Monday, March 06, 2023 // (IG): BB // Cyber-Roundup// Coffee for Bob
Ukraine believed that stopping software updates in Russia would put pressure on Moscow. But the war continues and Putin has his gun
Analyst Comments: Preventing a country from getting software updates can have unintended consequences, such as making it harder for the population to access certain technological services and potentially causing economic and social disruptions. It may also not be effective in changing the actions of a country's government or leadership, especially if they are committed to achieving cyber sovereignty and reducing their dependence on foreign software.
FROM THE MEDIA: The war in Ukraine has been ongoing for over a year, resulting in changes for both countries. Despite pressure from American and European companies, the war continues, and Russia's focus on cyber sovereignty has allowed it to be independent of US and European tech companies. Open source code continues to circulate globally without hindrance, making it difficult for tech companies to limit Russia's access to certain software tools. Russia's good relations with China also make it difficult for big tech to leave that market, and it has taken steps to reduce its dependence on software developed in other countries. In March 2022, Russia prepared to disconnect from the internet to protect itself from cyberattacks and avoid foreign dependencies, with unpredictable consequences.
READ THE STORY: GearRice
Russia is successfully evading Western technology sanctions
Analyst Comments: Russia is bypassing Western sanctions on technology and semiconductor imports by receiving goods via China. Shipments from China to Russia have surged and are now approaching a record $200bn turnover, with Beijing playing an increasingly important role in supplying Moscow with the necessary technology and goods.
FROM THE MEDIA: Russia is managing to bypass Western sanctions on technology and semiconductor imports to supply itself with technology to keep its economy working and build sophisticated weapons, according to a report by Bloomberg. A senior European diplomat said Russia is using middlemen and transit via “friendly countries” to sidestep EU and G7 sanctions to procure vital semiconductors and other technologies for its war in Ukraine. Turkey, the United Arab Emirates, and Kazakhstan are among Russia’s most important trade-sanction-busting partners. Despite multiple rounds of sanctions from the EU and G7 since the invasion of Ukraine a year ago, Russian imports have largely returned to their pre-war 2020 levels. Some officials believe that the impact of the sanctions is falling short of what was hoped for.
READ THE STORY: BNE
Germany and Ukraine hit two high-value ransomware targets
Analyst Comments: Germany is the largest economy in Europe and home to many large corporations and critical infrastructure, which can be targeted for ransomware attacks.
FROM THE MEDIA: On February 28th, 2023, German and Ukrainian police, with assistance from Europol, the Dutch police, and the United States Federal Bureau of Investigations, targeted suspected core members of the criminal group responsible for the DoppelPaymer ransomware attacks. The ransomware was distributed through various channels, including phishing and spam emails with attached documents containing malicious code. The criminal group relied on a double extortion scheme, using a leak website launched by the criminal actors in early 2020. The German authorities are aware of 37 victims of this ransomware group, all of the companies. Europol deployed experts to Germany to cross-check operational information against its databases and provide further operational analysis, crypto tracing, and forensic support. The investigation is expected to trigger further investigative activities.
READ THE STORY: Europol
Kuwait ministry hit by a ransomware attack
Analyst Comments: The United States has been a close ally of Kuwait since its independence from the United Kingdom in 1961, and this relationship has been strengthened by Kuwait's role as a key oil producer and a strategic partner in the Gulf region. The two countries have signed a number of agreements covering areas such as defense, trade, investment, and cultural exchange. The US has maintained a military presence in Kuwait, with around 13,000 US troops stationed there as of 2023.
FROM THE MEDIA: The reason why Kuwait's Ministry of Commerce and Industry was targeted by the Lockbit ransomware is not clear from the information provided in the article. However, it is common for cybercriminals to target government and public entities as they may have access to sensitive information and valuable resources. Additionally, the Ministry of Commerce and Industry, like other entities, faces numerous hacking and disruption attempts every day, highlighting the importance of implementing stricter measures to strengthen its network and electronic systems. The ministry's prompt response in disconnecting the affected computers and taking several security measures likely prevented any serious damage to its operations and data.
