Sunday, January 15, 2023 // (IG): BB // BSidesCharm// Coffee for Bob
Tracing Iran Drone Parts A Game Of ‘Whack A Mole’
FROM THE MEDIA: A Quebec-based company has passed to the government its internal report on how its engines ended up in Iranian-made drones used by Russia in Ukraine. Bombardier Recreational Products (BRP), best known for water-skis and snowmobiles, said it has established through a “thorough investigation” set up three months ago that an engine found in a shot-down Mohajer-6 drone had not been sold directly to either Iran or Russia. A company spokeswoman said this week that Bombardier was “in full compliance with all laws and regulations,” but disclosed nothing substantive in public about its investigation. The drone used the Rotax-912 engine made by BRP-Rotax, a subsidiary based in Gunskirchen, upper Austria. Bombardier ended supplies of the engines to Iran in 2019, although the Mahtabal company in Tehran still markets itself as official representative for Rotax engines.
READ THE STORY: Iran International
Cacti Servers Under Attack as Majority Fail to Patch Critical Vulnerability
FROM THE MEDIA: A majority of internet-exposed Cacti servers have not been patched against a recently patched critical security vulnerability that has come under active exploitation in the wild. That's according to attack surface management platform Censys, which found only 26 out of a total of 6,427 servers to be running a patched version of Cacti (1.2.23 and 1.3.0). The issue in question relates to CVE-2022-46169 (CVSS score: 9.8), a combination of authentication bypass and command injection that enables an unauthenticated user to execute arbitrary code on an affected version of the open-source, web-based monitoring solution. Details about the flaw, which impacts versions 1.2.22 and below, were first revealed by SonarSource. The flaw was reported to the project maintainers on December 2, 2022.
READ THE STORY: THN
How Taliban's takeover of US biometric devices threatens data privacy
FROM THE MEDIA: In the wake of the Taliban’s takeover of Kabul and the ouster of the Afghan national government in August 2021, alarming reports indicated that the insurgents had potentially accessed biometric data collected by the U.S. to track Afghans, including people who worked for U.S. and coalition forces. Afghans who once supported the U.S. have been attempting to hide or destroy physical and digital evidence of their identities. Many Afghans fear that the identity documents and databases storing personally identifiable data could be transformed into death warrants in the hands of the Taliban, and a March 30, 2022, report from Human Rights Watch indicated the Taliban have been collecting biometric data to potentially match against captured U.S. and Afghan government databases. U.S. military devices and the data they contain have since turned up on the open market.
READ THE STORY: Interesting Engineering
Drone Warfare In Ukraine Is Prompting Other Armies To Adapt To Its Use
FROM THE MEDIA: The unprecedented role played by drones in Ukraine, where they have become one of the decisive elements in the war, according to experts, shows the need to adapt modern armies to them, whether in terms of their use or to protect themselves from them. Samuel Bendett of the American “CNA” Center for Research told AFP that there are “other conflicts in which drones have been used extensively,” as happened in Syria against the “ISIS” organization, or in Libya. But “the number and scope of their use in Ukraine exceeds any other conflict.” This specialist in unmanned weapons referred to the “unprecedented use of commercial drones” for surveillance and reconnaissance operations as well as for combat operations in Ukraine. And he considered that the war showed that small marches are “essential for all units at all levels,” explaining, “because they can be sacrificed and their life cycle is short, and the forces must be equipped with very large quantities” of them.
READ THE STORY: Globe World News Echo
Ukrainian hackers hacked the Russian Mail.ru service and made the database publicly available
FROM THE MEDIA: The largest Russian hosting and registrar of domain names, Reg.ru, also suffered cyberattacks. On the morning of January 13, Ukrainian hackers from NLB and DumpForums hacked the Russian Mail.ru service and Reg.ru hosting. The founder of the Hackyourmom group, Mykyta Knysh, announced this on Facebook. According to him, after successful cyberattacks, all the data of employees of Mail.ru and Reg.ru ended up in free access. Mykyta Knysh is from Kharkiv, a former employee of the Security Service of Ukraine. Before the war, he headed the Kharkiv cyber security company HackControl.
