Daily Drop (527): ATP15: Backdoor, Apple: 2 Zero Days, U.S. Offers India Drones, Canada's energy sector: RU the attacker, ScarCruft: Ably API, China’s Cloud Computing, DDoS Botnet ‘Condi’: TP-Link
06-22-23
Thursday, Jun 22, 2023 // (IG): BB // Financial Enabler PODCAST // Coffee for Bob
Experienced China-based hacking group has a new backdoor tool, researchers say
Analyst Comments: Nickel's recent use of a new backdoor in its operations underscores the group's resilience and continued threat to global cybersecurity. The group's ability to evolve its techniques and bypass security measures is indicative of its advanced capabilities and resources. As they continue to develop new tools and strategies, governments and organizations worldwide must remain vigilant and proactive in their cybersecurity efforts to prevent and mitigate such sophisticated attacks.
FROM THE MEDIA: The Chinese cyber-espionage group, Nickel, also known as APT15, launched attacks on foreign affairs ministries in Central and South America using a previously unseen backdoor called Graphican. Symantec, which investigated the incident, reported that the campaign targeted a government finance department, an unidentified corporation, and several foreign affairs ministries from late 2022 into early 2023. Nickel used a variety of tools, including Graphican, which is an upgrade from the previously used Ketrican backdoor. The backdoor employs Microsoft Graph API and OneDrive services to connect with an encrypted command-and-control infrastructure, giving hackers remote control of compromised systems. Despite actions taken to disrupt its operations, Nickel continues to be a significant cyber threat, demonstrating a high level of resourcefulness and adaptability.
READ THE STORY: The Record // THN // DARKReading
Apple addresses two zero-days exploited in Operation Triangulation spyware campaign
Analyst Comments: The revelation of the spyware campaign and the associated zero-day vulnerabilities underscores the importance of continuous vigilance and cybersecurity practices. Apple's quick response in patching the vulnerabilities demonstrates its commitment to user security. However, the accusations by the FSB against U.S. intelligence and Apple point to the larger geopolitical implications of such cyber activities, potentially increasing tensions between the countries. The sophistication of the attack, with the malware operating solely in device memory and leaving no trace after a reboot, underlines the advanced capabilities of the threat actors involved and the challenges in detecting and preventing such attacks.
FROM THE MEDIA: Apple has issued patches for two zero-day vulnerabilities that were exploited in a spyware campaign, known as Operation Triangulation. The campaign, active since 2019, was exposed by the Russian cybersecurity firm, Kaspersky, and involves sending malicious iMessage attachments to iPhones. The two zero-days, CVE-2023-32434 and CVE-2023-32439, were reported by Kaspersky and do not affect devices running iOS versions newer than 15.7. Russia's Federal Security Service (FSB) claimed the spyware was used by U.S. intelligence to target Russian diplomats' iPhones, an accusation Apple denied. Kaspersky's investigation revealed the spyware operates only in the device's memory and is erased after a reboot or 30 days unless the attacker decides to extend it.
READ THE STORY: The Record // THN
U.S. Offers India Drones, Jet Engines to Lure It From Russia
Analyst Comments: The arms deal signals a significant shift in U.S.-India defense relations, representing a turning point towards greater cooperation and trust. The U.S.'s willingness to share advanced military technology with India is a major development, considering India's historical dependence on Russian arms. However, this shift may take years to fully materialize due to the deep-rooted defense ties between India and Russia. The deal also has strategic implications, particularly in the Indo-Pacific region. By strengthening ties with India, the U.S. is likely attempting to counter China's growing influence in the region. However, this balancing act brings its own complexities, as it needs to be navigated carefully to avoid escalating tensions.
FROM THE MEDIA: India is set to purchase advanced U.S. drones and participate in a joint production of jet-fighter engines in a multibillion-dollar deal with the United States. This significant move comes as India has traditionally been a significant buyer of Russian arms. The deal is expected to be announced during Indian Prime Minister Narendra Modi's visit to Washington. In addition to this, the two countries are planning to strengthen ties between their militaries in various areas like logistics and intelligence-sharing. The U.S. has also proposed other major commitments on technology, supply chains, and clean energy. Prime Minister Modi's visit, however, has sparked controversy, with some lawmakers boycotting his address to Congress due to concerns over his human rights record.
