Daily Drop (566): Sogou: Eavesdropper, Pro-Russian groups: Belarus, Pentagon launches AI competition, China-Linked Hackers, EvilProxy Phishing Kit, North Korea's Kim dismisses top general
08-10-23
Thursday, Aug 10, 2023 // (IG): BB // Financial Enabler PODCAST // Coffee for Bob
Popular Chinese-language service Sogou exposed to ‘eavesdropper,’ report says
Analyst Comments: The Sogou Input Method, utilized by over 455 million people monthly, suffered from serious security vulnerabilities that compromised user data. Citizen Lab's eight-year study of Chinese app vulnerabilities underscores the necessity for robust encryption standards, urging developers to use established protocols like Transport Layer Security (TLS) rather than devising custom encryption systems. While Sogou claims to have rectified the vulnerabilities, the practice of transmitting user data to its servers remains a concern for data security. The incident highlights broader issues of data privacy and government access to user information, especially for products with international users.
FROM THE MEDIA: A report from Citizen Lab, a human rights and global security organization, reveals vulnerabilities in the Sogou Input Method, a widely-used software for typing Chinese characters. The vulnerabilities exposed network transmissions to a "network eavesdropper," allowing real-time capture of keystrokes. Sogou's encryption system was found to have troubling weaknesses, potentially granting unauthorized access to user communications. The Chinese government's jurisdiction over the servers that receive Sogou's data raises concerns about users' data privacy, even though the vulnerabilities have reportedly been fixed.
READ THE STORY: The Record
Hackers with links to Pro-Russian groups compromised foreign embassies in Belarus, researchers say
Analyst Comments: The paper highlights the activities of the cyberespionage group "MustachedBouncer," shedding light on their sophisticated tactics in targeting foreign embassies. The group's strategic use of local ISPs and deployment of custom malware underscore their level of expertise. The collaboration between MustachedBouncer and Winter Vivern indicates a broader, coordinated effort in the realm of cyber espionage. However, the paper lacks in-depth technical details about the malware, its propagation methods, and potential mitigation strategies.
FROM THE MEDIA: A newly identified cyberespionage group known as "MustachedBouncer," operating in Belarus, has been targeting foreign embassies with the assistance of local internet service providers (ISPs). The group, active since 2014, compromised embassy staff from European, South Asian, and African countries. The group's tactics involve exploiting local ISPs using an adversary-in-the-middle attack, relying on a "lawful interception" system, and deploying custom malware named "Disco." Additionally, the group uses a separate malware framework called "NightClub" for undisclosed purposes. MustachedBouncer appears to cooperate closely with another suspected pro-Russian cyberespionage group, Winter Vivern.
READ THE STORY: CyberScoop
Pentagon launches AI competition to solicit help securing computer systems
Analyst Comments: DARPA's AI competition reflects the growing recognition of the importance of AI in addressing cybersecurity challenges. By incentivizing AI experts to create tools that enhance software security, DARPA aims to contribute to the defense against a diverse array of cyber threats. The competition's focus on creating accessible tools for identifying and mitigating vulnerabilities highlights the need for proactive measures to secure software systems. This initiative could potentially lead to innovative solutions and best practices that benefit the broader cybersecurity community.
FROM THE MEDIA: The Defense Advanced Research Projects Agency (DARPA), a Pentagon agency that funds technology innovations, has launched a two-year competition aimed at harnessing artificial intelligence to bolster cybersecurity. The competition, which begins at the Black Hat cybersecurity conference in Las Vegas, calls for participants to develop tools capable of identifying and fixing vulnerabilities in software to prevent hackers from exploiting them. A total of $18.5 million in prizes will be awarded to winners in different categories, with the competition concluding at the Def Con hacker conference in Las Vegas in August 2025. The winning tools will be released to the public to enhance global cybersecurity efforts.
READ THE STORY: NBC News
China-Linked Hackers Strike Worldwide: 17 Nations Hit in 3-Year Cyber Campaign
Analyst Comments: Recorded Future's report sheds light on a widespread and persistent cyber campaign orchestrated by a group linked to China's Ministry of State Security. The campaign's targets span multiple sectors and countries, reflecting the group's comprehensive approach. The exploitation of Log4Shell vulnerabilities and the deployment of backdoors showcase the group's technical sophistication. The multi-tiered infrastructure approach and the use of compromised infrastructure highlight the group's strategies for maintaining long-term access. The report comes in the wake of increasing concerns about state-sponsored cyber espionage and highlights the significant challenges in detecting and countering such attacks. The reported deep access of Chinese hackers to classified defense networks in Japan further underscores the urgency of addressing these threats.
