Friday, January 13, 2023 // (IG): BB // BSidesCharm// Coffee for Bob
Securing the World's Energy Systems: Where Physical Security and Cybersecurity Must Meet
Analyst Comments: Operational Technologies (OT) (ICS/IIoT) infrastructures are extremely target rich and are being manipulated in present day conflicts. On Jan 12th CISA released twelve Industrial Control Systems (ICS) advisories on January 12, 2023. These advisories provide timely information about current security issues, vulnerabilities, and exploits surrounding ICS.
FROM THE MEDIA: The physical threat to the world's critical national infrastructure (CNI) has never been greater. At least 50 meters of the Nord Stream 1 and 2 underground pipelines that once transported Russian gas to Germany were destroyed in an attack in late September 2022, though it remains unclear who is to blame. More recently, Russia has also shifted its war in Ukraine to targeting energy infrastructure with its own missiles and Iran-supplied Shahed-136 drones. According to a tweet from Ukraine's President Volodymyr Zelensky on Oct. 18, "30% of Ukraine's power stations have been destroyed, causing massive blackouts across the country," while on Nov. 1 during a meeting with the European Commissioner for Energy, Kadri Simson, Zelensky said that between "30% and 40% of [the country's] energy systems had been destroyed."
READ THE STORY: DarkReading
Russian cyberattacks on Ukrainian infrastructure redefine the game
FROM THE MEDIA: After failures in its physical-world warfare strategy, Moscow has launched a massive and constant cyber offensive on Ukrainian civilian infrastructure the likes of which the world has never seen, Politico reported Thursday. Ukraine was hit by more than 2,000 cyberattacks in 2022, according to statistics from Ukraine’s Computer Emergency Response Team noted in the report. While the US and Israel often talk about millions of cyberattacks on a regular basis, these 2,000 attacks were serious ones on infrastructure. The number of publicly known serious attacks on Israeli infrastructure, versus data, is in the single digits. In other words, 2,000 attacks of that caliber from Russia are completely redefining the game of what is possible.
READ THE STORY: JPOST
Researchers Find 'Digital Crime Haven' While Investigating Magecart Activity
FROM THE MEDIA: Cybercriminals engaged in one form of criminal activity can sometimes have their hands in a wide range of other nefarious campaigns as well, as researchers recently discovered when analyzing the infrastructure associated with a fresh iteration of a Magecart skimmer. Magecart is a notorious — and constantly evolving — syndicate of multiple groups that specializes in placing card skimmers on e-commerce sites to steal payment card information. Over the years, groups belonging to the syndicate have executed numerous — sometimes massive — heists of card information from websites, including those belonging to major companies like TicketMaster and British Airways. Researchers from Malwarebytes recently observed a threat actor deploying a payment card skimmer — based on a framework called mr.SNIFFA — on multiple e-commerce sites.
READ THE STORY: DarkReading
CISA adds recently-announced Microsoft zero-day to exploited vulnerability catalog
FROM THE MEDIA: The Cybersecurity and Infrastructure Security Agency added a recently revealed bug to its known exploited vulnerability list this week after Microsoft confirmed it was being used in attacks. CISA ordered all federal civilian agencies to patch CVE-2023-21674 by January 31. The bug – first unveiled in Microsoft’s initial Patch Tuesday release of 2023 – affects the Windows Advanced Local Procedure Call (ALPC) and has a CVSS score of 8.8 out of a possible 10. “An attacker who successfully exploited this vulnerability could gain SYSTEM privileges,” Microsoft said. The Zero Day Initiative’s Dustin Child said bugs like this are “often paired with some form of code exaction to deliver malware or ransomware” and added that because it was reported to Microsoft by researchers from Avast, “that scenario seems likely here.” Qualys’ Saeed Abbasi agreed that the bugs are “are frequently leveraged in tandem with malware or ransomware delivery” while others noted that there is a working proof of concept for the vulnerability.
READ THE STORY: The Record
DIRNSA: Foreign surveillance program helped fend off cyberattacks
FROM THE MEDIA: NSA Director Gen. Paul Nakasone said Thursday that the special targeted internet surveillance program for non-U.S. citizens known as Section 702 has played an “irreplaceable” role in helping the agency fend off ransomware attacks and prevent weapons components from reaching adversaries, as well as being used to identify threats to U.S. troops. “702 has helped us to understand the strategic intentions of the foreign governments,” Nakasone explained to the U.S. Privacy and Civil Liberties Oversight Board (PCLOB) in a keynote speech, adding that 702 authorities have allowed the agency to disrupt foreign cyber attacks and ransomware operations. Nakasone did not provide much rich detail about the operations, aside from the list. But the statement was part of a broader effort meant to build support for the renewal of what has become a central tool for the intelligence community. Section 702 of the Foreign Intelligence Surveillance Act, or FISA, is set to sunset at the end of the year.