READ THE STORY: ITP
Military Robots: Revolutionizing Warfare through Automation and Artificial Intelligence
Analyst Comments: The military is already using AI to some extent, such as for autonomous drones and unmanned ground vehicles. However, the level of AI use in the military is still somewhat limited, and there are ongoing debates and concerns about the ethical implications of using autonomous weapons. Some experts predict that AI will play an increasingly significant role in modern warfare in the future, but the pace and extent of that development will depend on a range of factors including technological advancements, regulatory frameworks, and public opinion.
FROM THE MEDIA: The use of military robots or unmanned ground vehicles (UGVs) is increasing in modern warfare as they can perform tasks such as reconnaissance, bomb disposal, and combat support. The market for military robots is projected to grow due to increasing demand for advanced military technologies, asymmetric warfare, and the need for improved situational awareness and response times. However, the high cost of development and deployment, ethical concerns around autonomous weapons, and the need for effective human-robot interaction are challenges that the market faces. The report provides insights into the current state of the military robot market, key players, growth opportunities, challenges, and future growth prospects. It also explores the latest technological advancements, such as the integration of artificial intelligence and machine learning. Despite ethical concerns, the development and use of military robots are expected to continue to grow as countries invest in military technology to gain a strategic advantage.
READ THE STORY: Digital Journal
A Privacy Hero's Final Wish: An Institute to Redirect AI's Future
Analyst Comments: Despite Eckersley's untimely death, AOI continues to work towards promoting AI objectives that align with human flourishing and address global challenges such as climate change. Eckersley's legacy as a privacy and encryption advocate has had a significant impact on the tech industry. Overall, the article highlights the importance of guiding the development of AI towards objectives that serve humanity's best interests.
FROM THE MEDIA: Peter Eckersley, a privacy and technology expert who died in 2022, co-founded the AI Objectives Institute (AOI) to guide AI development toward goals that promote human flourishing. Despite his death, AOI continues with Deger Turan as president and Brittney Gallagher as executive director. Eckersley's contributions to privacy and encryption through projects like Privacy Badger and the SSL Observatory transformed the tech industry. He founded AOI to address the "alignment problem" of AI development potentially amplifying destructive forces. AOI's projects, including Talk to the City and Mindful Mirror, promote AI objectives addressing global challenges like climate change. In a speech, Eckersley's sister urged support for AOI as an "incredible living legacy."
READ THE STORY: Wired
China to Create New Top Regulator for Data Governance
Analyst Comments: The creation of a new national data bureau in China reflects the country's efforts to centralize the management of its vast stores of data, streamline its regulatory structure, and address data security practices by businesses. The proposed agency would become the top Chinese regulator on various data-related issues, ruling on whether multinational companies can export data generated by their operations in China, enforcing data-collection and sharing rules, and investigating issues related to the digital domain. However, some technology executives have expressed concerns that the new regulator could stifle innovation in the already bruised technology sector, which has faced a two-year crackdown on powerful internet companies.
FROM THE MEDIA: China is reportedly planning to establish a new government agency that will oversee and centralize the management of the country's vast data stores. The move comes as Beijing seeks to address data security practices by businesses and streamline its regulatory structure. The proposed national data bureau is expected to become the top regulator for various data-related issues, shifting from the current structure in which multiple ministries share oversight. It is expected to rule on whether multinational companies can export data generated by their operations in China and set and enforce data-collection and sharing rules for businesses. The agency would also investigate issues in the digital domain, such as identifying data-security vulnerabilities prone to cyberattacks and the use of algorithms for data manipulation or inducing internet addiction among minors. The proposal aims to bring a more streamlined approach to data governance, simplifying the current structure in which data regulation in China is handled by several agencies. However, technology executives have expressed concern that a new regulator could stifle innovation in the technology sector, following a two-year crackdown on powerful internet companies.
READ THE STORY: WSJ
How Is The US Preparing To Build A “Safe And Secure Digital Ecosystem For All Americans”?
