Daily Drop (513): Senegal's Internet Shutdown, German Pilots Share TTP, SK Supports Chip Sector, Stealth Soldier: North Africa Attacks, Getting Online in DPRK, US/Taiwan/Japan Drone Alliance
06-08-23
Thursday, Jun 08, 2023 // (IG): BB // Intro Exploit Dev // Coffee for Bob
Senegal continues curfew-like internet shutdown to subdue protests
Analyst Comments: The curfew-style internet shutdowns imposed by the Senegalese government in response to protests and dissent raise concerns about freedom of expression and the right to access information. By limiting internet access, the government is suppressing communication and hindering the ability of citizens to express their opinions and engage in peaceful assembly. The targeting of social media platforms and the blocking of private TV signals further restrict the flow of information and limit transparency. These actions are seen as violations of human rights and international standards. The unique aspect of the Senegalese situation is the implementation of connectivity shutdowns during normal working hours, which disrupts not only the right to access information but also hinders economic activities and productivity. The use of internet shutdowns as a means to control information and silence dissent is a concerning trend, particularly in a democratic society where citizens should have the freedom to express their views.
FROM THE MEDIA: The government of Senegal has implemented curfew-like shutdowns on internet access across the country, blocking it from 1 p.m. to 2 a.m., in response to protests over the trial and conviction of opposition figure Ousmane Sonko. The government claims that the restrictions are necessary to prevent the spread of "fake news" on social media and messaging apps. Various organizations and companies monitoring internet access have confirmed the intentional limitation of mobile internet during specific times. The shutdowns have been criticized by Amnesty International and the Human Rights Foundation, who consider them arbitrary and in violation of international law.
READ THE STORY: The Record
Did German Pilots Just Pass NATO’s Tactics to China?
Analyst Comments: The training of PLAAF pilots by retired German and British pilots poses significant security concerns. Europe is seen as underestimating the threat to its security posed by China's rising military power, particularly given Beijing's revisionist perspective on the existing global order. China's strengthened military might due to such international training, especially in potential combat scenarios like Taiwan, has far-reaching implications. It poses a direct challenge to U.S. military efforts in the Asia-Pacific region and indirectly impacts European security. It may further necessitate the reallocation of high-end platforms and capabilities from the U.S., which could otherwise be used for maintaining adequate deterrence against Russia in Europe. Consequently, European governments are urged to enforce strict regulations to prevent any form of aid to the People's Liberation Army.
FROM THE MEDIA: Several retired German Luftwaffe pilots have reportedly been training Chinese People's Liberation Army Air Force (PLAAF) pilots over the past decade. This is seen as a continuation of a historical pattern dating back to the 1930s when Nazi Germany provided military advisories to China. The recent assistance to the PLAAF could potentially pass on valuable military expertise and operational tactics, thereby enhancing China's military capabilities. This situation also mirrors last year's revelation where former pilots from the British Royal Air Force were found to have advised the PLAAF.
READ THE STORY: FP
Winning the Mind Game: The Role of the Ransomware Negotiator
Analyst Comments: The influence of geopolitical factors and recent shifts in targeting strategies are discussed, underscoring the evolving nature of the ransomware landscape. This write-up also emphasizes the importance of implementing a crisis management structure and involving professional negotiators in managing ransomware incidents. The decision to pay the ransom is portrayed as a complex business decision influenced by multiple factors. Practical tips for protecting against ransomware attacks are provided, focusing on the significance of regular software patching, data backups, and strengthening defenses against phishing.
FROM THE MEDIA: The ransomware industry operates as a structured business, with core threat actors developing malware and affiliates distributing it through phishing attacks. Profits are divided between affiliates and developers, primarily targeting online industries. Geopolitical factors can also influence the industry, as seen in the Biden administration's response to recent ransomware attacks. Managing ransomware incidents requires a crisis manager, a decision-making group, law enforcement involvement, and insurance. Professional negotiators play a role in assessing the event, profiling threat actors, evaluating the consequences of not paying the ransom, and setting negotiation goals. The decision to pay or not pay is a business decision influenced by various factors.
READ THE STORY: THN
How US-China tensions shattered Sequoia’s venture capital empire
Analyst Comments: Sequoia's decision to decouple its Chinese operations underscores the increasingly challenging environment for cross-border investments due to geopolitical and trade tensions. The move might signal a shift in the global venture capital landscape as firms reevaluate their exposure to markets seen as politically or economically risky. This could lead to a reshaping of investment strategies, potentially limiting the flow of capital and stifling innovation in certain sectors. It could also prompt Chinese companies to seek funding from domestic or other non-US sources.
