Wednesday, October 26, 2022 // (IG): BB // INTSUM // Coffee for Bob
Who is cutting the world's fiber optic cables
FROM THE MEDIA: The world's fiber optic cables are being cut at an alarming rate and some people are starting to believe it might not be a coincidence. Recently, there has been a slew of cut internet cables, especially in the UK. An undersea “submarine cable” was recently cut off the coast of northern Scotland, which has now been blamed on a fishing vessel. A major fiber optic cable has been cut near Aix-en-Provence, France, causing a global internet connectivity slowdown. Cybersecurity company Zscaler. Experts believe that the cable was severed in a deliberate “act of vandalism"; others have described it as “sabotage.”
READ THE STORY: Fudzilla
Chinese hackers exploit gaps in US intelligence sharing, senator says
FROM THE MEDIA: Chinese hackers are more easily able to steal personal data because of a lack of intelligence sharing between U.S. spy agencies and the Federal Trade Commission, a member of the Senate Select Committee on Intelligence has warned. Sen. Ron Wyden, an Oregon Democrat, said Tuesday in a letter written jointly to Lina Khan, FTC chair, and Avril Haines, director of national intelligence, that “the intelligence community is sharing very little information” with the FTC, especially about personal information or employees that China is likely to target for cyber-espionage purposes.
READ THE STORY: Stars and Stripes
Massive cryptomining campaign abuses free-tier cloud dev resources
FROM THE MEDIA: An automated and large-scale 'freejacking' campaign abuses free GitHub, Heroku, and Buddy services to mine cryptocurrency at the provider's expense. The operation relies on abusing the limited resources offered to free-tier cloud accounts to generate a tiny profit from each free account, which, when combined, becomes something more significant. The threat actor behind the campaign, called 'Purpleurchin,' was observed performing over a million function calls daily, using CI/CD service providers such as GitHub (300 accounts), Heroku (2,000 accounts), and Buddy.works (900 accounts).
READ THE STORY: Bleeping Computer
Botnet Server Harvesting 167,000 Card Dumps Discovered
FROM THE MEDIA: Security researchers say attackers typically target payment card data using so-called Magecart tactics, which refers to using "digital skimmers" or sniffers, typically in the form of JavaScript, that they surreptitiously install onto e-commerce site servers to grab card data that is input by customers. Data stolen in such attacks typically includes card numbers, expiration dates and CVVs, as well as payment card owners' names and addresses.
READ THE STORY: GovInfoSec // HackRead // InfoSecMag // SecurityAffairs
Domestic Kitten updates its FurBall malware
FROM THE MEDIA: Researchers at ESET have observed a new version of the FurBall Android spyware used by the Iranian threat actor Domestic Kitten. The malware is targeting citizens of Iran, and is being distributed through "a translation app via a copycat of an Iranian website that provides translated articles, journals, and books": "Based on the contact information from the legitimate website, they provide this service from Iran, which leads us to believe with high confidence that the copycat website targets Iranian citizens."
READ THE STORY: The Cyberwire
Dormant Colors Campaign Injects 1M Chrome Browsers With Revenue Generating Malware
FROM THE MEDIA: Researchers at the cybersecurity company Guardio have uncovered a campaign that has stealthily injected malware into the chromium-based browsers of over one million victims. The campaign makes use of browser extensions distributed through the Google Chrome Web Store and the Microsoft Edge Add-ons store. However, the extensions don’t come packaged with any malicious payloads, enabling them to avoid detection It’s only after they’re installed that the extensions side-load malicious code, activating their pernicious behavior.
READ THE STORY: Hothardware
Dutch police arrest hacker who breached healthcare software vendor
FROM THE MEDIA: The Dutch police have arrested a 19-year-old man in western Netherlands, suspected of breaching the systems of a healthcare software vendor in the country, and stealing tens of thousands of documents. These documents might contain sensitive personal and medical data of patients of healthcare providers using the company's systems. At this time, it has not been determined if the hacker shared or attempted to sell the stolen data, as is common in data breaches.
