Tuesday, January 17, 2023 // (IG): BB // BSidesCharm// Coffee for Bob
Space industry deploying more satellites that deliver sharper images
FROM THE MEDIA: The war in Ukraine has made the world aware of the geopolitical, social and military impacts of satellite imagery. At the same time, the space industry is introducing new capabilities for “very high resolution imagery” that will make commercial spy satellites even more powerful, says a Jan. 16 report by the research and consulting firm Quilty Analytics. “We are witnessing a transformation in the domain of very high resolution imagery,” the report says. “Established operators are launching next-generation fleets – improving their imaging capacity, pointing accuracy and revisit rates.” Meanwhile, new players that started out with low-resolution satellites “are scaling up to increasingly sharper resolutions once thought unobtainable by small satellites.” These advances will benefit “demanding customers” that also have large budgets such as U.S. defense and intelligence agencies, says Quilty Analytics.
READ THE STORY: SN
Raccoon and Vidar Stealers Spreading via Massive Network of Fake Cracked Software
FROM THE MEDIA: A "large and resilient infrastructure" comprising over 250 domains is being used to distribute information-stealing malware such as Raccoon and Vidar since early 2020. The infection chain "uses about a hundred of fake cracked software catalogue websites that redirect to several links before downloading the payload hosted on file share platforms, such as GitHub," cybersecurity firm SEKOIA said in an analysis published earlier this month. The French cybersecurity company assessed the domains to be operated by a threat actor running a traffic direction system (TDS), which allows other cybercriminals to rent the service to distribute their malware. The attacks target users searching for cracked versions of software and games on search engines like Google, surfacing fraudulent websites on top by leveraging a technique called search engine optimization (SEO) poisoning to lure victims into downloading and executing the malicious payloads.
READ THE STORY: THN
Hacktivists Leak 1.7TB of Cellebrite, 103GB of MSAB Data
FROM THE MEDIA: According to the Enlace Hacktivista group, the Cellebrite and MSAB data (both are smartphone forensic firms) was provided to them by an “anonymous whistleblower.” The Israeli mobile forensics firm, Cellebrite, has apparently suffered yet another data breach in which hackers managed to steal 1.7 TB of data. The hackers are also claiming to have stolen 103 GB of data from MSAB, a Sweden-based forensics firm. In both cases, the trove of information is available for download on DDoSecrets and the official website Enlace Hacktivista. It is worth noting that, according to Enlace Hacktivista, the Cellebrite and MSAB data was provided to them by an “anonymous whistleblower.” The Petah Tikva, Israel-based Cellebrite is frequently criticized for aiding governments with its tools and spyware to monitor the activities of human rights activists, officials, dissidents, and journalists.
READ THE STORY: HackREAD
Smart deterrence: China’s AI-warfare plan for Taiwan
FROM THE MEDIA: Chinese military experts are reportedly exploring “smart deterrence” concepts, marking a significant evolution in China’s use of artificial intelligence (AI) and other emerging technologies from tactical and operational military levels to influence strategic-level decision-making. This week, South China Morning Post reported that China could become a leader in so-called “intelligent warfare”, drawing on advanced technologies such as AI, cloud computing, big data analytics and cyber offense and defense. Ni Yongjie, deputy director of the Shanghai Institute of Taiwan Studies, opined in the peer-reviewed journal Cross-Strait Taiwan Studies that China should use AI and other enabling technologies to deter the US and pro-independence factions in Taiwan, in addition to blockade exercises around the self-governing island, the South China Morning Post said. Ni also wrote that smart deterrence is already being studied in Chinese military circles.
READ THE STORY: Asia Times
Hackers use fear of mobilization to target Russians with phishing attacks
FROM THE MEDIA: Hackers took advantage of Russian concerns about mobilization to steal credentials through malicious links, according to new research. In a phishing campaign described by the Russian cybersecurity channel In2security on the messaging app Telegram and confirmed by researchers from antivirus provider Kaspersky Lab, attackers used a phishing website and Telegram bot to collect personal data from Russian users. The hackers sent out messages on Telegram urging Russians to follow a link to a site that purportedly contained lists of people who could be drafted into the army and sent to fight in Ukraine this February. The link was in fact malicious and had to be constantly updated “so that it would not be blocked by the Russian media regulator Roskomnadzor,” according to a post on the In2Security channel sent on January 11.