READ THE STORY: WSJ
Critical 'nOAuth' Flaw in Microsoft Azure AD Enabled Complete Account Takeover
Analyst Comments: The discovery of nOAuth vulnerability underscores the importance of robust security measures and continuous monitoring in cloud environments. The flaw could have led to severe consequences such as full account takeovers, persistent threats, data exfiltration, and potentially broader system compromise. Microsoft's response to this issue by issuing a warning and identifying and notifying affected applications indicates its proactive approach to mitigating these risks.
FROM THE MEDIA: Microsoft Azure Active Directory's (AD) Open Authorization (OAuth) process had a security flaw that could have led to a full account takeover, according to identity and access management service Descope. The California-based company, which discovered and reported the issue in April 2023, has dubbed it nOAuth. The vulnerability stems from a misconfiguration in which a malicious actor could change email attributes under "Contact Information" in the Azure AD account and exploit the "Log in with Microsoft" feature to hijack a victim account. Microsoft described the issue as an "insecure anti-pattern used in Azure AD applications," where the usage of the email claim from access tokens for authorization can result in an escalation of privilege.
READ THE STORY: THN
Russia-aligned hackers are looking to disrupt Canada's energy sector, intelligence agency warns
Analyst Comments: The CSE's warning showcases the widespread impact of the ongoing conflict in Ukraine and highlights the potential vulnerabilities of critical infrastructure sectors, like oil and gas, to cyber-attacks. Cyber threats to critical infrastructure have the potential to disrupt services and operations, negatively impacting economies and citizens' lives. The past successful breaches underline the seriousness of these warnings. The primary threats currently facing the sector include ransomware attacks and business email compromise, indicating the need for robust cybersecurity protocols, not just against state-level threats, but also from criminal entities. The call to bolster security within the sector reflects a growing international concern for the increasing cyber threat landscape, particularly in the context of geopolitical tensions.
FROM THE MEDIA: Canada's Communications Security Establishment (CSE), a foreign signals and cyber intelligence agency, has warned that Russia-aligned non-state threat actors will likely continue their attempts to compromise the country's oil and gas sector until the conflict in Ukraine concludes. The intent behind this cyber activity is likely to disrupt critical services for psychological impact, aiming to weaken Canadian support for Ukraine. The agency noted that these actors, while less sophisticated than Kremlin-sponsored counterparts, still possess the capability to cause harm. The threat assessment follows a suspected Russian-backed cyber breach into Canada's natural gas distribution network.
READ THE STORY: CBC
Kremlin-backed hacking group puts fresh emphasis on stealing credentials
Analyst Comments: The report of increased activity by Nobelium, known for high-profile attacks like the SolarWinds supply chain attack in 2020, underscores the persistent threat posed by state-affiliated advanced persistent threats (APTs). The group's tactics, such as using low-reputation proxy services and frequently changing IP addresses, demonstrate the sophistication and adaptability of these threat actors, which pose a significant challenge to cybersecurity defenses. This development is particularly concerning given the group's history of targeting critical sectors and the ongoing geopolitical tensions with Russia. Such attacks can lead to significant data breaches and disruptions, with potential implications for national security and infrastructure.
FROM THE MEDIA: Microsoft has reported an increase in credential-stealing cyberattacks perpetrated by Russian-affiliated hacker group APT29, also known as Cozy Bear, Nobelium, or as per Microsoft's new naming convention, Midnight Blizzard. These attacks are primarily targeting governments, IT service providers, non-governmental organizations (NGOs), as well as defense and critical manufacturing industries. Although the specific countries targeted in the recent campaign were not revealed, Nobelium has a history of conducting espionage against foreign ministries and diplomatic entities of NATO and European Union nations.
READ THE STORY: The Record
Chinese APT is the most documented Nation-State Actors
Analyst Comments: The report demonstrates the persistent and prevalent threat posed by nation-state cyber-actors, especially from China. These advanced persistent threats (APTs) leverage sophisticated tools and tactics to target crucial sectors across different nations. It is also noteworthy that China has been particularly active against Asian countries such as the Philippines and India, signifying regional geopolitical tensions translated into the cyber domain.