FROM THE MEDIA: Hackers associated with China's Ministry of State Security (MSS) have conducted a cyber campaign spanning 17 countries in Asia, Europe, and North America from 2021 to 2023. The cybersecurity firm Recorded Future has linked these attacks to a nation-state group named RedHotel (previously TAG-22), which is also associated with other activity clusters such as Aquatic Panda and Bronze University. The group primarily targeted sectors like academia, aerospace, government, media, telecommunications, and research, with government organizations being the primary victims. The group's objectives include intelligence gathering and economic espionage, particularly focusing on COVID-19 research and technology R&D.
READ THE STORY: THN
Ukrainian official: Russian hackers change tactics from disruptive attacks
Analyst Comments: The article highlights a significant shift in the tactics of Russian hackers targeting Ukraine, moving from disruptive attacks to strategic cyber espionage. This change suggests that hackers are adapting their methods to gather valuable intelligence for military purposes. The focus on targeting military personnel's devices and key military tools demonstrates a more targeted and sophisticated approach. The Ukrainian authorities' efforts to collaborate and share threat intelligence to thwart these attacks indicate a proactive stance in countering this evolving threat landscape.
FROM THE MEDIA: Russian hackers targeting Ukraine have shifted their tactics from disruptive attacks to focused cyber espionage and data collection. The Ukrainian cybersecurity official Victor Zhora, deputy chairman of the State Service of Special Communications and Information Protection of Ukraine, reported that the Russian hackers are now concentrating on gathering data that can provide an advantage on the battlefield. The hackers are targeting Ukrainian military personnel's Android phones and attempting to spread malware targeting configuration information of key military tools. This shift in tactics is seen as an attempt to gain intelligence for military operations.
READ THE STORY: CyberScoop
New BitForge cryptocurrency wallet flaws let hackers steal crypto
Analyst Comments: The 'BitForge' vulnerabilities highlight the significant security risks associated with cryptocurrency wallets and the importance of strong encryption and security practices in the cryptocurrency space. The fact that these vulnerabilities can allow attackers to steal digital assets rapidly and without user interaction underscores the potential financial losses that users could face. The active response from some wallet providers demonstrates the importance of timely fixes and responsible disclosure. Cryptocurrency users should be aware of potential vulnerabilities in their chosen wallets, keep their software up to date, and follow best security practices to protect their digital assets from such threats.
FROM THE MEDIA: Multiple zero-day vulnerabilities known as 'BitForge' have been discovered in widely used cryptographic protocols such as GG-18, GG-20, and Lindell 17, affecting popular cryptocurrency wallet providers including Coinbase, ZenGo, and Binance. These vulnerabilities could potentially allow hackers to quickly steal digital assets stored in these wallets without user interaction. The flaws were uncovered by the Fireblocks Cryptography Research Team in May 2023 and were publicly disclosed during the BlackHat presentation. Coinbase and ZenGo have already addressed the issues, but other providers like Binance remain vulnerable.
READ THE STORY: BleepingComputer
Cybercriminals Increasingly Using EvilProxy Phishing Kit to Target Executives
Analyst Comments: The use of phishing-as-a-service (PhaaS) tools like EvilProxy highlights the growing sophistication of cybercriminal tactics, particularly in targeting high-value individuals within organizations. The inclusion of AitM phishing kits demonstrates the adaptability of threat actors in circumventing security measures like multi-factor authentication. The focus on C-level executives and individuals with financial access underscores the attackers' intent to maximize their gains. As phishing attacks become more automated and streamlined, organizations must continue to educate their users about phishing risks, implement strong security practices, and consider advanced threat detection solutions to identify and mitigate such attacks.
FROM THE MEDIA: Cybercriminals are increasingly utilizing a phishing-as-a-service (PhaaS) toolkit called EvilProxy to target high-ranking executives at prominent companies. Proofpoint has identified an ongoing hybrid campaign using EvilProxy to target Microsoft 365 user accounts, sending phishing emails to organizations worldwide between March and June 2023. This toolkit helps attackers bypass multi-factor authentication (MFA) by incorporating adversary-in-the-middle (AitM) phishing kits to steal credentials, session cookies, and one-time passwords. The attacks deliberately focus on high-profile users, such as C-level executives, and target personnel with access to financial assets or sensitive information. The compromised accounts are then monetized for financial fraud, data exfiltration, or resale.
