Daily Drop (492): Orbit mishap risk rises, US must confront China, Chipmakers expand in Japan, Premom app data breach, Economic deterrence against China, Prof. freezes student grades, Cuba ransomware
05-18-2023
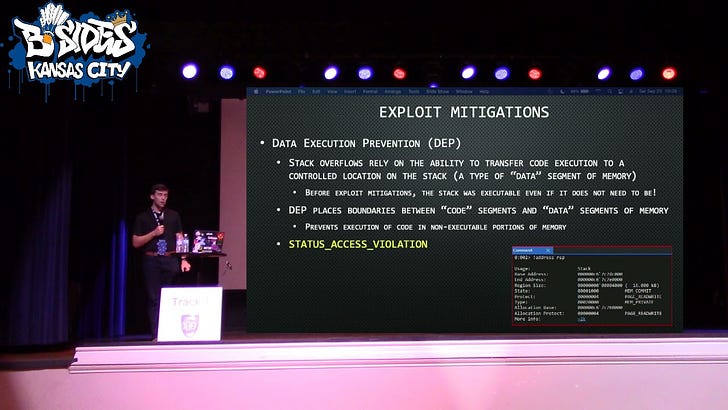
Thursday, May 18, 2023 // (IG): BB // Intro Exploit Dev // Coffee for Bob
Lack of communication with China increases the risk of mishaps in orbit
Analyst Comments: The article effectively highlights the significance of open communication in responsible space operations and the challenges posed by China's lack of transparency. Lt. Gen. DeAnna Burt's firsthand experience and examples demonstrate the negative consequences of a breakdown in communication between the U.S. and China. The article underscores the importance of open dialogue to prevent misunderstandings, miscalculations, and potential conflicts in the space domain. By comparing China's lack of communication to the U.S.'s transparency in discussing its own space capabilities, the article highlights the need for better awareness and trust-building measures. The concerns expressed by Burt and a senior Pentagon official further emphasize the potential risks of an unintended conflict arising from a lack of communication with China.
FROM THE MEDIA: The Defense Department has established a set of rules for responsible space operations due to concerns over the deployment of anti-satellite weapons by rival nations. One of these rules emphasizes the importance of open communication about U.S. military space activities to prevent misunderstandings. However, Lt. Gen. DeAnna Burt, Deputy Chief of the U.S. Space Force for operations, cyber, and nuclear, expressed frustration over China's lack of transparency regarding its own space activities. This lack of communication hinders efforts to manage space traffic and prevent mishaps, potentially leading to misinterpretation and miscalculations between the U.S. and China. Burt highlighted the consequences of this breakdown in communication, noting that the U.S. Space Command receives no response or acknowledgment from China when issuing warnings or notifications related to close approaches or potential collisions. The absence of open communication and mutual trust increases the risk of miscalculations and conflicts. Burt stressed the importance of open dialogue to ensure space security and mitigate misunderstandings, even if there are disagreements between nations.
READ THE STORY: Spacenews
Rep. Gallagher says the US needs to take off 'golden blindfolds' and 'open our eyes to China's risk
Analyst Comments: Rep. Gallagher's remarks reflect growing concerns among U.S. lawmakers about China's actions and their implications for national security, human rights, and economic interests. The bipartisan establishment of the House China Committee underscores the recognition of the need for a comprehensive approach to address the challenges posed by China. The hearing provides a platform for discussing the CCP's economic espionage and its impact on U.S. interests. It also highlights the importance of responsible investment practices and the role of American businesses in upholding ethical standards.
FROM THE MEDIA: During a Select Committee hearing on the Chinese Communist Party (CCP), Rep. Mike Gallagher (R-Wisconsin) emphasized the need for the United States to recognize and address the risks posed by China. He stated that American businesses should not be complicit in the CCP's ongoing human rights abuses, and investment managers, particularly U.S. pension and retirement fund stewards, cannot ignore their fiduciary duties. Gallagher highlighted the CCP's criminalization of routine due diligence and the undermining of the transparent disclosure system in capital markets. The House China Committee was established to re-examine the strategic competition between the U.S. and China, and there is bipartisan consensus that the era of trusting "communist China" has come to an end.