READ THE STORY: The Record
Millions of Aflac, Zurich insurance customers in Japan have data leaked after breach
FROM THE MEDIA: The Japanese customers of two large insurance companies have had their personal information leaked after the breach of a third-party service provider. Neither company would say if the two breaches were connected, and the attacked provider has not been named. But each company released statements this week warning their customers that their information was made public. Aflac director of communications Jon Sullivan said they recently became aware of a “data-related incident” involving Japanese customers. “The incident, caused by a vulnerability in a file transfer server, originated with a subcontractor of a third-party vendor that Aflac Japan uses for marketing purposes and affected approximately 1.3 million customers,” Sullivan said. “The data, which did not include personally identifiable information (PII), was posted on a dark website. This incident was confined to Aflac Japan and did not involve data related to U.S. operations or customers.”
READ THE STORY: The Record
QakBot Malware Used Unpatched Vulnerability to Bypass Windows OS Security Feature
FROM THE MEDIA: This paper investigates a recent QakBot phishing campaign’s ability to evade Mark-of-the-Web (MoTW) security features, allowing for escape from the designated security zone and successful installation of malicious software on victim device. Key observations: EclecticIQ analysts investigated QakBot phishing campaigns switching to a Zero-Day Vulnerability to evade Windows Mark of the Web (MoTW). QakBot may be able to increase its infection success rate as a result of the switch to a zero-day exploit. The threat actor distributes QakBot using phishing emails with a malicious URL inside. When a victim user clicks on the malicious URL, it starts to download an encrypted ZIP folder that contains an ISO image. If the ISO image is opened by victim, it will mount itself on a disk and open another File Explorer window that contains the final QakBot Loader as a JavaScript format which can be executed by a simple user click.
READ THE STORY: Security Boulevard
Fortinet says hackers exploited critical vulnerability to infect VPN customers
FROM THE MEDIA: An unknown threat actor abused a critical vulnerability in Fortinet’s FortiOS SSL-VPN to infect government and government-related organizations with advanced custom-made malware, the company said in an autopsy report on Wednesday. Tracked as CVE-2022-42475, the vulnerability is a heap-based buffer overflow that allows hackers to remotely execute malicious code. It carries a severity rating of 9.8 out of a possible 10. A maker of network security software, Fortinet fixed the vulnerability in version 7.2.3 released on November 28 but failed to make any mention of the threat in the release notes it published at the time. Fortinet didn’t disclose the vulnerability until December 12, when it warned that the vulnerability was under active exploit against at least one of its customers. The company urged customers to ensure they were running the patched version of the software and to search their networks for signs the vulnerability had been exploited on their networks. FortiOS SSL-VPNs are used mainly in border firewalls, which cordon off sensitive internal networks from the public Internet.
READ THE STORY: arsTECHNICA
Royal Mail cyberattack linked to LockBit ransomware operation
FROM THE MEDIA: A cyberattack on Royal Mail, UK's largest mail delivery service, has been linked to the LockBit ransomware operation. Yesterday, the Royal Mail disclosed that they suffered a cyber incident that forced them to halt international shipping services. "Royal Mail is experiencing severe service disruption to our international export services following a cyber incident," disclosed Royal Mail in a service update. While Royal Mail did not provide any details on the cyberattack, they said they were working with external cybersecurity experts and have notified UK regulators and law enforcement. As first reported by The Telegraph, the attack on Royal Mail is now confirmed to be a ransomware attack by the LockBit operation, or at least someone using their encryptors.
READ THE STORY: BleepingComputer // BBC
Microsoft: Cuba ransomware hacking Exchange servers via OWASSRF flaw
FROM THE MEDIA: Microsoft says Cuba ransomware threat actors are hacking Microsoft Exchange servers unpatched against a critical server-side request forgery (SSRF) vulnerability also exploited in Play ransomware attacks. Cloud computing provider Rackspace recently confirmed that Play ransomware used a zero-day exploit dubbed OWASSRF targeting this bug (CVE-2022-41080) to compromise unpatched Microsoft Exchange servers on its network after bypassing ProxyNotShell URL rewrite mitigations. According to Microsoft, the Play ransomware gang has abused this security flaw since late November 2022. The company advises customers to prioritize CVE-2022-41080 patching to block potential attacks.
