Wednesday, April 12, 2023 // (IG): BB // Financial Enabler // Coffee for Bob
Psyops run by Russian intelligence reflect HUMINT crisis, set to focus on further falsification of documents
Analyst Comments: Russian intelligence is expected to release falsified documents allegedly originating from US government agencies and NATO Allies' government bodies in the next 30-45 days. The objective of these leaks is to discredit the US and its military-technical cooperation with Ukraine. The Kremlin is using "leaks" to validate its narratives and political statements after Russian intelligence was hit hard in the US and Europe. Russian intelligence is struggling with limitations, coordination issues, and a lack of creativity among operatives. It is expected that cyber operations will intensify, and Russia will leverage its capabilities along with those from China, Iran, and North Korea.
FROM THE MEDIA: The Russian government is reportedly planning to release a series of falsified documents, disguised as leaks from US and NATO government agencies, in an attempt to discredit the US and its military cooperation with Ukraine. The release of such documents is expected to take place within the next 30-45 days. Russian intelligence operations are being stepped up in an effort to imitate Kremlin propaganda narratives and statements. Although the efficiency of such operations is affected by the degrading environment in Russian intelligence circles, the Russian government is likely to intensify its cyber domain operations with the help of China, Iran, and North Korea.
FBI warns of cybercriminals posing as PRC to target Chinese communities
Analyst Comments: These scammers claim to be law enforcement officers or prosecutors from the People's Republic of China (PRC), accusing the victims of financial crimes and threatening them with arrest or violence if they don't pay. The criminals exploit the well-publicized efforts by the PRC government to harass and repatriate individuals living in the US to give their scam plausibility. They often call their victims, sometimes using spoofed numbers to make it appear as though the call is from a Chinese ministry, bureau, or US-based consulate. It is worth noting that the Chinese government has been accused of using "special police" to govern Chinese nationals living abroad. These special police are tasked with monitoring Chinese nationals and detaining them if they are suspected of activities deemed harmful to the Communist Party. The Chinese government has defended this practice, stating that it is necessary to protect the country's national security.
FROM THE MEDIA: The FBI has issued a warning regarding cybercriminals posing as members of China's government and targeting Chinese nationals living in the US in an effort to defraud them. The criminals impersonate law enforcement officers or prosecutors from the People’s Republic of China (PRC) and threaten victims with arrest or violence for alleged financial crimes. The FBI has advised people to be cautious of any accusations of crimes being made against them from a foreign country, not to provide personal or financial information to anyone they don't know, and to report any scams to the FBI's Internet Crime Complaint Center. This alert is similar to a campaign the FBI announced in October of last year, where PRC security and intelligence agents were accused of conducting surveillance and engaging in a campaign to harass and coerce a US resident to return to the PRC as part of an international extralegal repatriation effort known as "Operation Fox Hunt."
READ THE STORY: The Record
Uncle Sam threatens AI with its nastiest weapon: An audit
Analyst Comments: The NTIA's AI Accountability Request for Comment could be the first step towards regulation in the US. While the Biden Administration has issued guidance aimed at protecting US democracy as AI technology encroaches on society in its AI Bill of Rights, it has yet to pass any laws. The initiative shows the US government is taking AI accountability seriously and is open to feedback from the public on how to shape policies that will help to create earned trust in AI systems.
FROM THE MEDIA: The National Telecommunications and Information Administration (NTIA), a US government agency responsible for advising the President on technological and regulatory matters related to the telecommunications industry, has opened an "AI Accountability Request for Comment". This request for public comments seeks feedback on policies that can support the development of AI audits, assessments, certifications, and other mechanisms to create earned trust in AI systems. The aim is to provide assurance that an AI system is trustworthy, similar to how financial audits create trust in the accuracy of a business' financial statements. The NTIA wants to encourage regulators and businesses to work together and support the responsible deployment and development of AI technology.