READ THE STORY: THN
North Korea's Kim dismisses top general, calls for war preparations
Analyst Comments: The replacement of the top general and Kim Jong Un's calls for heightened war preparations, weapons production, and military drills suggest a significant shift in North Korea's military strategy. The leadership change could be aimed at infusing fresh perspectives and accelerating military modernization efforts. The focus on readiness for potential conflict indicates that North Korea is intensifying its defensive posture amid regional security concerns. The move could also be aimed at reinforcing North Korea's image of strength in negotiations and diplomacy on the international stage.
FROM THE MEDIA: North Korean leader Kim Jong Un has replaced the country's top general, Chief of the General Staff Pak Su Il, and called for increased preparations for the possibility of war, boosting weapons production, and expanding military drills. The move comes as Kim chaired a meeting of the Central Military Commission to discuss countermeasures against unspecified enemies. The report did not name the adversaries. The newly appointed General Ri Yong Gil will take over as the top general, replacing Pak Su Il. The changes in leadership and strategic direction indicate a renewed focus on military readiness and an assertive stance by North Korea.
READ THE STORY: TBS News
Interpol Busts Phishing-as-a-Service Platform '16Shop,' Leading to 3 Arrests
Analyst Comments: The takedown of the 16Shop PhaaS platform highlights the global efforts to combat cybercrime and disrupt the tools and services that enable phishing attacks. Phishing kits like those offered by 16Shop significantly lower the technical barrier for cybercriminals, enabling them to launch sophisticated attacks on a large scale. The coordinated action by law enforcement and cybersecurity firms demonstrates the importance of international collaboration in countering cyber threats. However, this incident also serves as a reminder of the ongoing challenges in combating cybercrime, as new platforms and tactics can emerge to replace those that have been taken down.
FROM THE MEDIA: Interpol has successfully dismantled a phishing-as-a-service (PhaaS) platform known as 16Shop and arrested three individuals in Indonesia and Japan who were involved in its operations. The platform specialized in selling phishing kits to cybercriminals, enabling them to launch large-scale phishing attacks targeting popular services like Apple, PayPal, American Express, Amazon, and Cash App. These attacks aimed to steal credentials and payment details from users. The operation has disrupted the activities of the PhaaS platform, resulting in the arrest of the site's administrator and the seizure of electronic items and luxury vehicles. Over 70,000 users across 43 countries are estimated to have been compromised via services offered on 16Shop.
READ THE STORY: THN
Regulators fear Russia could access Yandex taxi data from Europe, Central Asia
Analyst Comments: The situation highlights the ongoing tension between data privacy and national security concerns, especially in regions where the government may have access to user data. The case of Yandex underscores the importance of clear regulations and safeguards to protect user data from potential misuse by government entities. As governments around the world enact laws to access user data for security purposes, it becomes crucial for companies operating across borders to navigate these legal and privacy challenges while maintaining user trust. This situation also highlights the challenges faced by multinational tech companies in complying with differing data protection regulations across various countries.
FROM THE MEDIA: News has emerged that concerns are arising among users and regulators in Europe and Central Asia over the potential for the Russian security service to access data collected by Yandex's taxi service. Yandex, often referred to as "Russia's Google," operates the largest search engine in Russia and offers a ride-hailing and food delivery service under the name Yango (YandexGo) in over 20 countries. Russian law allows the security service, FSB, to access user data collected by taxi services, leading to fears about user privacy and data security. Regulators in Finland and Norway have already banned Yandex from sharing the personal data of Yango's customers with Russia. Other countries where the service operates, such as Georgia and Kazakhstan, have also launched investigations into the matter. Yandex has denied claims that the FSB would gain access to customer data outside of Russia, stating that data about trips can only be obtained by law enforcement agencies in the country where the trip was made
READ THE STORY: The Record
Disposed-of Gadgets Can Lead to Wi-Fi Network Hacks, Kaspersky Says
Analyst Comments: The report highlights a critical concern regarding the security of disposed electronic devices. Many individuals overlook the potential risks associated with discarding gadgets without properly clearing sensitive information. The accessibility of Wi-Fi network data from discarded devices can provide threat actors with a pathway to breach networks and compromise connected devices. The article underscores the importance of secure disposal practices, emphasizing the need to reset and wipe device settings, change Wi-Fi passwords, and update network settings to ensure that sensitive data is not left vulnerable.