READ THE STORY: FoxNews
Global Chipmakers to Expand in Japan as tech decoupling accelerates
Analyst Comments: The plans of major semiconductor manufacturers to expand manufacturing and deepen partnerships in Japan demonstrate the ongoing efforts to diversify and secure the global chip supply chain amid geopolitical tensions. The move aligns with the goals of Western allies, particularly the US, to reduce reliance on Chinese technology and strengthen their semiconductor industries. Japan's support and subsidies are attractive to these companies, as they aim to establish a stronger presence in the country. The meeting also reflects the shifting dynamics in the region, as tensions between South Korea and Japan have eased and alignment among like-minded nations against China's technological and military influence increases. The investments and partnerships in Japan are likely to contribute to the development of more resilient supply chains and support efforts to safeguard critical technologies.
FROM THE MEDIA: Seven major semiconductor manufacturers, including Taiwan Semiconductor Manufacturing Company (TSMC), Samsung Electronics, Intel, and Micron, have revealed plans to increase manufacturing and deepen tech partnerships in Japan. The move comes as Western allies, led by the US, seek to reshape the global chip supply chain and reduce dependency on Chinese suppliers. Micron plans to invest up to $3.7 billion, including Japanese state subsidies, in building a plant for cutting-edge lithography technology. Samsung is discussing the establishment of a $275 million research and development center in Yokohama. The meeting in Tokyo with Japanese Prime Minister Fumio Kishida reflects Japan's aim to re-emerge as a semiconductor powerhouse and strengthen its semiconductor industry.
READ THE STORY: FT
FTC says fertility tracking app Premom shared sensitive health data with third parties
Analyst Comments: The FTC's action against Easy Healthcare highlights the importance of protecting sensitive health data and holding app developers accountable for their data handling practices. The allegations of sharing personal information with China-based firms raise concerns about data security and potential risks associated with data being accessed by foreign entities. This case underscores the need for robust privacy regulations and enforcement measures to safeguard user's personal information, particularly in the healthcare and fertility app sectors where sensitive data is involved. The proposed order's requirements, such as obtaining user consent for data sharing and providing transparency about data usage, align with best practices for privacy protection. The civil penalties imposed on Easy Healthcare serve as a deterrent for future violations and signal the FTC's commitment to enforcing privacy regulations.
FROM THE MEDIA: The Federal Trade Commission (FTC) has accused Easy Healthcare Corporation, the developer of the fertility app Premom, of improperly sharing sensitive personal and health data of its users with third parties, including China-based firms. The FTC alleges that Easy Healthcare violated its promises to users by disclosing health information, such as pregnancy status, to Google and AppsFlyer for marketing purposes and sharing geolocation data with Chinese advertising firms without adequate encryption. The FTC has proposed an order that would bar the company from sharing users' personal health data with third parties for advertising purposes and require obtaining user consent for any other data sharing. Easy Healthcare is also facing civil penalties, including a $100,000 fine and additional payments to Connecticut, the District of Columbia, and Oregon. The proposed order requires court approval before taking effect.
READ THE STORY: The Record
Combating China with economic deterrence
Analyst Comments: The article presents a compelling case for supporting Taiwan and employing economic deterrence strategies to counter China's potential aggression. It effectively highlights Taiwan's economic significance, emphasizing its role as a major trade partner and a leader in the semiconductor industry. The author's call for multilateral efforts and collaboration among G-7 leaders is a strategic approach to address the challenges posed by China's actions. By emphasizing the potential economic consequences for China, such as reputational damage and economic instability, the author underscores the importance of deterring aggressive actions while promoting a peaceful resolution.
FROM THE MEDIA: The article highlights the importance of supporting Taiwan, a democratic and economically prosperous nation, in the face of potential aggression from China. It emphasizes Taiwan's economic significance as a major trade partner and a global leader in the semiconductor industry. The author argues for the need to develop a comprehensive economic deterrence plan to counter China's potential malign activities, in addition to defense and military support. They suggest that G-7 leaders should collaborate to implement multilateral economic trade sanctions and encourage supply chain diversification away from China. The article also calls for reinforcing the international status of the Taiwan Strait and enacting foreign investment laws to counter Chinese influence. The author concludes by emphasizing the importance of sending a strong message of economic deterrence to dissuade China from altering the status quo with Taiwan.
READ THE STORY: The Hill
Professor freezes student grades after ChatGPT claimed AI wrote their papers
Analyst Comments: The case at the University of Texas A&M-Commerce highlights the challenges and controversies surrounding the use of AI software to detect machine-generated content in academic settings. While the instructor's intention may have been to ensure academic integrity, relying solely on ChatGPT to assess the authenticity of students' work proved to be problematic. The incident underscores the limitations of current AI detection tools, as ChatGPT itself cannot accurately determine whether an essay was generated by the software. Additionally, the study suggests that as AI models improve, it will become increasingly difficult to reliably detect AI-generated text. Institutions should exercise caution in using such tools and consider their unreliability in making final judgments on plagiarism or cheating.
