Sunday, April 23, 2023 // (IG): BB // Financial Enabler // Coffee for Bob
Countering China: The New Norm in Defense Technology
Analyst Comments: The United States' focus on competing with China is driving a historic increase in defense spending, particularly in the development of new technologies. The Pentagon is investing heavily in untested weapons like hypersonics and unmanned submarines, under the broad justification that they are needed to counter China. However, there is legitimate debate over the effectiveness of these technologies, with some arguing that they are costly and unnecessary. Meanwhile, initiatives such as cybersecurity, which actively work to defend the US against daily attacks, are being underfunded. This mismatch in funding priorities highlights the need for the Defense Department to change the way it invests in new technology, in order to better address the threats the country faces.
FROM THE MEDIA: The Biden administration has requested $842 billion for the 2024 Pentagon budget, which would be the largest defense budget in history. The budget proposal justifies the spending by highlighting the need to counter China. The Pentagon has spent $8 billion on hypersonic weapons and has requested a further $11 billion for their development. Unmanned and semi-autonomous submarines have also been touted as essential for countering China. However, there is debate over the effectiveness of hypersonic weapons and unmanned submarines. Cybersecurity operations are increasingly important, but the Cybersecurity and Infrastructure Security Agency (CISA) has historically been underfunded, understaffed, and outmatched. Despite the need to counter China's cyber threats, only $3.1 billion has been allocated for CISA, while the total spending on cyber initiatives is $13.5 billion.
READ THE STORY: BPR
Tackling food insecurity in Africa will require securing women’s rights. Here are two ways to start
Analyst Comments: The article provides important insights into the root causes of food insecurity in Africa and highlights the need for policymakers to take concrete steps to address the issue. It suggests that discriminatory laws that hamper women’s access to land and financial services are still in place in some countries and advocates for policymakers to equalize inheritance rights and support women’s entrepreneurship to fight food insecurity in full force. The article provides a good understanding of the challenges faced by women in African countries and calls for systemic changes to ensure that women have equal access to land and entrepreneurship, which can bring major benefits to the economy, agricultural productivity, and food security.
FROM THE MEDIA: Large parts of Africa are currently experiencing record levels of hunger, and the trend is heading in a more worrying direction. West and Central Africa are seeing increasing food insecurity year after year, and tens of thousands of people across Burkina Faso, Mali, and Niger are expected to experience “catastrophic” hunger in the coming months. The situation is, in part, being made worse by climate change, which is increasing temperatures and changing weather patterns, compounding the hardship already caused by droughts. But there’s more to this food insecurity trend than climate change. Fighting these rising levels of food insecurity requires a whole-of-nation approach. Policymakers in these food-insecure countries should take the following actions: Equalize inheritance rights and support women’s entrepreneurship.
READ THE STORY: Atlantic Council
Wagner group surges in Africa as U.S. influence fades, leak reveals
Analyst Comments: The leaked documents underscore the growing concern among U.S. intelligence and military officials about the rapid expansion of Russia's influence in Africa. The Wagner group's expanding global footprint is seen as a potential vulnerability for Russia, especially with its deepening involvement in the war in Ukraine. The trove of documents reveals the U.S. government's efforts to disrupt Wagner's network of bases and business fronts with strikes, sanctions, and cyber operations. However, there is little evidence to suggest that these efforts have caused more than minor setbacks for the paramilitary group. The trove portrays Wagner as a relatively unconstrained force in Africa, undermining each country's ability to sever ties with its services and exposing neighboring states to its destabilizing activities. The documents also reveal that France is willing to strike Wagner if the paramilitary organization supports a coup in Chad, indicating the extent of Wagner's destabilizing activities in the region.
FROM THE MEDIA: According to leaked secret U.S. intelligence documents, the Wagner group is rapidly expanding its influence in Africa with the aim of establishing a "confederation" of anti-Western states. The documents reveal that Wagner is using its paramilitary and disinformation capabilities to support Moscow's allies, while causing instability in the region. U.S. officials have expressed alarm about Russia's increasing influence in Africa, leading to a push over the past year to find ways to disrupt Wagner's network of bases and business fronts with strikes, sanctions, and cyber operations. However, the trove of documents portrays Wagner as a relatively unconstrained force in Africa, expanding its presence and ambitions on that continent even as the war in Ukraine remains a problem for the Kremlin.