FROM THE MEDIA: When disposing of old technology like phones, computers, printers, and smartwatches, it's crucial to clear stored Wi-Fi network information to prevent potential network attacks, as highlighted by Kaspersky. This information is often unprotected and easily accessible from discarded gadgets. Threat actors often steal Wi-Fi data from disposed of devices by identifying the device's owner and exploiting clues left behind, such as network names or device names. Even after a factory reset, they can access and steal Wi-Fi networks. Breaching a Wi-Fi network allows threat actors to compromise connected devices, leading to issues such as slower internet, leaked IP addresses, and even ISP blocking.
READ THE STORY: DARKReading
Pro-Russian hackers claim attacks on French, Dutch websites
Analyst Comments: The pro-Russian hacking group's claims of responsibility for cyberattacks on government and public services websites in France and the Netherlands underscore the ongoing cyber threats faced by European countries. The group's focus on DDoS attacks demonstrates their intent to disrupt online services and create a symbolic impact. These attacks highlight the vulnerability of government and public services to cyber threats, and the potential consequences of such disruptions, ranging from limited access to information to reputational damage.
FROM THE MEDIA: A pro-Russian hacking group known as NoName057(16) has claimed responsibility for cyberattacks on government and public services websites in France and the Netherlands. These attacks come shortly after the same group targeted Spanish and Italian government and private sector organizations with distributed denial-of-service (DDoS) attacks. The Dutch cybersecurity agency stated that the impact of these DDoS attacks has been limited and symbolic. The group targeted various Dutch websites, including the public transport website, the local bank SNS, the Groningen seaport, and the municipality of Vlardingen. In France, the hackers claimed to have targeted the country's customs service. NoName057(16) is known for its attacks on Ukraine and its allies using DDoS attacks, with disruptions causing short-lived impacts.
READ THE STORY: The Record
UK explains the likelihood of catastrophic cyberattacks — and its response plans
Analyst Comments: The publication of the National Risk Register by the British government reflects a comprehensive approach to understanding and mitigating potential catastrophic cyber risks. By outlining various scenarios and their potential impacts, the government is demonstrating a commitment to transparency, preparedness, and collaboration with businesses and organizations. The assessment underscores the complexity and interdependency of critical sectors and emphasizes the need for enhanced cybersecurity measures, resilience planning, and response capabilities. The inclusion of scenarios ranging from conventional attacks to space-based disruptions highlights the evolving nature of cyber threats and the importance of staying ahead of emerging risks.
FROM THE MEDIA: The British government has released a National Risk Register that outlines various scenarios of catastrophic cyberattacks and their potential impacts on critical sectors in the UK. The risk assessment is based on the government's internal, classified National Security Risk Assessment and covers scenarios related to cyberattacks on critical infrastructure. The assessment indicates that while the most likely risks are not the most impactful, the country remains exposed to malicious actions by hostile states, terrorists, and financially motivated criminals. The document includes scenarios involving cyberattacks on sectors such as electricity infrastructure, gas infrastructure, civil nuclear, financial networks, healthcare, transportation, telecommunications, undersea cables, drones, space, and more.
READ THE STORY: The Record
China Hacked Japan’s Sensitive Defence Networks, Claims Report
Analyst Comments: These incidents underscore the ongoing challenges posed by cyber espionage and the intensifying technological competition between nations. The hacking of Japan's defense networks by China highlights the potential for cyber attacks to compromise sensitive national security information. It also showcases the persistence and sophistication of state-sponsored hacking operations. The targeting of Russian institutions by Chinese hackers further illustrates how complex international relationships can be exploited for espionage purposes.
FROM THE MEDIA: According to a report by The Washington Post, in the fall of 2020, the Chinese military hacked into Japan's classified defense networks. Cyberspies from China's People’s Liberation Army gained deep and persistent access to Japan's sensitive computer systems, aiming to gather plans, capabilities, and assessments of military vulnerabilities. The breach prompted concerns about intelligence sharing between the Pentagon and Beijing's Defense Ministry. While Japan has been working to enhance its network security since the breach, the report suggests that its networks are still vulnerable to cyber threats from China. In a separate incident in 2022, Chinese hackers reportedly targeted Russian military research and development institutes with emails containing malware. The emails, seemingly from Russia's Ministry of Health, were actually sent by Chinese state-sponsored hackers aiming to steal sensitive military technological information.