FROM THE MEDIA: Trellix's recent CyberThreat Report indicates that China is the leading nation-state actor in aggressive cyberattacks and espionage, accounting for 79% of such activities. The report also highlights Mustang Panda, a China-based threat actor, as responsible for 72% of the attacks. The most common tools used by these actors include the legitimate pen-testing tool Cobalt Strike, which is used in 35% of attacks, and the remote access Trojan PlugX. The countries experiencing the highest number of nation-state activity detections are the Philippines and India. Key industries targeted by these state-based hackers are the oil and gas industry, outsourcing and hosting, wholesale, financial, and education sectors.
READ THE STORY: CyberSecurityConnect
ScarCruft Hackers Exploit Ably Service for Stealthy Wiretapping Attacks
Analyst Comments: ScarCruft's use of sophisticated techniques, including the Golang backdoor and abuse of the Ably API service, demonstrates their evolving capabilities and their focus on targeted information theft. The group's connections to the North Korean Ministry of State Security highlight its state-sponsored nature and the potential political motivations behind its operations. The use of spear-phishing and CHM files aligns with tactics employed by other North Korean-affiliated groups, indicating a consistent modus operandi. The findings serve as a reminder of the persistent cyber threats posed by nation-state actors and the need for robust cybersecurity measures to protect against their activities.
FROM THE MEDIA: The North Korean threat group ScarCruft, linked to the country's Ministry of State Security, has been observed employing new tactics in their cyber espionage campaigns. According to AhnLab Security Emergency Response Center (ASEC), ScarCruft has used a backdoor developed using Golang that exploits the Ably real-time messaging service for command-and-control communications. The group sent commands through the Golang backdoor, with the API key saved in a public GitHub repository. The email-based attack chain involves spear-phishing with Microsoft Compiled HTML Help (.CHM) files that deliver PowerShell malware named Chinotto, which sets up persistence and downloads additional payloads. One of the payloads is an information-stealing malware called FadeStealer, capable of taking screenshots, gathering data, logging keystrokes, and wiretapping. ScarCruft's primary focus is information theft, targeting specific individuals such as North Korean defectors, human rights activists, and university professors.
READ THE STORY: THN
China’s Cloud Computing Firms Raise Concern for U.S.
Analyst Comments: The US's focus on Chinese cloud companies demonstrates the escalating technological tensions between the two superpowers. It reflects the broader geopolitical concerns over data privacy, national security, and digital sovereignty. If enacted, new regulations could significantly impact Chinese cloud companies' growth in international markets, but there's also a risk of reciprocal actions from China, affecting US-based tech companies' operations in China and other regions.
FROM THE MEDIA: In response to increasing security concerns about Chinese cloud computing companies like Alibaba and Huawei, US officials are exploring tighter rules and strategies to curb their growth. The primary fear is that these companies could be leveraged by Beijing to gain access to sensitive data in the US and globally. Despite Chinese companies representing a small fraction of the US cloud market, they are making significant progress in regions such as Asia and Latin America. US strategies to restrict Chinese tech companies have yielded mixed results. While restrictions on Huawei suppliers damaged the company's smartphone business, attempts to eliminate Huawei equipment from US wireless networks are ongoing. Other efforts to force the sale of Chinese-owned apps like Grindr and TikTok have either succeeded or remained unsuccessful. The global cloud computing market had revenues of $544 billion last year, according to Synergy Research Group.
READ THE STORY: The New York Times
China TikTok figure fingered in ‘deepfake’ anti-U.S. Russian soldier videos
Analyst Comments: The deepfake incident highlights the increasing sophistication of digital misinformation campaigns and the potential for their use in shaping public perceptions or promoting specific narratives. It also raises concerns about the potential for social media platforms, especially those with large user bases like TikTok, to be used as conduits for spreading such deceptive content. The growing prevalence and sophistication of deepfakes could pose significant challenges for detecting and combating misinformation online.
