Daily Drop (489): China Sentences US citizen, ARM side-channel attack, More 'Chinese Police Stations' in Canada, Russia penalizes Google over LGBT, IP Theft
05-15-2023
Monday, May 15, 2023 // (IG): BB // Cloak & Dagger// Coffee for Bob
US citizen sentenced to life in prison for espionage
Analyst Comments: The conviction and life sentence of John Shing-wan Leung on charges of espionage underscore the increasingly tense relations between China and the U.S. The lack of specific details regarding the alleged offense raises concerns about transparency and due process. The case reflects China's strict approach to national security and its crackdown on perceived threats. The implications for U.S.-China relations and the potential impact on the rights and safety of U.S. citizens abroad will continue to be areas of concern.
FROM THE MEDIA: A 78-year-old U.S. citizen and Hong Kong resident, John Shing-wan Leung, has been convicted of espionage and sentenced to life imprisonment by a court in eastern China. The court provided no details of his alleged offense but stated that the investigation began on April 15, 2021, by Suzhou's National Security Bureau. Leung, a former senior member of a pro-China group in the United States, was also stripped of his political rights. The U.S. embassy acknowledged the case but did not provide further comment due to privacy considerations. The conviction comes amid escalating tensions between China and the U.S. on various issues. Hong Kong's Security Bureau has not responded to requests for comment on the matter.
READ THE STORY: Reuters // CNN
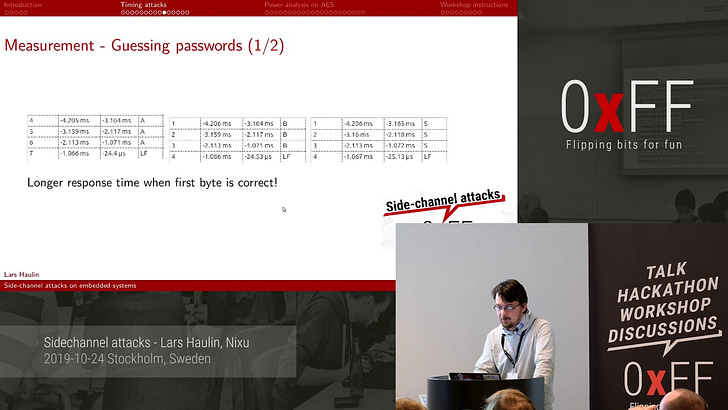
Arm acknowledges side-channel attack but denies Cortex-M is crocked
Analyst Comments: Arm has responded to the allegations of side-channel attacks on its Cortex-M microcontrollers, clarifying that such attacks are not specific to its architecture and can occur in any code with secret-dependent control flow or memory access patterns. The company highlighted its efforts to improve security and mentioned features like "Data Independent Timing" in the Armv8.1-M architecture as measures to protect against data-dependent timing side-channel attacks. The researchers have disclosed their findings to relevant parties and are seeking to demonstrate a similar attack variant in an application without a secret-dependent memory path.
FROM THE MEDIA: Arm, a chip design firm, has responded to allegations made at the Black Hat Asia infosec conference that its microcontrollers, specifically the Cortex-M based systems, are vulnerable to side-channel attacks. The researchers from Portugal's Universidade do Minho (UdM) claimed that microarchitectural timing attacks on microcontrollers are practical. Arm argued that the Security Extensions for the Armv8-M architecture do not claim to protect against side-channel attacks, which are not specific to the Armv8-M architecture but can apply to any code with secret-dependent control flow or memory access patterns. While acknowledging the attack, Arm advised that it can be mitigated by ensuring that control flow and memory access patterns do not depend on a secret state.
READ THE STORY: The Register
There May Be More 'Chinese Police Stations' in Canada, Minister Says
Analyst Comments: The Public Safety Minister of Canada has raised concerns about the possible existence of additional "Chinese police stations" in the country, indicating ongoing efforts by the Canadian authorities to address foreign interference. The investigation into community centers in Montreal and recent diplomatic expulsions highlight the tensions between Canada and China. The Canadian government has faced pressure to respond to allegations of Chinese interference and has taken steps, such as appointing a special investigator, to address the issue.