READ THE STORY: Good Morning Kashmir
Biden orders U.S. investment restrictions on some high-tech industries in China
Analyst Comments: The executive order reflects the Biden administration's efforts to address concerns about China's technological advancements that could have national security implications. By restricting U.S. investment in certain high-tech sectors, the administration aims to curb China's progress in areas that could potentially undermine U.S. military and intelligence capabilities. However, such actions also risk escalating tensions with China and could have economic consequences. China has consistently criticized U.S. restrictions on its technological development, and this order is likely to strain diplomatic relations further.
FROM THE MEDIA: President Joe Biden has signed an executive order that restricts U.S. investment in certain high-tech industries in China, including quantum computing, artificial intelligence, and advanced semiconductors. The executive order, prompted by growing tensions with China, cites China's "rapid advancement" in critical technologies and products that have military, intelligence, surveillance, or cyber-enabled applications. The order aims to address the perceived national security threat posed by China's technological advancements in these areas and directs the Treasury secretary to collaborate with other relevant agencies to issue regulations on restricted transactions and reporting with China. The Chinese Commerce Ministry expressed concern about the order, stating it deviates from market economy principles and undermines international trade order.
READ THE STORY: NBC News
Items of interest
Module extraction and DLL hijacking detection via single or multiple memory dumps
Analyst Comments: The paper addresses a significant challenge in digital forensics by enhancing memory forensics techniques on Windows systems. The development of Modex and Intermodex tools addresses the limitations of existing methods, providing a more comprehensive extraction of modules from memory dumps. By aggregating content from multiple processes, these tools offer a more accurate representation of module functionality, aiding forensic analysts in their investigations. The detection of DLL hijacking attacks is an important feature of the tools. This demonstrates the practical application of the tools in identifying security threats that exploit Windows mechanisms. However, the paper does not provide extensive details about the technical implementation of the tools, potential limitations, or real-world case studies showcasing their effectiveness.
FROM THE MEDIA: The research paper introduces two tools, Modex and Intermodex, developed on the Volatility 3 framework, aimed at enhancing memory forensics on Windows systems. Memory forensics involves analyzing memory dumps to investigate incidents where no activity traces are written to disk. The tools focus on extracting 64-bit modules from memory dumps in a comprehensive manner. These modules are critical for understanding system states, processes, and potential threats, such as DLL hijacking attacks, which involve loading malicious DLLs instead of benign ones. The paper outlines the challenges in extracting modules due to shared object files and highlights the limitations of existing methods. Modex and Intermodex address these limitations by aggregating the content of modules loaded by multiple processes in the same or different memory dumps. They aim to provide forensic analysts with a more complete view of module contents, aiding in identifying potential threats and malicious activities.
READ THE STORY: Science Direct
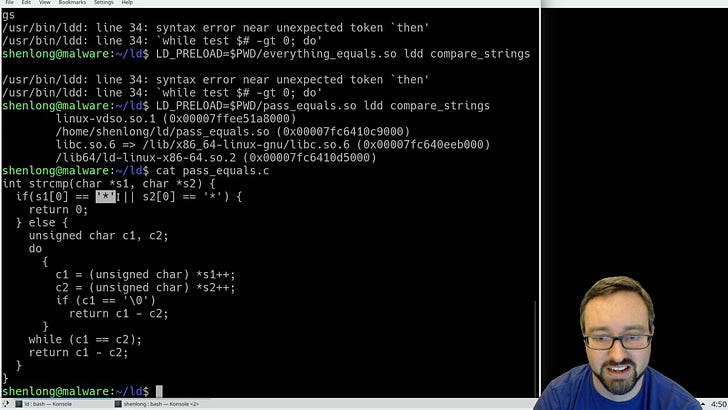
DLL injection for Linux: LD_PRELOAD Demo (Video)
FROM THE MEDIA: This video is part of the computer/information/cyber security and ethical hacking lecture series; by Z. Cliffe Schreuders at Leeds Beckett University.
SO Shared Object Files in Linux, (library modules) (Video)
FROM THE MEDIA: In this video, we look at how we can manage library modules and shared object libraries in Linux. We take the example that we may want to test a develop a new version of modules before distributing it to others. We can set up a variable LD_LIBRARY_PATH to point to our test location and this will only affect us and no one else. Main system users will collect the modules from the directories listed in the file /etc/ld.so.conf. If we edit this file to include new directories then we will need to run the command ldconfig.
These open-source products are reviewed by analysts at InfoDom Securities, providing possible context about current media trends related to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not endorse any third-party claims made in their original material or related links on their sites; the opinions expressed by third parties are theirs alone. For further questions, please contact InfoDom Securities at dominanceinformation@gmail.com.