FROM THE MEDIA: Instructor Jared Mumm at the University of Texas A&M-Commerce accused students of cheating by using AI software, ChatGPT, to write their essays. The instructor used ChatGPT to assess whether the assignments were human-written or computer-generated. Some essays were labeled as machine-crafted by the AI software, leading to grades being withheld and diplomas temporarily put on hold for graduating students. However, several students were later cleared of cheating allegations, and the university confirmed that no students failed the class or were barred from graduating. The incident has prompted discussions about the use of software to detect AI-generated content and its limitations.
READ THE STORY: The Register
Alameda seeks millions of dollars from firms including George Osborne’s 9Yard
Analyst Comments: The lawsuits filed by Alameda Research highlight allegations of misappropriation of funds and fraudulent transfers in connection with the acquisition of Embed Financial by FTX. If successful, Alameda could recover a significant amount of money to repay creditors and address the bankruptcy of FTX. The involvement of prominent individuals and venture capital firms in the lawsuits adds further attention to the case. The outcome of the legal proceedings will determine the extent to which the funds can be recovered and the potential consequences for the individuals and firms involved.
FROM THE MEDIA: Alameda Research, now run by restructuring expert John Ray, is seeking to recover hundreds of millions of dollars paid to individuals and firms, including former UK Chancellor George Osborne's venture capital vehicle, in connection with a deal struck by Sam Bankman-Fried before his cryptocurrency empire FTX entered bankruptcy. Alameda alleges that Bankman-Fried and other insiders misappropriated FTX funds to acquire Embed Financial, a start-up broker-dealer. The lawsuits filed by Alameda in Delaware aim to reclaim money from former Embed employees who received "retention" payments and the company's former shareholders. Defendants include prominent Silicon Valley firms such as Y Combinator, Bain Capital Ventures, and 9Yards, where Osborne is a partner. Alameda's lawyers are seeking to unwind "fraudulent transfers" and recover the funds under bankruptcy laws. None of the defendants are accused of wrongdoing.
READ THE STORY: FT
Serious Unpatched Vulnerability Uncovered in Popular Belkin Wemo Smart Plugs
Analyst Comments: The buffer overflow vulnerability in the second-generation Wemo Mini Smart Plug raises concerns about the security of the device and the potential for remote exploitation. Belkin's decision not to address the flaw due to the device's end-of-life status leaves users vulnerable and highlights the importance of ongoing support and security updates for IoT devices. Users should follow the recommended mitigation measures to minimize the risk of exploitation, including not exposing the device directly to the internet and implementing network segmentation.
FROM THE MEDIA: The second-generation version of Belkin's Wemo Mini Smart Plug has been found to have a buffer overflow vulnerability that could allow remote injection of arbitrary commands. Israeli IoT security company Sternum discovered the issue and reported it to Belkin on January 9, 2023. The vulnerability is related to a feature that allows users to rename the smart plug, as the firmware does not enforce the character limit set by the app, creating a buffer overflow condition. Belkin has stated that it will not address the flaw due to the device reaching end-of-life and being replaced by newer models. Users are advised to avoid exposing the smart plug directly to the internet and implement appropriate segmentation measures if used in sensitive networks.
READ THE STORY: THN
Elizabeth Holmes is going to prison – with a $500m bill
Analyst Comments: The failed bid by Elizabeth Holmes to avoid prison and the subsequent denial of her appeal by the Ninth Circuit Court of Appeals mark a significant development in the high-profile Theranos case. It underscores the principle that individuals who engage in fraudulent activities will be held accountable for their actions, regardless of their public image or prominence. Holmes, once hailed as a visionary entrepreneur, now faces an 11-year prison sentence for defrauding investors who believed in her blood-testing technology. This outcome sends a clear message that deceptive practices in the corporate world will not be tolerated, and those responsible will face serious consequences. The denial of Holmes' appeal by the Ninth Circuit Court of Appeals reflects the court's assessment that her appeal did not raise substantial legal or factual questions that could overturn the verdict or modify her sentence. This decision reinforces the validity of the original conviction and the judicial process that led to it.