Analyst Comments: As technology continues to advance and cyber threats become more sophisticated and prevalent, it is critical for governments to take proactive steps to protect their citizens, businesses, and national security interests. The strategy emphasizes the importance of collaboration between the public and private sectors, establishing mandatory cybersecurity regulations, investing in research and development, and preparing for emerging technologies such as quantum computing.
FROM THE MEDIA: The US government has announced a new National Cybersecurity Strategy, which seeks to support the creation of laws that enforce clear and robust limits on personal data use. The strategy also aims to establish mandatory cybersecurity regulations that prioritize the adoption of secure-by-design principles and minimum cybersecurity standards to support national security. The government highlights the importance of public-private collaborations and the harmonization of laws to integrate federal cybersecurity centers. To improve collective cybersecurity resilience, the government will invest in critical infrastructure and explore federal cyber insurance in the event of a catastrophic cyber incident. Additionally, research and development investments will prioritize clean energy technologies, biotechnologies and biomanufacturing, and computing-related technologies, such as microelectronics, quantum computing, and artificial intelligence. The US government will proactively identify potential cyber vulnerabilities and risk-mitigating strategies, particularly in relation to quantum computing, green energy models, and the integration of cybersecurity into interconnected hardware and software solutions.
READ THE STORY: Medianama
'Trojan horse': Why US officials have raised alarm over giant Chinese cargo cranes
Analyst Comments: Chinese-made cranes, specifically those made by ZPMC and operating at ports across America, are being used to register sensitive information. These "ship-to-shore" cranes contain sophisticated sensors that can register and track the provenance and destination of containers, enabling China to capture information about the material being shipped in or out of the US to support its military operations around the world. US officials have also expressed concerns that these cranes could provide remote access for someone looking to disrupt the flow of goods. While there have been no direct instances of Chinese cranes being used for espionage operations, this possibility is enough to raise alarm. Furthermore, ports in Virginia, South Carolina, and Maryland, which are at times used by nearby US military bases, have acquired new cranes from ZPMC in the last two years, prompting concern within the US national security community and FBI.
FROM THE MEDIA: The US government is concerned that Chinese-made cranes operating at ports across America may be used to register sensitive information. These ship-to-shore cranes are well-built and inexpensive, and officials suspect that they contain sophisticated sensors that can track the provenance and destination of containers, enabling China to capture information about materiel being shipped in or out of the US to support its military operations around the world. While US officials have not found any direct instances of Chinese cranes being used for espionage operations, the possibility is enough to raise alarm. The recent international uproar over a Chinese surveillance balloon shot down by the US has brought China's military surveillance capabilities back into the spotlight, and US officials have been pointing to a range of Chinese equipment that could facilitate either surveillance or disruptions. The Chinese foreign ministry dismissed the concerns as "overly paranoid" and accused the US of obstructing trade and economic cooperation with China.
READ THE STORY: The Time of India
The Russians are Playing A Thin Rope Game
Analyst Comments: Moscow's prioritization of its military operation in Ukraine and its efforts to prevent NATO from expanding eastward have led it to turn to Iran for allies, which is putting its relations with Israel and other Middle Eastern countries in jeopardy. Iran's potential development of nuclear weapons is also raising concerns, particularly for Israel, and may prompt military action. The situation is complex and delicate, and the actions of these countries could have significant implications for regional and global security.
FROM THE MEDIA: Recent developments in Ukraine have complicated Russia's relationships with Israel and Iran. Iran's enrichment of uranium to 84% has caused alarm in Israel, prompting high-level military meetings and the consideration of providing Ukraine with an air defense missile system. Israel has also voted in favor of a UN resolution demanding Russia withdraw its forces from Ukraine, ending its previous neutrality. Russia, meanwhile, is focused on the success of its military operation in Ukraine and turning to Iran for allies, while also maintaining good relations with Israel. However, as other Middle Eastern countries seek to counter Iran, it may be difficult for Moscow to reconcile its relations with both Israel and Iran. It is also unlikely that a nuclear deal with Iran will ease tensions in the region, and Putin may not be able to remain neutral if Israel were to launch an attack on Iran with support from Arab countries.