READ THE STORY: BleepingComputer
Chainalysis: Russian Exchange Dominates Illicit Crypto Volume
FROM THE MEDIA: The value of crypto transactions related to illicit activities rose for the second consecutive year in 2022 to $20.1 billion, according to a Chainalysis report, up from $18 billion in 2021. Around 44 percent of 2022’s illicit transaction volume was from activity associated with sanctioned entities with much of it originating from Russian exchange, Garantex. Chainalysis defines wallets as «illicit» if they are part of a sanctioned entity. While the volume of stolen crypto rose 7 percent, other illicit crypto transactions – including scams, ransomware, terrorism financing and human trafficking – fell in 2022. Chainalysis cited the market downturn as a potential driver to the drop, noting that crypto scams have historically taken in less revenue during bear markets. Chainalysis also said that the $20.1 billion figure only includes recorded on-chain activity and excludes off-chain crimes, like fraudulent accounting by crypto firms, as well as crypto proceeds from non-crypto-related crimes, like drug trafficking payments.
READ THE STORY: FINEWS
Air traffic control system failure highlights importance of infrastructure investment
FROM THE MEDIA: On Jan. 11, the Federal Aviation Administration Notice to Air Missions system failed. This resulted in a nationwide ground stop, impacting thousands of flights and thousands of passengers. Could this failure have been avoided? The National Airspace System is the highway for air travel, with the FAA serving as the de facto “traffic cops.” One of their objectives is to ensure the safe and efficient flow of air travel, from the moment airplanes leave their departure gate, on their trek to the runway, between takeoff and landing, and their path back to a deplaning gate. With around 25,000 flights every day, air traffic controllers are the unsung heroes of air travel in the United States. Yet their job is only as effective as the computer systems available to monitor flights and possible hazards that can compromise air travel safety. The Notice to Air Missions system is designed to provide short-term information for pilots prior to their departure. These may include emerging bird hazards at airports, runway closures or low-altitude construction obstacles that may be temporary or transient, all of which provide information that supports pilots and safe air travel.
READ THE STORY: The Dallas Morning News
North Korea’s Cryptocurrency Craze and its Impact on U.S. Policy
FROM THE MEDIA: In 2022 alone, North Korea, or the Democratic People’s Republic of Korea (DPRK), has reportedly stolen over $1 billion in cryptocurrency from organizations in the cryptocurrency sector via one of its primary hacking outfits—Lazarus Group. This is up from $400 million in 2021, and these heists account for a third of all losses from cyber intrusions in the cryptocurrency sector this year. Further upheaval in the cryptocurrency sector has already caused financial authorities to increase calls for regulation. Bankruptcy and scandals involving multiple companies are tanking the industry and the value of cryptocurrencies. Many of these companies are based in the United States, making U.S. regulation especially consequential. The country’s central role in both the cryptocurrency sector and efforts to regulate it—along with the sector’s current descent into chaos—make this the opportune moment to focus U.S. government policy initiatives on cryptocurrency companies and products.
READ THE STORY: Council on Foreign Relations
RAT malware campaign tries to evade detection using polyglot files
FROM THE MEDIA: Operators of the StrRAT and Ratty remote access trojans (RAT) are running a new campaign using polyglot MSI/JAR and CAB/JAR files to evade detection from security tools. The campaign was spotted by Deep Instinct, which reports that the threat actors achieve moderate success in evading detection by anti-virus engines. This is notable considering how old and well-documented the two particular RATs are. Polyglot files combine two or more file formats in a way that makes it possible for them to be interpreted and launched by multiple different applications without error. Threat actors have been using polyglot files to hide malicious code, confuse security solutions, and bypass protections for several years now. Most recently, we reported about this technique being employed by the StrelaStealer malware that targets Outlook and Thunderbird accounts.
READ THE STORY: BleepingComputer
IcedID Malware Strikes Again: Active Directory Domain Compromised in Under 24 Hours
FROM THE MEDIA: A recent IcedID malware attack enabled the threat actor to compromise the Active Directory domain of an unnamed target less than 24 hours after gaining initial access, while also borrowing techniques from other groups like Conti to meet its goals. "Throughout the attack, the attacker followed a routine of recon commands, credential theft, lateral movement by abusing Windows protocols, and executing Cobalt Strike on the newly compromised host," Cybereason researchers said in a report published this week. IcedID, also known by the name BokBot, started its life as a banking trojan in 2017 before evolving into a dropper for other malware, joining the likes of Emotet, TrickBot, Qakbot, Bumblebee, and Raspberry Robin. Attacks involving the delivery of IcedID have leveraged a variety of methods, especially in the wake of Microsoft's decision to block macros from Office files downloaded from the web.
READ THE STORY: THN
FortiOS Flaw Exploited as Zero-Day in Attacks on Government and Organizations
FROM THE MEDIA: A zero-day vulnerability in FortiOS SSL-VPN that Fortinet addressed last month was exploited by unknown actors in attacks targeting the government and other large organizations. "The complexity of the exploit suggests an advanced actor and that it is highly targeted at governmental or government-related targets," Fortinet researchers said in a post-mortem analysis published this week. The attacks entailed the exploitation of CVE-2022-42475, a heap-based buffer overflow flaw that could enable an unauthenticated remote attacker to execute arbitrary code via specifically crafted requests. The infection chain analyzed by the company shows that the end goal was to deploy a generic Linux implant modified for FortiOS that's equipped to compromise Fortinet's intrusion prevention system (IPS) software and establish connections with a remote server to download additional malware and execute commands. Fortinet said it was unable to recover the payloads used in the subsequent stages of the attacks. It did not disclose when the intrusions took place.