FROM THE MEDIA: Elizabeth Holmes, the founder of Theranos, has failed in her final bid to avoid prison and will begin her 11-year sentence for defrauding investors in her blood-testing startup. Holmes had appealed to the Ninth Circuit Court of Appeals to allow her to remain free on bail while appealing her conviction but was denied. The court concluded that her appeal did not raise substantial questions of law or fact that would likely reverse the verdict or modify her sentence. Holmes is expected to report to prison on May 30. In addition, a restitution order was issued in the case, holding Holmes and her co-defendant responsible for repaying $452 million to defrauded investors.
READ THE STORY: The Register
Darknet Carding Kingpin Pleads Guilty: Sold Financial Info of Tens of Thousands
Analyst Comments: The case highlights the illegal activities conducted on darknet platforms, involving the trafficking of financial information. Mihalo's guilty plea demonstrates the successful efforts of law enforcement in investigating and prosecuting cybercriminals operating on the dark web. The collaboration of various agencies and the shutdown of platforms like Try2Check indicate ongoing efforts to disrupt and dismantle cybercrime networks. The severity of the charges and potential jail time faced by Mihalo and his accomplices serve as a deterrent to individuals engaged in similar criminal activities.
FROM THE MEDIA: Michael D. Mihalo, also known as Dale Michael Mihalo Jr. and ggmccloud1, has pleaded guilty in a Missouri court to operating a darknet carding site called Skynet Market. Mihalo and his associates trafficked credit and debit card data belonging to tens of thousands of victims in the United States. They sold the stolen financial information on various dark web marketplaces, including AlphaBay Market, Wall Street Market, and Hansa Market, between February 2016 and October 2019. Mihalo personally possessed and distributed information associated with 49,084 stolen payment cards. One of Mihalo's accomplices, Taylor Ross Staats, worked as a "card checker" to verify the validity of the financial information. Staats pleaded guilty to conspiracy to commit access device fraud. Mihalo earned over $1 million worth of cryptocurrencies from the schemes. He pleaded guilty to multiple charges, including conspiracy to commit access device fraud, access device fraud, and money laundering.
READ THE STORY: THN // The Record
China imposes $2M fine for stand-up joke seen as mocking the military
Analyst Comments: The incident involving Li Haoshi's fine illustrates the strict regulations surrounding speech in China, particularly when it comes to sensitive subjects such as the military. The authorities in China are vigilant in safeguarding the reputation and image of the armed forces, imposing penalties for any perceived disrespect. This case highlights the potential consequences of public expressions that may be interpreted as mocking or insulting towards the military, even if unintended. It underscores the need for individuals and companies to exercise caution in their public statements and be aware of the boundaries set by the government. The incident reflects the broader context of controlled speech in China, where adherence to official narratives and protection of national interests are prioritized.
FROM THE MEDIA: Chinese comedian Li Haoshi's company has been fined approximately $2 million by the Beijing Municipal Bureau of Culture and Tourism after Li made a joke during a show that some interpreted as mocking the military. Li referenced a phrase used by the People's Liberation Army (PLA) during his performance, which garnered laughter from the audience but also drew a complaint and subsequent criticism. Li was suspended from his representation firm, and his social media account was suspended after he issued an apology expressing remorse. The bureau deemed the comments "seriously insulting" and emphasized their commitment to protecting the image of the PLA. China implemented a law in 2021 to prohibit defamation of the military.
READ THE STORY: The Hill
Cuba ransomware believed to be a Russian state-backed operation
Analyst Comments: The attribution of cyberattacks is a complex and challenging task, often involving various indicators and intelligence analysis. While BlackBerry researchers have linked the Cuba ransomware operation and RomCom RAT to Russian government hackers based on timing and similarities, there are differing opinions among cybersecurity experts. Attribution in the cyber realm can be challenging due to the use of deception techniques and the potential involvement of multiple actors. Further investigation and analysis are necessary to establish definitive attribution.
FROM THE MEDIA: According to BlackBerry researchers, the Russian government hackers are believed to be behind the Cuba ransomware operation, which is associated with the RomCom RAT malware used in attacks against Ukraine. BlackBerry reached this conclusion based on the timing of malicious operations coinciding with major events related to the Russia-Ukraine conflict. However, other cybersecurity experts, such as Doel Santos from Palo Alto Networks' Unit 42, are skeptical of attributing Cuba ransomware and RomCom RAT to Russian state-backed operations. Santos noted the more sophisticated nature of RomCom RAT operators, suggesting a potential espionage angle and a possible connection to a nation-state, but the extent of this relationship remains uncertain.
