Daily Drop (565): TikTok: Espionage, Space Pirates: Poss. APT, China Cyber Threat: Private Public Response, Rhysida Ransomware, Sandworm: Ukrainian, Cloudflare Tunnels: C2, TSMC: Germany
08-09-23
Wednesday, Aug 09, 2023 // (IG): BB // Financial Enabler PODCAST // Coffee for Bob
The All-American Myth of the TikTok Spy (But what if it's true)
Analyst Comments: The piece offers a deep dive into the racial biases Chinese individuals face in the U.S., especially within the context of national security. Integrating historical context with modern examples and personal anecdotes, the challenges confronting Chinese entities and individuals are effectively illustrated. One of its strengths is juxtaposing past prejudices with contemporary events, providing a nuanced perspective. However, a more balanced discussion might have addressed legitimate concerns about Chinese espionage. Documented cases exist of IP theft in the agricultural sector, targeting proprietary farming techniques and genetically modified crops. Concerns about academic espionage have also grown, with allegations against the United Front and so-called "Confucius Centers" in universities, which some critics argue are used to exert soft power and potentially gather intelligence. While biases are well-highlighted, incorporating these genuine security concerns would provide a fuller picture of the complex U.S.-China relationship.
FROM THE MEDIA: The article discusses the racialized suspicion against Chinese individuals and entities in the U.S., particularly in the context of espionage and national security. The author shares a personal experience of being treated with suspicion due to their Chinese origin. The article traces the history of espionage in the U.S., noting that while it was once associated with European powers and later the Soviet Union, the face of foreign espionage in the West has now become Chinese. The author points out that Chinese students, scientists, and products are often viewed with suspicion. The article references 19th-century stereotypes of the Chinese as secretive and deceptive. The author discusses the portrayal of Chinese individuals as potential spies and touches on the rise of surveillance capitalism. The article concludes by suggesting that in this age of surveillance, privacy is a form of communal care.
READ THE STORY: Wired
One woman's Orwellian experience with disinformation
Analyst Comments: The ordeal faced by Nina Jankowicz underscores the challenges and vulnerabilities that individuals, especially women, face in the digital age. The fact that she became a target immediately after her appointment suggests a coordinated effort to discredit her and the board she was meant to lead. The gendered nature of the attacks is particularly concerning, highlighting the need for more robust measures to combat online harassment and ensure the safety and dignity of individuals in the public eye. The lawsuit against Fox News and other entities may set a precedent for holding media outlets accountable for their role in perpetuating or amplifying false narratives and online abuse.
FROM THE MEDIA: Nina Jankowicz, an expert in the field of disinformation, was appointed to lead the Disinformation Governance Board, a new advisory board created by the U.S. Department of Homeland Security (DHS) to counter disinformation. However, soon after her appointment, she became a target of online abuse, particularly of the kind that seems to be reserved for women. The attacks were not just about the concept of disinformation but also questioned her qualifications. As a result, Jankowicz resigned, and the board never convened. Despite her resignation, the online abuse continued. Jankowicz has now filed a defamation lawsuit against her attackers, including Fox News. The lawsuit is reminiscent of the Dominion Voting Systems suit settled earlier in the year. In an interview, Jankowicz discussed her experiences and the gendered nature of online attacks.
READ THE STORY: The Record
Why the China cyber threat demands an airtight public-private response
Analyst Comments: There has been a change of urgency internationally for addressing the cyber threat from China, which has been consistently escalating over the years. The emphasis on public-private collaboration is crucial, as both sectors bring unique strengths and resources to the table. While government agencies can provide intelligence, oversight, and strategic direction, the private sector often has the technical expertise, innovation, and agility to respond to evolving threats. The mention of past cyberattacks serves as a stark reminder of the potential consequences of inadequate cybersecurity measures. The initiatives by CISA and NIST are commendable but need to be part of a larger, more integrated strategy that involves all stakeholders.
FROM THE MEDIA: Written by Tom Guarente, the piece discusses the increasing cyber threat posed by China and emphasizes the need for a strong public-private response to address it. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has been at the forefront of the national effort to secure cyber and physical infrastructure. CISA's director, Jen Easterly, has highlighted the significant threat from Chinese state actors, emphasizing their vast resources and capabilities. Several high-profile cyberattacks linked to Chinese hackers are mentioned, including the data breach at the federal Office of Personnel Management in 2015 and the Equifax breach in 2017. There is a suggestion of a "visibility gap" in U.S. preparedness, marked by a lack of a coordinated approach to threat analysis and information sharing among various stakeholders. Initiatives like CISA's Shields Up program and the National Institute of Standards and Technology's (NIST) efforts to improve cybersecurity in supply chains are steps in the right direction. The piece concludes by emphasizing the need for robust public-private collaboration to address the growing cyber threats.