READ THE STORY: The Washington Post
The Hacker Who Hijacked Matt Walsh’s Twitter Was Just ‘Bored’
Analyst Comments: The article reports on a cyber attack that breached the Twitter account of right-wing commentator Matt Walsh, which highlights the potential dangers of SIM swapping, a technique that has been increasingly used by hackers to gain access to sensitive data. The attack was apparently perpetrated to stir up controversy, but it still raises concerns about the potential impact of cyber attacks on individuals' privacy and security. The article also highlights the need for individuals to take steps to protect themselves from such attacks, including using more secure forms of authentication and being cautious with their personal information online. The suspension of the journalist's Twitter account by the social media platform raises concerns about the potential censorship of journalists and the freedom of the press.
FROM THE MEDIA: Twitter suspended WIRED senior reporter Dell Cameron's account after he published an article regarding a hacker, who claimed to have compromised the Twitter account of right-wing commentator Matt Walsh. The hacker, who goes by the name Doomed, apparently used a technique known as SIM swapping to compromise Walsh's accounts. Doomed said that the whole purpose of the attack was to stir up controversy and sow chaos on Twitter, using Walsh's account to post a series of out-of-character posts, including jabs at fellow conservative media figures. The hacker also gained access to Walsh's private emails, including screenshots of emails between Walsh and Steven Crowder. Doomed claims that the hack caused no financial harm, threatened anyone, nor ruined anything and that it was merely "a few silly words on social media."
READ THE STORY: Wired
What does an ex-Pharma Bro do next? If it's Shkreli, it's an AI Dr bot
Analyst Comments: Shkreli's release of a medical chatbot has raised concerns about the accuracy and reliability of healthcare advice being provided to the public. Given Shkreli's controversial history and legal issues, there is a risk that people may get bad advice from the model and follow that advice, leading to harm. The fact that the California Medical Board has no jurisdiction over AI chatbots or websites that do not claim to be licensed to practice medicine in California raises questions about the regulation of medical chatbots and their impact on healthcare. It remains to be seen whether Dr. Gupta will have any significant impact on the healthcare industry or if its claims of providing better answers than other chatbots are valid.
FROM THE MEDIA: Martin Shkreli, the controversial entrepreneur, and former pharmaceutical executive has launched a medical chatbot called Dr. Gupta. The chatbot, which Shkreli claims is the world's first physician chatbot, is designed to dispense healthcare advice. However, it is not licensed to practice medicine and comes with a disclaimer that it does not provide actual medical advice. Dr. Gupta is based on ChatGPT and other proprietary services, and Shkreli claims that its intricate prompt topology enables it to provide better answers than ChatGPT alone. The California Medical Board, which oversees medical professionals' licensing in the state, has confirmed that it has no jurisdiction over AI chatbots or websites where individuals or entities are not claiming to be licensed to practice medicine in California.
READ THE STORY: The Register
CISA Adds 3 Actively Exploited Flaws to KEV Catalog, including Critical PaperCut Bug
Analyst Comments: The addition of these three vulnerabilities to the Known Exploited Vulnerabilities catalog by CISA highlights the importance of patching vulnerabilities in a timely manner. Cybersecurity companies such as Arctic Wolf and GreyNoise have detected active exploitation of unpatched servers and have called for the remediation of identified vulnerabilities. Organizations should take note of these developments and ensure that they are using up-to-date software and regularly patching vulnerabilities to avoid falling prey to cyberattacks.
FROM THE MEDIA: The US Cybersecurity and Infrastructure Security Agency (CISA) has added three security vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, as they are being actively exploited. One of the flaws is CVE-2023-28432, a MinIO Information Disclosure Vulnerability that exposes all environment variables in a cluster deployment, including MINIO_SECRET_KEY and MINIO_ROOT_PASSWORD. As many as 18 malicious IP addresses from various countries have attempted to exploit the flaw in the past 30 days. Another vulnerability, CVE-2023-27350, is a critical remote code execution bug affecting PaperCut print management software that allows remote attackers to bypass authentication and run arbitrary code. The third vulnerability, CVE-2023-2136, is a Google Chrome Skia Integer Overflow Vulnerability that allows attackers to perform a sandbox escape via a crafted HTML page.