READ THE STORY: The Register
Tracing cryptocurrency: Q&A with the PhD candidate and her adviser who proved it wasn't anonymous
Analyst Comments: Meiklejohn and Savage's research focused on the privacy concerns associated with Bitcoin transactions. They wanted to develop techniques for identifying individuals or entities associated with Bitcoin addresses or pseudonyms. By clustering together different types of addresses, they could identify large exchanges or individual users. They realized that they could only go so far with their research without knowing who these entities were, so they started interacting with entities in the Bitcoin ecosystem who were willing to interact with them. This primarily involved opening accounts with exchanges or wallet services and creating transactions with them.
FROM THE MEDIA: Dark web markets have long assumed that the use of cryptocurrency makes their transactions untraceable. However, a PhD candidate named Sarah Meiklejohn published a paper in 2013 that revealed the blockchain, the digital ledger that records cryptocurrency transactions, holds clues to connect these underground purchases to real-world individuals. She and her adviser, Stefan Savage, discovered that they could identify pseudonyms and cluster multiple bitcoin addresses to expose illegal activities. They accomplished this by interacting with multiple entities within the Bitcoin ecosystem and buying items on the dark web, ultimately identifying over 200,000 addresses controlled by Silk Road.
READ THE STORY: The Record
China makes rare backtrack over no-fly zone near Taiwan
Analyst Comments: The announcement of a no-fly zone near Taiwan by the Chinese government has sparked concerns about the potential disruption to international travel and diplomatic engagements, as well as potential implications for regional stability. The move has been interpreted as a form of harassment towards Taiwan amid escalating tensions between the two countries. The fact that US Secretary of State Antony Blinken will need to fly through the no-fly zone on his way to attend a G7 foreign ministers' meeting in Japan raises further concerns about potential diplomatic fallout. The planned military exercises in the Beibu Gulf, close to Vietnam's border, have also been viewed as a provocation by some. The South Korean government has stated that the closure is due to falling debris from a satellite launch vehicle, but two experts familiar with satellite launch procedures have noted that such closures typically last only a few hours, and that other countries would usually avoid blocking such a busy airspace.
FROM THE MEDIA: China's government made an unexpected reversal on plans to block some of the busiest airspace in the world near Taiwan for three days, causing confusion over Beijing’s priorities in handling its ongoing dispute with Taipei and Washington. The Chinese government notified Taiwan and several other countries on Tuesday of the intended no-flight zone between April 16 and 18, which was perceived as a sharp escalation of tensions, coming just after China completed three days of military manoeuvres around Taiwan aimed at punishing the country for its president Tsai Ing-wen meeting US House Speaker Kevin McCarthy in California the previous week. However, on Wednesday afternoon, Taipei said Beijing had shortened the duration of the airspace closure to just 27 minutes on Sunday after fierce protests from Taiwan. The original plan would have affected a crucial location in east Asian air routes, which is a main transport artery in the western Pacific.
READ THE STORY: FT
Breaking down North Korea's advancing cyber prowess - mastermind in 3CX Supply Chain Attack
Analyst Comments: Experts caution against underestimating the regime's cyber threat, which has traditionally been viewed as a means for funding the government. The North Korean hackers, who are often hand-selected and trained from a young age, have successfully executed supply chain attacks, impersonated journalists and researchers, and exploited vulnerabilities to steal cryptocurrencies and conduct ransomware attacks. The regime's cyber operations serve a dual purpose of generating funds and spying on the US, South Korea, and their allies. While North Korea's cyber capabilities are often overshadowed by those of China and Russia, the US intelligence community has identified the country as a maturing cyber threat capable of causing temporary disruptions to critical infrastructure and business networks.
FROM THE MEDIA: According to media reports, North Korea's cyber threat should not be underestimated, as the country's hackers have been responsible for some of the most severe cyberattacks and espionage campaigns in recent years. They are often hand-selected and trained from a young age to join the regime's hacking teams, and their activities serve a dual purpose of generating funds for the government and spying on the US, South Korea, and their allies. The regime's cyber operations are technically adept and creative, with recent attacks including supply chain attacks, impersonation of journalists and researchers, and the exploitation of vulnerabilities to steal cryptocurrencies and conduct ransomware attacks. Despite being overshadowed by the cyber capabilities of China and Russia, the US intelligence community has identified North Korea as a maturing cyber threat capable of temporarily disrupting critical infrastructure and business networks. The regime is also suspected of using stolen funds to support its nuclear programs, and its cyber operations are reorganized periodically to keep the precise structure under wraps.