READ THE STORY: C4ISR Net
Space Pirates: A Sophisticated Cyber Threat Targeting Russia and Serbia
Analyst Comments: Space Pirates' increasing activities and evolving tactics underscore the dynamic nature of cyber threats. Their ability to target a diverse range of sectors, from government agencies to agricultural producers, indicates a broad scope and potentially significant backing. The use of innovative techniques, like exploiting legitimate forums for C2 and the adoption of sophisticated malware, showcases their advanced capabilities. The potential link to Chinese cyber espionage groups, while not definitive, suggests possible state-sponsored activities or at least some level of collaboration.
FROM THE MEDIA: The cyber threat actor, Space Pirates, has been actively targeting entities in Russia and Serbia, expanding its range of targets and evolving its tactics. A report from Positive Technologies reveals the group's activities over the past year, highlighting their focus on espionage and data theft. The group uses novel techniques, including the previously undocumented malware Voidoor and the Deed RAT, which has similarities to tools used by Chinese cyber espionage groups. Positive Technologies has been instrumental in uncovering these activities and recommends proactive measures to counter such threats.
READ THE STORY: Atlas News
Hackers Abusing Cloudflare Tunnels for Covert Communications
Analyst Comments: There is a been an uptick in resourcefulness of threat actors in exploiting available tools for malicious purposes. The use of Cloudflare Tunnels for covert communications is a testament to the evolving tactics of cyber adversaries. The detailed explanation of how Cloudflared works, and its potential misuse provides valuable insights for cybersecurity professionals. The real-world examples, such as the attacks on the PyPI repository, underscore the practical implications of these threats.
FROM THE MEDIA: Recent research has exposed that threat actors are exploiting Cloudflare Tunnels to establish covert communication channels from compromised systems, ensuring persistent access. Nic Finn, a senior threat intelligence analyst at GuidePoint Security, compared "Cloudflared" to "ngrok" but highlighted its enhanced usability features, especially its free offerings. Cloudflared is a command-line tool for Cloudflare Tunnel, which allows users to create secure connections between an origin web server and Cloudflare's nearest data center. This hides the web server IP addresses and blocks potential DDoS and brute-force login attacks. Threat actors with elevated access on a compromised host can exploit this feature to establish a foothold by generating a token required to set up the tunnel from the victim's machine. The tunnel's Private Networks functionality can also be misused by adversaries to access a range of IP addresses. Two software supply chain attacks targeting the Python Package Index (PyPI) repository earlier this year saw fraudulent packages downloading cloudflared to remotely access endpoints via a Flask web application.
READ THE STORY: THN
Ukraine says it thwarted attempt to breach military tablets
Analyst Comments: The continuous attempts by Russian hackers to compromise Ukrainian military systems underscore the escalating cyber warfare dimension in the ongoing conflict between the two nations. The focus on Android tablets, which are crucial for the Ukrainian military's battlefield operations, indicates a strategic approach to disrupt communication and gain sensitive information. The creation of multiple new malware strains for this operation signifies a high level of sophistication and determination. As cyber warfare becomes an integral part of modern conflicts, nations must prioritize securing their digital infrastructure and communication systems.
FROM THE MEDIA: Ukrainian security services have reported thwarting an attempt by Russian state-controlled hackers to infiltrate the battlefield management system used by the Ukrainian military. The hackers, identified as the Sandworm group, which operates under Russia’s military intelligence agency, tried to infect the Ukrainian military networks with at least seven new custom malware variants. The primary target of the attack was to gain access to Android tablets used by the Ukrainian military on the battlefield. Through these devices, the hackers aimed to access other connected devices and infect them with malware. The Ukrainian security services highlighted that the preparation for this cyber operation by Russia was extensive. In a previous attempt in December, pro-Russia hackers tried to compromise the Ukrainian system called Delta, which collects data on various fronts using drones, satellite images, electronic warfare systems, and surveillance cameras.
READ THE STORY: The Record
The Rhysida Ransomware: Activity Analysis and Ties to Vice Society
Analyst Comments: The Rhysida ransomware group's activities have been linked to several major cyberattacks since its emergence in May. An in-depth analysis by CPIRT and CPR has revealed that the group's tactics are strikingly similar to those of the Vice Society ransomware group. This connection is further supported by the coinciding decline in Vice Society's activities with the rise of Rhysida. The consistent TTPs used by major ransomware actors highlight the importance of understanding the entire process leading to a ransomware deployment, not just the payload itself. Monitoring these tactics can be instrumental in preventing future attacks.