READ THE STORY: SCMAG
Lemon Group Uses Millions of Pre-Infected Android Phones to Enable Cybercrime Enterprise
Analyst Comments: The discovery of the Lemon Group's operation highlights the persistent problem of Android devices being shipped with pre-installed malware. While this issue has been known for years, the malware has evolved and become more dangerous, with Lemon Group's Guerrilla malware exhibiting advanced capabilities and significant reach. The connection between Lemon Group's operations and the Triada Trojan underscores the sophistication of their tactics. This report serves as a reminder of the importance of device security and the need for users to remain vigilant in protecting their Android devices against pre-installed malware
FROM THE MEDIA: The Lemon Group, a cybercriminal outfit, has been found to pre-infect Android devices with malware called "Guerrilla," turning them into tools for various malicious activities. Researchers from Trend Micro discovered that Lemon Group has infected devices in 180 countries, with over 55% of victims in Asia. The malware is primarily distributed through inexpensive mobile devices, including Android phones, Smart TVs, TV boxes, and children's watches. Lemon Group profits from stolen SMS messages, one-time passwords, ad fraud, and setting up fake accounts on messaging and social media platforms. The pre-installed malware poses a significant threat to Android users and critical infrastructure, with potential long-term financial gains for Lemon Group.
READ THE STORY: DARKReading
The Post Office Is Spying on the Mail. Senators Want to Stop It
Analyst Comments: The senators' letter raises important concerns about the practice of mail covers and their potential impact on privacy and civil liberties. The ability to conduct surveillance on physical mail without a higher evidentiary threshold or judicial oversight raises questions about the scope of government monitoring. The senators' call for transparency and restrictions on mail covers aligns with the need to balance law enforcement objectives with individual rights and protections.
FROM THE MEDIA: A bipartisan group of US senators has written a letter to the chief postal inspector of the United States Postal Service (USPS), expressing concern over the practice of conducting surveillance on physical mail through a request known as a "mail cover." The senators argue that mail covers threaten privacy and First Amendment rights, equating them to unchecked government monitoring. They highlight the potential for abuse and cite historical cases of surveillance by intelligence agencies. The senators call for increased transparency, requesting that mail covers only be allowed with the permission of a federal judge and that annual statistics on their use be published.
READ THE STORY: Wired
Xi Jinping courts Central Asia as Russian influence weakens
Analyst Comments: The summit between President Xi Jinping and Central Asian leaders reflects China's increasing focus on the region and its desire to expand its influence, particularly as Russia's presence wanes. China's Belt and Road Initiative and its economic investments in Central Asia have the potential to boost the region's development and connectivity. However, there are concerns about the implications of China's growing presence, including issues related to debt, soft power, and national sovereignty. The outcome of the summit and China's further actions in Central Asia will continue to shape regional dynamics and the competition for influence in the region.
FROM THE MEDIA: Chinese President Xi Jinping is hosting an in-person summit with leaders from Kazakhstan, Kyrgyzstan, Tajikistan, Uzbekistan, and Turkmenistan, seeking to strengthen China's economic and political relationships in Central Asia. The summit comes as Russia's influence in the region weakens due to distractions like the war in Ukraine. China views Central Asia as strategically important for its own security and trade interests. The summit provides an opportunity for Xi to showcase China's Belt and Road Initiative and expand cooperation on infrastructure projects, green energy, and security.
READ THE STORY: FT
Lawmakers advance cyber bills aimed at open-source, satellite vulnerabilities
Analyst Comments: The advancement of bipartisan cybersecurity legislation in both the House and Senate reflect the growing recognition of the importance of protecting critical infrastructure and improving cybersecurity measures. The focus on open-source software and the need to address vulnerabilities highlight the challenges posed by reliance on such code. By developing risk frameworks and hiring experts, the federal government aims to enhance the security of open-source software and reduce cyber threats. The bills related to satellite defense and the civilian cybersecurity reserve program also demonstrate the commitment to bolstering cybersecurity capabilities.
FROM THE MEDIA: The House Homeland Security Committee has approved bipartisan legislation that requires the Cybersecurity and Infrastructure Security Agency (CISA) to develop a risk framework for the federal government's use of open-source software. The bill aims to address security vulnerabilities exposed in the popular open-source code Log4j in 2021, which impacted millions of devices worldwide. The legislation directs CISA to hire open-source security experts and developers to enhance the defense against future threats. The committee also approved a bill to establish a program for training Homeland Security Department employees in cybersecurity roles. In the Senate, the Homeland Security Committee advanced a bill to provide commercial satellite owners with resources to defend against cyberattacks and another bill to establish a civilian cybersecurity reserve pilot program.