Another zero-click Apple spyware maker just popped up on the radar again
Analyst Comments: The discovery of the QuaDream malware highlights the proliferation of commercial spyware, an issue that has been growing in recent years. The use of zero-click exploits, like the one used to deliver the Reign malware, poses significant risks to individual privacy and security. The involvement of little-known companies like QuaDream and their clients, including governments with questionable human rights records, underscores the lack of regulation and accountability in the commercial spyware industry. The similarities between QuaDream's Reign and NSO Group's Pegasus spyware further highlight the problem. While Apple has fixed the vulnerability used in the ForcedEntry exploit, and Microsoft and Citizen Lab have provided indicators of compromise, the use of zero-click attacks makes detection and prevention difficult.
FROM THE MEDIA: Reports from Microsoft and The University of Toronto's Citizen Lab state that a malware believed to have been developed by QuaDream, a little-known Israeli commercial spyware maker, has been found on devices belonging to journalists, politicians, and an NGO worker in multiple countries. The malware, marketed as Reign, was delivered via a zero-click exploit that targeted Apple devices running iOS 14. The exploit used a vulnerability in the iOS calendar app to automatically add backdated events to a target's calendar without their knowledge or consent. Once the malware was operational, it could exfiltrate various device, carrier, and network info, retrieve files, use the camera, monitor calls, access the iOS keychain, generate iCloud one-time passwords, and more. QuaDream uses a subsidiary known as InReach to sell Reign to government customers outside of Israel, with clients in Singapore, Saudi Arabia, Mexico, and Ghana.
READ THE STORY: The Register
Misconfiguration Allowed For Manipulation of Bing Search Results, Attacks on Users
Analyst Comments: The Microsoft misconfiguration error discovered by Wiz researchers highlights the importance of paying attention to the seemingly minor aspects of security configuration, as they can create major vulnerabilities that can be easily replicated. While Microsoft has patched the vulnerability, it is unclear how long the vulnerability existed and if it was exploited by threat actors. The incident underscores the need for organizations to prioritize regular security audits and testing, as well as to stay vigilant against potential vulnerabilities in third-party applications.
FROM THE MEDIA: Researchers with Wiz discovered a vulnerability, named "BingBang," in Microsoft's Azure Active Directory that allowed attackers to manipulate Bing search results and potentially steal Office 365 credentials. The vulnerability was due to a configuration issue that was easy to replicate in Azure Active Directory multi-tenant apps, and approximately 25% of the apps scanned were found to be vulnerable. The issue was reported to Microsoft, and a patch was released prior to the publication of the vulnerability. The incident adds to a string of Azure-related security issues over the past few years.
READ THE STORY: CPO
Exploiting Server Side Request Forgery (SSRF) in an API
Analyst Comments: The article provides a comprehensive overview of SSRF vulnerabilities and the ways they can be exploited. The author's explanation of the different types of SSRF vulnerabilities and their potential impacts is clear and informative. The article is well-structured and provides practical tips for identifying and testing SSRF vulnerabilities. However, the article could benefit from more concrete examples of real-life SSRF attacks and their consequences. Additionally, the article could have provided more information on how to prevent and mitigate the impact of SSRF attacks beyond implementing proper security controls and regular vulnerability tests.
FROM THE MEDIA: Server Side Request Forgery (SSRF) is a security vulnerability that allows a malicious threat actor to induce a web application or API to perform unauthorized actions. This can result in sensitive data leaks, access to files and resources, remote code execution, or even server crashes. Detecting SSRF vulnerabilities can be challenging, as some cases can be elusive and tricky to pinpoint. Common areas of vulnerability include parameters, webhooks, file imports, and PDF generators. SSRF attacks can be prevented by implementing proper security controls and conducting regular vulnerability tests. However, attackers can still bypass these protections by using exotic URL schemas, hostnames instead of IPs, non-standard IP notation, and open redirects.
