Monday, October 24, 2022 // (IG): BB // INTSUM // Coffee for Bob
Iran’s atomic energy agency claims that alleged state-sponsored hackers have compromised its email system
FROM THE MEDIA: Iran’s atomic energy agency revealed on Sunday that a nation-state actor had access to a subsidiary’s network and free access to its email system, the Associated Press reports. The Iranian government has yet to attribute the attack to a specific hacker group, which calls itself Black Reward announced the hack of the Atomic Energy Organization on Telegram and shared files of contracts, construction plans, and details about equipment at the Bushehr plant as proof of the intrusion.
READ THE STORY: Security Affairs // VOA // The Print
Unattributed RomCom Threat Actor Spoofing Popular Apps Now Hits Ukrainian Militaries
FROM THE MEDIA: The previously unknown RomCom RAT threat actor is now targeting Ukrainian military institutions. The same threat actor is known to deploy spoofed versions of popular software "Advanced IP Scanner." After being publicly exposed, it switched to another popular application called "PDF Filler." That indicates the group behind it is actively developing new capabilities. The initial "Advanced IP Scanner" campaign occurred on July 23, 2022. Once the victim installs a Trojanized bundle, it drops to the system RomCom RAT. On October 10, 2022, the threat actor improved evasion techniques by obfuscation of all strings, execution as a COM object, and others.
READ THE STORY: Blackberry
SideWinder APT Using New WarHawk Backdoor to Target Entities in Pakistan
FROM THE MEDIA: SideWinder, a prolific nation-state actor mainly known for targeting Pakistan military entities, compromised the official website of the National Electric Power Regulatory Authority (NEPRA) to deliver a tailored malware called WarHawk. "The newly discovered WarHawk backdoor contains various malicious modules that deliver Cobalt Strike, incorporating new TTPs such as KernelCallBackTable injection and Pakistan Standard Time zone check in order to ensure a victorious campaign," Zscaler ThreatLabz said.
READ THE STORY: THN
Typosquatting campaign delivers Windows, Android malware
FROM THE MEDIA: A massive typosquatting campaign using various fraudulent domains to infect unsuspecting users' Windows and Android devices with malware has recently been found. Typosquatting, also known as URL hijacking, is a form of cyberattack wherein threat actors trick unsuspecting users into visiting a fraudulent website by registering a domain name similar to the ones used by genuine brands. Typically, users end up on these malicious websites when they mistype the domain of the website they want to visit. They can also be lured to these websites via phishing emails, SMS messages, direct messages, and malicious social media and forum posts.
READ THE STORY: Neowin
CISA Warns of Daixin Team Hackers Targeting Health Organizations With Ransomware
FROM THE MEDIA: U.S. cybersecurity and intelligence agencies have published a joint advisory warning of attacks perpetrated by a cybercrime gang known as the Daixin Team primarily targeting the healthcare sector in the country. "The Daixin Team is a ransomware and data extortion group that has targeted the HPH Sector with ransomware and data extortion operations since at least June 2022," the agencies said. The alert was published Friday by the Federal Bureau of Investigation (FBI), Cybersecurity and Infrastructure Security Agency (CISA), and the Department of Health and Human Services (HHS).
READ THE STORY: THN
SpaceX Starlink Kits are Being Smuggled into Iran: Report
FROM THE MEDIA: With SpaceX having activated Starlink service in Iran last month, activists have started smuggling Starlink user terminals into the country as the conflict between Iran’s theocratic government and its people rages on — reports TIME. Starlink is a high-speed internet service that is powered by a constellation of satellites in low Earth orbit and doesn’t need terrestrial connections to function. A Starlink terminal on the ground connects to and communicates with orbiting satellites, providing (impressively fast) internet access.
READ THE STORY: Tesla North
Iran's assistance to Russian war effort could make the country an enemy combatant
FROM THE MEDIA: Continued assistance to Russia in the form of drones and weapons could place Iran at risk of being considered an enemy combatant in Ukraine, a status that opens the country up to sharing responsibility for war crimes. "With the potential for missiles to be transferred by Iran to Ukraine, one has to begin to consider the Islamic Republic as a combatant on the side of Russia in the Ukraine war," Foundation for Defense of Democracies senior fellow Behnam Ben Taleblu told Fox News Digital.
READ THE STORY: Yahoo News
Could you not? BlackByte ransomware slinger twists the knife with data stealer
FROM THE MEDIA: At least one affiliate of the high-profile ransomware-as-a-service (RaaS) group BlackByte is using a custom tool to exfiltrate files from a victim's network, a key step in the fast-growing business of double-extortion. The exfiltration tool, dubbed Exbyte, is written in Go for Windows computers, and is designed to upload files to the Mega cloud storage service, according to researchers in Symantec's Threat Hunter Team this month. Exbyte lets the affiliate speedily grab a victim's sensitive internal documents and stash them out of sight, yet another indication of BlackByte's rising status in the always-dynamic ransomware world.