READ THE STORY: The Record
Critical Flaws in Cisco Small Business Switches Could Allow Remote Attacks
Analyst Comments: The security vulnerabilities in Cisco's Small Business Series Switches highlight the importance of timely patching to address critical flaws. The availability of proof-of-concept exploit code underscores the need for swift action to prevent potential attacks. Cisco's decision not to release updates for certain end-of-life product lines emphasizes the importance of regularly updating and upgrading network infrastructure to maintain security. Organizations using the affected switches should promptly apply the available patches to mitigate the risk of exploitation.
FROM THE MEDIA: Cisco has released security updates to address nine vulnerabilities in its Small Business Series Switches. The flaws rated critical, could be exploited by remote attackers to execute arbitrary code, cause a denial-of-service (DoS) condition, or read unauthorized information. The vulnerabilities are related to improper validation of requests sent to the web interface. Cisco has provided firmware updates for some product lines, while others have reached end-of-life and will not receive patches. The company has not observed any evidence of malicious exploitation but urges users to apply the updates to mitigate potential threats.
READ THE STORY: THN
What if San Francisco never pulls out of its ‘doom loop’
Analyst Comments: San Francisco is facing a complex and interconnected set of challenges that require a multi-faceted approach. The drug crisis, homelessness, and wealth inequality are pressing issues that demand immediate attention. The expansion of naloxone distribution and initiatives like Urban Alchemy demonstrate localized efforts to address these problems. However, the city needs comprehensive strategies that tackle the root causes of these issues, including affordable housing, accessible healthcare, and support services for vulnerable populations. The impact of remote work and the decline of the tech industry's presence in the city have significant implications for San Francisco's economy and social fabric. Rebuilding the commercial real estate sector and fostering economic diversification will be crucial for the city's recovery.
FROM THE MEDIA: San Francisco is grappling with a multitude of challenges, including a worsening drug crisis, a significant homeless population, wealth inequality, vacant commercial real estate, and high-profile violent incidents. The city's response to these issues, such as expanding the distribution of naloxone kits and employing ex-convicts to clean up streets, reflects attempts to address the problems. However, comprehensive and long-term solutions are needed. The impact of remote work, tech industry layoffs, and the exodus of prominent figures from the city have further exacerbated the situation.
READ THE STORY: FT
Patients angered after Oklahoma allergy clinic blames Cyberattack for Shutdown
Analyst Comments: The cyberattack on the Oklahoma allergy clinic highlights the increasing frequency and impact of cyber threats on healthcare facilities. The clinic's sudden closure and lack of communication with patients raise concerns about the clinic's preparedness to handle such an incident and its ability to protect sensitive patient data. The frustrations expressed by patients regarding canceled appointments and difficulties accessing necessary treatments underscore the immediate impact of cyberattacks on healthcare services. The involvement of federal agencies, such as the Department of Justice and the Department of Defense, indicates the severity and potential implications of the attack.
FROM THE MEDIA: The Oklahoma Institute of Allergy Asthma and Immunology, an allergy clinic, abruptly closed its doors, citing a cyberattack as the cause. The closure left angry parents and patients demanding answers, with some showing up for scheduled appointments only to find the clinic permanently closed. The clinic posted a notice stating that a limited area would still be used for infusions and injections, but wait times may increase due to the cyberattack. Patients expressed frustration and confusion over the lack of notice and the clinic's unresponsiveness. The clinic's operators explained that they were locked out of their systems, including phones, email, and electronic medical records, after downloading a problematic iPhone app. The FBI denied being contacted about the incident. The Department of Justice and the Department of Defense are reportedly investigating the incident.
READ THE STORY: The Record
Threat Group UNC3944 Abusing Azure Serial Console for Total VM Takeover
Analyst Comments: The abuse of Microsoft Azure Serial Console by UNC3944 highlights the growing trend of threat actors leveraging cloud services and taking advantage of living-off-the-land (LotL) techniques to evade detection and sustain their attacks. This method allows the attackers to bypass traditional security measures and gain full control over compromised VMs. The use of SIM-swapping attacks demonstrates the group's sophistication in targeting privileged users and bypassing two-factor authentication (2FA) measures. The exploitation of Azure VM extensions and the serial console functionality showcases the need for organizations to properly configure and secure their cloud resources.