FROM THE MEDIA: Sequoia Capital China is separating from its parent US venture capital group Sequoia Capital due to the escalating geopolitical tensions and trade conflicts between the US and China. Sequoia's US and European operations will be split off from the China arm, which will take the name HongShan, and continue managing nearly $56bn in assets. The Indian and Southeast Asian businesses will form a third entity. The decision reflects the growing complexity of investing in China for US institutions, due to regulatory scrutiny and allegations over national security risks. Sequoia China has also faced challenges due to its investments in companies like DJI and ByteDance, which are viewed controversially by the US. The Biden administration is considering an investment-screening mechanism to curb US capital flow into Chinese firms in sensitive sectors such as AI and semiconductors.
READ THE STORY: FT
Kimsuky Targets Think Tanks and News Media with Social Engineering Attacks
Analyst Comments: The activities of Kimsuky highlight the ongoing cybersecurity threats originating from North Korea. With a history of spear-phishing and establishing rapport with targets, Kimsuky demonstrates a commitment to gathering strategic intelligence and accessing sensitive information. This indicates the group's focus on advancing North Korea's geopolitical interests. Additionally, Lazarus Group, another North Korean hacking group, has been observed engaging in financially motivated intrusion campaigns, targeting cryptocurrency exchanges and financial institutions globally. The involvement of multiple North Korean threat actors in different cyber operations demonstrates the diverse motivations and tactics employed by these groups.
FROM THE MEDIA: The North Korean threat actor Kimsuky has been conducting a social engineering campaign targeting experts in North Korean affairs. The group aims to steal Google credentials and deliver reconnaissance malware. By distributing emails that redirect victims to a fake website resembling the legitimate NK News site, Kimsuky lures individuals into entering their login credentials, allowing the group to gain unauthorized access. This recent disclosure follows an alert from US and South Korean intelligence agencies about Kimsuky's social engineering tactics, specifically targeting think tanks, academia, and news media.
READ THE STORY: THN
How US-China tensions shattered Sequoia’s venture capital empire
Analyst Comments: Sequoia's decision to decouple its Chinese operations underscores the increasingly challenging environment for cross-border investments due to geopolitical and trade tensions. The move might signal a shift in the global venture capital landscape as firms reevaluate their exposure to markets seen as politically or economically risky. This could lead to a reshaping of investment strategies, potentially limiting the flow of capital and stifling innovation in certain sectors. It could also prompt Chinese companies to seek funding from domestic or other non-US sources.
FROM THE MEDIA: Sequoia Capital China is separating from its parent US venture capital group Sequoia Capital due to the escalating geopolitical tensions and trade conflicts between the US and China. Sequoia's US and European operations will be split off from the China arm, which will take the name HongShan, and continue managing nearly $56bn in assets. The Indian and Southeast Asian businesses will form a third entity. The decision reflects the growing complexity of investing in China for US institutions, due to regulatory scrutiny and allegations over national security risks. Sequoia China has also faced challenges due to its investments in companies like DJI and ByteDance, which are viewed controversially by the US. The Biden administration is considering an investment-screening mechanism to curb US capital flow into Chinese firms in sensitive sectors such as AI and semiconductors.
READ THE STORY: FT
Deepmind’s AI Is Learning About the Art of Coding
Analyst Comments: This is a significant development in the use of AI for programming. AlphaDev's ability to write new and more efficient algorithms, starting with sorting, demonstrates the potential of AI to optimize routine programming tasks. The application of reinforcement learning, where AI is rewarded for increasing program efficiency, is a promising approach for automating and optimizing code. While the size of the programs AlphaDev can currently handle is small, the progress suggests that AI could contribute to further improvements in code efficiency and possibly generate larger, more complex algorithms in the future.
FROM THE MEDIA: Google's Deepmind has developed an AI system called AlphaDev that can build new algorithms to optimize coding tasks. AlphaDev used reinforcement learning to improve sorting algorithms in the programming language C++, making the execution slightly faster. It created these improvements by writing new algorithms in assembly code, the instructions that act as the interface between high-level programming languages and computer hardware. These new sorting algorithms are up to 1.7% more efficient for long sequences of numbers and 70% faster for five-item sequences. AlphaDev's improvements have been adopted by Libc++, a major open-source library for C++. Daniel Mankowitz, the lead of the sorting project, indicated that AlphaDev is being developed to optimize the entire computing stack.