FROM THE MEDIA: Canadian Public Safety Minister Marco Mendicino stated in an interview that there may be additional "Chinese police stations" operating in Canada, months after an investigation was launched into community centers in Montreal suspected of being used for intimidation or harassment. Mendicino expressed confidence in the Royal Canadian Mounted Police's efforts to disrupt foreign interference and assured decisive action if new stations emerge. Canada recently expelled a Chinese diplomat over allegations of targeting a critical Canadian lawmaker, leading to reciprocal expulsions by China. The Canadian government faces pressure to address suspected Chinese interference and has appointed a special investigator to examine the issue.
READ THE STORY: VOA
Shifting Focus: IP Theft Gains Attention Beyond the Beltway
Analyst Comments: The hearing shed light on the inadequate IP protections in the U.S. The rise of new technologies, such as artificial intelligence, has made it easier for IP theft to occur, and current measures to address cyber infringement violations are often ignored or insufficient. While China is recognized as a major violator of IP in the U.S., American conglomerates, especially tech giants like Google, are also engaging in IP theft practices. The lack of enforcement of laws against IP theft has allowed these thefts to persist. The USPTO's focus on IP rights and enforcement is a positive step forward, but more needs to be done. The U.S. must modernize its IP laws to effectively combat IP theft in the digital age.
FROM THE MEDIA: The House Judiciary Subcommittee on Courts, Intellectual Property, and the Internet recently held a hearing to address the widespread problem of intellectual property (IP) theft and its detrimental effects on the U.S. economy. IP theft is considered one of the most significant threats to small businesses in the country, yet it remains a largely overlooked issue. The financial impact of IP theft is staggering, with billions of dollars drained from the economy. The high cost of patent litigation, averaging between $2.3 million and $4 million, poses a significant challenge for small businesses seeking to pursue their claims. During the hearing, Kathy Vidal, Under Secretary of Commerce for Intellectual Property, highlighted the need to modernize the existing IP ecosystem. Vidal recognized that new technologies and globalization present evolving and challenging IP issues. She emphasized the importance of cultivating an innovation mindset, promoting inclusive innovation and entrepreneurialism, and enhancing U.S. competitiveness and economic prosperity.
READ THE STORY: Townhall
Russia Imposes Penalties on Google for Allegedly Promoting LGBT Propaganda and Disseminating Alleged False Information
Analyst Comments: The Russian court's decision to penalize Google highlights the ongoing conflict between the government's censorship measures and tech companies' commitment to freedom of expression. While the specific claims of spreading "LGBT propaganda" and disseminating fake information need to be evaluated based on evidence, it is important to recognize that these allegations are made from the perspective of the Russian authorities. The fines imposed on Google are part of the broader landscape of online content regulation in Russia, where the government seeks to exert greater control over the flow of information.
FROM THE MEDIA: A Russian court has allegedly penalized Google for purportedly spreading "LGBT propaganda" and disseminating fake information through YouTube videos. The company has been fined three million roubles ($38,600) for its alleged failure to remove the said videos. This comes after a previous fine of 21.1 billion roubles ($373 million) in July 2022 for repeated non-compliance with Russia's content removal requests. Russia has been increasingly cracking down on Western tech companies, particularly targeting YouTube, to exert greater control over online content.
READ THE STORY: Inventiva
Former Ubiquiti Employee Gets 6 Years in Jail for $2 Million Crypto Extortion Case
Analyst Comments: The case of Nickolas Sharp highlights the potential insider threat and the risks associated with employee misconduct. His actions demonstrate the misuse of privileged access to steal confidential data and attempt to extort the company. Ubiquiti's decision to involve law enforcement and not yield to the ransom attempt showcases a proactive approach to cybersecurity incidents. The sentencing of Sharp serves as a reminder of the legal consequences individuals may face for such criminal activities
FROM THE MEDIA: A former employee of Ubiquiti, Nickolas Sharp, has been sentenced to six years in jail after pleading guilty to posing as an anonymous hacker and attempting to extort nearly $2 million worth of cryptocurrency from the company. Sharp, who worked as a senior developer, used his insider access to steal confidential data and sent an anonymous email demanding payment in exchange for the stolen information. Ubiquiti refused to comply and involved law enforcement, leading to Sharp's identification. He tampered with log retention policies and session file names to conceal his unauthorized activities. In addition to the prison sentence, Sharp has been ordered to pay restitution and forfeit personal property.