FROM THE MEDIA: A financially motivated threat group known as UNC3944, Roasted 0ktapus, or Scattered Spider has been observed exploiting Microsoft Azure Serial Console on virtual machines (VMs) to install third-party remote management tools within compromised environments. Mandiant, a threat intelligence firm, discovered this unique method of attack, which allows the threat actors to gain full administrative access to the VM and evade traditional detection methods within Azure. UNC3944 is also known for utilizing SIM-swapping attacks to breach telecommunications and business process outsourcing companies. The group employs techniques such as SMS phishing to obtain the credentials of privileged users and conducts SIM swaps to gain control over the two-factor authentication (2FA) token. After gaining elevated access, the threat actors exploit Azure VM extensions to survey the target network and then use the serial console functionality to establish an administrative command prompt within an Azure VM. They deploy legitimate remote administration tools using PowerShell.
READ THE STORY: THN
Zoom executives knew about key elements of the plan to censor Chinese activists
Analyst Comments: Zoom's compliance with Chinese censorship demands and the subsequent harassment of dissidents on its platform demonstrate the challenges faced by American tech companies operating in China. The case underscores the influence exerted by the Chinese Communist Party (CCP) over foreign businesses and the trade-offs companies must make to maintain access to the Chinese market. While many U.S. companies are reassessing their relationships with China, they are constrained by the potential financial implications of losing access to a vast market. The Chinese government's control over data storage, flow, and access through cybersecurity and data protection laws further strengthens its leverage over foreign companies.
FROM THE MEDIA: In 2019, videoconferencing platform Zoom faced a crisis when Chinese authorities blocked its service for not suppressing anti-government speech. To regain access to the Chinese market, Zoom complied with Beijing's demands to suppress speech on the platform, including monitoring user communications for politically sensitive content. A criminal complaint revealed that Zoom employee Julian Jin cooperated with Chinese government officials to harass dissidents based in the United States and suppress their speech. While Zoom's senior leadership was largely unaware of the scheme, the updated complaint suggests that they had some knowledge of Jin's actions.
READ THE STORY: Cyberscoop
Ukraine War: Vast hacker ‘militias’ do little damage – but can rally mass support, says study
Analyst Comments: A new study from think tank CSIS explores the role of non-government groups in the cyber conflict between Russia and Ukraine. The study highlights the blurring of traditional lines between civilian and non-combatant, neutrality and intervention, and peace and war in the cyber domain. The report discusses the involvement of corporate giants like Microsoft and tech upstarts like SpaceX in supporting Ukraine's cybersecurity efforts. It also examines the activities of loosely organized volunteer groups, such as the pro-Kremlin Killnet and the self-proclaimed IT Army of Ukraine, which leverage social media to build support and shape the narrative of the conflict. The study raises important questions about the legal and ethical implications of civilians engaging in cyber attacks and the challenges in determining appropriate responses to such activities.
FROM THE MEDIA: VA new study from think tank CSIS explores the role of non-government groups in the cyber conflict between Russia and Ukraine. The study highlights the blurring of traditional lines between civilian and non-combatant, neutrality and intervention, and peace and war in the cyber domain. The report discusses the involvement of corporate giants like Microsoft and tech upstarts like SpaceX in supporting Ukraine's cybersecurity efforts. It also examines the activities of loosely organized volunteer groups, such as the pro-Kremlin Killnet and the self-proclaimed IT Army of Ukraine, which leverage social media to build support and shape the narrative of the conflict. The study raises important questions about the legal and ethical implications of civilians engaging in cyber attacks and the challenges in determining appropriate responses to such activities.
READ THE STORY: Breaking Defense
Ex-contractor's computer in Russia breached D.C. Metrorail transit system, watchdog finds
Analyst Comments: The incident involving the former contractor accessing WMATA data from Russia highlights the importance of promptly revoking access rights when an individual's employment ends to prevent unauthorized access. Failure to do so can expose sensitive data to potential risks and compromise cybersecurity. It also raises questions about proper oversight and accountability in managing access permissions.
FROM THE MEDIA: A former contractor for the Washington Metropolitan Area Transit Authority (WMATA) was able to remotely access sensitive WMATA data from a computer in Russia because his supervisor failed to revoke his high-level administrative access, according to a memo from the WMATA Office of Inspector General. The contractor's access to WMATA systems was not revoked in the hopes of contract renewal. The incident raised concerns about the vulnerability of WMATA's systems and the potential risks to its critical and sensitive data. The inspector general also highlighted a "disconnect" between WMATA's IT and cybersecurity staff, which has hindered cybersecurity implementation. The inspector general had previously warned WMATA about security vulnerabilities and issued cybersecurity recommendations that were not acted upon.