READ THE STORY: Security Boulevard
Healthcare websites are being attacked with fake requests
Analyst Comments: Healthcare organizations need to be aware of the potential impact of DNS NXDOMAIN flood DDoS attacks and take proactive measures to mitigate them. HC3 recommends several mitigations and actions, such as blackhole routing/filtering suspected domains and servers, implementing DNS Response Rate Limiting, and applying rate limiting on traffic to overwhelmed servers. Organizations should remain cautious when blocking IPs, as this could result in legitimate users being prevented from accessing public services.
FROM THE MEDIA: The Health Sector Cybersecurity Coordination Center (HC3) has warned healthcare organizations of distributed denial-of-service (DDoS) attacks that could potentially shut down their websites. HC3 received information from a trusted third party about these attacks that have been ongoing since November. The DDoS attacks are flooding targeted networks and servers with fake Domain Name Server (DNS) requests for non-existent domains (NXDOMAINs). As a result, the DNS server will spend time trying to locate something that does not exist instead of processing legitimate user requests, slowing down the server and preventing authorized users from gaining access to the website or services. These attacks are carried out by large botnets, making them difficult to detect and block. If network providers cannot control or mitigate the attack, it may lead to customers being unable to access their websites and services.
READ THE STORY: Healthcare Finance
US cyber chiefs warn AI will help crooks, China develop nastier cyberattacks faster
Analyst Comments: Rob Joyce's comments provide valuable insight into how attackers are using AI tools to refine their operations and develop more sophisticated and targeted attacks. The fact that attackers are using machine learning to develop better phishing lures and identify sensitive data underscores the need for organizations to be proactive in implementing measures to defend themselves against such attacks. Furthermore, Joyce's remarks highlight the need for organizations to remain vigilant in their approach to security, and to focus on developing tools that can give them the upper hand in defending against attacks.
FROM THE MEDIA: The director of the NSA's Cybersecurity Directorate, Rob Joyce, warns that while AI is not yet being used for automated attacks that can rip through systems, machine learning and chatbot technologies are "the tools that are going to flow and increase the pace of the threat". Attackers can use ML software to craft better phishing lures and scan larger volumes of data to identify valuable information, while also automating several stages of a cyberattack, such as generating boilerplate code for malware, sending out messages and gathering data on a target. Meanwhile, network defenders can also leverage AI to gain an advantage over attackers. The remarks were made during Joyce's keynote speech at CrowdStrike's Government Summit, where he also identified Russia, China, Iran and North Korea as major nation-state threats, and said that the lack of societal resilience shown during the Colonial Pipeline attack highlighted the need for a sustainable security posture.
READ THE STORY: The Register
Starlink opens final frontier for radio astronomers
Analyst Comments: The GO-LoW project is a visionary proposal that could enable the observation of exoplanet magnetospheres and significantly aid the discovery of the mechanisms and nature of energetic sources of low-frequency electromagnetic radiation in the cosmos. Starlink's high-performance swarm of data-driven satellites could make VLBI at wavelengths below 10 MHz possible. However, there are several challenges associated with the project, such as how to deal with the huge amounts of data over such a long range and what mixture of antennas and sensors will be practical and useful on such small spacecraft. Nonetheless, GO-LoW could open up a new era of radio astronomy, paving the way for new discoveries and techniques for other missions.
FROM THE MEDIA: A group of astronomers at MIT's Haystack radio observatory has proposed the Great Observatory for Long Wavelengths (GO-LoW) project, which could exploit SpaceX's Starlink constellation of internet satellites for radio astronomy purposes. The project aims to enable Very Long Baseline Interferometry (VLBI) at wavelengths below 10 MHz, which is currently blocked by Earth's ionosphere. Starlink's swarm of small, data-driven satellites could offer a solution by living in clusters at the Lagrange 4 and 5 points, which are inherently stable and located 150 million km ahead of and behind Earth. The project will begin to deal with the huge amounts of data over such a long range, but many questions still need to be answered.