READ THE STORY: Wired
US to link up with Taiwan and Japan drone fleets to share real-time data
Analyst Comments: The decision to share real-time data from drones between the US, Taiwan, and Japan is a significant development in the geopolitics of the Indo-Pacific. It enhances Taiwan's surveillance and defense capabilities while solidifying cooperation among the US, Taiwan, and Japan. However, it's fraught with potential for tension, given the long-standing issues between Taiwan and China, with the latter viewing any bolstering of Taiwan's defense as a provocation. The enhanced coordination among these nations could serve as a deterrent to potential Chinese aggression, but it could also provoke a response from Beijing, creating additional uncertainty in the region's balance of power.
FROM THE MEDIA: The United States, Taiwan, and Japan have agreed to share real-time data from naval reconnaissance drones in a move aimed at strengthening coordination in the event of a Chinese attack on Taiwan. US defense contractor General Atomics is scheduled to deliver four MQ-9B Sea Guardian drones to Taipei in 2025. These drones can identify, track, and target enemy ships and radars, which could be crucial in a conflict over Taiwan. The data will be integrated into the same system used by US forces and the Japanese Self-Defense Force. This collaboration is viewed as extremely sensitive, due to the US's history with Taiwan and the potential for escalating tensions with China.
READ THE STORY: FT
The Bizarre Reality of Getting Online in North Korea
Analyst Comments: The level of internet censorship in North Korea underscores the regime's intent to suppress the flow of outside information and maintain control over its narrative. Given that international organizations and the UN have declared internet access as a human right, North Korea's policies represent a clear violation of these principles. Achieving universal internet access, however, also depends on factors such as affordability, digital literacy, and overcoming discriminatory barriers. In the case of North Korea, significant political and systemic changes are required to implement such transformations. Increased internet access could potentially improve healthcare, education, and human rights in North Korea, but the regime's current policies and restrictions pose significant obstacles.
FROM THE MEDIA: Research by South Korean human rights organization Pscore reveals the harsh reality of internet access in North Korea. The internet is virtually inaccessible for the majority of the population, with only a few thousand privileged individuals able to access a heavily surveilled and censored version of the global internet. Internet use involves a stringent approval process and constant surveillance, with monitors approving browsing activities every five minutes. Despite an increase in digital devices in the country, the usage of these devices is heavily controlled, with limited data speeds and content restrictions.
READ THE STORY: Wired
Biden taps Senate Intel Committee staff director to lead NCSC
Analyst Comments: Casey's nomination marks a crucial step in the Biden administration's efforts to bolster U.S. counterintelligence capabilities amid growing foreign espionage threats. His deep knowledge of intelligence practices and experience in handling espionage threats, particularly from China, is likely to be pivotal in his new role. If confirmed, Casey's leadership could bring a sharper focus on tackling cyber threats, foreign interference, and other evolving challenges in the intelligence domain.
FROM THE MEDIA: President Joe Biden has announced the nomination of Michael Casey, a longstanding Democratic staff director for the Senate Intelligence Committee, as the director of the National Counterintelligence and Security Center (NCSC). The NCSC, under the Office of the Director of National Intelligence (ODNI), coordinates U.S. counterespionage activities across the 18-member clandestine community. Casey's appointment comes after an acting chief filled the role since Biden's inauguration. Casey's experience in handling intelligence tradecraft and foreign espionage threats from his time at the Intelligence panel could be invaluable in his new role, given the increasing espionage threats from adversaries like China.
READ THE STORY: The Record
South Korea vows support for its chip sector amid China-US tension
Analyst Comments: The proactive approach taken by South Korea indicates the country's acknowledgment of the critical role the semiconductor industry plays in its economy. While it is positive to see that the government is actively engaging with industry leaders to mitigate risks and uncertainties, the geopolitical tension between the U.S. and China places the country in a precarious position. South Korea’s strategy seems to be one of careful navigation between the two superpowers, which is highlighted by their move to maintain cooperation with the U.S. while also trying to avoid a trade dispute with China.
FROM THE MEDIA: South Korean President Yoon Suk Yeol is backing the country's semiconductor industry amidst growing tensions between the U.S. and China. In a meeting with industry leaders and lawmakers, strategies to maintain South Korea's lead in memory chips, develop system semiconductors, and secure necessary resources were discussed. The government's planned support includes promoting R&D, assisting smaller businesses, increasing legal protection for chip technology, and establishing a chip testing facility. South Korea finds itself in a complex situation as its chip manufacturers, Samsung and SK Hynix, depend on both the U.S. for technology and China as a major export market.