READ THE STORY: The Record
Industrial espionage: How China sneaks out America's technology secrets
FROM THE MEDIA: It was an innocuous-looking photograph that turned out to be the downfall of Zheng Xiaoqing, a former employee with energy conglomerate General Electric Power. According to a Department of Justice (DOJ) indictment, the US citizen hid confidential files stolen from his employers in the binary code of a digital photograph of a sunset, which Mr Zheng then mailed to himself. It was a technique called steganography, a means of hiding a data file within the code of another data file. Mr Zheng utilised it on multiple occasions to take sensitive files from GE. GE is a multinational conglomerate known for its work in the healthcare, energy and aerospace sectors, making everything from refrigerators to aircraft engines.
READ THE STORY: BBC
Gamaredon Leverages Microsoft Office Docs to Target Ukraine
FROM THE MEDIA: The Gamaredon group, a misspelled anagram of "armageddon", is a Russian state-sponsored cyber-espionage group that has perpetrated cyberattacks against military, government, and non-profit organizations in Ukraine since at least 2013. This threat actor group leverages legitimate Microsoft® Office documents to carry out remote template injection. The technique works even with Microsoft® Word security features enabled. This means attackers can bypass Microsoft Word macro protections to compromise target systems with malware, gain access to information, then spread the infection to other users. In this blog, we’ll examine how Gamaredon operates this campaign, and share Indicators of Compromise (IOCs), mitigation tips, and YARA rules to defend against this and similar attacks.
READ THE STORY: Inferse
Pirated CIA spyware being used by threat actors, says analyst
FROM THE MEDIA: The cyber watchdog claims it detected a variant of the CIA cyberattack kit Hive – no relation to the ransomware group of the same name – on October 21 after it caught it communicating with an internet protocol (IP) address using forged Kaspersky certificates. “After further lookup, we confirmed that this sample was adapted from the leaked Hive project server source code from the CIA,” said Netlabs. “This is the first time we caught a variant of the CIA Hive attack kit in the wild.” Netlabs describes the variant, which it nicknamed xdr33 after its digital certification code, as a backdoor designed to collect sensitive data “and provide a foothold for subsequent intrusions.” xdr33 uses SSL, an internet security tool that allows data encryption, to relay sensitive information back to the threat actor in control of it.
READ THE STORY: CyberNews
Google's DeepMind says it'll launch a more grown-up ChatGPT rival soon
FROM THE MEDIA: Google subsidiary DeepMind says it could launch a ChatGPT rival soon – and its chatbot promises to be a safer kind of AI assistant. DeepMind has been a pioneer in AI research for the last decade and was acquired by Google nine years ago. However, with ChatGPT stealing the recent headlines, DeepMind CEO Demis Hassabis told Time(opens in new tab) that it's considering releasing its own chatbot, called Sparrow, for a "private beta" sometime in 2023. Sparrow was introduced to the world last year as a proof-of-concept in a research paper(opens in new tab) that described it as a "dialogue agent that’s useful and reduces the risk of unsafe and inappropriate answers".
READ THE STORY: TechRadar
Website of Canadian Liquor Distributor LCBO Infected With Web Skimmer
FROM THE MEDIA: Canadian liquor distributor Liquor Control Board of Ontario (LCBO) has announced that a web skimmer injected into its online store was used to steal users’ personal data. One of the largest liquor sellers in Canada, LCBO retails and distributes alcoholic beverages throughout the Ontario province, operating over 670 stores and employing more than 8,000 people. Last week, the company abruptly took offline its online store and mobile application, only to later explain that it fell victim to a cyberattack in which a web skimmer was injected into LCBO.com. “At this time, we can confirm that an unauthorized party embedded malicious code into our website that was designed to obtain customer information during the checkout process,” the retailer said.