READ THE STORY: The Register
Experts Eye Future of U.S.-China Relations
Analyst Comments: The article discusses the recent tensions in the U.S.-China relationship and the opinions of four experts on how this relationship may unfold in the next 10 years. The experts agree that there are increasing tensions between the two nations, particularly in areas such as trade, technology, and human rights, and there is a lack of constructive forces to push towards a more positive direction. While some believe that the competition between China and the U.S. is driven by ideology, others argue that it is primarily a cyber-political competition centered around digital technology superiority.
FROM THE MEDIA: The recent meeting between U.S. President Joe Biden and Chinese President Xi Jinping aimed to stabilize relations, but tensions have increased due to incidents such as the U.S. shooting down an alleged Chinese spy balloon and U.S. House Speaker Kevin McCarthy meeting with the president of Taiwan. China responded by staging combat drills to simulate sealing off Taiwan, and by welcoming French President Emmanuel Macron to counter America’s goal of creating a global coalition to resist Chinese policies. Four scholars were asked to predict how the U.S.-China relationship will unfold over the next 10 years, and they expressed concerns about the lack of constructive forces and the trend towards more security-related actions, weapons development, and military buildup, increasing the possibility of accidents.
READ THE STORY: VOA
Beijing lists the stuff it wants generative AI to censor
Analyst Comments: The proposed regulations highlight China's efforts to regulate AI and LLMs, which have been a national policy priority. The regulations are consistent with the Chinese government's preference for tech sourced from overseas to be sold and operated by local companies. China's tech giants are racing to bring generative AI tools to market, and while the government supports the development and use of AI algorithms and frameworks, it will be difficult to fill the wish list of adhering to nuanced censorship rules and protecting IP, company secrets and user information. The proposed regulations put a lot of responsibility on the designers of AI tools and the providers of generative AI services, who may face fines and possible criminal investigations for violating the rules.
FROM THE MEDIA: China has released proposed regulations for the development and use of generative AI chatbots, with the document calling for AI-generated content to "reflect the core values of socialism" and prohibiting subversion of state power, terrorism, extremism, ethnic hatred and discrimination. The draft rules, published by the Cyberspace Administration of China, put the onus on designers of AI tools to prevent discrimination, based on race, ethnicity, belief, country, region, gender and occupation, through careful selection of training data, algorithm design and other optimizations. Users must register with their real names, and companies providing generative AI services will be responsible for privacy and other measures. The rules debuted after Huawei and Alibaba prepared updates to their generative AI models, while companies like Baidu pressed on with early services, all part of a race to be the first viable Chinese ChatGPT analogue.
READ THE STORY: The Register
Tech industry’s pain is NSA’s gain, cyber leader says about layoffs
Analyst Comments: The layoffs at tech companies have created a pool of talent for the NSA to tap into. The agency has been expanding its workforce, especially after the SolarWinds hack. The agency's cybersecurity role will continue to be critical in the face of rising cyber threats. However, the increase in recruitment by the agency should not come at the cost of the civil liberties of Americans. The NSA should ensure that its hiring process is transparent and inclusive, with a focus on recruiting diverse talent.
FROM THE MEDIA: The National Security Agency (NSA) has reported an increase in recruitment efforts in the wake of waves of layoffs across major tech giants. The NSA’s Director of Cybersecurity, Rob Joyce, stated during an event at the Center for Strategic and International Studies in Washington that the agency had seen an “uptick” in recruitment, with a pool of mid-career professionals seeking opportunities in the intelligence community. While Joyce did not provide specific figures, tech layoffs have affected tens of thousands of employees across Amazon, Meta, Microsoft, Google and Apple in recent months. The NSA has been on a hiring push since January, with its talent management senior strategist, Christine Parker, stating the agency would be seeking to scoop up qualified applicants. Joyce, who has worked for the agency for 34 years, referred to himself as an NSA “lifer” and spoke of the mission being “spectacular” with the opportunity to work with smart people on hard and meaningful problems keeping people at the agency.
READ THE STORY: The Record
Cybercriminals Turn to Android Loaders on Dark Web to Evade Google Play Security
Analyst Comments: The fact that malicious loader programs are being purchased and used to Trojanize Android applications is not surprising, given that attackers can monetize such tools and also target a large number of users through apps downloaded from the Google Play Store. This underlines the need for robust mobile security solutions to protect against such threats, alongside user education and a strong security culture. To avoid such malicious apps, users are recommended to install apps from trusted sources, scrutinize app permissions, and keep their devices updated.
