Daily Drop (493): Russian Cyber Operations, Vesuvius: £3.5M Cyber, IT Worker Jailed for Pro-Uk, China's Kazakhstan Adv, 8220 Gang Exploits Oracle, Minimizing Manufacturing Attack Surface
05-19-2023
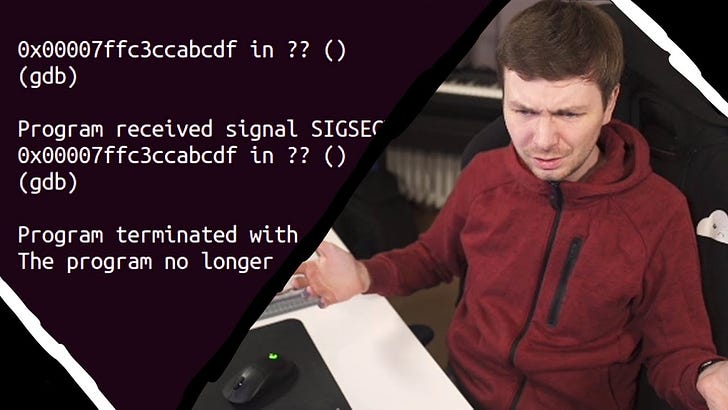
Friday, May 19, 2023 // (IG): BB // Intro Exploit Dev // Coffee for Bob
Turla Disrupted: What Does That Mean for Russian Cyber Operations?
Analyst Comments: The disruption of the Turla cyber espionage group is a significant achievement, as it dismantles one of the most sophisticated and long-running cyber operations attributed to Russia. The multinational effort and collaboration among intelligence agencies highlight the importance of coordination in countering state-sponsored cyber threats. However, it is expected that Turla will adapt and continue its operations, potentially adopting more decentralized networks and creating backup infrastructures. The operation serves as a warning to Russia that its cyber activities are being closely monitored and countered by allied countries. The ongoing cyber battle between the West and Russia is likely to continue, with Turla regrouping and potentially becoming even more dangerous in the future.
FROM THE MEDIA: The US Justice Department, along with allied countries, conducted Operation MEDUSA to disrupt the Turla cyber espionage group, which has been operating for nearly 20 years. Turla, attributed to Russia's Federal Security Service's 16th Center, has targeted high-value organizations in at least 50 countries, including government institutions and media. The Snake malware used by Turla is highly sophisticated and has been consistently updated since 2003. The operation required a multilateral effort and cooperation from Five Eyes intelligence and law enforcement partners. While the disruption is a significant blow to Turla, it is expected that the group will re-tailor its operations in response. The operation demonstrates the effectiveness of collaboration among intelligence agencies and sends a message to Russia about the coordinated efforts against state-sponsored cyber activities.
READ THE STORY: OODALOOP
UK steel industry supplier Vesuvius says ‘cyber incident’ cost £3.5 million
Analyst Comments: The article highlights the financial impact of a cyber incident on engineering company Vesuvius, with the episode projected to cost £3.5 million. The nature of the incident has not been disclosed, but the company remains optimistic about its trading performance. The report also mentions a similar incident experienced by another industrial ceramics manufacturer, Morgan Advanced Materials. These incidents underscore the financial and reputational risks associated with cyber-attacks and the need for organizations to invest in robust cybersecurity measures to mitigate potential damages.
FROM THE MEDIA: Engineering company Vesuvius has revealed that a cyber incident it experienced earlier this year will cost the company £3.5 million ($4.6 million). The nature of the incident has not been disclosed, but the company stated that despite the episode, it had exceeded trading expectations. Vesuvius is one of the 350 most valuable businesses listed on the London Stock Exchange and employs over 10,000 people. The company's shares rose 3% following the announcement. Another British industrial ceramics manufacturer, Morgan Advanced Materials, also reported a cyber incident in January, which could cost the company up to £12 million.
