, indicating that French-speaking users might be the primary targets. The strategic choice of these industries is due to their reliance on high GPU power computers, making them attractive targets for cryptojacking
READ THE STORY: THN
Japan's ispace: A Moonshot Gone Awry
Analyst Comments: The journey of ispace underscores the multifaceted challenges of space exploration in today's age. While technological strides have made space missions more accessible, the interplay of corporate culture, financial constraints, and technical hurdles can lead to significant impediments. The aspiration to venture into and understand space persists, but the path is laden with challenges that demand a harmonious amalgamation of technical acumen, financial prudence, and a conducive corporate environment.
FROM THE MEDIA: Japan's ambitious start-up, ispace, aimed to etch its name in history by landing its Hakuto-R lander on the Moon. This would have positioned Japan as the fourth nation to achieve such a feat and marked ispace as the pioneering private enterprise to do so. However, the mission concluded in disappointment with the lander crashing on the lunar surface. Delving deeper into the events leading to this failure, The Financial Times unveiled a series of internal challenges faced by the company. From a corporate culture described by some insiders as "toxic" to allegations of bullying and discrimination, the company's internal environment seemed tumultuous. Furthermore, despite the resurgence of interest in Moon missions globally, Japan's endeavors in this realm have yet to bear fruit. The investigation by the Financial Times suggests that the failure of Hakuto-R was not a mere accident but the result of months of financial, technological, and corporate turmoil within ispace. The company's financial trajectory also appeared shaky. Even though its shares soared post its initial public offering, the broader funding landscape for space ventures seems to be on a decline.
READ THE STORY: FT
TSMC Forecasts AI Chip Shortage to Persist
Analyst Comments: The ongoing chip shortage has been a significant concern for various industries, and TSMC's announcement further underscores the complexities involved in chip manufacturing. The delay isn't just about producing the silicon but also about the advanced packaging required to assemble these high-performance chips. This situation emphasizes the importance of diversifying supply chains and investing in advanced manufacturing capabilities to mitigate such bottlenecks in the future. The AI industry, in particular, which relies heavily on these high-end GPUs, will need to strategize and possibly look for alternative solutions or suppliers to ensure continuity in their operations.
FROM THE MEDIA: Taiwan Semiconductor Manufacturing Company (TSMC), the world's largest semiconductor foundry, has alerted consumers that the scarcity of Nvidia's high-end GPUs, such as the A100 and H100, will continue until the end of 2024. Contrary to assumptions, the issue isn't TSMC's inability to produce enough chips. The real challenge lies in the shortage of advanced packaging capacity, crucial for assembling the silicon components. TSMC's chairman, Mark Liu, informed Nikkei Asia that the company can currently fulfill only about 80% of the demand for its chip on wafer on substrate (CoWoS) packaging technology. This technology is pivotal for high-end chips, especially those relying on high-bandwidth memory (HBM) suitable for AI tasks. Liu anticipates this production bottleneck to be temporary, with more CoWoS capacity expected to be available in approximately 18 months. TSMC has also announced its intention to augment its advanced packaging capacity in Taiwan with a new $3 billion facility.
READ THE STORY: The Register
China's EMP Advancements: A Looming Threat to U.S. Infrastructure
Analyst Comments: The implications of China's progress in EMP weaponry are profound. The interconnected nature of U.S. systems means that an EMP attack could trigger cascading failures across various sectors. While the immediate threat to military assets is concerning, the potential disruption to civilian infrastructure, including power grids and transportation hubs, could have far-reaching economic and societal consequences. The U.S. must prioritize the development of countermeasures and strategies to mitigate this emerging threat. The intertwined nature of global systems further underscores the need for international cooperation and dialogue to address the challenges posed by EMP weapons.
FROM THE MEDIA: Chinese military researchers have made significant strides in the development and testing of electromagnetic pulse (EMP) weapons, as revealed by a recent report. These weapons, which emit radiating energy capable of damaging or destroying electronic systems, pose a potential threat to U.S. warplanes, military bases, and critical civilian infrastructure, including the electric grid. The report, titled “There’s Darkness in the Distance,” was authored by analysts L.J. Eads, Ryan Clarke, and Xiaoxu Sean Lin, who are part of the Chinese Communist Party BioThreats Initiative. Their findings suggest that China's advancements in EMP technology could disrupt both military and civilian operations, with the potential to disable everything from advanced warplanes to essential communication networks.