READ THE STORY: SecurityWeek
Spyware found stealing Iranian user data via infected VPN installer
FROM THE MEDIA: Spyware has been discovered stealing Iranian users data via an infected VPN installer, antivirus provider Bitdefender has revealed. The company's joint-research with cybersecurity firm Blackpoint found components of Iranian-made EyeSpy malware to be injected "through Trojanized installers of VPN software (also developed in Iran)." The majority of targets were within the country's borders, only a few victims were found to be based in Germany and the US. This is particularly concerning in a country like Iran, where using one the best VPN services has increasingly become a necessity. Whether this is for bypassing its strict online censorship, or preserving anonymity to avoid dangerous government surveillance. Most likely, a mix of both.
READ THE STORY: TechRadar
Rhadamanthys malware hidden in Google Ads
FROM THE MEDIA: Info-stealing malware Rhadamanthys is hijacking Google ads to lure victims into downloading malicious software. The malware lifts data like passwords and email addresses as well as targeting cryptocurrency wallet credentials. Marketed to criminals as malware-as-a-service (MaaS), the popularity of Rhadamanthys is rising as infostealers become a popular way to attack targets. Rhadamanthys is named after the demigod child of Zeus and Europa in Greek mythology, and has been occupying Google ads for free video recording and streaming service OBS (Open Broadcasting Service), a platform widely used by streamers, according to threat researcher Germán Fernández. Rhadamanthys has been growing in popularity since November last year. It has now advanced to a point where, if a user searches for OBS they will be met with five dangerous ads at the top of their Google search before legitimate results appear below, the cybercriminals having apparently purchased advertising spots on Google.
READ THE STORY: TechMonitor
Ransomware Attack Affects 1,000 Vessels Worldwide
FROM THE MEDIA: A ransomware attack shut down servers hosting software used to manage the crewing and maintenance schedules of about 1,000 vessels across the globe. Norwegian classification society DNV, maker of ShipManager software, says it took the servers offline after detecting a cyber incident on Jan. 7. Onboard software functionally continues to operate, says DNV, which also sets standards for the construction and operation of ships. "There are no indications that any other software or data by DNV is affected. The server outage does not impact any other DNV services," the company says. It has contacted Norwegian police. DNV says more than 7,000 vessels owned by 300 customers use ShipManager.
READ THE STORY: Gov Info Security
Researchers Uncover 3 PyPI Packages Spreading Malware to Developer Systems
FROM THE MEDIA: A threat actor by the name Lolip0p has uploaded three rogue packages to the Python Package Index (PyPI) repository that are designed to drop malware on compromised developer systems. The packages – named colorslib (versions 4.6.11 and 4.6.12), httpslib (versions 4.6.9 and 4.6.11), and libhttps (version 4.6.12) – by the author between January 7, 2023, and January 12, 2023. They have since been yanked from PyPI but not before they were cumulatively downloaded over 550 times. The modules come with identical setup scripts that are designed to invoke PowerShell and run a malicious binary ("Oxzy.exe") hosted on Dropbox, Fortinet disclosed in a report published last week.
READ THE STORY: THN
Datadog rotates RPM signing key exposed in CircleCI hack
FROM THE MEDIA: Cloud security firm Datadog says that one of its RPM GPG signing keys and its passphrase have been exposed during a recent CircleCI security breach. However, the company added that it has yet to find evidence that this key was leaked or misused. "As of January 16th, 2023, Datadog has no indication that the key was actually leaked or misused, but we are still taking the following actions out of an abundance of caution," Datadog said. In response to CircleCI's disclosure that the threat actor stole customers' environment variables, tokens, and keys from its databases, Datadog has released a new version of its Agent 5 RPM for CentOS/RHEL, signed with a new key. The company has also released a new Linux install script that removes the affected key from the Datadog repo file and the RPM database. Datadog added that even if the attacker managed to steal the signing key and would craft a malicious RPM package, they wouldn't be able to use it to target the company's customers because they would also need access to the official package repositories.