FROM THE MEDIA: A series of "deepfake" videos claiming to follow a Russian special operations soldier in Ukraine has been found to be created by a Chinese TikTok user. The videos were used to promote narratives of Russia-China friendship to hundreds of thousands of followers on Douyin, the Chinese version of TikTok. However, officials recently suspended the account, asserting the AI-generated videos were spreading misinformation. The user, identified as Baoer Kechatie, allegedly used deepfake technology to fool his 400,000 followers, claiming he was a Russian special ops fighter in Ukraine. This incident has sparked renewed concerns over the spread of deepfakes on social media.
READ THE STORY: Washington Times
European Council agrees to water down protections for journalists from spyware
Analyst Comments: The proposed amendments by the European Council could significantly weaken the protections offered to journalists under the EMFA, potentially increasing their vulnerability to state surveillance and cyber-attacks. While the invocation of national security and public interest may justify certain exceptions, broadening these parameters could risk enabling potential abuses of power. It is crucial to strike a balance that upholds both national security and press freedom. The potential for these changes to sideline the European Court of Justice's jurisdiction over such issues also raises concerns about accountability and the enforcement of these protections.
FROM THE MEDIA: The European Council is seeking amendments to the proposed European Media Freedoms Act (EMFA) that would reduce protections for journalists from government surveillance and spyware. The original version of the EMFA prohibited such surveillance and use of spyware, except in cases of "an overriding requirement in the public interest" or for "national security." However, the Council's amended version broadens the circumstances in which spyware can be used against journalists and emphasizes member states' sovereignty over their national security interests. Critics, including civil society groups, argue that these changes would effectively remove the European Court of Justice's power to rule against member states accused of hacking into a journalist's phone.
READ THE STORY: The Record
Russia-aligned hackers pose a threat to Canada's energy sector
Analyst Comments: The energy sector, including oil and gas, is a frequent target of such attacks due to its critical role in a nation's economy and infrastructure. A successful cyber attack on this sector could cause significant economic damage and potentially disrupt critical services. Therefore, this warning from the CSE underscores the importance of robust cybersecurity measures in critical infrastructure sectors, especially during periods of heightened geopolitical tension.
FROM THE MEDIA: The Communications Security Establishment (CSE), a Canadian spy agency, has warned that hackers aligned with Russia could disrupt Canada's oil and gas sector due to Canada's support for Ukraine. The CSE states that Russia has a history of launching destructive cyber attacks against adversaries amid escalating geopolitical crises. The agency believes that the oil and gas sector, which employs about 600,000 people and makes up 5% of Canada's GDP, could be a likely target. The most probable targets for cyber attacks are operational technology networks overseeing large industrial assets. The CSE also stated that Russian-aligned actors are attempting to compromise the networks of Canadian infrastructure providers, particularly in the oil and gas sector, with the likely aim of disrupting critical services and weakening Canadian support for Ukraine.
READ THE STORY: Reuters
New DDoS Botnet ‘Condi’ Targets Vulnerable TP-Link AX21 Routers
Analyst Comments: The discovery of the Condi botnet demonstrates the persistent threat of DDoS botnets exploiting unpatched vulnerabilities in commonly used devices. Its capacity to neutralize competitor botnets and its older versions reflects the increasing sophistication of cyber threats. Despite its lack of persistence after a system reboot, the botnet's aggressive monetization techniques, including DDoS-as-a-service and selling malware source code, pose a significant risk. Regular patching and software updates are vital to mitigate such threats.
FROM THE MEDIA: A DDoS-as-a-service botnet called Condi is being distributed by exploiting TP-Link Archer AX21 (AX1800) Wi-Fi 6 routers that are vulnerable to CVE-2023-1389, as per a report by FortiGuard Labs. This marks the second botnet to exploit this flaw after the Mirai botnet did so in April 2023. Condi looks for vulnerable routers and delivers malware via a shell script from a remote server. Interestingly, Condi can terminate competitor botnet processes and prevent its older versions from operating. However, it lacks system persistence and gets wiped out after a system reboot. The botnet is believed to be operated by a threat actor who uses the alias zxcr9999 on Telegram and monetizes by providing DDoS-as-a-service and selling malware source code.