READ THE STORY: Odessa Journal
Israel's Cognyte won tender to sell intercept spyware to Myanmar before coup
FROM THE MEDIA: Israel's Cognyte Software Ltd won a tender to sell intercept spyware to a Myanmar state-backed telecommunications firm a month before the Asian nation's February 2021 military coup, according to documents reviewed by Reuters. The deal was made even though Israel has claimed it stopped defense technology transfers to Myanmar following a 2017 ruling by Israel's Supreme Court, according to a legal complaint recently filed with Israel's attorney general and disclosed on Sunday. While the ruling was subjected to a rare gag order at the request of the state and media cannot cite the verdict, Israel's government has publicly stated on numerous occasions that defense exports to Myanmar are banned. The complaint, led by high-profile Israeli human rights lawyer Eitay Mack who spearheaded the campaign for the Supreme Court ruling, calls for a criminal investigation into the deal. It accuses Cognyte and unnamed defense and foreign ministry officials who supervise such deals of "aiding and abetting crimes against humanity in Myanmar."
READ THE STORY: Reuters
Why a Paid-For, ChatGPT Professional Is Inevitable
FROM THE MEDIA: Internet users are having fun with OpenAI's ChatGPT. We've seen people write computer programs with it, author an entire book, compose rap songs, and even seen malicious actors create dangerous malware. This has all been possible at the expense of OpenAI—at no cost to the user. Now, OpenAI is piloting plans to monetize the tool. Here's everything we know so far. OpenAI's decision to make ChatGPT publicly available at no cost is a money-guzzling decision but one that may soon pay off. By making the AI chatbot available to anyone who can sign up, the company created unparalleled publicity for its tool without too much of a publicity effort. Now, the company has announced ChatGPT Professional, a premium version of ChatGPT geared at professional use. However, if you want to use it, you'll need to sign-up for the ChatGPT Professional waitlist. OpenAI stressed in the waitlist document that access and potential use of the premium version are still experimental, subject to changes, and would only be available to a few select people for now.
READ THE STORY: MUO
TikTok Fined $5.4 Million by French Regulator for Violating Cookie Laws
FROM THE MEDIA: Popular short-form video hosting service TikTok has been fined €5 million (about $5.4 million) by the French data protection watchdog for breaking cookie consent rules, making it the latest platform to face similar penalties after Amazon, Google, Meta, and Microsoft since 2020. "Users of 'tiktok[.]com' could not refuse cookies as easily as accepting them and they were not informed in a sufficiently precise way of the objectives of the different cookies," the Commission nationale de l'informatique et des libertés (CNIL) said in a statement. The regulator said it conducted several audits between May 2020 and June 2022, finding that the ByteDance-owned company did not offer a straightforward option to refuse all cookies as opposed to just one click for accepting them. The option to "refuse all" cookies was introduced by TikTok in February 2022.
READ THE STORY: THN
MetaMask warns of new 'Address Poisoning' cryptocurrency scam
FROM THE MEDIA: Cryptocurrency wallet provider MetaMask is warning users of a new scam called 'Address Poisoning' used to trick users into sending funds to a scammer rather than an intended recipient. When MetaMask users send or receive cryptocurrency, it appears in the wallet transaction list. Clicking the transaction displays more details, including the token, the amount sent or received, and a short form of the third party's address. For example, below are examples of two shortened addresses that could be shown in MetaMask cryptocurrency transactions. While both wallet addresses look identical in their short form, they could be completely different, easily confusing MetaMask users. In a new post by MetaMask, the developers warn of a new scam called 'Address Poisoning' that relies on poisoning the wallet's transaction history with scammer's addresses that are very similar to addresses that a user recently had transactions.