READ THE STORY: Bleeping Computer
Russia’s Sberbank repels largest cyber attack in its history
FROM THE MEDIA: The DDoS attack, which is a denial-of-service attack, involved at least 104,000 hackers with at least 30,000 computers located in different countries, Kuznetsov told Rossiya 24 television channel on Tuesday. The senior executive stressed that the bank activated its advanced security protocols and continued to operate without interruptions, although working in such conditions was very complicated. ‘Our team found the necessary resources to stop the cyberattack successfully,’ the banking executive explained.
READ THE STORY: Prensa Latina
Grand jury indicts Ukrainian for role in vast Raccoon Infostealer cybercrime operation
FROM THE MEDIA: The Justice Department on Tuesday unsealed charges against a Ukrainian national for his role in the Raccoon Infostealer malware-as-a-service operation, which U.S. law enforcement officials blamed for infecting millions of computers around the world to steal personal data. Raccoon Infostealer sold its malware on the for $75 per week or $200 per month, but reportedly claimed it shut down in March after one of its developers died in the Russian invasion of Ukraine, Bleeping Computer reported at the time.
READ THE STORY: Cyberscoop // FOX34 // ABCNEWS
Dirty bomb disinformation
FROM THE MEDIA: Russia has sought to evacuate civilians from Kherson as it braces for Ukraine's offensive in the south. Despite some signs of withdrawal from Kherson, the Telegraph and others report Ukraine's view that Russia intends to fight for the occupied city and province. The recapture of Kherson would effectively isolate Russian-occupied Crimea. The civilian evacuations are not necessarily a humanitarian gesture; many reports of the evacuations characterize them as forcible deportation.
READ THE STORY: The Cyberwire
Over 120 large cyber attacks targeted Iran’s infrastructure in 20 days: Senior cmdr
Analyst Notes: The successfulness maybe exaggerated and could be used as a means to measure effectiveness.
FROM THE MEDIA: Brigadier General Gholamreza Jalali said Tuesday that Iran has been witnessing the “heaviest” of cyber, media and ideological attacks, which “would have destroyed any other country,” adding that the people acted vigilantly and prevented the enemies from achieving their goals. “This level of cyber threats has never been posed to any other country,” said the official, adding that Iran managed to confront 90 percent of the attacks.
READ THE STORY: SCMAG
Microsoft: Vice Society targets schools with multiple ransomware families
FROM THE MEDIA: A threat group known as Vice Society has been switching ransomware payloads in attacks targeting the education sector across the United States and worldwide. While this isn't necessarily new information, since the group is known for using multiple ransomware strains in some attacks, Microsoft has also seen them use this tactic against organizations in the U.S. education sector between July and October 2022.
READ THE STORY: Bleeping Computer
Chinese Huawei ‘Spies’ Charged — FBI is Mad as Hell
FROM THE MEDIA: Two Chinese intelligence officers tried to bribe a U.S. law-enforcement official to obtain what they believed was inside information about the U.S. criminal case against Chinese telecommunications giant Huawei … prosecutors alleged. … Guochun He and Zheng Wang, were charged in a federal criminal complaint. … The two are described in the complaint as Chinese intelligence officers who are conducting foreign intelligence operations against the U.S. on behalf of the Chinese government.
READ THE STORY: Security Boulevard
Equifax's Lessons Are Still Relevant, 5 Years Later
FROM THE MEDIA: On the morning of Sept. 7, 2017, US credit bureau giant Equifax announced hackers had infiltrated its network and exfiltrated customer names, Social Security numbers, birthdates, and addresses. The news of the breach — which compromised the private records of 147.9 million Americans (almost 50% of the entire US population), 15.2 million Britons, and almost 19,000 Canadians — immediately created pandemonium across organizations, forcing many business leaders to reconsider their security postures. Much has changed over the past five years, but the lessons from the Equifax breach are still relevant for enterprises.