READ THE STORY: HackRead
Apple issues emergency patch to address alleged spyware vulnerability
Analyst Comments: The allegations from Russia's FSB add to the global tension over cybersecurity, specifically regarding state-sponsored cyberattacks. Apple's prompt response in patching the vulnerabilities highlights the company's commitment to user privacy and security, a significant selling point of its devices. The incident underscores the importance of cooperation between tech companies and cybersecurity firms to ensure the rapid identification and resolution of potential security threats. It also serves as a reminder for users to keep their devices updated with the latest security patches.
FROM THE MEDIA: Apple has released a security update for all its operating systems to patch critical vulnerabilities that could enable attackers to control an entire device. These flaws led Russia's Federal Security Service (FSB) to allege that Apple intentionally left these vulnerabilities in its iOS for the National Security Agency and other U.S. entities to exploit, compromising numerous iPhones in Russia. Apple has denied these claims. The vulnerabilities were first revealed in cybersecurity firm Kaspersky's report on an ongoing zero-click iMessage exploit campaign named "Operation Triangulation." Kaspersky, however, did not attribute the campaign to any operators. The company shared information about the attack with Apple, leading to the creation of the patch. Apple confirmed that the issues may have been actively exploited and assured users that it has never worked with any government to introduce a backdoor into its products.
READ THE STORY: Cyberscoop
The Russians Are Turning Old Vehicles Into Rolling Bombs. The Ukrainians Are Trying To Spot Them Before They Explode.
Analyst Comments: The use of VBIEDs by Russian forces illustrates a significant shift in warfare strategies and highlights the threat posed by such crude but effective weapons. The combination of older vehicles with large amounts of explosives demonstrates how conventional military equipment can be repurposed for unconventional warfare. While Ukrainian forces have successfully countered some of these VBIEDs using drones and rocket strikes, the challenge remains due to the wide range of potential attack paths these vehicles can take.
FROM THE MEDIA: Russian forces have been using old armored vehicles, filled with explosives and sent unmanned toward Ukrainian positions, in recent attacks around Marinka, eastern Ukraine. Although at least two of these attacks were unsuccessful, Russia claims one vehicle-borne improvised explosive device (VBIED) caused "significant losses" on a Ukrainian strongpoint. VBIEDs can be filled with tons of explosives, presenting a serious threat to unprotected enemy troops from hundreds of feet away. However, these devices are typically used by forces with too many outdated vehicles and limited modern long-range weaponry. Armies with sufficient stocks of rocket artillery rarely use VBIEDs. Despite the Russians' access to support from artillery brigades, it's unclear why they are opting for VBIEDs. The presence of such explosive vehicles could be an indicator of a temporary shortage of rockets and shells. The Ukrainian forces have been countering these VBIEDs by patrolling with drones and striking with rockets or anti-tank missiles.
READ THE STORY: Forbes
America must wean itself from China
Analyst Comments: The suggestion to alter economic relations with China reflects a broader discourse regarding the U.S.'s approach to managing its relationship with China. The idea of decreasing dependency on Chinese manufacturing and promoting domestic production represents a significant policy shift, which would have substantial implications for global trade and domestic economies.
FROM THE MEDIA: The United States is urged to combat Chinese expansionism by striking at its economy. The economic stagnation in China presents a potential opportunity for the U.S. to decrease its economic dependency on China, given that the U.S.'s trade deficit with China is approximately $355.3 billion. Analysts argue for an increase in domestic manufacturing, particularly for prescription drugs, as one of the steps in detaching from China. This step would require a bipartisan effort from U.S. politicians to halt China's ambitions for global dominance. Despite potential higher costs for goods, many Americans might be willing to support such a strategy if it were in their country's best interests. Critics argue that policymakers are currently maintaining economic flows between the U.S. and China while also planning for potential military conflict over Taiwan.