FROM THE MEDIA: The Rhysida ransomware group, which surfaced in May, has been implicated in several significant cyber breaches, including an attack on the Chilean Army. More recently, they were linked to an attack on Prospect Medical Holdings, which had a widespread impact on numerous U.S. healthcare facilities. The U.S. Department of Health and Human Services has subsequently categorized Rhysida as a major threat to the healthcare sector. During an investigation into a Rhysida ransomware attack on an educational institution, the Check Point Incident Response Team (CPIRT) and Check Point Research (CPR) identified unique Techniques, Tactics, and Tools (TTPs) that bore significant similarities to those of the Vice Society ransomware group. This group, active since 2021, has been known to primarily target the education and healthcare sectors. The connection between Vice Society and Rhysida, which was recently proposed, is further substantiated by this technical analysis.
READ THE STORY: Checkpoint Research
QakBot Malware Operators Expand C2 Network with 15 New Servers
Analyst Comments: The QakBot malware operators have expanded their command-and-control network with 15 new servers. This malware, known for its transient C2 servers, operates with a tiered architecture similar to other malware like Emotet and IcedID. Recent findings show a decline in the number of C2s communicating with the T2 layer, attributed to null-routing actions by Black Lotus Labs.
FROM THE MEDIA: The QakBot malware, also known as QBot, has seen its operators expand their command-and-control (C2) network by adding 15 new servers since late June 2023. This development follows an analysis by Team Cymru, which comes two months after Lumen Black Lotus Labs highlighted the transient nature of QakBot's C2 servers, with 25% being active for only a day. Interestingly, QakBot's activity tends to wane during the summer months, resuming in September. This pattern has led to speculations about whether this "break" is a period of infrastructure and tool refinement for the operators. The malware's C2 network is structured similarly to Emotet and IcedID, with a tiered architecture. Most of the bot C2 servers are located in India and the U.S., while the destination IP addresses for outbound T2 connections are primarily in the U.S., India, Mexico, and Venezuela. The malware also features a BackConnect server, turning infected bots into proxies for other malicious activities.
READ THE STORY: THN
TSMC and pals chip in for €10B German fab
Analyst Comments: The joint venture signifies a strategic move by TSMC and its partners to tap into the European market, particularly focusing on the automotive and industrial sectors. While the decision to use mature technology might raise eyebrows, it aligns with the specific needs of the target sectors. Germany's substantial financial commitment underscores its aggressive strategy to position itself as a semiconductor hub. However, the allocation of funds and potential market distortions due to subsidies could lead to industry contention, as highlighted by GlobalFoundries' concerns. The venture's success will largely depend on its ability to navigate these challenges and effectively cater to the European market's demands.
FROM THE MEDIA: TSMC, in a partnership with NXP, Infineon, and Bosch, has unveiled plans for a joint venture. Their goal is to establish a 300mm-wafer fab located near Dresden, with the capability to produce 40,000 wafers every month. Interestingly, the technology they plan to use for this venture, specifically TSMC's 28/22nm planar CMOS and 16nm/12nm FinFET nodes, will be nearly a decade old by the time production commences in 2027. However, this isn't perceived as a setback. Given that the facility's primary focus will be on producing chips for the automotive and industrial sectors, the use of slightly older technology aligns with the sector's needs, which often don't require the absolute latest in tech.
READ THE STORY: The Register
UK electoral register hacked by ‘hostile actors’, watchdog reveals
Analyst Comments: This breach underscores the vulnerabilities present in public sector systems and the potential risks to democratic processes. The prolonged undetected access granted to the hackers is particularly concerning, highlighting gaps in cybersecurity monitoring and response. While the commission asserts that the breach poses minimal risk to election outcomes or voter impersonation, the potential misuse of the data for profiling or inferring behavioral patterns remains significant. The incident serves as a stark reminder of the importance of robust cybersecurity measures, especially for institutions holding sensitive data.
FROM THE MEDIA: The UK's Electoral Commission has disclosed that hackers accessed the details of tens of millions of British voters in a cyber-attack that went unnoticed for over a year. The breach began in August 2021, with the hackers accessing the commission's file-sharing and email systems and copying the electoral register. The suspicious activity was only detected in October 2022. The compromised data includes names, home addresses, and voting age dates for individuals registered between 2014 and 2022. The commission has not identified the culprits, and no group has claimed responsibility. This breach is among the largest UK data breaches in terms of the number of affected individuals. The National Cyber Security Centre (NCSC) has been assisting the commission in the aftermath of the incident. The breach follows other cyber incidents affecting the public sector, including a ransomware attack on Capita and a hacking spree by the Clop gang.
READ THE STORY: FT
New Android 14 Security Feature: IT Admins Can Now Disable 2G Networks
Analyst Comments: Google's decision to allow the disabling of 2G networks on Android devices is a proactive measure to enhance cybersecurity. Given the known vulnerabilities of 2G networks, this move is crucial in protecting users from potential cyber threats. The emphasis on end-to-end encryption for messaging further underscores the company's commitment to user privacy and security. However, the broader challenge remains the global reliance on outdated and insecure technologies, which can be exploited by malicious actors.