READ THE STORY: ModernDiplomacy
Where are the women in cyber security? On the dark side, study suggests
FROM THE MEDIA: At least 30% of cyber criminal forum users are women, according to a study by Trend Micro, which analyzed five English-language cybercrime forums and five Russian-language sites. The study relied on anonymized data and language analysis tools, so the numbers cannot be taken as exact, but they suggest that women are more visible in cybercrime than in white hat security, where women make up just 12% of visitors to programming forums, according to Semrush. “Developers are valued for their skills and experience, and not necessarily for their gender when it comes to conducting business in the underground,” the report said.
READ THE STORY: The Register
China’s AI-powered influence operations at India’s doorstep
FROM THE MEDIA: A recent report by Graphika has revealed a pro-Chinese political spam operation using AI-generated videos of fictitious people to create deceptive political content. The spam, called "spamouflage," promotes a narrative favorable to China and has been operating since 2019 on popular social media platforms like Facebook, Twitter, and YouTube. The usage of AI-generated content started from deepfake apps, which use deep learning algorithms for face-swapping. While deepfakes can sow doubts, disrupt trust, further existing biases, and manipulate opinions and choices, AI-powered deepfake tools can wreak havoc by accelerating the process. As AI-related technologies advance, the dangerous possibilities of the usage of deceptive content for political and geopolitical gains will only increase.
READ THE STORY: HT
Huawei fights for a role as Malaysia reviews 5G tender
FROM THE MEDIA: Huawei is lobbying for a role in Malaysia's 5G plans, which have become a test of the country's relations with China and the West, according to three people briefed on the situation. The move comes after the country's new government announced a review of its predecessor's plans, which had seen Ericsson awarded the tender to build a state-owned network. Since winning the election in November, Prime Minister Anwar Ibrahim has ordered a review of the public tender process, citing transparency concerns. It may also select a second vendor besides Ericsson to assist with the current rollout, the people said.
READ THE STORY: FT
Municipal CISOs grapple with challenges as cyber threats soar
FROM THE MEDIA: The recent ransomware attack on the City of Oakland highlights the challenges that municipal Chief Information Security Officers (CISOs) face in protecting a broad range of diverse services. One of the biggest challenges is the sheer range of services that local governments need to factor into their cybersecurity plans and policies, from publicly owned hospitals to trash collection to subway systems. Municipal CISOs must navigate a welter of federal, state, and local regulations and laws, which vary widely and may overlap. The regulatory environment for municipal governments is further complicated by differing and potentially overlapping regulations, politics, and workforce shortages while dealing with budgetary constraints. Resource-constrained municipalities find it hard to compete for cybersecurity talent with the private sector, which also faces a shortage of qualified professionals. Furthermore, municipal governments have become prime targets for ransomware actors and geopolitical threat groups. Municipal CISOs are required to deftly handle the politics of the governments they serve and the individual service providers themselves.
READ THE STORY: CSO
MQsTTang – Chinese Hackers Using Custom Malware To Evade AV Detection
FROM THE MEDIA: ESET researchers have analyzed the newly discovered MQsTTang custom backdoor and attributed it to the Mustang Panda APT group. The group, also known as TA416 and Bronze President, is known for its worldwide data theft attacks, targeting government and political organizations in Europe and Asia. The new malware uses spear-phishing emails for distribution and is compressed in RAR archives. MQsTTang provides the attacker with remote command execution capabilities and allows them to receive the output of the commands. It also has the ability to withstand C2 takedowns and evade detection by defenders by utilizing the MQTT protocol for communication between the command and control server. The malware has a mechanism to detect the presence of debugging or monitoring tools on the host system and adapt its behavior to avoid detection. It is uncertain whether the malware will be incorporated into the group's long-term arsenal or used solely for a specific operation.
