Thursday, December 22, 2022 // (IG): BB // THM:Windows RE // Coffee for Bob
Guardian newspaper hit by suspected ransomware attack, staff told not to come to office
FROM THE MEDIA: Staff at The Guardian newspaper have been told not to come into the office and to work from home for the rest of the week due to a suspected ransomware attack which struck late on Tuesday. The attack has impacted a number of business services at the 200-year-old news organization, but not its online site and apps which will continue to publish stories. An email sent to The Guardian’s employees on Wednesday and seen by The Record tells staff: “The issues affecting Kings Place, the VPN, and the wires are ongoing, and our IT and engineering teams are working to resolve them.” It is not yet clear what if any data the attackers may have accessed or stolen, but the sensitive information held on newsroom systems could cause a significant data protection breach if one has taken place, alongside potentially exposing sources.
READ THE STORY: The Record
Zerobot Botnet Emerges as a Growing Threat with New Exploits and Capabilities
FROM THE MEDIA: The Zerobot DDoS botnet has received substantial updates that expand on its ability to target more internet-connected devices and scale its network. Microsoft Threat Intelligence Center (MSTIC) is tracking the ongoing threat under the moniker DEV-1061, its designation for unknown, emerging, or developing activity clusters. Zerobot, first documented by Fortinet FortiGuard Labs earlier this month, is a Go-based malware that propagates through vulnerabilities in web applications and IoT devices like firewalls, routers, and cameras. "The most recent distribution of Zerobot includes additional capabilities, such as exploiting vulnerabilities in Apache and Apache Spark (CVE-2021-42013 and CVE-2022-33891 respectively), and new DDoS attack capabilities," Microsoft researchers said.
READ THE STORY: THN
FBI warns of search engine ads pushing malware, phishing
FROM THE MEDIA: The FBI warns that threat actors are using search engine advertisements to promote websites distributing ransomware or stealing login credentials for financial institutions and crypto exchanges. In today's public service announcement, the federal law enforcement agency said threat actors purchase advertisements that impersonate legitimate businesses or services. These ads appear at the top of search result pages and link to sites that look identical to the impersonated company's website. "When a user searches for that business or service, these advertisements appear at the very top of search results with minimum distinction between an advertisement and an actual search result," warns the FBI.
READ THE STORY: Bleeping Computer
Godfather malware makes banking apps an offer they can’t refuse
FROM THE MEDIA: Crooks are using an Android banking Trojan dubbed Godfather to steal from banking and cryptocurrency exchange app users in 16 countries, according to Group-IB security researchers. The security firm first detected Godfather in June 2021 and as of October, the credential-stealing malware has targeted the users of more than 400 applications. This includes 215 international banks, 94 cryptocurrency wallets, and 110 crypto exchange platforms in the US, Turkey, Spain, Canada, Germany, France and the UK. Additionally, the malware's code has an interesting functionality that stops it from attacking Russian-speaking users or those that speak a handful of other languages used in the former Soviet Union including Azerbaijani, Armenian, Belarusian, Kazakh, Kyrgyz, Moldovan, Uzbek, or Tajik.
READ THE STORY: The Register
Info-stealing malware targeting Ukraine’s military system
FROM THE MEDIA: Ukraine's DELTA military intelligence system had its users targeted by phishing attacks spreading the FateGrab and StealDeal information stealing malware, according to The Hacker News. The UAC-0142 threat cluster sent phishing emails relating to fake root certificate update warnings that included PDF attachments with links to archive files on a fake DELTA domain, which then proceeds to deploy the malware, said the Computer Emergency Response Team of Ukraine. Files containing certain extensions are being exfiltrated by FateGrab while passwords and other data stored in web browsers are being targeted by the StealDeal malware.
READ THE STORY: SCMAG
Cyberattack compromises German industrial giant ThyssenKrupp
FROM THE MEDIA: German multinational industrial engineering and steel production giant ThyssenKrupp AG has suffered a cyberattack that compromised its Materials Services division and corporate headquarters. According to a spokesperson, Thyssenkrupp is currently the target of a cyberattack that is probably being carried out by organized crime. As of right now, no harm has been done, and there are no signs that any data has been stolen or altered. Even though ThyssenKrupp did not specify the attack’s nature, the company’s cybersecurity team quickly identified and stopped the intrusion, according to a company spokesperson. There is no evidence of any damage, data theft, or modification resulting from it. The spokesperson further stated that other business divisions were unaffected by the attack.