READ THE STORY: Washington Times
Better Choreography Required For Complex Chips
Analyst Comments: The rising complexity in ASIC design introduces several new challenges that require rethinking traditional workflows and design processes. The emphasis on shifting left—moving steps earlier in the planning and design processes—indicates a proactive approach to managing complexity, rather than dealing with issues retroactively. While this approach seems necessary given the scale and intricacy of modern ASIC design, it also highlights the increasing importance of advanced tools and technologies in aiding this process, such as multiphysics simulation tools.
FROM THE MEDIA: In the realm of ASIC (Application-Specific Integrated Circuit) design, the escalating complexity of devices and a corresponding increase in the number of features necessitates a shift in planning and coordination. Design flow now requires precise orchestration, with certain steps being moved earlier (shifting left) in the planning process. Greater emphasis is placed on early detection and resolution of problems to avoid costly later-stage corrections. The iterative approach, in which designs are continuously refined, is advocated for managing this increasing complexity. The choice of traditional 2D SoC (System on Chip) or a 3D-IC (Integrated Circuit) design also adds to the complexity. Further, questions of how to handle heat dissipation and mechanical stresses in 3D stacked designs necessitate additional considerations. Designers are encouraged to adopt a holistic approach, considering system-wide solutions rather than focusing solely on chip reliability.
READ THE STORY: SemiEngineering
Chinese Firms Are Evading Chip Controls
Analyst Comments: The U.S.'s efforts to cut off China's access to advanced chips are undermined by smuggling and cloud computing rentals. While the initial restrictions intended to curb China's access to AI chips, it seems a lot of gaps and vulnerabilities were left unaddressed, making the ban less effective than intended. The suggested strategies to tighten the enforcement of the ban, such as a random chip sampling program and stricter cloud computing regulations, might increase the efficacy of the ban, but their implementation is challenging due to logistical and regulatory complexities.
FROM THE MEDIA: Last fall, the Biden administration instituted a ban to cut off China's supply of powerful chips used in AI and supercomputing. However, reports suggest that Chinese entities, including their top nuclear weapons lab, have been able to access these restricted chips through smuggling and renting via cloud computing. The challenge lies in enforcing this ban due to the scale at which these chips are produced and their compact size, which makes smuggling feasible. The proposed solution to address this issue includes a random chip sampling program that requires sellers of controlled chips to register their sales and notify the Bureau of Industry and Security (BIS) about secondhand sales or cases where chips are destroyed or lost. This approach is aimed at deterring smuggling and ensuring that supercomputer-scale smuggling of chips to China is not occurring.
READ THE STORY: FP
A (cautionary) tale of two patched bugs, both exploited in the wild
Analyst Comments: This situation illustrates the critical importance of the timely application of security patches. Although patches were released for both vulnerabilities, the continued exploitation indicates that many systems remain unpatched. Users of affected VMware and TP-Link products must apply the patches as soon as possible to mitigate risk. The emergence of DDoS-as-a-service botnets, such as Condi, lowers the barrier to entry for cybercrime, increasing the threat landscape for unpatched vulnerabilities. Thus, regular patching schedules, awareness of new vulnerabilities, and timely response to security advisories should be an integral part of any organization's cybersecurity strategy.
FROM THE MEDIA: Two security vulnerabilities, one in a VMware network and application monitoring tool (Aria Operations for Networks) and the other in TP-Link routers, are currently being exploited. The VMware vulnerability (CVE-2023-20887), a command-injection vulnerability with a high severity rating, has been confirmed to be exploited in the wild. The TP-Link vulnerability (CVE-2023-1389) is being exploited by a DDoS-as-a-service botnet called Condi, which targets TP-Link Archer AX21 routers. Both vulnerabilities were patched earlier, but are still being exploited due to unapplied patches.
READ THE STORY: The Register
AMD's 128-core Epycs could spell trouble for Ampere Computing
Analyst Comments: AMD's Epyc processors pose a strong challenge to Ampere's dominance in the cloud-native workload market. Though initial comparisons favor AMD in terms of performance, power efficiency might still favor Ampere. Ultimately, it could come down to which features and specs are most valued by the cloud providers. Furthermore, the compatibility of AMD's x86 architecture with existing software ecosystems could offer an advantage over Arm-based chips from Ampere. However, this market segment is still very fluid and it remains to be seen how things will unfold once the next-gen AmpereOne chips are released.