READ THE STORY: THN
'EvilExtractor' All-in-One Stealer Campaign Targets Windows User Data
Analyst Comments: The use of sophisticated malware continues to be a popular method for cybercriminals to steal data and compromise systems. With phishing attacks being one of the most common ways to launch such an attack, it is crucial for organizations to train employees on how to spot and avoid such emails. Additionally, implementing multi-factor authentication and keeping software up to date can help protect against such attacks. As for the EvilExtractor tool, it highlights how even legitimate-seeming software can be repurposed by malicious actors for nefarious ends, underscoring the importance of vetting any third-party software before implementation.
FROM THE MEDIA: A phishing campaign that began in March has been actively targeting Microsoft operating system users in Europe and the US. Researchers from FortiGuard Labs have detailed the EvilExtractor attack chain, which starts with a legitimate-looking Adobe PDF or Dropbox link that deploys malicious PowerShell when opened or clicked, before leading to the modular EvilExtractor malware. The primary purpose of the malware appears to be to steal browser data and information from compromised endpoints and upload it to the attacker's FTP server. EvilExtractor was developed by Kodex as an "educational tool", according to the EvilExtractor report. However, cybercriminals are actively using it as an information stealer, FortiGuard Labs has found.
READ THE STORY: DARKReading
How ChatGPT—and Bots Like It—Can Spread Malware
Analyst Comments: Large language models like ChatGPT and Midjourney are being used to create convincing text, audio, and video that can be tailored to specific audiences. While these applications have been deployed in many areas, including web searches and children's books, they can also be used for nefarious purposes such as phishing attacks and the spread of malware. Persuasive and authentic-sounding text required for scams can now be generated easily, without human effort, and can be endlessly tweaked and refined for specific audiences. Although OpenAI has built safeguards into ChatGPT to prevent it from engaging in any malicious activities, cybercriminals are already finding ways to get around these safety measures. Criminal organizations could develop their own large language models to make their scams sound more convincing. The use of AI bots can produce text, audio, and video that sound natural and tailored to specific audiences, quickly and constantly on demand.
FROM THE MEDIA: The increased sophistication of natural language processing (NLP) models has enabled AI-powered scams that rely on social engineering to be pumped out with greater accuracy and in greater quantities than ever before. Although some safeguards have been put in place to stop LLMs like ChatGPT from being used for malicious purposes, cybercriminals are finding ways around them. There are two types of AI-related security threats to think about: tools like ChatGPT or Midjourney being used to get you to install something you shouldn't, and AI that's used to create text, audio, or video that sounds convincingly real. To avoid falling into these traps, always go to the original source first and double-check wherever possible.
READ THE STORY: Wired
Ukraine's Tech Minister Believes Ukraine Can Win Technology War Against Russia
Analyst Comments: The war between Ukraine and Russia has been ongoing for years and has involved various forms of technology. Both countries have been investing in drones, satellite communications, and other advanced technologies to gain an advantage on the battlefield. While it is difficult to predict which country will ultimately come out on top in this war of technology, it is clear that Ukraine is determined to compete with Russia and has made significant progress in developing its technological capabilities. However, it is important to note that the conflict between the two countries is a complex issue with many factors at play, and the outcome of any technological competition is just one aspect of this ongoing conflict.
FROM THE MEDIA: The ongoing conflict between Ukraine and Russia has not only manifested itself on the front lines but also in a war of technology as both countries compete to gain an advantage with their drones and satellite communications. Ukraine's minister in charge of technology expressed confidence in an interview with The Associated Press that his country has the motivation and abilities to out-innovate Russia in this war of technology. He stated that Ukraine had made significant progress in areas such as cybersecurity and AI and had a thriving startup ecosystem that could help to develop cutting-edge technology.