READ THE STORY: The Record
Russian IT worker jailed for participating in pro-Ukraine DDoS attacks
Analyst Comments: The sentencing of Kotikov highlights the Russian government's crackdown on individuals involved in DDoS attacks against Russian targets in support of Ukraine. The case demonstrates the authorities' efforts to deter Russians from supporting the Ukrainian cause, particularly in cyberspace. The involvement of individuals in such attacks remains a challenge for authorities, as they are seen as low-hanging fruit and easier to apprehend compared to the infrastructure used for DDoS attacks. The targeting of Kotikov serves as a warning to others who may perceive participating in DDoS attacks as a means to confront the government. The incident reflects the ongoing tensions between Russia and Ukraine in both physical and digital realms, with each side accusing the other of cyberattacks and interference.
FROM THE MEDIA: An IT worker named Yevgeny Kotikov has been sentenced to three years in prison by a Russian regional court for participating in distributed denial-of-service (DDoS) attacks against Russian government websites in support of Ukraine. Kotikov was found guilty of targeting the Ministry of Defence and the website of the Russian president. The Federal Security Service (FSB) stated that Ukraine had organized the DDoS attacks and confiscated Kotikov's personal computer. He was fined 800,000 rubles (approximately $10,000) and sentenced to a "colony-settlement," which is a less strict form of imprisonment for first-time offenders. The severity of the sentence is seen as a deterrent against Russians supporting Ukraine, even in cyberspace.
READ THE STORY: The Record
China Makes Inroads into Kazakhstan
Analyst Comments: The article highlights China's growing influence in Central Asia, particularly in Kazakhstan, amid the Russia-Ukraine crisis. The expansion of economic cooperation, signing of significant agreements, and investments demonstrate China's efforts to strengthen bilateral relations and expand its presence in the region. The expansion of the Kazakhstan-China oil pipeline and the establishment of a logistics center at Xi'an Dry Port is indicative of China's economic ambitions and its aim to enhance trade connectivity. The upcoming China-Central Asia Summit further underscores China's engagement and growing influence in the region.
FROM THE MEDIA: During the Russia-Ukraine crisis, China has made significant strides in strengthening its relations with Central Asian countries. Kazakhstan, in particular, has expanded its economic cooperation with China, resulting in stronger bilateral ties. The two countries signed 47 agreements worth $22 billion, and China has become one of the top five investors in the Kazakh economy with a total investment of $23 billion. The expansion of the Kazakhstan-China oil pipeline, estimated to cost $200 million, will boost Kazakhstan's oil exports and increase throughput capacity. Additionally, construction has begun on a logistics center at Xi'an Dry Port, which will facilitate trade between the two countries and enhance cooperation. The China-Central Asia Summit, to be held in Xi'an, will involve leaders from Kazakhstan, Kyrgyzstan, Tajikistan, Turkmenistan, and Uzbekistan, further cementing China's engagement in the region.
READ THE STORY: Modern Diplomacy
How to Reduce Exposure to the Manufacturing Attack Surface
Analyst Comments: The article highlights the growing cybersecurity risks faced by the manufacturing sector due to the convergence of OT and IT. The shift towards ransomware attacks and stolen credential attacks reflects the changing tactics of cybercriminals. Manufacturers, driven by the need for uninterrupted operations, need to prioritize cybersecurity measures to protect against potential attacks. The recommended steps, such as regular testing, automation, adversarial perspective, prioritized patching, and benchmarking, provide a comprehensive approach to improving cybersecurity posture. The emphasis on automation and the use of industry-standard frameworks demonstrates the need for efficiency and adherence to best practices. Manufacturers should consider adopting automated security validation programs to gain real-time insights into their attack surface and address vulnerabilities effectively.
FROM THE MEDIA: The convergence of Operational Technology (OT) and Information Technology (IT) in the manufacturing sector has led to increased productivity but also increased cybersecurity risks. Ransomware attacks and stolen credential attacks have become prevalent in the manufacturing sector, with downtime being a major concern for manufacturers. However, many manufacturing companies are not adequately prepared to handle cyber attacks, with a significant number scoring low in security assessments. Recent high-profile incidents have highlighted the crippling effects of ransomware attacks on manufacturers. To reduce exposure to cyber attacks, manufacturers are advised to regularly test and assess their networks, automate security processes, take an adversarial perspective to identify vulnerabilities, prioritize patching based on actual risk, and benchmark their security posture.