READ THE STORY: Reuters
Stealth Soldier Backdoor: Targeted Espionage Attacks in North Africa Linked to Advanced Malware
Analyst Comments: This attack demonstrates an elevated level of sophistication, suggesting a highly skilled and probably politically motivated threat actor. The connection to the "Eye on the Nile" campaign indicates that the operation could be part of a broader and more extensive campaign than initially identified. With its modular nature and continued updates, it's likely that Stealth Soldier will persist and evolve, posing a significant threat to targets in the region. Given the stealthy and complex nature of the infection process, traditional cybersecurity measures may not be sufficient to detect or prevent such threats. Therefore, entities, particularly in the targeted region, must bolster their cybersecurity defenses, stay vigilant to potential spear-phishing attempts, and ensure up-to-date threat intelligence to prevent infection.
FROM THE MEDIA: Check Point Research has identified an espionage operation targeting Libya, employing a new custom modular backdoor malware called "Stealth Soldier". The malware enables surveillance operations such as keystroke logging, screen and microphone recording, and stealing browser data. It also revealed a connection with a previous operation called "The Eye on the Nile" which targeted Egyptian civilians in 2019. The attack appears to be highly targeted, involving complex infection chains and continues to be updated, with the latest version found being Version 9, delivered in February 2023. Check Point also discovered that the threat actor is using a network of phishing domains, which often impersonate sites belonging to the Libyan Foreign Affairs Ministry.
READ THE STORY: Checkpoint
Lazarus, North Korean Hacking Group, Tied to Atomic Wallet Cryptocurrency Theft
Analyst Comments: This incident highlights the persistent threat posed by state-sponsored cybercriminals such as the Lazarus Group. Given North Korea's international isolation and sanctions, it's likely these cyber-attacks serve as a key revenue source for the regime. The group's repeated success in stealing substantial amounts from digital platforms raises serious questions about the security of cryptocurrency exchanges and wallets. The exact attack details remain unclear, with some speculating a bug exposed users' private keys, emphasizing the need for robust security measures and continuous software auditing in the crypto industry.
FROM THE MEDIA: North Korean hacker collective, Lazarus Group is suspected to be behind the recent $35 million cryptocurrency theft from the decentralized wallet platform, Atomic Wallet. According to blockchain analytics firm Elliptic, less than 1% of Atomic Wallet's 5 million global users were affected by the hack. The attack was attributed to the Lazarus Group due to the similar techniques used in their past attacks, such as laundering stolen assets via services like the Sinbad mixer. This theft is notable because of its size and it is the first significant crypto theft publicly linked to the Lazarus Group since a $100 million attack on Horizon Bridge in June 2022.
READ THE STORY: The Record
US takes aim at China Over Latin America trade tactics and fentanyl role
Analyst Comments: This incident highlights the persistent threat posed by state-sponsored cybercriminals such as the Lazarus Group. Given North Korea's international isolation and sanctions, it's likely these cyber-attacks serve as a key revenue source for the regime. The group's repeated success in stealing substantial amounts from digital platforms raises serious questions about the security of cryptocurrency exchanges and wallets. The exact attack details remain unclear, with some speculating a bug exposed users' private keys, emphasizing the need for robust security measures and continuous software auditing in the crypto industry.
FROM THE MEDIA: CSC 2.0, a congressionally mandated group of experts has released a report stating that US government policies and agencies tasked with protecting critical infrastructure against cyber threats are outdated and inadequate. The report highlights the shortcomings of current policies in light of recent cyberattacks on critical infrastructure, such as the Colonial Pipeline ransomware attack. It criticizes the public-private partnership model and points out the limitations of the Cybersecurity and Infrastructure Security Agency (CISA) in facilitating rapid response to cyberattacks. The report emphasizes the need for an updated policy directive and a systemic and holistic approach to address evolving cybersecurity risks and technologies. It also highlights the inconsistencies and gaps within federal agencies and calls for improved leadership, resources, and coordination among sector-specific agencies.
READ THE STORY: Cyberscoop
The Future Of Cyber Espionage, The Uncomfortable Truth In The Near And Distant Future
Analyst Comments: The U.S.' criticism of China reflects increasing geopolitical tensions and competition for influence in Latin America. China's significant investments in the region may challenge U.S. influence, which likely drives the push for a viable U.S. alternative. However, this strategy will depend on the U.S. capacity to provide appealing and substantial economic and diplomatic incentives. The focus on the fentanyl crisis emphasizes a critical public health issue and security concern for the U.S., linking it directly to China's lack of control over precursor chemicals. These allegations heighten the stakes for China's response and cooperation.