READ THE STORY: ET
Russian War Report: Russia cancels Victory Day parades and moves “Immortal Regiment” marches online
Analyst Comments: The ongoing conflict between Russia and Ukraine shows no signs of slowing down, with continued Russian offensive actions and Ukrainian defensive efforts in Eastern Ukraine. Russia's continued efforts to replenish its forces with volunteer formations, contract soldiers, and mobilized military personnel from ethnic regions of Russia like the Republic of Bashkortostan is a cause for concern. Reports of Russian-mobilized soldiers being coerced to join the Wagner Group are also troubling. The cancellation of Victory Day parades and moving the "Immortal Regiment" march online due to security concerns indicate that tensions remain high. The amplification of false stories about the Russian army's alleged destruction of a NATO bunker in Lviv by pro-Kremlin media is a reminder of Russia's propaganda and disinformation tactics to undermine its opponents.
FROM THE MEDIA: The Atlantic Council’s Digital Forensic Research Lab (DFRLab) continues to monitor Russia's movements across the military, cyber, and information domains as Russia continues its offensive actions against Ukraine, with Ukraine's defensive efforts ongoing. In the past few days, there has been an escalation of attacks on Ukrainian positions in the direction of Marinka, Avdiivka, and Bakhmut. The Ukrainian army reported repulsing more than 70 attacks by the Russian army in a single day. The Russian army continued to assault Bakhmut and Marinka on April 18 and April 19, as well as offensive operations in the Avdiivka area. The Ukrainian army has recorded more than 60 Russian attacks between April 18-19. On the night of April 20, the Russian army attacked the south and east of Ukraine with Shahed attack drones. Ten out of eleven drones were shot down, and sirens for Russian attacks were reported in many regions of Ukraine.
READ THE STORY: Atlantic Council
Security News This Week: Criminals Are Using Tiny Devices to Hack and Steal Cars
Analyst Comments: The rise of small hacking tools being used by criminals to steal cars highlights a new breed of car theft that is spreading across the U.S. These devices are becoming more accessible and cheaper, making it easier for thieves to steal even high-end luxury cars. The fact that encrypting traffic sent in CAN messages could help prevent these types of attacks is positive, but this would require a software update to be introduced, which could take time. The automotive industry needs to take note of this report and take measures to address these vulnerabilities.
FROM THE MEDIA: According to a report by Motherboard, car thieves are using small hacking tools to break into and steal vehicles. Criminals use Controller Area Network (CAN) injection attacks to steal cars without the need for keys. The hacking tools are sometimes hidden in Bluetooth speakers or Nokia 3310 phones. These devices allow thieves with very little technical experience to steal cars, even high-end luxury cars in as little as 15 seconds. The tools are available to purchase online for between $2,700 and $19,600. According to security researchers at Canis Labs, encrypting traffic sent in CAN messages would help to stop these types of attacks.
READ THE STORY: Wired
Breaking down of the US-Saudi ‘Oil Pact’
Analyst Comments: The article presents a compelling argument that OPEC+'s decision to cut crude output has negative implications for the US economy and could signal a shift in Saudi Arabia's geopolitical alliances away from the US. The article provides context for how the US-Saudi "oil for security pact" has historically functioned and how it is now facing significant challenges. However, the article could benefit from more information about the broader context of global oil markets and how they are affected by OPEC+ decisions, as well as potential strategies for the US to mitigate the economic impact of the cuts.
FROM THE MEDIA: Saudi Arabia and Russia's oil alliance, known as OPEC+, has decided to cut crude output for the second time since President Biden's visit to Saudi Arabia in the summer of 2021, a move that may have negative implications for the US economy, including higher inflation and recession risks. The OPEC+ decision may also signal a shift in Saudi Arabia's geopolitical alliances, as it increasingly coordinates oil production levels with Russia and brokers deals with China, while Western influence over the oil cartel declines. The US-Saudi "oil for security pact" has been a longstanding pillar of the energy market, but it appears to be wobbling due to a combination of factors, including the Khashoggi assassination, Biden's criticisms of Saudi Arabia, and OPEC+'s decision to cut production twice since Biden's visit. Saudi Arabia's high social spending and dependence on petrodollars to fund non-oil industries also play a role in its decision-making.