FROM THE MEDIA: Criminals are reportedly buying malicious loader programs, costing up to $20,000, as a way to Trojanize Android applications and bypass Google Play Store defenses. A new report by Kaspersky reveals that the most popular types of applications for hiding malware and unwanted software are cryptocurrency trackers, financial apps, QR-code scanners, and dating apps. Dropper apps are the primary means of threat actors for sneaking malware through the Google Play Store, which masquerade as seemingly innocuous apps. They are introduced as malicious updates once cleared by the review process and these apps amass a significant user base. Such apps incorporate anti-analysis features that detect if they are being debugged or installed in a sandboxed environment, and in those cases, halt their operations on the compromised devices.
READ THE STORY: THN
Why Biden hasn’t loaned weapons to Ukraine
Analyst Comments: Current administration has not yet utilized its Lend-Lease authority to send weapons to Ukraine, despite the option being available. Instead, the administration has committed nearly $35 billion in security assistance to Ukraine since Russia's invasion, coming from drawdowns of US military stocks or future weapons production. One reason for not using Lend-Lease could be due to the administration prioritizing security assistance that Ukraine would not have to pay back for. However, some lawmakers are not satisfied with the option remaining unused and believe using Lend-Lease is a better plan than continuing to give weapons away for free. The White House and Congress are currently questioning why the administration is not using Lend-Lease, with some believing it could address concerns about the US giving away too much to Ukraine. On the other hand, some argue that using Lend-Lease may not solve the problem of America's dwindling weapons stockpile and may even incentivize the transfer of scarce weapons to Ukraine. Despite this, the administration states that Ukraine has what it needs for this stage of the war and will receive more weapons and equipment if needed.
FROM THE MEDIA: The Biden administration has not yet used its Lend-Lease authority to gift weapons to Ukraine, according to senior administration officials and lawmakers. Congress granted the Biden administration Lend-Lease authority last year, enabling the US to gift weapons to Ukraine with the expectation of reimbursement down the line. However, the administration has not yet used that option due to the congressionally approved pot of money that hasn’t been zeroed out yet. There is bipartisan support for sending weapons to Ukraine, and some lawmakers are not satisfied that the Lend-Lease option remains unused. However, the administration stated that Ukraine has what it needs for this stage of the war, and it will get more weapons and equipment if facts on the ground change.
READ THE STORY: Politico
Claim a Canadian energy company was target of Russian cyberattack highlights our vulnerability, but could just be fake
Analyst Comments: The claim made by the Russian hackers, if true, highlights the threat of cyberattacks on critical infrastructure such as oil and gas companies, which could cause severe disruption to critical systems and energy supplies. However, skepticism exists over the claim, with some experts warning that it could be false or part of a disinformation campaign, and others suggesting that Zarya's ability to cause real damage to oil and gas companies may be low. Regardless, the incident highlights the vulnerability of critical infrastructure systems to cyberattacks, which is an even greater threat in the age of the Internet of Things, where nearly every electronic device is connected to the internet. It is crucial to protect these systems from attacks and ensure that security measures are taken seriously to prevent potential cyberattacks that could cause significant damage and disruptions.
FROM THE MEDIA: A group of Russian hackers called Zarya claimed to have caused damage to a Canadian natural gas company on February 25, according to leaked Pentagon documents. The group's primary motive is to advance Russia's political interests rather than make money. They shared screenshots with Russian Federal Security Service officers that showed they had acquired the ability to increase valve pressure, disable alarms, and initiate an emergency shutdown of an unspecified gas distribution station. The officers anticipated that a successful attack would cause an explosion at the gas distribution station and were monitoring Canadian news reports for any indications of an explosion. However, some experts warn that the claim could be false or part of a disinformation campaign, while others say that Russia's targeting of critical infrastructure should not be entirely dismissed.