READ THE STORY: DarkReading
LV Ransomware Exploits ProxyShell in Attack on a Jordan-based Company
FROM THE MEDIA: The Trend Micro research team recently analyzed an infection related to the LV ransomware group, a ransomware as a service (RaaS) operation that has been active since late 2020, and is reportedly based on REvil (aka Sodinokibi). The exact nature of the relationship between the LV ransomware and REvil groups cannot be definitively established or verified — the LV ransomware’s developers do not appear to have had access to the Revil source code, and likely modified REvil binary script instead.
READ THE STORY: Trend Micro
Microsoft detects opportunistic ransomware campaigns impacting global education sector
FROM THE MEDIA: Microsoft has identified active ransomware and extortion campaigns by a threat actor it tracks as DEV-0832, also known as Vice Society. While the cybercriminal group's previous opportunistic attacks have affected various industries, the latest attacks between July and October 2022 have heavily impacted the education sector, particularly in the United States. In several cases, Microsoft assesses that DEV-0832 did not deploy ransomware, instead, the threat actors appeared to exfiltrate data and dwell within compromised networks.
READ THE STORY: Devdiscourse
Apple patches new iPhone zero-day
FROM THE MEDIA: Apple has released a series of security updates to its iOS 16.1 and iPadOS 16 mobile operating systems (OSes), targeting 20 newly discovered vulnerabilities, including one actively exploited zero-day. Tracked as CVE-2022-42827, and credited to an anonymous researcher, the vulnerability affects iPhone 8 and later, all models of iPad Pro, iPad Air 3rd generation and later, iPad 5th generation and later, and iPad Mini 5th generation and later. It is an out-of-bounds write issue by which an application may be able to execute arbitrary code with kernel privileges.
READ THE STORY: ComputerWeekly
How Teams of Volunteer Technologists Hunt Down Ransomware Gangs
FROM THE MEDIA: In an excerpt from their new book, The Ransomware Hunting Team: A Band of Misfits’ Improbable Crusade to Save the World From Cybercrime, writers Renee Dudley and Daniel Gold take readers inside the complex and mysterious world of the hacker underground. The book reveals the ins and outs of the modern ransomware industry, while also charting the tireless work of a team of volunteer technologists who have devoted their lives to thwarting the criminal scourge.
READ THE STORY: Gizmodo
Russian hackers say Japan hospital paid $30,000 in ransomware attack
FROM THE MEDIA: A Russia-based hacker group has claimed a Japanese hospital paid $30,000 to regain access to electronic medical records that were encrypted in a ransomware attack last October, causing major disruption to the medical institution's operations. The town of Tsurugi, Tokushima Prefecture, which runs the targeted Handa Hospital, has denied paying ransom money, and experts suspect that an IT firm involved in attempts to restore access to the records secretly reached a deal with the hackers.
READ THE STORY: Kyodo News
Feds Issue Cyber Advisory on Daixin Ransomware Hackers
FROM THE MEDIA: The Cybersecurity and Infrastructure Security Agency (CISA) along with the Federal Bureau of Investigation (FBI) and the Department of Health and Human Services (HHS) released a new Cybersecurity Advisory (CSA) on Oct. 21 warning about ransomware attacks by the Daixin Team hacking group. The advisory says the Daixin Team has been targeting U.S. healthcare organizations with extortion attempts via ransomware and tools, and says the group is linked to hackers operating within China.
READ THE STORY: MeriTalk
Wisconsin school district attacked by Snatch ransomware group
FROM THE MEDIA: The Snatch ransomware gang has claimed to be behind the ransomware attack against the Kenosha Unified School District in Wisconsin, which caters to almost 20,000 students, according to The Record, a news site by cybersecurity firm Recorded Future. No specifics regarding the amount of data or types of files stolen were detailed by the ransomware group. Kenosha Unified School District was impacted by the attack on Sept. 25, with officials noting that the school district has since restored systems it took down as a precaution, as well as sought assistance from law enforcement and a cybersecurity firm in investigating the incident.