READ THE STORY: Modern Diplomacy
DEA infiltration of Mexican cartels should not be seen as a novelty
Analyst Comments: The DEA's infiltration into a criminal group in Mexico without informing the Mexican government has further strained the already complicated relationship between the US and Mexico. President Lopez Obrador's reaction reflects the sensitivity of the issue and his concern about the US's unauthorized activity within Mexico's borders. The development could have far-reaching consequences on the bilateral relationship and underscores the need for better communication and coordination between the two countries law enforcement agencies.
FROM THE MEDIA: The president of Mexico, Andres Manuel Lopez Obrador, has described the DEA's "infiltration" into the criminal group Los Chapitos as abusive interference and assured that Mexico was not informed. The DEA infiltrated the Sinaloa cartel faction to investigate the origin of the fentanyl health crisis affecting the US. Erika Pania, a specialist in the Mexico-United States relationship, stated that the case highlights the complexity of the relationship, and the consequence of the DEA's actions on the bilateral relationship remains unclear. President Lopez Obrador announced that he will "protect" the information of the Armed Forces, which are "objects of espionage" by the US Pentagon.
READ THE STORY: CAL18
Google moves to keep public sector cybersecurity vulnerabilities leashed
Analyst Comments: The establishment of the Google Cloud Alliance with CIS is a positive step towards advancing digital security in the public sector in the US. The collaboration brings together two cybersecurity experts to address the rapidly changing cybersecurity needs of the state, local, tribal, and territorial government organizations, which have been historically underserved in this area. The partnership will allow the organizations to offer best-in-class, cost-effective cybersecurity solutions and operational support, which is critical to securing government operations and the broader technology ecosystem. Additionally, Google's recent launch of the Assured Open Source Software service for Java and Python ecosystems and the establishment of the Hacking Policy Council and Security Research Legal Defense Fund shows that the tech giant is committed to cybersecurity and building a more secure digital world.
FROM THE MEDIA: Google Cloud and The Center for Internet Security (CIS) have announced the formation of the Google Cloud Alliance aimed at promoting digital security in the public sector. The CIS was established in 2000 to provide cybersecurity protocols and standards, such as CIS Critical Security Controls and CIS Benchmarks, and offers support to state and local governments in the US in combating cyber threats. The new partnership will combine the expertise of CIS with the Google Cybersecurity Action Team and its Threat Horizons reports to enhance cybersecurity practices in the public sector.
READ THE STORY: TechRepublic
Hacker Group Names Are Now Absurdly Out of Control
Analyst Comments: While Microsoft's new naming system for hacker groups may be more distinct, memorable, and searchable, some cybersecurity experts argue that it is absurd and counterproductive for actual cybersecurity analysis. The industry needs a standard naming convention that can be adopted across the industry, but it seems unlikely that companies will stick to it. The proliferation of different names for the same group adds to the confusion and undermines the credibility of the cybersecurity industry.
FROM THE MEDIA: Microsoft has recently announced a new naming system for the hundreds of hacker groups it tracks. Instead of its previous scientific-sounding system, it will now give hacker groups two-word names that indicate what country the hackers are believed to work for and whether they are state-sponsored or criminal, along with a weather-based term. For example, Phosphorous, an Iranian group that targeted US critical infrastructure, is now called Mint Sandstorm, and Russia's dangerous cyberwar-focused military hacker unit, Iridium, is now called Seashell Blizzard. However, critics claim that this new system is counterproductive for actual cybersecurity analysis as it locks in educated guesses about the national loyalties of hackers, and forces analysts and customers across the industry to revise their databases and even some of their products to match Microsoft's new naming scheme.
READ THE STORY: Wired
Taiwan asks the US if it could chill out on the anti-China rhetoric
Analyst Comments: The article highlights the complex situation that Taiwan is facing in the ongoing chip war between the US and China. While the Taiwanese semiconductor industry is a major contributor to the country's economy, Taiwan is caught between the US, which is trying to reduce its reliance on imported chips, and China, which considers Taiwan a renegade province. The article also notes that the US and China's chip war is increasing global dependence on South Korea for memory chips. Additionally, the makers of chip manufacturing equipment reportedly expect sales to China to rise this year despite US sanctions. Overall, the article provides a glimpse into the challenges faced by Taiwan and the broader semiconductor industry in the face of geopolitical tensions.