READ THE STORY: The Star // NBC
Newly Discovered "By-Design" Flaw in Microsoft Azure Could Expose Storage Accounts to Hackers
Analyst Comments: The discovery of a "by-design flaw" in Microsoft Azure represents a significant threat to the security of cloud-based systems. As more companies migrate to the cloud, attackers are increasingly targeting cloud environments. The flaw allows attackers to execute remote code and gain access to critical business assets, potentially causing extensive damage. While Microsoft has acknowledged the issue and plans to update how Functions client tools work with storage accounts, organizations must take steps to protect themselves by disabling Shared Key authorization and using more secure authentication methods.
FROM THE MEDIA: Cybersecurity firm Orca Security has reported a "by-design flaw" in Microsoft Azure which could be exploited by attackers to execute remote code, gain access to storage accounts, and move laterally in the environment. The flaw involves Shared Key authorization, which is enabled by default on storage accounts, and the use of Azure Functions to steal access tokens of higher-privileged identities. These access tokens can be stolen, allowing the attacker to escalate privileges, move laterally, access new resources, and execute a reverse shell on virtual machines. Organizations are advised to consider disabling Azure Shared Key authorization and using Azure Active Directory authentication instead.
READ THE STORY: THN
How China developed its first large domestic airliner to take on Boeing and Airbus
Analyst Comments: This news report highlights China's efforts to create a passenger jet, the C919, that looks similar to Boeing's 737, and the concerns it raises among US national security experts. The report indicates that China's success with the C919 could be achieved through economic pressure and espionage, including forced technology transfer and intense hacking efforts to obtain corporate secrets. This news could be of interest to people in the aviation industry, policymakers, and national security experts who are concerned about China's efforts to gain technological superiority.
FROM THE MEDIA: China's state-owned aircraft manufacturer has created a large domestic airliner, the C919, which national security experts argue is a threat to the US economy and a chance for China's military to access American-made technology. The C919 is designed to look similar to the Airbus A-320 and the Boeing 737, a move that critics argue was achieved through economic pressure and espionage, including forced technology transfer and intense hacking efforts to obtain corporate secrets. Experts believe the C919 is a chance for China to eventually dominate one of the world's largest markets for jets, potentially costing the US economy up to $1.5tn over the next 20 years.
READ THE STORY: CBS News
Ukrainian hackers say they have compromised Russian spy who hacked Democrats in 2016
Analyst Comments: The hack of Morgachev's emails could potentially provide valuable information about Russia's hacking operations, including the 2016 hack and leak of emails from the DNC and Clinton's campaign. While Reuters was not able to fully corroborate the claim by Cyber Resistance, the fact that the information provided by the hackers aligns with previously leaked data adds credibility to the claim. The lack of response from the Russian Embassy in Washington and the FBI suggests that they are either unaware of the hack or are choosing not to respond publicly. It remains to be seen what impact, if any, this hack will have on US-Russia relations or the ongoing tensions between Ukraine and Russia.
FROM THE MEDIA: Ukrainian hacking group, Cyber Resistance, has claimed responsibility for hacking the emails of Lt. Col. Sergey Morgachev, who is accused of being involved in the 2016 hack and leak of emails from the Democratic National Committee (DNC) and Hillary Clinton's campaign. Cyber Resistance posted a message on Telegram on Monday announcing the hack and shared some of Morgachev's personal information with Ukrainian publication InformNapalm. While Reuters was unable to fully corroborate the claim, the leaked information provided by the hackers aligns with previously leaked data. It is unclear what information the hackers were able to obtain, but Morgachev's emails may provide insight into Russia's hacking operations.
READ THE STORY: Arab News
China: Taiwan heading for ‘stormy seas’ under President Tsai Ing-wen
Analyst Comments: The ongoing tensions between China and Taiwan continue to escalate, with China accusing Taiwan's President of provocation and pushing Taiwan into "stormy seas." The military exercises conducted by China in response to Tsai's visit demonstrate the volatile situation between the two sides, with China's continued military activities around Taiwan. The situation underscores the ongoing geopolitical tensions in the region and highlights the fragility of Taiwan's status as a self-ruled island.