FROM THE MEDIA: Senior U.S. policymakers, including Brian Nichols, assistant secretary of state for Western Hemisphere Affairs, and Todd Robinson, assistant secretary of state for International Narcotics and Law Enforcement Affairs, criticized China's commercial approach to Latin America, claiming it lacks transparency and often involves manipulative conditions. Nichols suggested that Latin American countries are experiencing "buyer's remorse" over China's investment tactics and that the U.S. needs to present an alternative through diplomacy, aid, and private investment. They also accused China of not doing enough to combat the illegal fentanyl trade, stating that most fentanyl seized in the U.S. comes from Mexico, using precursor chemicals sourced from China.
READ THE STORY: Reuters
Beijing proposes rules to stop Wi-Fi and Bluetooth networks from going rogue
Analyst Comments: The proposed regulations represent an intensification of Beijing's control over digital communication and information dissemination. This move suggests an intent to regulate every facet of the internet within China, ensuring it aligns with Communist Party values. The requirement for real identity disclosure could deter free speech and privacy, leading to self-censorship. While the specifics are not entirely clear – particularly around the impact on domestic Wi-Fi points and the inclusion of Bluetooth networks – it seems evident that China is tightening its grip on its digital landscape. The implications for individual privacy and freedom of expression could be significant, depending on how these rules are enforced. It also signals further challenges for foreign tech companies operating in China, as they must navigate an increasingly controlled and scrutinized digital environment.
FROM THE MEDIA: China's Cyberspace Administration (CAC) has proposed new regulations for operators of Bluetooth and Wi-Fi networks to adhere to politically correct standards as defined by Beijing. Announced on Tuesday, these regulations aim to prevent the spread of non-socialist values or any deviation from existing laws. Network operators will be expected to resist and report any use of their equipment for spreading what Beijing labels as fake news. The guidelines also require users of these networks to provide their real identities and consent to any information sent over the networks.
READ THE STORY: The Register
Foreign Interference: France Bad Student In The “Informational War”
Analyst Comments: The report suggests that French political life is unprepared to confront the significant challenge of foreign interference, particularly from nations like Russia. This lack of preparedness may be due to a mixture of naivety and possible complicity within certain political factions. The recognition of this gap represents an essential first step in addressing the issue. The report's findings may likely prompt France to review its counter-interference strategies and bolster its defenses against such threats. Increased awareness of foreign interference may lead to a broader discussion about how to combat this problem effectively, possibly leading to new regulations, legislation, or collaborative efforts with international partners.
FROM THE MEDIA: The final report from a parliamentary commission examining foreign interference in French politics has revealed a significant gap in the country's understanding of this critical issue. Published on June 8, the report has primarily highlighted internal disputes within French politics, but it also underscores a lack of awareness in France about the extent and severity of foreign interference, which it attributes to both naivety and collusion. The report suggests that this issue is particularly crucial concerning Russia, which it identifies as the most significant source of interference threats to Western democracies. The commission suggests that Moscow is engaged in an "information warfare" strategy aimed at destabilizing Western countries.
READ THE STORY: Globe Echo
Combating the cyber heists that are costing the global economy
Analyst Comments: The global community's struggle against economic cyber espionage underlines the complexity of managing cyber threats in an increasingly digitized world. Efforts to counter this threat will require both domestic and international cooperation and capacity building. Governments and organizations should invest in stronger cybersecurity measures, while international bodies should work to enforce and strengthen agreements that discourage state-sponsored cyber espionage.
FROM THE MEDIA: The global community is struggling to combat the growing threat of economic cyber espionage, where states use digital technology to steal intellectual property for commercial advantage. Despite the 2015 agreement by G20 leaders to refrain from such activities, there's been an increase in the number, severity, and scale of cyber espionage cases worldwide. The primary difficulty in countering this threat lies in the ability to accurately attribute attacks to specific actors due to the covert nature of these operations. Advanced persistent threats (APTs), typically indicative of state-backed cyber operations, add to the complexity due to blurred boundaries between states and criminal gangs. Beyond merely attributing the attacks, building resilience against them also involves investing in domestic cybersecurity capacity and national IP systems. The increase in state-sponsored cyber operations targeting developing economies demands enhanced efforts to counter this threat.