READ THE STORY: TEISS
Second-gen Starlink ready to launch
FROM THE MEDIA: SpaceX has told the Federal Communications Commission (FCC) that it is ready to start launching its second generation Starlink satellites. The letter to the FCC says that it anticipates beginning its second generation satellites “before the end of December”. SpaceX has also asked for FCC permission to bring into use these second generation craft and have them connect to existing users and their terminals. SpaceX wants the FCC to grant a 60-day permission for these new broadband services. The request is made to give the FCC time to make its expected long-term approval. This move, says SpaceX, will allow access to “the increased capacity for low-latency broadband services from SpaceX’s upgraded, next-generation NGSO system as soon as its satellites are deployed.”
READ THE STORY: Advanced Television
S. Korea releases high-resolution satellite photo of Pyongyang
FROM THE MEDIA: South Korea on Thursday released a photo of Pyongyang taken from one of its own satellites after North Korea published imagery of Seoul using what it claimed was a military spy satellite. The color photo, taken with "land satellite No. 1," clearly shows Kim Il-sung Square and its surrounding facilities, including a history museum, an art museum and a department store. By contrast, the North Korean photo released Monday was in black and white, and barely showed the outlines of bridges across the Han River and a port in the western city of Incheon. The North's Korean Central News Agency said the camera fitted on the "test-piece satellite" built for military reconnaissance purposes had a resolution of 20 meters.
READ THE STORY: Yonhap News Agency
The Guardian newspaper hacked in suspected ransomware attack
FROM THE MEDIA: Guardian News & Media Ltd., the publisher of the U.K. newspaper The Guardian, has been struck by a suspected ransomware attack. Details of the suspected ransomware attack were fittingly published today by The Guardian, which said that the “incident” began late Tuesday night U.K. time and had affected parts of the company’s technology infrastructure. The online publishing of The Guardian has not been affected by the attack. However, there is said to have been some disruption to behind-the-scenes services, and staff were told to work from home. Guardian News & Media said it was confident it could still produce the print copy of its newspaper on Thursday.
READ THE STORY: siliconANGLE
Ukraine’s Cyber Units Aim to Retain Staff, Keep Services Stable as War Enters Year Two
FROM THE MEDIA: Victor Zhora, deputy chief of Ukraine’s State Service of Special Communications and Information Protection, said that the country is still battling Russian cyberattacks, and although the strikes haven’t been as destructive as many people expected, the situation could escalate quickly. Ukrainian President Volodymyr Zelensky on Wednesday met President Biden at the White House and addressed a joint session of Congress, seeking to gather political support for the country’s defense against Russia’s invasion. Mr. Biden used the occasion to say that the U.S. will provide a Patriot antimissile battery to Ukraine. Mr. Zhora’s agency has adjusted strategy in several ways since Russia invaded Ukraine in February. His team has moved data abroad, to countries including Poland, to protect it during the war and learned how to safeguard data centers during frequent power outages.
READ THE STORY: WSJ
Espionage, Not Blackouts, Is Theme of Russian Hacking in Ukraine
FROM THE MEDIA: Oleh Derevianko, co-founder of the cyber firm ISSP, which has an office in Ukraine, told me he wasn’t overly concerned when hackers defaced several government websites with the message “be afraid and expect the worst,” in January, before the Russian invasion began. After all he’d seen more serious attacks, like when Russians were accused of hacking Ukrainian power facilities on multiple occasions in recent years. One of those breaches, in 2015, resulted in blackouts for 230,000 people. And while the world never experienced a Russian “cyber Pearl Harbor” — a phrase that makes me wince — the invasion of Ukraine shows how cyber-espionage is used as a tool to gather information and taunt the enemy in war, rather than as a means to cause destruction. At the same time that ground troops are churning through traditional weaponry, Russian military-linked spies have attempted to break into the Kyiv’s networks to aid Moscow’s efforts in more nuanced ways.