READ THE STORY: THN
Russia criticizes Reuters story on Russian hackers targeting U.S. nuclear scientists
FROM THE MEDIA: Russia's Foreign Ministry on Thursday criticized Reuters for spreading what it said was poorly sourced anti-Russian propaganda with a story about a Russian hacking team which targeted three nuclear research laboratories. Reuters on Jan. 6 reported the Russian hacking team, known as Cold River, had targeted three nuclear research laboratories in the United States this past summer, according to internet records reviewed by Reuters and five cyber security experts. Russia's Federal Security Service (FSB), the domestic security agency that also conducts espionage campaigns for Moscow, and Russia's embassy in Washington did not respond to emailed requests for comment for the Jan. 6 article. "The latest pseudo investigation was unfortunately published by Reuters news agency," Maria Zakharova, Russia's Foreign Ministry spokeswoman, told reporters.
READ THE STORY: Reuters
French army hails Ukraine’s cyber defense ‘revolution’
FROM THE MEDIA: Ukraine has managed to carry out “a real revolution by moving upmarket in its defensive cyber fight” while suffering from high-level cyber attacks, the head of France’s Cyber Defense Command (COMCYBER), General Aymeric Bonnemaison, said on Thursday. Cyber attacks, particularly of Russian origin, have been hitting Ukraine and its critical infrastructure since at least 2014, Bonnemaison said during a press conference on Thursday. In response, the French Ministry said that the country has strengthened “its cyber defense capabilities,” which has enabled it to carry out “a real revolution by moving upmarket in its computer defense fight,” according to Bonnemaison. Last December, during a closed-door hearing at the National Assembly, which was made public on Thursday, General Bonnemaison explained that Ukraine “worked on its vulnerabilities with the Western cyber powers, first and foremost the United States.
READ THE STORY: EURACTIV
Items of interest
China moves to take ‘golden shares’ in Alibaba and Tencent units
FROM THE MEDIA: China is moving to take “golden shares” in local units of Alibaba and Tencent as Beijing formalizes a greater role in overseeing the country’s powerful tech groups. The Chinese government has responded to a stuttering economy by backing away from the tough fines and sanctions that were a hallmark of its campaign to rein in the country’s largest tech groups, but which also scared off foreign investors. While the heavy-handed crackdown has ebbed, the government is increasingly snapping up small equity stakes in the local operations of big tech companies, as it recently did with TikTok owner ByteDance. This provides the Communist party with a mechanism to remain deeply involved in their businesses, particularly the content they broadcast to millions of Chinese people.
READ THE STORY: FT
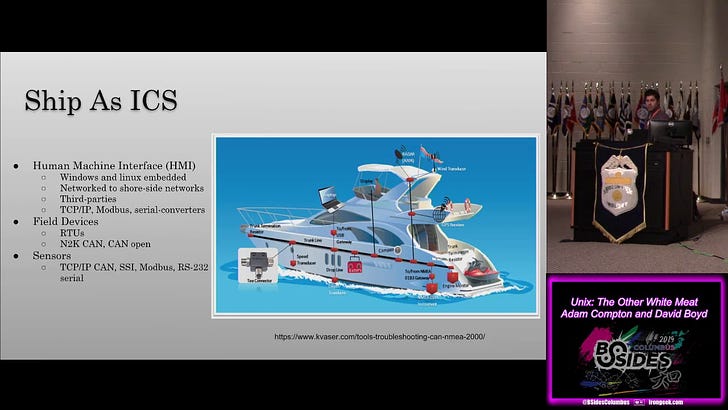
Ship Hacking Data on the Open Seas Brian Olson (Video)
FROM THE MEDIA: These are the videos from BSides Columbus 2019.
Hack the Port 2022 (Video)
FROM THE MEDIA: Fathom5 was live at Hack the Port 2022, in Ft. Lauderdale, Florida to demonstrate the Grace Maritime Cyber Testbed systems as well as facilitate an event in the Capture the Flag competition. Gary Kessler, Fathom5's principal consultant participated as part of several panels throughout the event. Hack the Port is a cybersecurity event, presented by MISI and Dream Port, focusing on the maritime industry.
These open source products are reviewed from analysts at InfoDom Securities and provide possible context about current media trends in regard to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not specifically endorse any third-party claims made in their original material or related links on their sites, and the opinions expressed by third parties are theirs alone. Contact InfoDom Securities at dominanceinformation@gmail.com