READ THE STORY: BleepingComputer
Brave browser’s new Snowflake feature help bypass Tor blocks
FROM THE MEDIA: Brave Browser version 1.47 was released yesterday, adding the Snowflake extension in the software's settings, enabling users to turn their devices into proxies that help users in censored countries connect to Tor. Brave had already added support for Tor Bridges in Private Windows with Tor in version 1.44, released in September 2022, helping users bypass restrictions in the countries using the company's own resources. Starting yesterday, Brave users can now participate in the volunteer effort to promote freedom of information in areas where oppressive governments may try to restrict it. Tor Bridges are relays operated by volunteers to help people bypass censorship and Tor blocks by giving them an alternative entry point to the Onion network. The bridges are not listed publicly to protect them from the local regimes and their operators, who might try to block access to them, rendering them useless.
READ THE STORY: BleepingComputer
A Police App Exposed Secret Details About Raids and Suspects
FROM THE MEDIA: Last September, law enforcement agents from five counties in Southern California coordinated an operation to investigate, raid, and arrest more than 600 suspected sex offenders. The mission, Operation Protect the Innocent, was one of the largest such raids in years, involving over 64 agencies. According to the Los Angeles Police Department, it was coordinated using a free trial of an app called SweepWizard. The raid was hailed as a success by Chief Michael Moore of the LAPD at a press conference the following week. But there was a problem: Unbeknownst to police, SweepWizard had been leaking a trove of confidential details about the operation to the open internet. The data, which the LAPD and partners in the regional Internet Crimes Against Children (ICAC) Task Force uploaded to SweepWizard, included private information about the suspects as well as sensitive details that, in the wrong hands, could tip off suspects as to when they were going to be raided and cast suspicion on people who had not yet been convicted of any crime.
READ THE STORY: Wired
NSA asks Congress to let it get on with that warrantless data harvesting, again
FROM THE MEDIA: A US intelligence boss has asked Congress to reauthorize a controversial set of powers that give snoops warrantless authorization to surveil electronic communications in the name of fighting terrorism and so forth. NSA director General Paul Nakasone told the Privacy and Civil Liberties Oversight Board yesterday that the loss of Section 702 of the Foreign Intelligence Surveillance Act (FISA) would mean American spies would "lose critical insights into the most significant threats to our nation" if allowed to lapse on December 31. In his speech, Nakasone said Section 702 is "irreplaceable," and he provided several stories of the FBI and NSA cooperating using the law to stop terrorist plots and online attacks to justify his claim. Section 702 was added to the Foreign Intelligence Surveillance Act in 2008, and has long been a bone of contention between civil liberties groups arguing it's a gross privacy violation, and those who say that, if you're not a terrorist, surely a little harmless observation by Uncle Sam is okay.
READ THE STORY: The Register
The Difficulty of Disrupting Iranian Drones
FROM THE MEDIA: On January 6, the Treasury Department imposed sanctions on the executive board members of the Qods Aviation and Aerospace Industries Organization (IAIO), an Iranian defense company founded by the Islamic Revolutionary Guard Corps (IRGC) in 1985. IAIO designs and manufactures Mohajer-6 mid-range reconnaissance and combat drones, which were supposedly transferred to Russia in the summer. In September, Russia reportedly used the Mohajer-6 to coordinate an attack on the Ukrainian port of Odessa, contradicting Tehran’s denials of supplying drones to Moscow after the invasion of Ukraine. IAIO has been sanctioned by the Treasury Department’s Office of Foreign Assets Control (OFAC) since December 2013. The U.S. government may also increase sanctions against officials of the Iran Aircraft Manufacturing Industries Corporation (HESA), which produces the Shahed-136 suicide drone that Russia has renamed the Geran-2 and that has featured prominently in the war in Ukraine.
READ THE STORY: National Interest
Hacked evidence and stolen data swamp English courts
FROM THE MEDIA: A multimillion-pound high court case between an authoritarian Gulf emirate and an Iranian-American businessman has revealed how hacked evidence is being used by leading law firms to advance their clients’ claims. The case has included allegations that a former Metropolitan Police officer hired Indian hackers and that lawyers from a top City firm held a secret “perjury school” in the Swiss Alps to prepare false witness testimonies about how they got hold of illegally obtained information. In November the Bureau of Investigative Journalism and the Sunday Times exposed the criminal activities of Aditya Jain, a 31-year-old computer security expert who set up a “hack-for-hire” operation from his apartment in Gurugram, India.