FROM THE MEDIA: Taiwanese officials have reportedly held informal discussions with their US counterparts, urging them to scale back on anti-China rhetoric on chips made in Taiwan. The discussions were prompted by fears that the scare stories about relying on Taiwan-made chips are hurting the country's business interests. US Commerce Secretary Gina Raimondo had earlier condemned American reliance on chip supplies from Taiwan as "untenable" and "unsafe." Taiwan's semiconductor industry is a major contributor to its economy, but the country is caught between China and the US. While Taiwan can count on US help if China invades, Washington is trying to minimize its reliance on imported chips by building up its own domestic manufacturing capacity through CHIPS Act funding.
READ THE STORY: The Register
Items of interest
China vs US: Making of the Second Cold War
Analyst Comments: The article provides a comprehensive analysis of the factors that have contributed to the changing global power dynamics and the challenges faced by the US in maintaining its dominance. It highlights the economic and societal effects of globalization and the loss of manufacturing jobs to China, as well as the consequences of the unsuccessful invasions of Iraq and Afghanistan and the 2007 financial crisis. The article also provides insights into the emergence of China as a major economic and political power and the US's response in the form of a "New Cold War" strategy. Overall, the article presents a thought-provoking analysis of the changing global power dynamics and the challenges faced by the US in maintaining its dominance. However, it could have benefited from a more nuanced discussion of the factors that have contributed to China's rise as a major economic and political power, as well as the potential consequences of the "New Cold War" strategy.
FROM THE MEDIA: The article discusses the rise of the United States as a global superpower following the collapse of the Soviet Union and the challenges it faced in maintaining its dominance in the face of changing global dynamics. It highlights the economic and societal effects of the loss of manufacturing jobs to China, the unsuccessful invasions of Iraq and Afghanistan, and the 2007 financial crisis. The article also discusses the emergence of China as a major economic and political power and the US's response in the form of a "New Cold War" strategy.
READ THE STORY: Modern Diplomacy
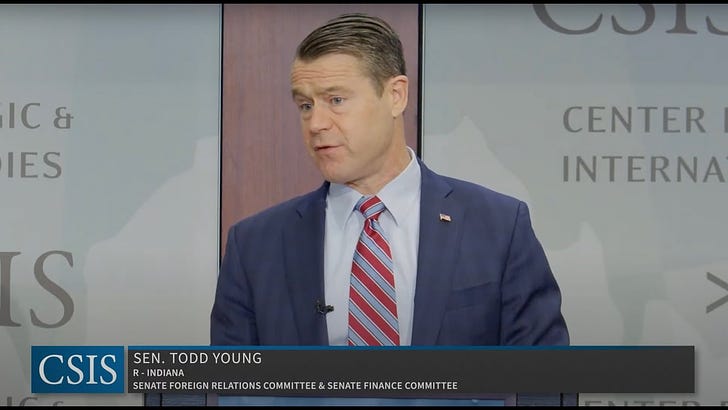
Countering Chinese Economic Coercion (Video)
FROM THE MEDIA: The Center for Strategic and International Studies (CSIS) hosted an event to launch a new report titled "Deny Deflect Deter: Countering China's Economic Coercion," funded by the Smith Richardson Foundation. The report proposes a counter-strategy to deter China's economic coercion by building resilience and providing relief to targeted countries. The report's findings are based on 16 months of study and eight case studies of Chinese economic coercion over the past decade. The report also suggests a proactive diplomatic messaging campaign to point to US efforts to build resiliency and to draw attention to China's coercion.
US-China Relationship: What's Next (Video)
FROM THE MEDIA: The transcript is a discussion about the complex relationship between the US and China, with a focus on economic and security issues. The panelists include experts on China and its history, and they discuss the origins of the current tensions between the two countries. They also examine China's current economic situation and its political system, as well as the role of Taiwan in the relationship. The panelists share different perspectives on how the US and China can move forward, and the importance of understanding each other's perspectives.
These open-source products are reviewed by analysts at InfoDom Securities, providing possible context about current media trends related to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not endorse any third-party claims made in their original material or related links on their sites; the opinions expressed by third parties are theirs alone. For further questions, please contact InfoDom Securities at dominanceinformation@gmail.com.