Daily Drop (500): Taiwan's Silicon Power Defense, Russia's Grid-Harming Malware, Zero-Day Breach Warning, China's Tech Industry Transformation, UK's Semiconductor Success Foundation, Intel Poss. Cuts
05-26-2023
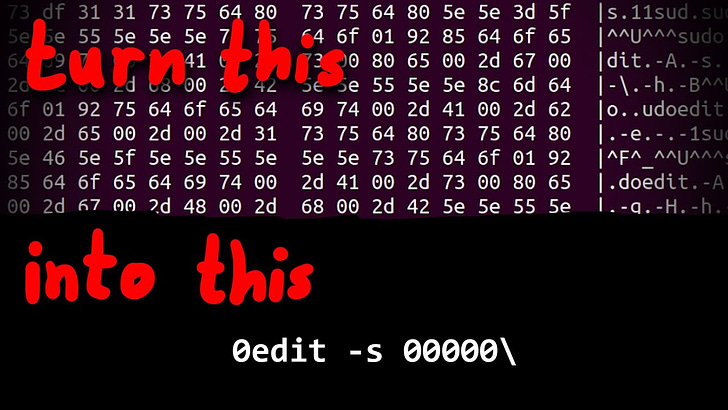
Friday, May 26, 2023 // (IG): BB // Intro Exploit Dev // Coffee for Bob
The Crucial Role of Taiwan's Silicon Semiconductor Production in Deterring a Mainland China Takeover
Analyst Comments: The significance of Taiwan's silicon semiconductor production in deterring a mainland China takeover is effectively conveyed in the article. It highlights the critical role played by semiconductors across various industries and underscores Taiwan's position as a key player in the sector. The article provides valuable insights into the historical context, the current state of Taiwan's semiconductor industry, and potential deterrence strategies. While acknowledging different viewpoints on the effectiveness of certain approaches, the article emphasizes the importance of maintaining the status quo to safeguard Taiwan's security and ensure global economic stability.
FROM THE MEDIA: Taiwan's silicon semiconductor production plays a crucial role in protecting the country from a potential mainland China takeover. Dr. Miin Wu, a prominent figure in Taiwan's semiconductor industry, is highlighted for his contribution to establishing Taiwan as a major global supplier of advanced semiconductors. With Taiwan supplying over 90% of advanced chips worldwide, the article argues that the reliance of both China and the United States on Taiwanese semiconductor manufacturing acts as a deterrent against a Chinese invasion. The concept of a "silicon shield" is discussed, underscoring the significant geopolitical ramifications that would arise from disruptions in Taiwan's semiconductor industry. The article also touches on Taiwan's efforts to strengthen its defense capabilities and the potential consequences of an invasion of the global semiconductor supply chain.
READ THE STORY: The Monthly
Ukraine is already looking to a postwar digital future
Analyst Comments: Ukraine's DIIA app demonstrates the country's progress in digital innovation and government digitization. The widespread adoption of DIIA and its potential for export highlight Ukraine's capacity for technological advancement and resilience, even in the face of conflict and economic challenges. The app's success not only improves efficiency but also addresses corruption by providing a transparent and accountable governance system. DIIA represents a shift in the traditional innovation paradigm, where emerging countries are now capable of producing groundbreaking solutions that can be adopted globally. The app's success may also contribute to Ukraine's vision of becoming a tech hub and attracting foreign investments. However, the ongoing conflict and geopolitical challenges in the region may hinder immediate progress in terms of investment.
FROM THE MEDIA: Ukraine's digital innovation, known as DIIA, has gained significant traction since its launch three years ago. The app, which enables citizens to perform private sector and government services on their phones, is installed on 70% of Ukrainian phones, with 19 million citizens regularly accessing its services. DIIA offers a range of functions, including a digital passport, digital driving licenses, tax payments, digital signatures, and even features that teach Ukrainians how to fly drones and report the activities of Russian troops. The success of DIIA has attracted international attention, with countries like Estonia, Zambia, Kosovo, and Colombia considering importing the app's code. The US Agency for International Development (USAID) is also working to export DIIA and sees it as a model of government digitization that could be emulated in other countries.