READ THE STORY: The Bureau of Investigative Journalism
Canada's largest alcohol retailer's site hacked to steal credit cards
FROM THE MEDIA: The Liquor Control Board of Ontario (LCBO), a Canadian government enterprise and the country's largest beverage alcohol retailer, revealed that unknown attackers had breached its website to inject malicious code designed to steal customer and credit card information at check-out. LCBO revealed on Wednesday that third-party forensic investigators found a credit card stealing script that was active on its website for five days. "At this time, we can confirm that an unauthorized party embedded malicious code into our website that was designed to obtain customer information during the checkout process," LCBO said. "Unfortunately, customers who provided personal information on our check-out pages and proceeded to our payment page on LCBO.com between January 5, 2023, and January 10, 2023, may have had their information compromised."
READ THE STORY: BleepingComputer
Guccifer, the Hacker Who Launched Clinton Email Flap, Speaks Out After Nearly a Decade Behind Bars
FROM THE MEDIA: Arcel Lehel Lazar walked out of Federal Correctional Institute Schuylkill, a Pennsylvania prison, in August 2021. The 51-year-old formerly known only as Guccifer had spent over four years incarcerated for an email hacking spree against America’s elite. Though these inbox disclosures arguably changed the course of the nation’s recent history, Lazar himself remains an obscure figure. This month, in a series of phone interviews with The Intercept, Lazar opened up for the first time about his new life and strange legacy. Lazar is not a household name by unauthorized access standards — no Edward Snowden nor Chelsea Manning — but people will be familiar with his work. Throughout 2013, Lazar stole the private correspondence of everyone from a former member of the Joint Chiefs of Staff to “Sex and the City” author Candace Bushnell.
READ THE STORY: The Intercept
TSMC Chairman, Founder’s Details Hacked As Part of Data Breach
FROM THE MEDIA: The Taiwan Semiconductor Manufacturing Company's (TSMC) founder and chairman's personal details were leaked after an airline database was hacked and information posted online. The hack part of efforts by a group to blackmail the company. According to media reports, once the airline contacted the authorities, the details were posted in a forum. China Airlines has confirmed the breach, and it has also outlined that after cross-referencing some of the leaked information with its records, the company found some discrepancies. Details from the Taiwanese press reveal that China Airlines, which is the state-owned national carrier of the People's Republic of China (Mainland China), witnessed its membership database breached by a hacker group. This database contained details of a wide variety of both domestic and international high-profile figures, with the list covering politicians, businesspeople and media celebrities. The hackers did not ask the airline for a ransom, but they encouraged the affectees to file lawsuits with regulatory bodies to ensure that China Airlines complies with data protection laws, including those in the European Union and pays the affectees compensation.
READ THE STORY: WCCFTECH
AMD Revealed 31 Vulnerabilities Within Its Processor Lines, Ryzen & EPYC CPUs Included
FROM THE MEDIA: The company has created numerous mitigations to alleviate the exposed processors and has also disclosed a report from the company in cooperation with teams from three top companies — Apple, Google, and Oracle. The company also announced several AGESA variants listed in the update (AGESA code is found when building the system's BIOS and UEFI code). Due to the vulnerability's nature, the AGESA changes have been delivered to OEMs, and any patching will depend on each vendor to release it as soon as possible. It would be wise for consumers to visit the vendor's official website to find out if there is a new update waiting for download rather than waiting for the company to roll it out later. AMD Processors vulnerable to this new attack include Ryzen models for desktops, HEDT, Pro, and mobile CPU series. There is a single vulnerability labeled as "high severity," while two others are less extreme but still important to patch. All exposures are attacked through the BIOS and ASP bootloader (also known as the AMD Secure Processor bootloader).