READ THE STORY: CBSNEWS
Deepfake Startups Become a Focus for Venture Capital
Analyst Comments: The surge in venture capital funding for deepfake technology reflects the growing interest and potential of synthetic media in various industries. However, it also raises concerns about the potential misuse and negative implications of this technology. Deepfake content has already been used for political manipulation and disinformation campaigns, highlighting the need for effective detection and mitigation measures. The growth in the deepfake detection market demonstrates the increasing recognition of the risks associated with deepfakes and the demand for tools and solutions to identify and combat them. It is crucial to invest in research and development to stay ahead of deepfake technology advancements and ensure the protection of individuals and institutions from potential harm.
FROM THE MEDIA: Venture capital investment in deepfake technology startups has seen a significant increase in recent years, with $187.7 million invested in 2021 alone, compared to just $1 million in 2017. The global market for deepfake detection is also projected to grow at a compound annual growth rate of 42% through 2026. Several prominent deepfake startups have received substantial funding, including Runway, Synthesia, Deepdub, and Deep Voodoo. While some of these startups focus on benign applications such as commercial production and internal training, concerns persist regarding the potential misuse of deepfake technology for disinformation and the erosion of democratic institutions.
READ THE STORY: Bloomberg
Items of interest
Congress looks to expand CISA’s role, adding responsibilities for satellites and open-source software
Analyst Comments: The passage of these bills demonstrates a commitment to enhancing cybersecurity capabilities and protecting critical systems from cyber threats. The focus on open-source software is particularly crucial, as it is widely used and has become a target for cyber attacks. By engaging with the open-source community and developing frameworks for assessing risks, CISA can contribute to strengthening the security of software supply chains and mitigating vulnerabilities. The expansion of CISA's responsibilities and authorities aligns with the agency's central role in coordinating cybersecurity efforts at the national level. However, concerns have been raised about the potential for CISA to become overly regulatory. Balancing the need for enhanced cybersecurity measures with concerns about government overreach will be an ongoing challenge.
FROM THE MEDIA: Lawmakers have passed a series of bills aimed at strengthening the role of the Cybersecurity and Infrastructure Security Agency (CISA) in safeguarding open-source software, protecting critical infrastructure, and expanding the cybersecurity workforce. The bills include provisions such as requiring CISA to work with the open source community to improve its security, assessing the risks of open source components for federal agencies, creating voluntary cybersecurity recommendations for the space sector, and establishing a pilot civilian cyber reserve program. These legislative efforts reflect the growing recognition of the need to address cybersecurity risks and vulnerabilities in critical infrastructure and promote a more robust cybersecurity posture across government and industry.
READ THE STORY: Cyberscoop
Exploit Development Is Dead, Long Live Exploit Development! (Video)
FROM THE MEDIA: It is no secret that the days of jmp esp are far gone. In the age of Virtualization-Based Security and Hypervisor Protected Code Integrity -- code execution, as a result of a memory corruption vulnerability, is not as trivial as it once was. However, a few times a year, there is always that vulnerability that makes headlines, is remotely exploitable, and obtains code execution in ring 0. What gives? This talk addresses the history of binary exploitation and the mitigations operating systems instrument to thwart those vulnerabilities, how adversaries constantly adopt novel and creative solutions to bypass said mitigations, and the future of exploit development in both user mode and kernel mode.
Exploit Development for Dummies (Video)
FROM THE MEDIA: Have you ever asked yourself how vulnerabilities are discovered and how exploits are written? Well, then this is the perfect talk for you. We will begin by discussing how so-called Fuzzers can be used to find previously unknown bugs in applications. Then we will analyze the generated crash dumps to find out if the underlying issue is exploitable and finally, we will write a fully-fledged exploit. All this will be demonstrated live, based on the example of a well-known application with more than 1 million downloads per month. This is your chance to be part of the disclosure of a previously unknown zero-day vulnerability!
These open-source products are reviewed by analysts at InfoDom Securities, providing possible context about current media trends related to the realm of cyber security. The stories selected to cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not endorse any third-party claims made in their original material or related links on their sites; the opinions expressed by third parties are theirs alone. For further questions, please contact InfoDom Securities at dominanceinformation@gmail.com.