READ THE STORY: GBhackers
US public transport service struck by a ransomware attack
FROM THE MEDIA: A public transport service in Washington state, Pierce Transit, was hit by a ransomware attack on Valentine's Day, resulting in temporary disruptions to some of its systems. Although Pierce Transit did not identify the hacker, the LockBit ransomware group claimed responsibility and demanded a ransom of US$1,999,999 for the data's destruction or return by 28 February. The group exfiltrated information that included "postal correspondence, NDA agreements, personal data of customers, contracts, and much more," according to LockBit. However, Pierce Transit declined to pay, and LockBit has now published the information. LockBit has been identified as a Russian-speaking group that has been operating since at least 2019 and has become a prolific threat actor in the last year.
READ THE STORY: Cyber Security Connect
The Sandbox discloses security breach
FROM THE MEDIA: A third party gained unauthorized access to the computer of an employee at blockchain metaverse company, The Sandbox, and used the data to launch phishing attacks. The threat actor accessed several email addresses and sent phishing emails impersonating the company, which contained a hyperlink to malware that could remotely install malware on a user’s computer and access their personal information. The Sandbox stated that the third-party access was limited to a single employee’s computer and that they had reached out to all email recipients with instructions on what to do next. The company blocked the employee’s accounts, reformatted the laptop, and reset all related passwords, including implementing two-factor authentication. The Sandbox is working with its team to enhance its security policies and practices.
READ THE STORY: Cybernews
Class Action against Intelsat insiders
FROM THE MEDIA: Lawyers for the Class Action against Intelsat shareholders and the company chairman have submitted a detailed claim for the Northern District of California Court stating that “any reasonable person – and juror – would believe that there was insider trading.” The action claims that the defendants in the case sold shares worth $246m, avoiding $185m in losses, but “innocent investors were left [with nothing].” The action argues that each of the named defendants “owed a fiduciary duty to Intelsat shareholders” and that investors expect that those who have special access to information should be barred from using it to gain an advantage. The case is due to be heard on April 28.
READ THE STORY: Advanced Television
North Korea boasts about satellite launch capabilities (DPRK)
FROM THE MEDIA: Orignal source is state-sponsored media - North Korea announced on Monday that it has developed a high-thrust engine that provides a "sure guarantee" of launching various satellites into relevant orbits, including the possibility of a reconnaissance satellite by April. The announcement by the vice director of Pyongyang’s National Aerospace Development Administration, Pak Kyong-su, comes as the country marks the 14th anniversary of its accession to the 1967 Outer Space Treaty. While North Korea claims that it is pursuing peaceful space technology, it is barred from using ballistic missile technology for any launches under United Nations Security Council Resolution 1874. The timing of the announcement, coinciding with the crisis management training by South Korea and the United States, has raised concerns about the regime's intentions.
READ THE STORY: Kora JoongAng Daily
Astro Bob: Satellite streaks spoil Hubble photos
FROM THE MEDIA: The growing number of satellites in orbit, particularly SpaceX's Starlink constellation, is causing problems for orbiting and ground-based observatories. The sheer number of satellites means they are photobombing images and contaminating scientific data. In a recent study, scientists found that satellite trails now cross 2.7% of Hubble images, and by 2021, the chances of finding a streak in a Hubble image had risen to 6%. While SpaceX has tried to adjust the tilt of the Starlinks to make them appear fainter, their increasing numbers mean they have become overwhelming. Satellite "constellations" like Starlink and OneWeb continue to grow, with SpaceX hoping to have 42,000 Starlinks in orbit and China aiming to launch nearly 13,000 satellites. This could result in additional space debris and collisions with active satellites and space telescopes.
READ THE STORY: Duluth News Tribune
Experts Discover Flaw in U.S. Govt's Chosen Quantum-Resistant Encryption Algorithm
FROM THE MEDIA: Researchers from KTH Royal Institute of Technology have discovered a vulnerability in one of the encryption algorithms chosen by the U.S. government as quantum-resistant. The exploit relates to "side-channel attacks on up to the fifth-order masked implementations of CRYSTALS-Kyber in ARM Cortex-M4 CPU." CRYSTALS-Kyber is one of four post-quantum algorithms selected by the U.S. National Institute of Standards and Technology. The vulnerability relates to extracting secrets from a cryptosystem through measurement and analysis of physical parameters, and the researchers developed a new message recovery method to increase the success rate of message recovery. NIST said the approach does not break the algorithm itself and that the findings don't affect the standardization process of CRYSTALS-Kyber.