FROM THE MEDIA: Google has unveiled a new security feature in Android 14 that empowers IT administrators to disable 2G cellular networks on managed devices. This move is in response to the vulnerabilities associated with 2G networks, which use weak encryption and are prone to interception and traffic decryption attacks. These networks can be exploited by malicious actors to intercept communications, distribute malware, and initiate other cyberattacks. In 2020, Amnesty International revealed an instance where a Moroccan journalist was targeted using a fake cell tower to deploy the Pegasus spyware. Google had previously introduced an option to disable 2G at the modem level with Android 12 in 2022. The latest update further restricts a device's ability to revert to 2G connectivity. The company is also addressing the risk of null ciphers in commercial networks and has announced end-to-end encryption (E2EE) for RCS conversations in its Messages app.
READ THE STORY: THN
Items of interest
This AI Company Releases Deepfakes into the Wild. Can It Control Them
Analyst Comments: The piece underscores the dual-edged nature of advancements in AI. While Synthesia's deepfakes represent a significant stride in technological innovation, they also present a myriad of challenges, particularly concerning the spread of misinformation. The article serves as a testament to the broader implications of the AI industry's growth, emphasizing the need for companies to strike a balance between innovation and ethical responsibility. As AI tools become increasingly accessible and integrated into various sectors, there's an amplified call for robust content moderation and ethical considerations in their deployment. The narrative surrounding Synthesia serves as a cautionary tale for the AI industry at large, highlighting the importance of proactive measures to curtail potential misuse.
FROM THE MEDIA: Synthesia offers its clients digital avatars capable of reading scripts, with the primary intention of serving as an advanced tool for corporate training and presentations, rivaling traditional tools like Microsoft PowerPoint. However, these avatars have been misappropriated for malicious purposes, including the spread of misinformation about geopolitical events and involvement in crypto scams. Victor Riparbelli, the CEO of Synthesia, acknowledges these challenges and emphasizes the company's ongoing efforts to address them. They have notably expanded their content moderation team and have implemented more stringent controls on content creation. The article also touches upon the company's growth trajectory, highlighting its recent valuation of $1 billion. Synthesia's avatars are uniquely trained using real human actors in their in-house studios. Looking ahead, Riparbelli envisions a future where synthetic video becomes as dynamic and interactive as modern websites.
READ THE STORY: Wired
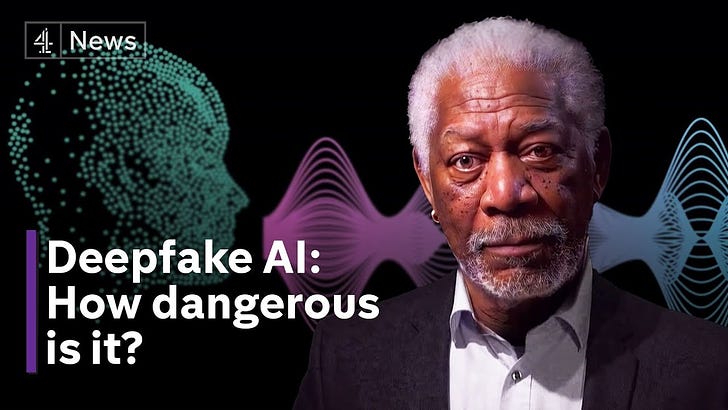
How do we prevent AI from creating deepfakes (Video)
FROM THE MEDIA: Money Saving Expert Martin Lewis is one of the most trusted people in the country - so it's easy to take his endorsement seriously. But it also made him an obvious target for AI scammers to replicate his face and voice and create a fake endorsement. And that's deeply worrying because as deepfake technology becomes more ubiquitous, that kind of impersonation could make us all vulnerable to fraud.
China's Deepfake Regulations: navigating security, misinformation and innovation (Video)
FROM THE MEDIA: China implemented new regulations on 'deep synthesis' technology in January 2023. Some commentators have called it a 'landmark', 'first-of-its-kind' and the 'most comprehensive' law in the world regulating deepfakes. The regulations prohibit the use of such technology for spreading 'fake' news or information that could disrupt the economy or national security, which authorities have wide latitude to interpret. Providers of 'deep synthesis technologies' must take steps to prevent the use of their services for illegal or harmful purposes, protect user privacy by requiring consent, authenticate user identity, and label synthetic content, among other legal obligations.
These open-source products are reviewed by analysts at InfoDom Securities, providing possible context about current media trends related to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not endorse any third-party claims made in their original material or related links on their sites; the opinions expressed by third parties are theirs alone. For further questions, please contact InfoDom Securities at dominanceinformation@gmail.com.