READ THE STORY: FT
Zyxel Issues Critical Security Patches for Firewall and VPN Products
Analyst Comments: The discovery of critical buffer overflow vulnerabilities in Zyxel's firewall and VPN products highlights the importance of regularly updating and patching network infrastructure devices. The remote code execution capabilities of these vulnerabilities pose significant risks to organizations' security. Promptly applying the software updates provided by Zyxel is crucial to mitigate the threat. The involvement of threat actors associated with the Mirai botnet in actively exploiting the previously fixed vulnerability indicates the potential for widespread attacks targeting vulnerable Zyxel devices.
FROM THE MEDIA: Zyxel has released software updates to address two critical buffer overflow vulnerabilities, CVE-2023-33009 and CVE-2023-33010, affecting select firewall and VPN products. The vulnerabilities could be exploited by remote attackers to cause denial-of-service (DoS) conditions and achieve remote code execution. The impacted devices include ATP, USG FLEX, USG FLEX50(W) / USG20(W)-VPN, VPN, and ZyWALL/USG models. Security researchers from TRAPA Security and STAR Labs SG discovered and reported the flaws. This advisory follows Zyxel's recent fixes for another critical security flaw, CVE-2023-28771, which also allowed remote code execution on affected systems and was actively exploited by threat actors associated with the Mirai botnet.
READ THE STORY: THN
New Russia-linked malware can physically harm power grids, Mandiant reports
Analyst Comments: The discovery of CosmicEnergy malware targeting critical infrastructure systems underscores the ongoing risks faced by such industries and the potential for cyberattacks to cause significant disruptions. The similarities with Industroyer and the connection to Rostelecom's Solar Polygon project suggest a potential link to Russian threat actors. The ability of hackers to repurpose such malware and target existing critical infrastructure facilities highlights the importance of robust cybersecurity measures and ongoing vigilance within these sectors. It is crucial for organizations to prioritize the protection of their infrastructure and implement strong security protocols to mitigate the risk of attacks. The targeting of communication protocols and the reliance on insecure design features in industrial environments pose long-term challenges, requiring industry-wide efforts to address vulnerabilities and enhance cybersecurity practices.
FROM THE MEDIA: Security researchers at Mandiant have discovered a new malware named CosmicEnergy, which appears to be designed to disrupt and damage critical infrastructure systems, including power grids. The malware shares similarities with Industroyer, which was used by Russia to attack Ukraine's energy infrastructure in 2016 and 2022. Mandiant researchers found a comment in the code linking the malware to Rostelecom's "Solar Polygon" project, aimed at training cybersecurity specialists and safeguarding Russia's banking, energy, and oil infrastructure. Although the exact origin and purpose of CosmicEnergy remain unclear, the discovery raises concerns as hackers could repurpose the malware to target existing critical infrastructure facilities. The malware targets a communication protocol used in the electric power industry and possesses disruption tools called PieHop and LightWork.
READ THE STORY: The Record // THN
Building a Foundation for Semiconductor Success: The UK's Path to Innovation and Growth
Analyst Comments: The commitment of up to £1 billion over the next decade demonstrates the government's recognition of the importance of the semiconductor sector and its willingness to invest in its future. This funding will support infrastructure development, research and development initiatives, and international collaboration, serving as a catalyst for innovation and commercialization. The government's collaborative approach, working alongside industry, is commendable as it acknowledges the crucial role of public-private partnerships in driving progress and ensuring the successful implementation of the strategy. The initiatives outlined in the strategy, such as the creation of the UK Semiconductor Advisory Panel and the incubator pilot program, demonstrate a comprehensive and holistic approach to supporting the semiconductor industry. By bringing together key stakeholders and addressing challenges faced by start-ups, the strategy seeks to create an enabling environment for growth and foster a vibrant semiconductor ecosystem.