READ THE STORY: THN
The UK’s Secretive Web Surveillance Program Is Ramping Up
Analyst Comments: The expansion of surveillance technology, particularly the collection and storage of internet connection records, raises significant concerns about privacy and data protection. Critics argue that ICRs are intrusive and can be misused or abused, posing risks to individuals' security. The lack of transparency and limited public information surrounding the development and use of ICRs further fuels these concerns. It is essential for the government to strike a balance between national security interests and protecting individuals' privacy rights.
FROM THE MEDIA: The UK government is reportedly expanding and developing a surveillance technology that can log and store the web histories of millions of people. Known as "internet connection records" (ICRs), these records reveal information about individuals' online activities and are stored by internet providers and phone companies for 12 months under the Investigatory Powers Act. The government claims that the trial of ICRs has been successful, leading to potential plans for a national rollout. Critics argue that ICRs are highly intrusive and raise concerns about data protection. The development and use of ICRs have been shrouded in secrecy, with limited information available to the public.
READ THE STORY: Wired
CLR SqlShell Malware Targets MS SQL Servers for Crypto Mining and Ransomware
Analyst Comments: The targeting of poorly managed MS SQL servers and the use of CLR SqlShell malware highlights the importance of robust security practices and proper server management. Organizations should ensure that MS SQL servers are properly configured and patched to prevent unauthorized access and potential exploitation. It is crucial to implement strong authentication measures, monitor for any unusual activities or vulnerabilities, and regularly update the software and security solutions.
FROM THE MEDIA: A new malware campaign is targeting poorly managed Microsoft SQL (MS SQL) servers, spreading a strain of malware called CLR SqlShell. This malware is capable of executing commands and facilitating malicious behavior on compromised MS SQL servers. The attack method involves using CLR stored procedures to install the malware through the xp_cmdshell command. Threat actors are exploiting internet-exposed MS SQL servers through brute-force and dictionary attacks, leveraging CLR stored procedures to download additional payloads such as Metasploit and cryptocurrency miners. The malware can install backdoors, coin miners, and proxyware, as well as execute malicious commands received from threat actors.
READ THE STORY: THN
The Curious Case of the Missing Google Assistant
Analyst Comments: The absence of Google Assistant from the recent I/O conference suggests that Google may be reevaluating its AI strategy and working to enhance its capabilities to compete with emerging AI bots like ChatGPT. The limitations of older AI assistants in engaging in natural conversation and performing complex tasks have become more apparent. Integrating generative AI into established voice assistants presents technical and user experience challenges that require careful development and testing. Google Assistant's existing user base and its integration into Google's new devices indicate that it is still an important part of Google's ecosystem.
FROM THE MEDIA: Google's recent I/O developer conference highlighted its focus on artificial intelligence (AI) and showcased the public availability of its large language model, Bard, along with several generative AI features. However, there was a notable absence of discussion about Google Assistant, which was previously a major focus of the conference. This omission raises questions about Google's AI strategy and whether it is scrambling to catch up with competitors like ChatGPT. The introduction of ChatGPT and similar AI bots has exposed the limitations of older AI assistants, including Google Assistant and Amazon's Alexa, which struggle with natural conversation and complex tasks. While Google Assistant still has a large user base, integrating generative AI capabilities into established voice assistants presents challenges and requires careful consideration.
READ THE STORY: Wired
Vice Media files for bankruptcy protection ahead of the sale
Analyst Comments: Vice Media's bankruptcy filing and proposed sale reflect the difficulties faced by digital media companies in maintaining their early success and adapting to evolving market conditions. The shift of audiences to traditional media outlets and the changing strategies of tech platforms have affected the viability of digital media groups. Vice's bankruptcy protection and sale to a consortium of lenders provide an opportunity for the company to restructure and secure its future. However, the outcome for existing investors is likely to be unfavorable. The challenges faced by Vice and other digital media companies highlight the need for continued innovation and adaptation in the rapidly evolving media landscape.
FROM THE MEDIA: Vice Media, a digital media group known for its edgy content and millennial appeal, has filed for bankruptcy protection and agreed to sell the business to a consortium of lenders, including Fortress Investment Group and Soros Fund Management. Despite its initial success, Vice has struggled to achieve lasting financial success, facing competition from traditional media groups and the dominance of tech giants like Meta in digital advertising. The sale to the consortium of lenders, subject to higher bids from other parties, will provide Vice with credit and financing to continue its operations during the sale process. Existing investors, including James Murdoch, Disney, and TPG, are expected to be wiped out as a result of the deal. Other digital media companies, such as BuzzFeed and Vox, have also faced challenges and cutbacks in recent times due to changing market dynamics and the shifting priorities of tech platforms.