READ THE STORY: ASPI
The Terrifying Truth Behind its Revised Counter-Espionage Law
Analyst Comments: The revised Counter-Espionage Law significantly widens the net of potential activities that could be deemed as espionage in China. The added scope for "protecting the people's interests" and the broad "holistic view of national security" give authorities wider discretion in pursuing anti-espionage investigations. The new definitions could potentially target foreign companies, organizations, and individuals conducting seemingly innocuous activities. This development further complicates the already challenging environment for foreign businesses in China and heightens the risk of operating in the country.
FROM THE MEDIA: On April 26, the National People's Congress of China passed amendments to its Counter-Espionage Law, set to come into effect from July 1. Notably, the law has expanded its purpose to include "protecting the people's interests," broadening its scope significantly beyond just preserving national security. The revisions also introduce the principle of a "holistic view of national security," a concept that expands the notion of security to include various fields like politics, economics, culture, science and technology, and natural resources and energy. A key change is in Article 4, which redefines espionage, no longer limiting it to dealing with "state secrets" but extending it to "other documents, data, materials, or items related to national security." This change can potentially label ordinary business activities, including data collection for business purposes or procuring product samples, as espionage.
READ THE STORY: Japan Forward
Items of interest
US needs an AI Czar to help regulate risky technology, ex-Google CEO Eric Schmidt says
Analyst Comments: Schmidt's comments reflect growing concerns in the tech industry about the global regulation of AI, its implications for national security, and the potential risks posed by AI in various sectors. His specific criticism of the EU's approach suggests a perception that overly restrictive regulations could hinder technological progress. However, his call for a focused problem-solving approach and the establishment of an AI Czar indicates that he acknowledges the need for robust oversight and regulatory frameworks. Schmidt's concerns about AI-driven misinformation and privacy threats highlight the ethical and societal challenges posed by AI, emphasizing the importance of creating adaptable, future-focused policies to ensure its responsible use.
FROM THE MEDIA: Former Google CEO, Eric Schmidt, criticized the current handling of AI regulation by governments in a panel discussion. Schmidt highlighted the potential of AI to cause substantial harm in the future and suggested that governments often focus on irrelevant AI threats. He particularly criticized the European Union's pending EU AI Act for being overly restrictive. Schmidt recommended that the U.S. define clear problems associated with AI and then work on solving those problems, suggesting the creation of an AI Czar to facilitate this process. He highlighted the dysfunction in the U.S. government's approach to AI's national security implications, mentioning the military's risk aversion and funding conflicts with Congress.
READ THE STORY: The Record
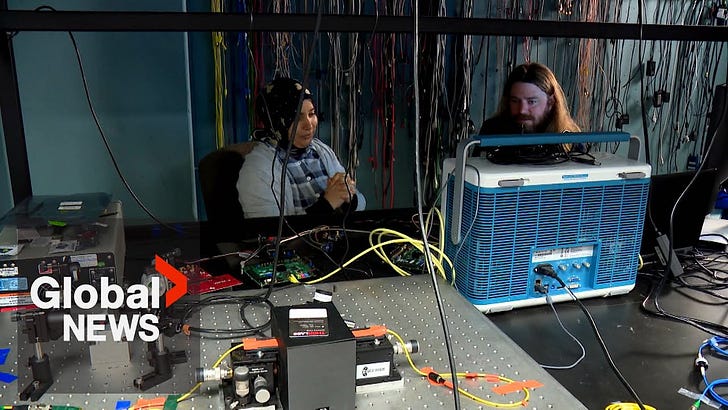
Quantum computing: Exploring the dangers and possibilities in the age of AI (Video)
FROM THE MEDIA: The University of Calgary's Quantum Hub is working on reducing these issues by creating a stable environment at extremely low temperatures. Quantum computing challenges traditional computing rules and offers both significant advantages and threats. Current encryption methods used in classical computers will become insecure, prompting researchers to race against time to crack the quantum code and develop new models of quantum security.
The Path to Getting Real-Time AI Right (Video)
FROM THE MEDIA: How can all types of businesses overcome challenges when it comes to adopting AI? And what's the best path for launching a real-time AI strategy? AI experts Shawn Rogers, Scott Burk, and Davor Bonaci discuss this on LinkedIn Live.
These open-source products are reviewed by analysts at InfoDom Securities, providing possible context about current media trends related to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not endorse any third-party claims made in their original material or related links on their sites; the opinions expressed by third parties are theirs alone. For further questions, please contact InfoDom Securities at dominanceinformation@gmail.com.