FROM THE MEDIA: The UK government has unveiled its National Semiconductor Strategy, a comprehensive plan aimed at leveraging the country's existing strengths in semiconductors to bolster the sector, enhance resilience, and safeguard national security. Published by the Department for Science, Innovation, and Technology, the strategy charts a course for the UK to attain a global leadership position in future semiconductor technologies over the next two decades. It emphasizes key areas of expertise such as intellectual property and design, compound semiconductors, and research and development. To support the strategy, the UK government has pledged to invest up to £1 billion over the next ten years. This funding will be channeled into bolstering infrastructure, driving research and development initiatives, and fostering international collaboration. For the initial phase spanning 2023 to 2025, an allocation of up to £200 million has been earmarked. By partnering with industry, the government's investment aims to catalyze research, innovation, and commercialization, facilitating the transition of cutting-edge semiconductor technologies from the laboratory to the marketplace.
READ THE STORY: FT
New Russia-linked malware can physically harm power grids, Mandiant reports
Analyst Comments: The discovery of CosmicEnergy malware targeting critical infrastructure systems underscores the ongoing risks faced by such industries and the potential for cyberattacks to cause significant disruptions. The similarities with Industroyer and the connection to Rostelecom's Solar Polygon project suggest a potential link to Russian threat actors. The ability of hackers to repurpose such malware and target existing critical infrastructure facilities highlights the importance of robust cybersecurity measures and ongoing vigilance within these sectors. It is crucial for organizations to prioritize the protection of their infrastructure and implement strong security protocols to mitigate the risk of attacks. The targeting of communication protocols and the reliance on insecure design features in industrial environments pose long-term challenges, requiring industry-wide efforts to address vulnerabilities and enhance cybersecurity practices.
FROM THE MEDIA: Security researchers at Mandiant have discovered a new malware named CosmicEnergy, which appears to be designed to disrupt and damage critical infrastructure systems, including power grids. The malware shares similarities with Industroyer, which was used by Russia to attack Ukraine's energy infrastructure in 2016 and 2022. Mandiant researchers found a comment in the code linking the malware to Rostelecom's "Solar Polygon" project, aimed at training cybersecurity specialists and safeguarding Russia's banking, energy, and oil infrastructure. Although the exact origin and purpose of CosmicEnergy remain unclear, the discovery raises concerns as hackers could repurpose the malware to target existing critical infrastructure facilities. The malware targets a communication protocol used in the electric power industry and possesses disruption tools called PieHop and LightWork.
READ THE STORY: The Record
Xi's Crackdown Transforms China's Tech Industry in His Image
Analyst Comments: Xi's influence on China's tech industry has been substantial, with notable transformations observed in various sectors. The focus on maintaining China's lead in electronics manufacturing has led to significant wealth accumulation in hardware companies. However, the semiconductor sector has faced challenges, and the internet sector has been subjected to regulatory crackdowns and disruptions. The divergence in market valuations between internet giants and hardware/semiconductor companies underscores the contrasting trajectories of these sectors. The emphasis on R&D reflects Xi's goal of achieving self-reliance and technological innovation. Hardware companies have been at the forefront of research expenditure, while internet companies have also made substantial investments. Fundamental research is expected to play a crucial role in China's tech war with the US.
FROM THE MEDIA: Chinese leader Xi Jinping has used policy, capital, and direct decrees to reshape China's technology industry in alignment with his vision. While he has prioritized science, technology, and research and development (R&D), his crackdown on the internet sector and challenges in the semiconductor industry have raised questions about the future direction of China's tech landscape. The hardware sector has seen significant growth in wealth and the emergence of unicorns, while the semiconductor industry has faced obstacles. R&D has become a focal point, with both hardware and internet companies investing heavily in research.
READ THE STORY: Bloomberg
New Russia-linked malware can physically harm power grids, Mandiant reports
Analyst Comments: The move by Ukraine to classify cyberattacks as war crimes and present evidence to the ICC reflects the country's determination to address the impact of cyber warfare on civilian and critical infrastructure. By seeking international recognition of cyberattacks as part of Russia's hybrid warfare strategy, Ukraine hopes to establish a legal framework for holding perpetrators accountable. However, achieving this goal will require strong political will and international cooperation.
FROM THE MEDIA: Ukraine is seeking to classify cyberattacks against civilian and critical infrastructure as war crimes and present evidence to the International Criminal Court (ICC) in The Hague. Cybersecurity experts in Ukraine argue that the ongoing cyberattacks, combined with kinetic and information attacks, demonstrate the need for international recognition of cyberattacks as part of Russia's hybrid warfare strategy. They believe that the ICC should classify cyberattacks as a component of Russia's war machine. Ukraine is also strengthening its legislation around cybersecurity and critical infrastructure protection, aiming to enhance cyber defense and information sharing to prevent and respond to cyberattacks.