READ THE STORY: FT
Understanding and Addressing Cyber Threats in the Academic Sector
Analyst Comments: The academic sector is highly targeted by cyber adversaries, with eCrime groups posing the most disruptive threat. Unauthorized access to systems and compromised user credentials facilitate various financially motivated attacks. Ransomware attacks and data theft/extortion campaigns are prevalent, necessitating immediate action. Legacy technology solutions often fail to detect sophisticated attacks, emphasizing the need for advanced cybersecurity measures.
FROM THE MEDIA: The academic sector faces significant cybersecurity risks, including targeted attacks by cyber adversaries. These threats range from ransomware attacks to the exploitation of user identities and unauthorized access to systems. Nation-state actors and eCrime groups are the primary adversaries targeting the sector, seeking non-public information for espionage or financial gain. Access brokers, who sell unauthorized access to institutions' systems, pose a disruptive threat. To mitigate these risks, academic organizations should prioritize full visibility into their technology infrastructure, identity protection, securing cloud investments, threat intelligence, and incident response preparedness.
READ THE STORY: HEPI
Leaked Documents Reveal Wagner Chief's Offer to Provide Russian Troop Locations to Ukraine
Analyst Comments: The leaked documents shed light on Prigozhin's frustration with the ongoing fight in Bakhmut and his strained relationship with Russian military commanders. As an ally of Russian President Vladimir Putin, Prigozhin's offer to trade the lives of Wagner fighters for Russian soldiers could be seen as a treasonous betrayal. While Ukrainian officials confirmed the contacts with Prigozhin, they rejected the offer due to a lack of trust and concerns about its genuineness. Similarly, doubts exist in Washington about Prigozhin's intentions. The leaked documents highlight the complex dynamics and communication channels that exist in wartime, but Prigozhin's ultimate motive remains unclear.
FROM THE MEDIA: Leaked U.S. intelligence documents reveal that Yevgeniy Prigozhin, the owner of the Wagner Group, made an extraordinary offer to Ukraine in late January. Prigozhin proposed providing Ukraine with information on Russian troop positions if Ukrainian commanders withdrew their soldiers from the area around Bakhmut. The offer was conveyed to Ukrainian military intelligence, with whom Prigozhin has maintained secret communications throughout the war. The leaked documents do not specify which Russian troop positions Prigozhin offered to disclose.
READ THE STORY: The Washington Post
Apple supplier Foxconn to invest $500 million in India's Telangana state
Analyst Comments: Foxconn's investment in manufacturing plants in Telangana, India, aligns with Apple's strategy of diversifying its production away from China. India offers a favorable manufacturing environment and a large labor force, making it an attractive destination for technology companies seeking alternative production bases. The move is expected to strengthen India's position as a manufacturing hub and create employment opportunities. By expanding its manufacturing capabilities in India, Apple aims to reduce risks associated with geopolitical tensions and supply chain disruptions. This investment further signifies the ongoing shift in global manufacturing dynamics and highlights the importance of India as a key player in the technology manufacturing sector.
FROM THE MEDIA: Foxconn, an Apple Inc supplier, is set to invest $500 million to establish manufacturing plants in the southern Indian state of Telangana. The investment is expected to create 25,000 jobs in the initial phase. This move comes as Apple has been diversifying its production away from China, where manufacturing was previously impacted by COVID-related restrictions and geopolitical tensions between China and the United States. In March, it was reported that Foxconn had secured an order to produce AirPods for Apple and planned to build a factory in India for manufacturing purposes. The company had also received approval from the Karnataka government for a $968 million investment in the state.
READ THE STORY: Yahoo Finance
Cyber risk: Can banks win the arms race?
Analyst Comments: The banking sector is recognized for its mature and collaborative approach to cybersecurity, but it remains a prime target for cybercriminals. Financial institutions need to stay proactive by investing in robust security measures, testing and measuring controls, and preparing for emerging threats. As technologies evolve, banks must balance the potential risks and benefits they bring.
FROM THE MEDIA: The banking sector faces persistent cyber threats as hackers exploit emerging technologies to breach defenses. Digital transformation and reliance on third-party suppliers have increased vulnerability. Banks must prioritize high-friction experiences for cybercriminals while delivering low-friction customer experiences. Multi-factor authentication, access management, incident response plans, and training for crisis management are essential. Artificial intelligence offers both opportunities and challenges in cybersecurity. Technologies like confidential computing and quantum computing impact data protection.