READ THE STORY: SCMAG
Data hacked from Tata Power servers leaked on dark web
FROM THE MEDIA: Tata Power disclosed that its Information Technology infrastructure had been hit by a cyberattack and some of its systems were affected as a result of it. In a Bombay Stock Exchange filing, the Mumbai-headquartered company said all critical operational systems were functioning and it had “taken steps to retrieve and restore its systems.” On Tuesday, Hive claimed responsibility for the cyberattack and began to release the hacked data on their dark web forum.
READ THE STORY: Hindustan Times
Threat Groups Repurpose Banking Trojans into Backdoors
FROM THE MEDIA: Threat groups continue to recycle code from older tools into more generalized frameworks, a trend that will continue as the codebases incorporate more modularity, security experts said this week. In the latest example, the threat group behind Ursnif — aka Gozi — recently moved the tool away from a focus on financial services to more general backdoor capabilities, cybersecurity services firm Mandiant stated in an analysis. The new variant, which the company has dubbed LDR4, is likely intended to facilitate the spread of ransomware and the theft of data for extortion.
READ THE STORY: DarkReading
See Tickets discloses 2.5 years-long credit card theft breach
FROM THE MEDIA: Ticketing service provider 'See Tickets' has disclosed a data breach, informing customers that cybercriminals might have accessed their payment card details via a skimmer on its website. Skimmers are snippets of JavaScript code injected on order checkout pages to steal inputted payment card details from customers, in this case, people who bought a ticket to a live entertainment event. According to a data breach notification shared with the Montana Attorney General's office, See Tickets discovered the breach in April 2021, when they started an investigation with the help of a forensics firm.
READ THE STORY: Bleeping Computer
Remember the Equifax breach? You might have payout options in your email
FROM THE MEDIA: After years of waiting, millions of Americans will soon be seeing their payouts following a class-action lawsuit against Equifax. A deadline recently passed for changing the method of payout, but there’s still a way to get your money electronically. The 2017 Equifax breach saw hackers take roughly 147.9 million Americans‘ personal information, making it one of the largest data breaches in history.
READ THE STORY: News Channel 8
Commission Initiates Proceeding to Address Robotexting
FROM THE MEDIA: The Federal Communications Commission (“Commission”) is proposing to extend some of its call authentication and blocking requirements to text messaging. On September 27, the Commission released a Notice of Proposed Rulemaking (“NPRM”) seeking comment on a proposal that would require mobile providers to block illegal text messages and apply caller ID authentication technology to text messages.
READ THE STORY: The National Law Review
New government directives and persistent threats reinforce urgency of securing software
FROM THE MEDIA: More than a year after President Biden signed Executive Order (EO) 14028 on Improving the Nation’s Cybersecurity, standards and compliance expectations are coming into sharper focus. The National Institute of Standards and Technology (NIST), the Office of Budget and Management (OMB), and other U.S. government bodies have released a series of best practice guidance and directives that will accelerate software supply chain visibility and security.
READ THE STORY: Security Boulevard
China’s Race for Technological Dominance Could Raise Its Global Stature
FROM THE MEDIA: Recently, China convened its 20th Congress of the Chinese Communist Party, an event that features the CCPs to leadership with an intent to adjust its constitution as it lays forth a blueprint for the country’s policies for the next five years. Xi opened the Congress affirming the nation’s need to win the race for the development of “core technologies” with the objective of becoming self-reliant in strategic technologies. Perhaps most notable was his emphasis on innovation being focused on national strategic requirements – and therefore making it clear that China’s national security was directly tied to the development of advanced information technology.
READ THE STORY: OODALOOP
US unseals indictments of PRC intelligence officers
FROM THE MEDIA: The US Department of Justice yesterday afternoon held a press conference to announce the unsealing of three cases against thirteen Chinese nationals, including ten Chinese intelligence officers. The first involved charges against two Chinese intelligence officers who allegedly bribed a US citizen, an insider, to reveal sensitive and non-public information about the US prosecution of a Chinese telecommunications company. The Justice Department declined to name the Chinese company involved in the prosecution, but the Wall Street Journal reports that sources confirm that the company involved is Huawei. The second case involved the activities of a front Chinese academic organization.