READ THE STORY: BLOOMBERG
Biden signs quantum computing cybersecurity bill into law
FROM THE MEDIA: President Biden on Wednesday signed legislation to encourage federal government agencies to adopt technology that is protected from decryption by quantum computing. The Quantum Computing Cybersecurity Preparedness Act earlier this month progressed through the Senate after companion legislation passed the House in July. It is co-sponsored by Sens. Rob Portman, R-Ohio, and Maggie Hassan, D-N.H. The newly enacted legislation comes amid fears that significant leaps in quantum technology being made by countries hostile to the United States, including China, could allow existing forms of secure encryption to be cracked much more quickly.
READ THE STORY: Fedscoop
A global ad fraud campaign based on Google Ads has made millions
FROM THE MEDIA: Scammers have used the traffic from an adult website to generate clicks on Google Ad banners, netting them huge returns, experts have revealed. Researchers from Malwarebytes, which first spotted the campaign, revealed how someone created an ad campaign on one of the major adult ad networks and used the “popunder” ad format. It’s essentially a pop-up, but it goes under the active browser window. That way, the ads displayed can only be seen after the user closes, or minimizes, the browser. Then, they created a fake news website, whose content is scraped from other content sites. The articles published on this website include various tutorials, guides, and similar. Being “clean” (no adult content, gambling, or similar), the site was allowed to show ads from the Google Ads network.
READ THE STORY: TechRadar
SEO Poisoning Attack Linked to 144,000 Phishing Packages
FROM THE MEDIA: In a recent incident involving the NuGet, PyPI, and NPM packages, threat actors uploaded approximately 144,000 malicious packages to these open-source package repositories, containing links to phishing and scam websites. These packages contain links to phishing and scam websites. These packages were part of a BlackHat SEO / Search Engine Poisoning campaign, intended to manipulate search engine results and promote the ranking of the threat actors' scam pages by creating backlinks from trusted websites. Search engine poisoning (also known as "malicious search results") is a technique used to inject spammy or malicious content into the search results of a search engine. One way this can be done is by creating backlinks from legitimate websites to malicious websites.
READ THE STORY: Security Boulevard
FCC proposes record fine for robocallers who spammed at least 500 million
FROM THE MEDIA: The Federal Communications Commission is recommending a nearly $300 million fine for two men accused of running a robocall scheme offering scam auto warranties. According to the FCC announcement on Wednesday, California residents Roy Cox, Jr. and Michael Aaron Jones are behind the operation, which made 5 billion robocalls to 500 million people during a three-month span last year. The proposed fine is the largest in the FCC’s history. The calls were conducted through their company, Sumco Panama company, “as well as other domestic and foreign entities, and a host of international cohorts located in Panama and Hungary,” the FCC said, beginning in 2018. The calls attempted to mislead people into thinking their warranties were expiring and getting them to transfer to a “warranty specialist.”
READ THE STORY: The Record
GitHub incident allowed attacker to copy Okta’s source code
FROM THE MEDIA: Access management giant Okta had some of its source code copied after an intruder gained unauthorized access to its private GitHub repositories, the company said Wednesday. The security incident, which took place “in early December,” affected Okta Workforce Identity Cloud, which provides anti-phishing features, passkey management, and a number of other security tools to enterprise users. The incident does not pertain to Okta’s Auth0 products, according to a statement posted to the company’s website Wednesday afternoon. “Our investigation concluded that there was no unauthorized access to the Okta service, and no unauthorized access to customer data,” the company said. “Okta does not rely on the confidentiality of its source code for the security of its services. The Okta service remains fully operational and secure.”
READ THE STORY: The Record
Raspberry Robin Malware Caught Employing A Clever Tactic To Dupe Security Researchers
FROM THE MEDIA: Earlier this year, researchers from the threat intelligence group Red Canary identified an infectious computer worm that was found to have been present in customers’ environments going back to September 2021. According to later analysis by Microsoft, this malware, which researchers named “Raspberry Robin,” may date as far back as 2019 and has since grown to integrate with a larger malware ecosystem. New research by Trend Micro has revealed an updated version of Raspberry Robin that began spreading through telecommunications and government systems in September. This new variant attempts to trick security researchers by obscuring its real payload and deploying a fake payload when it detects active security tools.