READ THE STORY: FT
Criminal Website Genesis ‘Still Online’ After Takedown
Analyst Comments: The persistence and quick recovery of Genesis Market highlight the challenges law enforcement faces in combating cybercrime on the dark web. Despite successful takedown efforts, criminal operations can quickly resurface, making it crucial to address the root causes and infrastructure supporting these platforms. Cooperation between international agencies is vital to disrupt such criminal networks effectively.
FROM THE MEDIA: The dark-web hacking platform Genesis Market has reemerged and remains fully functional, just a month after law enforcement agencies conducted an international operation to take it down. The operation led by the FBI and the Netherlands disrupted the site for only about two weeks. The administrators of Genesis have released a new version of their hacking browser, resumed collecting data from hacked devices, and added over 2,000 new victim devices to the market. Genesis facilitates identity fraud by providing stolen credentials and other data, allowing users to impersonate victims. While the volume of stolen data and users has been reduced, the site continues to operate on the dark web, and criminal trust in the service has been damaged.
READ THE STORY: Silicon
Items of interest
A Comprehensive Study of India and Pakistan’s Cyber Strengths and Weaknesses
Analyst Comments: The comparison of India and Pakistan's cyber capabilities reveals a significant gap, with India being more advanced in terms of cybersecurity. Pakistan's lag in cyber capabilities puts its digital assets, national security, and economy at risk. It is crucial for Pakistan to prioritize cybersecurity, develop comprehensive national strategies, and invest in research, infrastructure, and education. International collaboration and confidence-building measures with India can also contribute to a more secure cyberspace.
FROM THE MEDIA: This study compares the cyber capabilities of India and Pakistan, two nuclear-armed neighbors with a turbulent history. India has made significant advancements in cyber capabilities, investing in research, education, and infrastructure related to cybersecurity. The private sector has also contributed to India's cyber capabilities, with companies like Infosys and Tata Consultancy Services improving the cybersecurity environment. In contrast, Pakistan's cyber capabilities are still in the early stages of development, with limited investment and fewer cybersecurity experts. The widening cyber capability gap poses challenges to Pakistan's digital assets, national security, and economic growth. To address this gap, Pakistan needs to strengthen its cyber institutions, invest in secure infrastructure, enhance cybersecurity education, seek international collaboration, and establish confidence-building measures with India.
READ THE STORY: Modern Diplomacy
What are Side-channel attacks (Video)
FROM THE MEDIA: The transcript discusses side-channel attacks, specifically focusing on timing attacks and power consumption analysis on AES encryption algorithms. The speaker, Lucia Lane, introduces the concept of side-channel attacks, which exploit information leakage from the implementation of a program rather than weaknesses in algorithms or implementations themselves. Side-channel attacks can involve various channels, such as execution time, power consumption, sound, or electromagnetic radiation. These attacks typically require physical access to the device, making them harder to exploit remotely. The equipment needed to capture side-channel attacks involves measurement tools that can capture weak signals, including logic analyzers and digital oscilloscopes. However, interfacing with different instruments from various vendors can be a challenge due to different communication protocols.
A Hacker's Guide to Programming Microcontrollers (Video)
FROM THE MEDIA: This tutorial titled "A Hacker's Guide to Programming Microcontrollers" explores the difference between a Raspberry Pi and a microcontroller. The tutorial aims to teach how to program a microcontroller and focuses on creating a simple LED that blinks on and off. It explains the structure of the code and highlights the differences between programming a microcontroller and a regular computer. The tutorial also covers working with hardware, using pins for input and output, and using a resistor to prevent damage to the LED. It mentions two hardware setups, one cheaper and one more expensive, and provides instructions for wiring the components. The code section discusses the use of functions, particularly the setup and loop functions, and introduces concepts such as pin mode, delays, and variables. It demonstrates how to set up the pin mode for the LED, turn it on, and add a delay to control the blinking speed. The tutorial emphasizes the usefulness of microcontrollers for prototyping and creating unique electronic designs.
These open-source products are reviewed by analysts at InfoDom Securities, providing possible context about current media trends related to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not endorse any third-party claims made in their original material or related links on their sites; the opinions expressed by third parties are theirs alone. For further questions, please contact InfoDom Securities at dominanceinformation@gmail.com.