READ THE STORY: BleepingComputer
Vice Society ransomware leaks University of Duisburg-Essen’s data
FROM THE MEDIA: The Vice Society ransomware gang has claimed responsibility for a November 2022 cyberattack on the University of Duisburg-Essen (UDE) that forced the university to reconstruct its IT infrastructure, a process that's still ongoing. The threat actors have also leaked files they claim to have stolen from the university during the network breach, exposing potentially sensitive details about the university's operations, students, and personnel. UDE has since confirmed that they are aware the threat actors published the stolen data and said that they will not be paying a ransom. "After the cyber attack on the University of Duisburg-Essen (UDE) at the end of November, the criminal group responsible for it has now published data on the Darknet," UDE said in a statement. "The university had not complied with the attackers’ demands and had not paid a ransom."
READ THE STORY: BleepingComputer
GCC hit hard with ransomware attacks, with Saudi and UAE organizations most affected
FROM THE MEDIA: Organizations in Saudi Arabia and the United Arab Emirates (UAE) fell victim to the highest number of ransomware attacks out of all GCC countries between mid-2021 and mid-2022, according to a report from cybersecurity company Group-IB. A ransomware attack happens when an individual or group uses software to access a company or organizations files to either extort the business or steal its data. “In terms of industries, the energy, telecoms, IT and manufacturing sectors were frequently targeted,” the report said. In the second half of 2021 and first half of 2022, 42 companies in the GCC region fell prey to these attacks – 33 percent of the companies were UAE-based and 29 percent were from Saudi Arabia - Group-IB said in Tuesday’s report. A total 21 percent of the companies who were victim to these ransomware attacks in the report were Kuwaiti, 10 percent from Qatar, while Omani and Bahraini organizations made up less than 10 percent of the organizations targeted.
READ THE STORY: Alarabiya
Chainalysis ‘Crypto Crime Report’ details OFAC sanctions’ impact
FROM THE MEDIA: The global ‘crypto’ market may have crashed hard in 2022 yet the total value of illicit crypto activity hit an all-time high of over $20 billion. Blockchain analytics firm Chainalysis is set to release its latest annual Crypto Crime Report next month, but the company has begun previewing some of its marquee findings for 2022. The headline figure is that the total value of digital currencies received by ‘illicit’ addresses hit a record $20.1 billion last year, and the company cautions that this is likely to be “a lower bound estimate.” For instance, while Chainalysis originally pegged 2021’s total crypto crime value at $14 billion, they’ve since revised that sum to $18 billion, “mostly due to the discovery of new crypto scams.” Chainalysis also cautions that these sums don’t include proceeds from “non-crypto native crime,” such as drug traffickers using crypto as payment in lieu of fiat currency.
READ THE STORY: Coingeek
Crypto exchanges freeze accounts tied to North Korea’s notorious Lazarus Group
FROM THE MEDIA: Two cryptocurrency exchanges have frozen accounts identified as having been used by North Korea’s notorious Lazarus Group. This story starts with a crypto researcher who goes by “ZachXBT” and late last week spotted an entity called “Lazarus Group” moving 41,000 ETH “from the Harmony Bridge hack through Railgun on Jan 13-14 2023 before depositing funds on three exchanges.” The Harmony bridge was a crypto-transfer service that was attacked in June 2022, with around $100m of crypto lost as a result of the attack. Analysts quickly identified Lazarus Group as the sort of entity that could be interested in attacking Harmony. Lazarus Group is identified suspected of being a cybercrime crew run by the government of North Korea and is infamous for the WannaCry ransomware, attacking Sony Pictures and stealing secrets from energy companies.
READ THE STORY: The Register
Malicious ‘Lolip0p’ PyPi packages install info-stealing malware
FROM THE MEDIA: A threat actor has uploaded to the PyPI (Python Package Index) repository three malicious packages that carry code to drop info-stealing malware on developers' systems. The malicious packages, discovered by Fortinet, were all uploaded by the same author named 'Lolip0p' between January 7 and 12, 2023. Their names are 'colorslib,' 'httpslib,' and 'libhttps.' All three have been reported and removed from the PyPI. PyPI is the most widely used repository for Python packages that software developers use to source the building blocks of their projects. Unfortunately, its popularity makes it a attractive for threat actors targeting developers or their projects. Typically, malicious packages are uploaded masquerading as something useful or they mimic renowned projects by modifying their name.