READ THE STORY: THN
Flutterwave denies being hacked, assures customers of security measures
FROM THE MEDIA: Flutterwave, an African fintech unicorn, has denied reports that it was hacked and that hackers stole over $4 million from its accounts in Nigeria. The company stated that during a routine check of its transaction monitoring system, it identified an unusual trend of transactions on some users' profiles, but no user lost any funds, and its security measures were able to address the issue before any harm could be done to its users. Flutterwave's legal counsel reported the case to the Deputy Commissioner of Police, State Criminal Intelligence Department, Panti, Yaba, Lagos, on February 19, 2023, and a suit was filed in the Magistrate Court of Lagos to investigate accounts holding the stolen funds across various financial institutions in Nigeria.
READ THE STORY: Business Insider Africa
Items of interest
Royal Ransomware Made Upto $11 Million USD Using Custom-Made Encryption Malware
FROM THE MEDIA: The FBI and CISA have issued a Cybersecurity Advisory (CSA) warning of the Royal ransomware's activities, which has been used to breach US-based and foreign organizations' security since September 2022. The ransomware disables targeted organizations' antivirus software and exfiltrates data before the final deployment of the ransomware and encryption of affected computers. The Royal ransomware has demanded ransom payments ranging from $1 million to $11 million in Bitcoin from their victims. The attackers have targeted a broad range of critical infrastructure sectors, including manufacturing, communications, healthcare, public healthcare, and education. The attackers use double extortion tactics and repurpose valid Windows software to strengthen their foothold in the targeted network, which evades detection by security protocols. The Royal ransomware has advanced its capabilities and can now target both Windows and Linux environments.
READ THE STORY: CyberSecurityNews
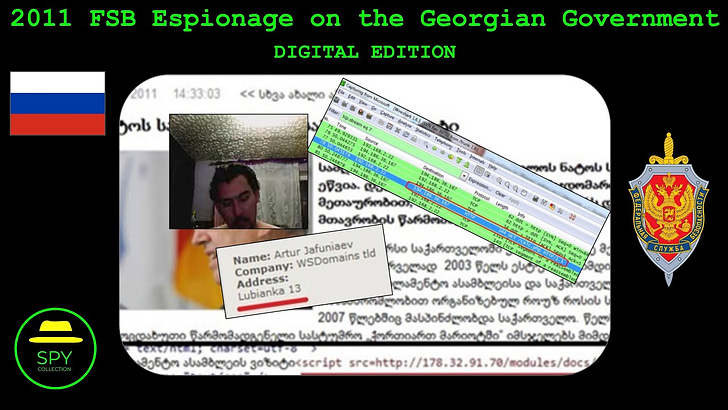
FSB Cyber Espionage Operation Targeting the Georgian Government (2011) (Video)
FROM THE MEDIA: The video discusses a cyber espionage operation by the FSB targeting the Georgian government in 2011, which was revealed in a detailed cyber threat intelligence report by Georgia's national CERT. The FSB began by hacking popular news websites in Georgia and modifying specific content to covertly inject a backdoor into visitors' computers.
Chinese MSS 2014 Cyber Espionage on Japanese Monju Nuclear Power Plant (Video)
FROM THE MEDIA: The video discusses a cyber espionage operation that occurred in early 2014, targeting Japan's Monju Nuclear Power Plant. The operation was attributed to China's Ministry of State Security (MSS), and the video details the methodology used by the MSS operatives to gain access to the plant's systems. The video explains how the cyber operators compromised GOM Player, a popular media player, and used it to host a modified update bundle that included a backdoor implant.
These open-source products are reviewed by analysts at InfoDom Securities, providing possible context about current media trends related to the realm of cyber security. The stories selected to cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not endorse any third-party claims made in their original material or related links on their sites; the opinions expressed by third parties are theirs alone. For further questions, please contact InfoDom Securities at dominanceinformation@gmail.com.