READ THE STORY: WCCFTECH
No Black Boxes: Keep Humans Involved In Artificial Intelligence
FROM THE MEDIA: During the 1950s, Alan Turing proposed an experiment called the imitation game (now called the Turing test). In it, he posited a situation where someone—the interrogator—was in a room, separated from another room that had a computer and a second person. The goal of the test was for the interrogator to ask questions of both the person and the computer; the goal of the computer was to make the interrogator believe it was a human. Turing predicted that, eventually, computers would be able to mimic human behavior successfully and fool interrogators a high percentage of the time. Turing’s prediction has yet to come to pass, and there’s a fair question of whether computers will ever be able to truly complete the test. However, it’s both a useful lens to view the dynamic of how people view the potential capabilities of artificial intelligence and a source of irony. Though AI has amazing capabilities, it also has limits. Today, it’s clear that no one knows the full workings of the AI we create, and the lack of “explainability” and humans in the loop causes problems and missed opportunities.
READ THE STORY: Forbes
Pwn2Own 2023: Tesla Up for Grabs for Hackers
FROM THE MEDIA: Tesla has returned to the Pwn2Own hacking contest and is offering a $600,000 USD cash reward to anyone who can write an exploit capable of bypassing multiple systems in its electric vehicles (EVs) and achieving an arbitrary code execution — reports SecurityWeek. In addition to the cash prize, any hacker who succeeds will also get a free Tesla. “Success here gets a big payout and, of course, a brand-new Tesla,” the contest’s organizers announced on Thursday. Pwn2Own is a biannual ethical hacking contest where contenders gather to exploit widely used hardware and software through previously unknown vulnerabilities. Those who succeed are awarded a cash prize, and also get to keep the device they exploited.
READ THE STORY: Tesla North
Items of interest
Trump Promises to Use Special Forces On Smugglers and Cartels If Elected President Saying They Deserve The Death Penalty
FROM THE MEDIA: Former President Trump proclaimed Thursday that if elected again as US Commander-in-Chief, he would arm the military with special forces and other assets to unleash a powerful blow against smugglers, human trafficking groups, and cartels infiltrating our southern border. "Joe Biden has sided against the United States and with the cartels," Trump said in a video Thursday. "Biden’s open border policies are a deadly betrayal of our nation." "When I am president, it will be the policy of the United States to take down the cartels, just as we took down ISIS and the ISIS caliphate–and just as, unlike the situation we are in today, we had a very strong border," Trump continued. people saw him boasting about his administration having the most concrete and firm border in the history of the United States of America.
READ THE STORY: Philosophy Blogger
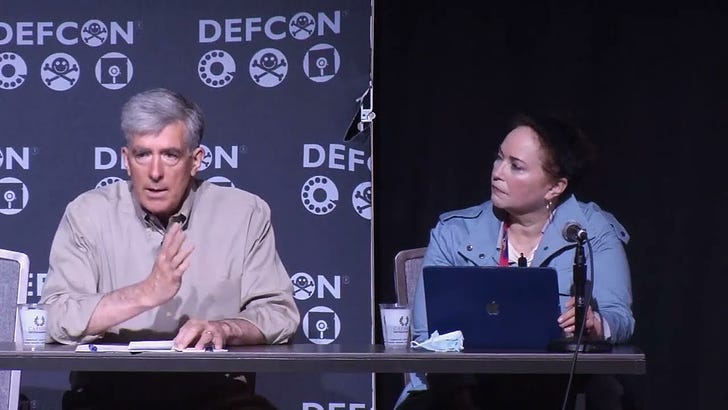
DEF CON 30 - Chris Inglis, Kim Zetter - A Policy Fireside Chat with the National Cyber Director (Video)
FROM THE MEDIA: A Policy Fireside Chat with the National Cyber Director Chris Inglis, moderated by Kim Zetter.
DEF CON 30 - Kenneth Geers - Computer Hacks in the Russia-Ukraine War (Video)
FROM THE MEDIA: The Russia-Ukraine war has seen a lot of computer hacking, on both sides, by nations, haxor collectives, and random citizens, to steal, deny, alter, destroy, and amplify information. Satellite comms have gone down. Railway traffic has been stymied. Doxing is a weapon. Fake personas and false flags are expected.
These open source products are reviewed from analysts at InfoDom Securities and provide possible context about current media trends in regard to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not specifically endorse any third-party claims made in their original material or related links on their sites, and the opinions expressed by third parties are theirs alone. Contact InfoDom Securities at dominanceinformation@gmail.com