READ THE STORY: THN
US Lawmakers Issue Dire Warnings on China Competition
Analyst Comments: The hearings underscore the growing concern in the U.S. about China's economic practices and their impact on global trade and security. The discussions suggest a bipartisan consensus on the need to counter China's economic aggression. However, the effectiveness of any proposed measures will depend on a range of factors, including the willingness of U.S. allies to cooperate, the ability of the U.S. to leverage its own economic power, and China's response. The hearings also highlight the ongoing debate about the best ways to protect U.S. intellectual property and ensure fair competition in global markets.
FROM THE MEDIA: This week, two U.S. House committees held hearings to discuss the impact of China's use of economic power against the U.S. and its allies and to consider countermeasures. Witnesses testified about China's use of economic might to coerce smaller countries into favorable trade arrangements and to force businesses to surrender intellectual property. They also discussed China's broader ambition to become a globally dominant economic player. Robert Lighthizer, former U.S. Trade Representative, stated that the Chinese Communist Party has been waging an economic war against the U.S. for decades.
READ THE STORY: VOA
8220 Gang Exploiting Oracle WebLogic Flaw to Hijack Servers and Mine Cryptocurrency
Analyst Comments: The article highlights the activities of the 8220 Gang, a crypto jacking group that exploits an old vulnerability in Oracle WebLogic servers to distribute cryptocurrency mining malware. The gang's tactics include scanning for vulnerable hosts and employing SSH brute force attacks for lateral movement. By leveraging the WebLogic vulnerability, the group manages to disable security measures and retrieve payloads from remote servers. The misuse of legitimate tools, such as lwp-download, adds to the challenge of detecting and blocking these attacks.
FROM THE MEDIA: The 8220 Gang, a notorious crypto jacking group, has been exploiting a six-year-old security flaw in Oracle WebLogic servers to distribute cryptocurrency mining malware. The vulnerability, known as CVE-2017-3506, allows unauthorized remote execution of arbitrary commands. The group, previously documented by Cisco Talos, scans the internet for vulnerable hosts and employs SSH brute force attacks for lateral movement within compromised networks. The recent attack chain involves leveraging the WebLogic vulnerability to deliver a PowerShell payload, which in turn creates an obfuscated PowerShell script to disable Windows Antimalware Scan Interface (AMSI) detection and retrieve a payload from remote servers. The gang also misuses the legitimate Linux tool lwp-download to save arbitrary files on compromised hosts. Trend Micro warns that the group's tendency to reuse tools and abuse legitimate utilities poses challenges for detection and blocking solutions.
READ THE STORY: THN
Malicious emails aimed at Taiwan have spiked in 2023
Analyst Comments: The increase in cyberattacks targeting Taiwan is likely linked to the escalating geopolitical tensions between Taiwan and China. Chinese officials have made forceful statements asserting China's sovereignty over Taiwan, which has contributed to an already tense atmosphere. The phishing attacks observed by Trellix bear the hallmarks of state-sponsored groups, using sophisticated malware and tactics. The targeted sectors indicate an interest in gaining access to sensitive information and intellectual property. Cyberattacks pose a significant concern for individuals, businesses, and governments worldwide, highlighting the need for robust cybersecurity measures and international cooperation. The bipartisan Taiwan Cybersecurity Resiliency Act introduced in the United States reflects the growing recognition of the cyber threats facing Taiwan and the importance of bolstering its cybersecurity capabilities.
FROM THE MEDIA: Taiwan has experienced a surge in malicious emails targeting government officials and various companies, coinciding with rising concerns over China's intentions toward the island. Cybersecurity firm Trellix reported a significant increase in extortion emails aimed at Taiwan's government, with a 30-fold rise in the number of malicious emails in January compared to the previous year. The heightened tensions between Taiwan and China have led to an increase in phishing attacks, often attributed to state-sponsored groups. These campaigns have targeted government agencies, as well as IT, manufacturing, and logistics industries, using malware such as PlugX, known for its ability to evade antivirus software. Other malware families, including Kryptik, Zmutzy, and Formbook, have also been observed in attacks targeting Taiwan.