FROM THE MEDIA: AMD has launched its 128-core Epyc processors, codenamed Bergamo, providing stiff competition for Ampere Computing in the cloud and hyperscale market. Ampere had carved a niche in this area by producing power-efficient, core-dense parts for cloud-native, scale-out workloads. Despite competition from industry giants such as AMD and Intel, Ampere remains confident of its position. AMD's Bergamo, fabricated using TSMC's 5nm and 6nm processes, differs considerably from Ampere's Altra Max, which is over two years old and uses an older 7nm technology. AMD claims a 2.9x performance lead over the Altra Max in cloud-native workloads, although power consumption is also significantly higher. However, the true competition might come from Ampere's next-generation AmpereOne lineup, offering up to 192 cores.
READ THE STORY: The Register
Items of interest
One person's trash is another's 'trashware' – the art of refurbing old computers
Analyst Comments: Perotti's efforts through PCOfficina underscore the potential of "trashware" in bridging the digital divide by making technology accessible to those who might not afford new equipment. This kind of initiative not only promotes digital inclusion but also reduces e-waste by giving a new purpose to older hardware. The recommendation of Linux Mint 21 Xfce edition, despite it being a Red Hat event, shows a practical approach, focusing on what works best in a given context.
FROM THE MEDIA: Andrea Perotti, a Platform Technical Account Manager for Red Hat, presented an inspiring talk at Red Hat's Devconf.cz conference, highlighting his involvement in a volunteer organization, PCOfficina. The group refurbishes surplus IT equipment to help people who cannot afford new computers. This concept, referred to as "trashware," gives a second life to end-of-life hardware by updating them to run modern operating systems and software. PCOfficina has certain minimum specifications for the devices they refurbish, and they recommend using the Linux Mint 21 Xfce edition due to its modest hardware requirements and long support life-cycle.
READ THE STORY: The Register
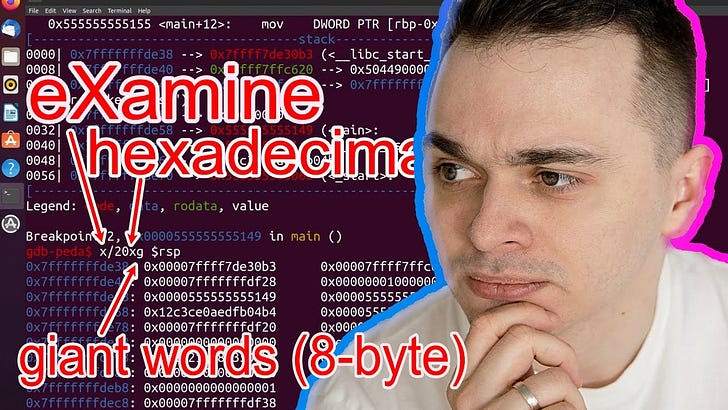
GDB Tutorial for Reverse Engineers: Breakpoints, Modifying Memory and Printing its Contents (Video)
FROM THE MEDIA: The tutorial explains how to open a file in GDB, start program execution, and set breakpoints using symbol names or addresses. It mentions commands for managing breakpoints, such as listing and deleting them. The "start" command from Peda is introduced as a shortcut for starting program execution and stopping at the beginning of the "main" function. The transcript covers single-stepping through code using commands like "step" and "next," with additional tips like pressing "Return" on an empty line to repeat the previous command. It explains the "xuntil" command to continue execution until a specific address or function. Modifying registers is demonstrated using the "set" command, treating registers as variables in GDB.
Finding main() in Stripped Binary - bin 0x2C (Video)
FROM THE MEDIA: Stripped binaries miss the symbol information of functions and variables. Debugging such a binary is a little bit more tricky, but there is a simple method to find the main() function of the program.
These open-source products are reviewed by analysts at InfoDom Securities, providing possible context about current media trends related to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not endorse any third-party claims made in their original material or related links on their sites; the opinions expressed by third parties are theirs alone. For further questions, please contact InfoDom Securities at dominanceinformation@gmail.com.