READ THE STORY: Hothardware
Zerobot malware now spreads by exploiting Apache vulnerabilities
FROM THE MEDIA: The Zerobot botnet has been upgraded to infect new devices by exploiting security vulnerabilities affecting Internet-exposed and unpatched Apache servers. The Microsoft Defender for IoT research team also observed that this latest version adds new distributed denial-of-service (DDoS) capabilities. Zerobot has been under active development since at least November, with new versions adding new modules and features to expand the botnet's attack vectors and make it easier to infect new devices, including firewalls, routers, and cameras. Since early December, the malware's developers have removed modules that targeted phpMyAdmin servers, Dasan GPON home routers, and D-Link DSL-2750B wireless routers with year-old exploits.
READ THE STORY: Bleeping Computer
Researchers Develop AI-powered Malware Classification for 5G-enabled IIoT
FROM THE MEDIA: The global industrial internet of things (IIoT) market reached an all-time high in 2022 and, by many accounts, it is expected to continue to grow. It is estimated the market will reach $106.1bn by 2026, according to MarketsandMarkets. Meanwhile, Data Bridge Market Research mentions a global value of $541bn by 2029 and Future Markets Insight expects it to reach $1.3tn by 2032. This surge comes in a context where there are very few IoT standards and regulations, let alone IIoT specific standards. This poses a significant security risk, leaving devices used in critical applications such as healthcare, safety systems, or utilities, vulnerable to cyberattacks. To start addressing the problem, a team of multinational researchers led by Professor Gwanggil Jeon from Incheon National University, in South Korea, have developed a deep learning-based malware detection and classification system. Their work was published online on September 9, 2022 in the journal IEEE Transactions on Industrial Informatics.
READ THE STORY: InfoSecMag
Corsair keyboard bug makes it type on its own, no malware involved
FROM THE MEDIA: Corsair has confirmed that a bug in the firmware of K100 keyboards, and not malware, is behind previously entered text being auto-typed into applications days later. The company's statement comes after multiple K100 users have reported that their keyboards are typing text on their own at random moments. This behavior was first reported on the Corsair forums in August 2022, leaving people puzzled and concerned that some form of keylogging or malware was behind the behavior. Some said they had tested their K100 keyboards in safe mode to exclude the chances of malware running on Windows and still witnessed random word typing, so the source of the problem was determined to be in the hardware itself. As first reported by Ars Technica, a Corsair spokesperson responded to concerns, saying that their keyboards do not have keylogging capabilities, nor do they actively monitor what users type on them.
READ THE STORY: Bleeping Computer
XLL files in Excel increasingly used for malicious activity
FROM THE MEDIA: Significantly more advanced persistent threat groups and malware families have adopted XLL files in Excel to serve as an initial vector following the adoption of the technique by the Dridex and Formbook commodity malware families last year, reports The Register. China-linked threat operation APT10, also known as Potassium, Chessmaster or menuPass, has leveraged XLLs to facilitate Anel Backdoor malware injection, a Cisco Talos report showed. XLLs have also been used by the Stone Panda operation, also known as TA410 or Cicada, as well as the DoNot APT group and Russian cybercrime operation FIN7. With most users disregarding warnings by Excel prior to loading the files, more XLL-based malware attacks are expected in the coming year.
READ THE STORY: SCMAG
Kaspersky Research Finds Reverse Engineering Is the Most On-Demand Skill Among InfoSec Specialists
FROM THE MEDIA: According toresults shown by the latest statistics from participantspassing Kaspersky Expert Training courses, the most desired skill IT security professionals wanted to advance in 2022 is the ability to reverse engineer malware. According to the Burning Glass report, the number of new cybersecurity programs is rapidly growing, but demand for cyber professionals is growing faster and outstripping the supply of skilled workers, as companies now pay more attention to their cybersecurity than previously. Kaspersky has launched Expert Training, a series of courses for those who want to advance their IT security skills and take them to the next level by learning how to identify threats quicker and with less effort.