READ THE STORY: The Record
A Chinese comedian walks into a political storm after an army joke falls flat
Analyst Comments: The article highlights the consequences faced by Chinese comedian Li Haoshi after making a joke about the People's Liberation Army during a stand-up routine. The incident reflects the tightening control on freedom of expression in China and the intolerance of dissenting voices. The severe punishment faced by Li and the concerns expressed by other comedians demonstrates the challenges and risks associated with the art form in an increasingly authoritarian state. The incident has also triggered a broader discussion about the role of comedy and the limitations imposed by the government on creative expression.
FROM THE MEDIA: Chinese comedian Li Haoshi, performing under the stage name House, has sparked controversy and faced severe consequences after making a joke about the People's Liberation Army motto during a stand-up routine. The joke led to outrage among conservative and nationalist commentators, resulting in a $2.1 million fine for Li's management company, an investigation by Beijing police, and the termination of Li's contract. The incident has raised concerns about free expression and intolerance of dissent in China, where comedy has grown in popularity but is increasingly subjected to government censorship. Comedians are now worried about losing their jobs and self-censorship is on the rise, leading to limited room for creative expression.
READ THE STORY: FT
Escalating China-Taiwan Tensions Fuel Alarming Surge in Cyber Attacks
Analyst Comments: The report underscores the connection between geopolitical tensions and cyber attacks, particularly in the context of the China-Taiwan conflict. The increase in cyber attacks targeting Taiwan aligns with the strained relationship between the two sides and reflects the use of cyber warfare as a means to exert influence or gather intelligence. The emphasis on phishing emails and social engineering techniques highlights the role of human vulnerability in these attacks. Organizations operating in countries experiencing geopolitical conflicts should be vigilant and proactive in monitoring and enhancing their cybersecurity measures to mitigate potential risks.
FROM THE MEDIA: The rising tensions between China and Taiwan have led to an increase in cyber attacks targeting Taiwan, according to a report by the Trellix Advanced Research Center. The attacks, which have seen a four-fold increase in malicious emails, aim to deliver malware and steal sensitive information. The most impacted sectors include networking, manufacturing, and logistics. The report also highlights a 15x increase in PlugX detections, indicating that phishing emails were used as an initial access vector. Other malware families identified include Kryptik trojan, Zmutzy, and FormBook. The attacks often employ socially engineered messages and mimic legitimate brands to trick users into entering their credentials. Geopolitical conflicts are identified as one of the main drivers for cyber attacks, and organizations are advised to monitor such events to predict potential attacks.
READ THE STORY: THN
Russian Push to lure western attendees to St Petersburg forum stalls
Analyst Comments: The lack of Western participation in the forum underscores the ongoing geopolitical tensions and the impact of Western sanctions following Russia's invasion of Ukraine. It also highlights the challenges Russia faces in engaging with global business leaders and attracting foreign investment under the current circumstances. The forum's attendee list, dominated by countries that have not condemned Russia's actions, reflects the shifting dynamics of international relations and trade.
FROM THE MEDIA: The St Petersburg Economic Forum, Russia's premier economic event, is reportedly struggling to attract Western participants, as per a draft program. High-profile figures such as former Google CEO Eric Schmidt, Lucid Motors CEO Peter Rawlinson, and Stanford professor Ilya Strebulaev, who were listed as speakers, have confirmed they do not plan to attend. The forum, established by President Putin to draw foreign investment, is primarily attended by representatives from countries like the UAE, Saudi Arabia, India, and China, which have maintained and deepened trade relations with Russia despite Western sanctions. The event is slated for June 14-17.
READ THE STORY: FT
Keep reading with a 7-day free trial
Subscribe to Bob’s Newsletter to keep reading this post and get 7 days of free access to the full post archives.