READ THE STORY: The Washington Times
Nation-State Hackers Target Aerospace Company: A Deep Dive
Analyst Comments: The exploitation of vulnerabilities in widely used software and hardware products, combined with tactics like using deactivated accounts, showcases the hackers' sophistication. Organizations must prioritize cybersecurity, regularly update and patch their systems, and maintain a clear data centralization strategy. Additionally, they should ensure timely deactivation and removal of outdated user accounts and continuously monitor server logs for any anomalies. Collaboration with security agencies and timely reporting of suspicious activities can further bolster defense mechanisms against such advanced threats.
FROM THE MEDIA: U.S. security agencies, including the Cybersecurity and Infrastructure Security Agency (CISA), have raised alarms about multiple nation-state hackers exploiting vulnerabilities to infiltrate an undisclosed aerospace company. The breach traces back to January, with both the FBI and U.S. Cyber Command corroborating the alert. The hackers exploited a vulnerability, CVE-2022-47966, in the Zoho ManageEngine ServiceDesk Plus application, which the aerospace company used for IT service management. This flaw allowed the attackers to remotely execute malicious code, gain full control of the company's web server, create an administrative user account, and further navigate through the organization's network. While the extent of the data breach remains uncertain due to the company's unclear data centralization and CISA's limited network coverage, another vulnerability, CVE-2022-42475, was identified. This vulnerability, affecting Fortinet devices, was exploited using the login credentials of a former contractor.
READ THE STORY: The Record
NASA's Psyche Mission: Exploring the Secrets of a Metal-Rich Asteroid
Analyst Comments: The Psyche mission stands out as a significant endeavor in space exploration. The asteroid Psyche offers a unique celestial laboratory, potentially providing an unprecedented glimpse into the building blocks of early planets. The spacecraft's journey to the asteroid will be marked by key milestones and test periods, especially for NASA's Deep Space Optical Communications (DSOC) technology. This mission is not just about reaching the asteroid but also about testing and validating new technologies that could be pivotal for future space explorations. The recent data suggesting that Psyche might be a blend of metal and silicate further amplifies the mission's scientific potential.
FROM THE MEDIA: NASA's Kennedy Space Center in Florida is in the final stages of preparation for the much-anticipated Psyche mission, scheduled to launch on October 5. This mission aims to explore the metal-rich asteroid named Psyche, using a suite of advanced scientific instruments, including a multispectral imager, magnetometer, and gamma-ray and neutron spectrometer. The spacecraft's primary objective is to gather insights about the asteroid, which could potentially be a fragment of a planetesimal's core. Such insights could revolutionize our understanding of early planet formation.
READ THE STORY: Interesting Engineering
Spyware Disguised as Telegram Apps Infects Millions on Google Play
Analyst Comments: The infiltration of spyware within popular app platforms like Google Play Store underscores the evolving sophistication of cyber threats. The use of well-known apps as a disguise for malicious activities highlights the importance of vigilance and thorough verification before downloading any application, even from reputed sources. The rapid response by Google in removing these apps is commendable, but the sheer number of downloads indicates the scale of potential compromise.
FROM THE MEDIA: A recent discovery has unveiled the presence of spyware hidden within counterfeit versions of the Telegram app on the Google Play Store. These malicious apps are designed to extract sensitive data from compromised Android devices, including names, user IDs, contacts, phone numbers, and chat messages, which are then sent to servers controlled by the attackers. Kaspersky security researcher, Igor Golovin, has identified these apps, which have been collectively downloaded millions of times before their removal by Google. The spyware operation has been dubbed "Evil Telegram" by the Russian cybersecurity firm. Notably, the fake apps employ typosquatting techniques, using package names similar to the legitimate Telegram app, to deceive users and evade detection. This revelation follows a recent disclosure by ESET about the BadBazaar malware campaign that exploited a rogue version of Telegram to gather chat backups.