READ THE STORY: DARKReading
Ukraine Takes Down Domestic Pro-Kremlin Bot Farms
FROM THE MEDIA: Ukrainian law enforcement dismantled more than a dozen bot farms that were active inside the country, accusing their operators of spreading Russian propaganda through more than 1.5 million fake accounts. Searches conducted by the Cyber Police of Ukraine - a unit of the Ministry of Internal Affairs - resulted in the seizure of more than 100,000 SIM cards, including cards from Russian mobile operators, Ukrainian authorities said on Tuesday. Police arrested 31 individuals across 24 locations. Russia's attempted conquest of Ukraine is accompanied by heavy doses of online disinformation and propaganda aimed at splitting support for Kyiv. The rise in internet usage in Ukraine over the past decade is fueling the spike in Kremlin digital messaging. Three-fourths of Ukrainians are online and nearly 9 out of 10 can receive cellular signals at least as fast as 3G.
READ THE STORY: BankInfoSec
CISA Warns Healthcare Organizations of Cuba Ransomware Threat
FROM THE MEDIA: Cuba ransomware actors, with no connection to the Republic of Cuba, have continued to attack U.S. entities, including healthcare organizations, since they were first identified in November 2021. The FBI and the Cybersecurity and Infrastructure Security Agency released a new cybersecurity advisory (CSA) this month warning health IT leaders that the number of U.S. entities compromised by Cuba ransomware has doubled since December 2021. Not only has the frequency of attacks increased, but their tactics, techniques and procedures (TTPs) have become more sophisticated. According to the CSA, third-party sources have identified possible links between Cuba ransomware actors, RomCom remote access Trojan actors and Industrial Spy ransomware actors.
READ THE STORY: Health Tech Magazine
Items of interest
Chris Inglis to resign as national cyber director
FROM THE MEDIA: National Cyber Director Chris Inglis plans to step down from his position as a senior White House cybersecurity adviser, a decision first reported by CNN and confirmed to CyberScoop by three sources with direct knowledge of the matter. The news comes as Inglis is traveling in Japan on a trip meant to strengthen cyber collaboration with a key ally in the region and as cybersecurity issues generally are topping the White House agenda. President Biden nominated Inglis, the former deputy director of the National Security Agency, to lead the newly formed Office of the National Cyber Director last year, tasking him to stand up an office that aims to bring a unified approach to U.S. cybersecurity policy.
READ THE STORY: Cyberscoop
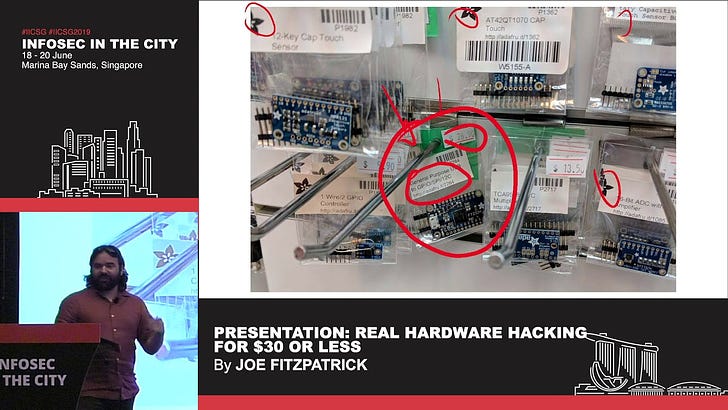
Real Hardware Hacking for S$30 or Less (Video)
FROM THE MEDIA: Without too much investment, you can download some software and tools and start hacking on them. Hardware, on the other hand, requires physical tools and target systems.
Open Source Tools of the Hardware Hacking Trade - Joe Grand (Video)
FROM THE MEDIA: Many embedded systems contain design flaws that could lead to exploitable vulnerabilities. In order to discover such flaws, hackers and engineers use a specific set of tools. In this session, Joe will discuss his favorite open source hardware hacking and reverse engineering tools, including those that monitor/decode digital communications, extract firmware, inject/spoof data, and identify/connect to debug interfaces.
These open source products are reviewed from analysts at InfoDom Securities and provide possible context about current media trends in regard to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not specifically endorse any third-party claims made in their original material or related links on their sites, and the opinions expressed by third parties are theirs alone. Contact InfoDom Securities at dominanceinformation@gmail.com