READ THE STORY: BleepingComputer
DPRK Hacking Group Disguised as Portal Website Attempts to Steal Information
FROM THE MEDIA: A North Korean hacker group has attempted to steal user passwords with phishing mails by disguising itself as a domestic portal site, a cybersecurity firm said Monday. ESTsecurity recently published an analytical report on malicious code on its corporate blog. The newly-detected phishing emails used a “Daurn” domain that is similar to Kakao-owned portal website Daum. The emails contained text and hyperlinks asking users to change their passwords. Once the hyperlinks are clicked, users are connected to a phishing site that looks similar to the login page of Kakao. If users input information into the site, it is instantly sent to the server of the hacker group. ESTsecurity noted that the group behind the phishing scam is “kimsuky,” a cyberespionage group operating under the umbrella of the North Korean General Bureau of Reconnaissance.
READ THE STORY: Korea BizWire
Researchers to release PoC exploit for critical Zoho RCE bug, patch now
FROM THE MEDIA: Proof-of-concept exploit code will be released later this week for a critical vulnerability allowing remote code execution (RCE) without authentication in several VMware products. Tracked as CVE-2022-47966, this pre-auth RCE security flaw is due to using an outdated and vulnerable third-party dependency, Apache Santuario. Successful exploitation enables unauthenticated threat actors to execute arbitrary code on ManageEngine servers if the SAML-based single-sign-on (SSO) is or was enabled at least once before the attack. The list of vulnerable software includes almost all ManageEngine products.
READ THE STORY: BleepingComputer
Items of interest
Companies race to work around choke points in world trade
FROM THE MEDIA: It is a year since New York Federal Reserve economists unveiled the Global Supply Chain Pressure Index. The barometer of port backlogs and freight costs, looking back over 25 years, showed that constraints on moving goods around the globe peaked in late 2021, at a level for which they could find no precedent. The gauge started to fall as economies slowed, and as Covid-19 disruptions eased. Then Russia invaded Ukraine. As governments and multinationals scrambled to navigate the fallout, the index eased back, only for progress to be stalled by an upsurge in Covid-19 cases in China as 2022 ended. Michael Farlekas, chief executive of freight-booking software company E2open, likens his clients’ response to the stages of grief: “At first you’re shocked, then at some point you reach acceptance.”
READ THE STORY: FT
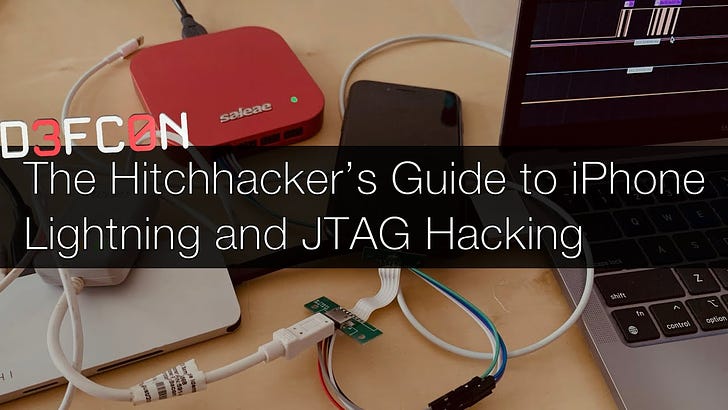
DEFCON 30 - The Hitchhacker’s Guide to iPhone Lightning and JTAG Hacking (Video)
FROM THE MEDIA: At DEF CON 30 I talked about a project I've been working on with a couple of friends for the past few month: The Tamarin Cable! An open-source Kanzi Cable.
IoT Security: Backdooring a smart camera by creating a malicious firmware upgrade (Video)
FROM THE MEDIA: In this video we look at reverse engineering a basic firmware format of a commonly found IoT camera - and then creating a backdoored firmware that calls back to our command & control server and allows us to remotely control it.
These open source products are reviewed from analysts at InfoDom Securities and provide possible context about current media trends in regard to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not specifically endorse any third-party claims made in their original material or related links on their sites, and the opinions expressed by third parties are theirs alone. Contact InfoDom Securities at dominanceinformation@gmail.com