READ THE STORY: DARKReading
Barracuda Warns of Zero-Day Exploited to Breach Email Security Gateway Appliances
Analyst Comments: The disclosure of the zero-day vulnerability in Barracuda's ESG appliances highlights the ongoing risks associated with email security and underscores the need for timely patching and vulnerability management. The active exploitation and unauthorized access to a subset of email gateway appliances indicate a significant security incident for Barracuda customers. Organizations using the affected ESG versions should apply the patches and follow the remedial actions provided by Barracuda to mitigate the risk.
FROM THE MEDIA: Barracuda, an email protection and network security services provider, has disclosed a zero-day vulnerability, CVE-2023-2868, that has been exploited to breach its Email Security Gateway (ESG) appliances. The vulnerability allows remote code injection through the processing of .tar files, potentially leading to the execution of system commands with the privileges of the ESG product. Barracuda released a patch to address the vulnerability and has notified affected users with remedial actions. The company also reported evidence of active exploitation but did not disclose the scale of the attack. The threat actors behind the attack are currently unknown. In a separate development, Defiant has alerted users to large-scale exploitation of a fixed cross-site scripting (XSS) flaw in the Beautiful Cookie Consent Banner plugin used on over 40,000 sites, leading to site takeovers and malvertising attacks.
READ THE STORY: THN
US Embassy in Cuba Currently Leases Chinese Electric Vehicles, Aims to Promote American Brands
Analyst Comments: The decision by the US embassy in Havana to rent Chinese electric cars highlights the dominance of Chinese companies in Cuba's electric vehicle market. Despite efforts by the Biden administration to support American companies, China has already established itself as Cuba's leading trading partner and has built an assembly plant for electric vehicles in the country. The slow progress of US companies in exporting electric cars to Cuba and the embassy's rental of Chinese models reflect the challenges faced by American companies in competing with China's economic presence. The lack of American-made electric cars in Cuba and the country's limited infrastructure for supporting electric vehicles pose significant barriers to the widespread adoption of electric transportation.
FROM THE MEDIA: The Biden administration has allowed a US company to sell electric cars to Cuba as a means to support the island's private sector. However, bureaucratic requirements have slowed down the process, and cheaper Chinese electric car models are already available for rent in Cuba. Surprisingly, the US embassy in Havana is renting Chinese-made electric cars due to the lack of American-made options on the island. China has already established a larger economic presence in Cuba, with Chinese companies being granted preferential treatment. While the US embassy plans to transition to American-made electric vehicles in the future, the availability of charging infrastructure and the affordability of electric cars remain significant challenges in Cuba.
READ THE STORY: Miami Herald
Intel mulls cutting ties to 16 and 32-bit support
Analyst Comments: Intel's proposal to simplify the x86 architecture by removing outdated features reflects the company's aim to optimize future processors and streamline system startup. By eliminating 16-bit and certain 32-bit support, Intel aims to create a more efficient architecture that directly boots into x86-64 mode. This move may not have a significant impact on average users, as most modern operating systems primarily operate in ring zero and ring three. The removal of support for older operating systems and software may not be noticeable for the majority of users who rely on 64-bit systems and applications. While Intel's proposal suggests a departure from its traditional focus on backward compatibility, it aligns with the industry trend of optimizing hardware for modern technologies and performance.
FROM THE MEDIA: Intel has proposed a potential simplification of the x86 architecture by introducing a new x86S architecture that removes certain features, including 16-bit and some elements of 32-bit support. The goal is to streamline the design of future processors and the startup process of PCs. The proposed changes would allow processors to boot directly into x86-64 mode, eliminating the need for transitional modes during startup. While the impact on most users may be invisible, the move signifies a departure from Intel's long-standing commitment to backward compatibility.
READ THE STORY: The Register
Keep reading with a 7-day free trial
Subscribe to Bob’s Newsletter to keep reading this post and get 7 days of free access to the full post archives.