READ THE STORY: THN
Grid Battery Boom: Balancing Renewable Energy Needs with Safety Concerns
Analyst Comments: The tension between the urgent need for renewable energy solutions and public safety concerns is palpable. The grid battery industry, while promising in its potential to combat climate change, faces the challenge of ensuring safety and effectively communicating these measures to the public. As the industry continues to grow, striking a balance between rapid adoption and addressing valid safety concerns will be pivotal for its widespread acceptance and success.
FROM THE MEDIA: The global push against climate change has accelerated the demand for grid battery installations, which serve as backups for renewable energy sources and can replace dirtier parts of the grid. However, as highlighted in a WIRED article by Gregory Barber, this surge is accompanied by growing public concerns, particularly regarding the potential fire risks associated with these installations. While large grid batteries generally have a commendable safety record, instances of fires, such as those in Surprise, Arizona, and Geelong, Australia, have fueled skepticism. The industry, learning from past incidents, has been proactive in enhancing safety measures, but strategies vary among manufacturers.
READ THE STORY: Wired
Items of interest
Major U.S. Financial Institution Targeted in Massive DDoS Attack
Analyst Comments: The rapid and effective response by Akamai Technologies underscores the importance of robust cybersecurity measures, especially for institutions in the financial sector. Given the critical role financial institutions play in the economy, they remain attractive targets for cybercriminals. The increasing frequency and sophistication of DDoS attacks highlight the need for continuous vigilance, advanced threat detection, and swift mitigation strategies to safeguard vital systems and data.
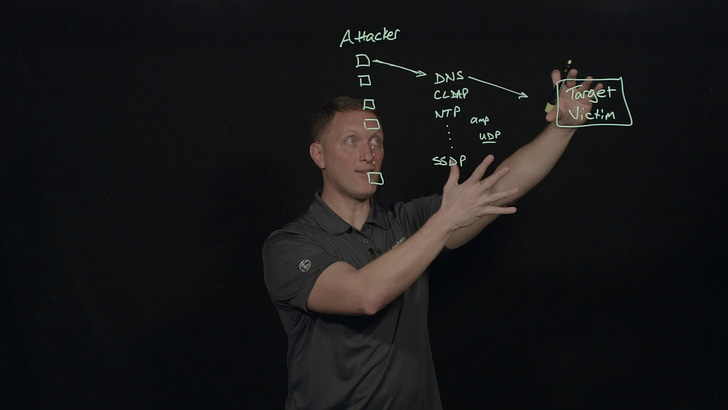
FROM THE MEDIA: A significant distributed denial-of-service (DDoS) attack aimed at a prominent American financial institution was successfully identified and mitigated by cybersecurity firm Akamai Technologies. Although the name of the targeted financial company remains undisclosed, Akamai described it as one of their "largest and most influential" clients in the financial sector. DDoS attacks work by inundating websites with excessive traffic, rendering them temporarily inaccessible to users. The attack, detected on a Tuesday, reached a peak of 633.7 gigabits of traffic per second. For context, cloud computing company Gcore has noted that DDoS attacks this year can surge up to 800 gbps. Akamai highlighted that the attack was intense but lasted less than two minutes, ensuring no disruption or harm to the victim's services.
READ THE STORY: The Record
Real Attack Stories: Asia/Pacific Financial Companies (Video)
FROM THE MEDIA: The F5 Silverline Security Operations Center (SOC) stopped another DDoS attack against several financial and high-tech companies in Asia. This attack included a multi-vector amplification attack by a large botnet controlled by the attacker and resulted in a volumetric attack that peaked at 50 Gbps. These attacks are real, and you need to have a defense against them.
Why DDoS attacks are a serious threat to media freedom (Video)
FROM THE MEDIA: Access to your favorite news website could be shut down within seconds. DDoS attacks aimed at silencing critical media are becoming more and more of a threat. The latest wave has hit several media outlets in Hungary.
These open-source products are reviewed by analysts at InfoDom Securities, providing possible context about current media trends related to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not endorse any third-party claims made in their original material or related links on their sites; the opinions expressed by third parties are theirs alone. For further questions, please contact InfoDom Securities at dominanceinformation@gmail.com.