FROM THE MEDIA: China's Taiwan Affairs Office spokesperson, Zhu Fenglian, accused Taiwan's President, Tsai Ing-wen, of pushing Taiwan into "stormy seas" after Tsai's recent visit to the United States and stops in Guatemala and Belize. Tsai's trip included a meeting with US House Speaker Kevin McCarthy and was seen as showing the world Taiwan's determination to defend freedom and democracy. China views Tsai as a separatist and has rebuffed repeated calls from her for talks. In response to the visit, China held military exercises around Taiwan designed to show that it could forcefully retake control of the self-ruled island, which China claims as its own.
READ THE STORY: Arab News // Modern Diplomacy
Items of interest
Why we think Intel may be gearing up to push its GPU Max chips into China
Analyst Comments: Intel's decision to cancel its mid-tier Data Center GPU Max 1350 accelerator card and to introduce a new GPU SKU for different markets suggests the company is rethinking its strategy for GPU production. Focusing on other markets and reduced memory bandwidth may indicate that Intel is targeting China's large AI/ML and HPC services market, although the TDP of the new chip is not yet clear. However, trade tensions between the US and China may affect Intel's plans to sell its new GPU SKU in China.
FROM THE MEDIA: Intel is cancelling its mid-tier Data Center GPU Max 1350 accelerator card and introducing the Data Center GPU Max 1450 SKU later in 2023, which has lower I/O bandwidth for different markets and will be able to use air- and liquid-cooling solutions. The TDP of the new chip is not clear, but Intel is reportedly focusing on other markets and reduced memory bandwidth, which could suggest that Intel may be gearing up to sell the GPUs in China. Trade restrictions announced last fall barred the export of processors capable of 600GBps of memory bandwidth to China.
READ THE STORY: The Register
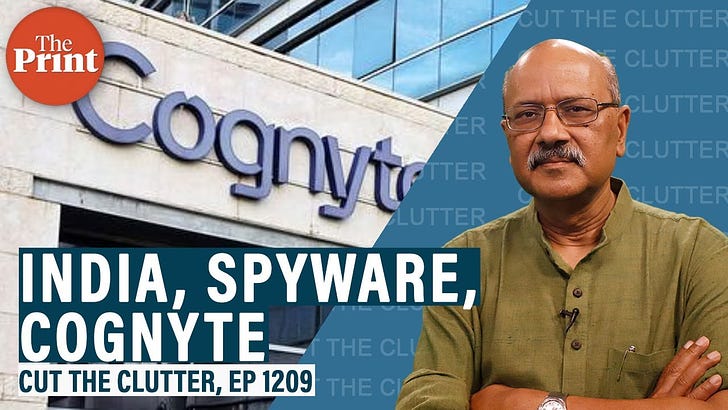
India Expands Search for Spyware Beyond Pegasus; Cognyte, a Company with Ties to Israeli Unit 8200, Emerges (Video)
FROM THE MEDIA: The Indian Government and its surveillance agencies are reportedly looking for new spyware following the Pegasus controversy from a few years ago. Reports suggest that Cognyte, a company with origins in the Israeli military's Unit 8200, may be the frontrunner for India's new spyware needs. This has raised concerns about whether the software will be used for legitimate purposes or misused against the opposition, critics, and journalists. The Congress party has held a press conference, accusing the government of purchasing Cognyte's software for around $120 million. Cognyte has previously sold its software to countries like Myanmar, Kenya, Mexico, and Indonesia, where it has been used to spy on journalists and politicians.
North Korea and the triads: gangsters, ghost ships and spies (Video)
FROM THE MEDIA: This investigative report by the Financial Times and the Royal United Services Institute reveals the connections between North Korean sanctions evasion, triads, and organized crime networks. These criminal networks facilitate the illicit oil trade that keeps North Korea's weapons program alive. The Unica, a tanker ship, is a key player in this story, as it regularly delivers fuel to North Korea despite sanctions and patrols.
These open-source products are reviewed by analysts at InfoDom Securities, providing possible context about current media trends related to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not endorse any third-party claims made in their original material or related links on their sites; the opinions expressed by third parties are theirs alone. For further questions, please contact InfoDom Securities at dominanceinformation@gmail.com.