READ THE STORY: The Cyberwire
Ukraine Seeks Billions in Funding As Needs Grow
FROM THE MEDIA: Ukrainian President Volodomyr Zelenskiy is appealing for at least $17 billion in urgent financing, though the request doesn’t even factor in widespread damage inflicted by Russia on its neighbor’s energy infrastructure. The EU is pressing ahead to deliver about a third of the country's funding requirements for next year, even as Berlin, which hosted the postwar reconstruction conference yesterday, is still dragging its feet over loans earmarked for this year.
READ THE STORY: Bloomberg
Cyber Crime The Dark Web Uncovered – Now available on Amazon
FROM THE MEDIA: The documentary, now available on Amazon, features Rene Miller of Ener Systems LLC, and other cybercrime experts from around the country. CEOs and business owners will benefit from this film as it reveals the insidious ways cybercriminals use the Dark Web to profit, such as ransomware, human trafficking, phishing, and hacktivism. Cyber Crime The Dark Web Uncovered reveals key strategies and ways to detect, deflect, and protect businesses from this growing threat.
READ THE STORY: Digital Journal
Items of interest
Perspectives for Influence Operations Investigators
FROM THE MEDIA: As public urgency swells around online influence operations, professionals from sectors including academia, private industry, and the nonprofit space have rushed to fill gaps in capacity. They bring with them assumptions and approaches from diverse fields like cybersecurity, counterextremism, and offline investigations. As a result, the space is bustling, but it lacks consistent, widely articulated standards and best practices to guide and evaluate its work.
In a 2020 community survey by the Partnership for Countering Influence Operations (PCIO), a third of respondents noted the lack of shared standards as an important concern. PCIO’s Influence Operations Researchers’ Guild exists in part to address this issue. Investigative standards serve a dual purpose.
READ THE STORY: Carnegie Endowment for International Peace
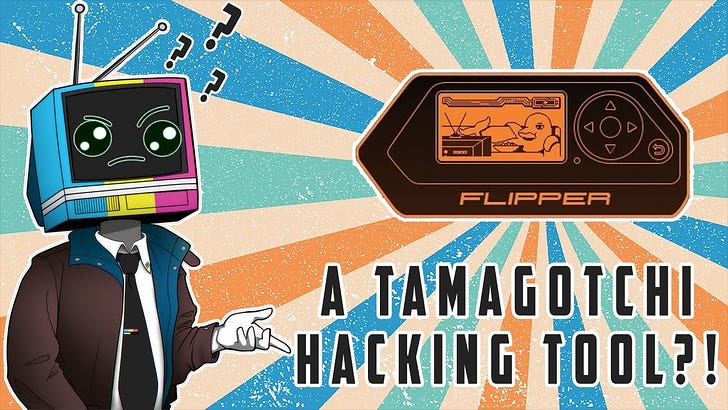
Tamagotchi Hacking Tool, Flipper Zero Unboxing and Review (Video)
FROM THE MEDIA: The Flipper Zero is a swiss army knife of hacking tools. This device has it all, Infrared, GPIO pins, RFID, NFC, IButton, Sub-GHZ, a Micro SD card slot, and an adorable dolphin pet!
Flipper Zero — Multi-Tool Device for Hackers in a Tamagotchi Body (Video)
FROM THE MEDIA: Flipper Zero is a portable multi-tool for pen-testers and geeks in a Tamagotchi body. It loves to hack digital stuff around such as radio protocols, access control systems, hardware and more. It's fully open source and customizable so you can extend it in whatever way you like.
These open source products are reviewed from analysts at InfoDom Securities and provide possible context about current media trends in regard to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not specifically endorse any third-party claims made in their original material or related links on their sites, and the opinions expressed by third parties are theirs alone. Contact InfoDom Securities at dominanceinformation@gmail.com