READ THE STORY: The Register
AI-based Model to Predict Extreme Wildfire Danger
FROM THE MEDIA: Researchers at Gwangju Institute of Science and Technology have developed an AI-based, hybrid system to predict wildfire danger. This brand-new, innovative forecast system combines deep learning algorithms with the currently available forecast models for accurately detecting wildfire conditions and enhanced coverage of existing models. No doubt, raging wildfires across the world are causing substantial economic damage. Also concerning is the ever-increasing number of fatalities caused by wildfires. If there’s a system that can predict this catastrophic event, it can substantially decrease damage since the available forecast systems aren’t as accurate or effective.
READ THE STORY: HackRead
The Evolution of Cyber Insurance Policies: The Unintended Consequences of Ransomware
FROM THE MEDIA: The rise of ransomware in the last couple of years has been well reported as it has crippled organizations worldwide. The uptick in ransomware has led victim organizations to look for the cheapest and most legally compliant way out in the face of an attack. As such, many organizations have prioritized adopting cyber insurance programs. Whilst cyber insurance has developed in tandem with cyber risks, staying ahead of these risks and being able to predict outcomes has proved a difficult task and a unique challenge for underwriters and brokers alike.
READ THE STORY: TechNative
With All Eyes on Russia, China Continues to Strike
FROM THE MEDIA: For the last year or so, the cybersecurity world has prepared itself for Russian strikes intended to cripple its victims. Disruptions to the global food supply, the energy sector, and other critical infrastructures have all been attributed to nation-state-grade attacks stemming from the Russian bear. In the world of cyber threats, Russia is the alpha, beating its chest and going after targets with ransomware and malware. This perception has intensified since the Ukrainian invasion. Cybersecurity experts have cautioned against future attacks targeting the West’s critical infrastructure and financial sectors.
READ THE STORY: Security Boulevard
Medibank hack started with theft of staff member’s credentials, investigation suggests
FROM THE MEDIA: The Medibank hack began with the theft of the credentials of a staff member who had high-level access within the organization, which were then sold on a Russian-language cybercrime forum, according to a source close to the company investigation. The Australian health insurer told its customers on 13 October it had taken two systems offline as a result of a “cyber incident”. It later reported it had been contacted by hackers over 200GB of customer data allegedly stolen from the Medibank systems.
READ THE STORY: The Guardian
Toyota: Data breach involving source code hosted on GitHub
FROM THE MEDIA: The Toyota Motor Corporation is warning that customers’ personal information could have been exposed. This occurred after an access key was publicly available on GitHub for almost five years. This relates to the official connectivity app used by vehicle owners that enables owners of Toyota cars to link their smartphone with the vehicle’s infotainment system. Looking into this manufacturing related data issue for Digital Journal is Jason Kent, Hacker in Residence at Cequence Security.
READ THE STORY: Digital Journal
Most data breaches caused by insiders in India, shows report
FROM THE MEDIA: In cyber security terms, an insider threat or insider refers to a malicious threat to an organization through people within the company. These insiders may include existing or former employees who are familiar with the company’s security practices, data and computer systems. Insiders may be most responsible for data breaches from companies in India, a recent research report has suggested after studying listings on the dark web, where underground market places exist for hacked or leaked sensitive personal data that people share with websites.
READ THE STORY: HT
Blazing South Korean datacenter operator raided by cops, blames its own batteries
FROM THE MEDIA: South Korean police have reportedly raided the premises of SK C&C, the operator of the datacenter that caught fire on the weekend of October 15 and disrupted the operations of local web giants Naver and Kakao. Local media report that local police visited the company late last week, inspected the site of the fire, and left with company documents. SK C&C, meanwhile, has apologized for the incident and admitted that uninterruptible power supplies appear to have caught fire. Which is embarrassing, because parent company SK Group is thought to be the manufacturer of the batteries.
READ THE STORY: The Register
Russians Against Putin: NRA Claims Massive Hack of Russian Government Contractors’ Computers
FROM THE MEDIA: In perhaps one of the largest IT-security breaches in Russian history, Kyiv Post was contacted on Oct. 17 by hackers who indicated that they were supporters of the Russian NRA. As Kyiv Post has previously reported, the NRA is an organization of Russian opposition members seeking the overthrow of the Putin regime, including via the use of violent means. The NRA-affiliates told Kyiv Post that they had hacked several major Russian technology firms that are currently providing services critical to the Russian Government’s national security.
READ THE STORY: HSToday
Researchers discovered thousands of GitHub repositories that offer fake proof-of-concept (PoC) exploits for various flaws used to distribute malware
FROM THE MEDIA: A team of researchers at the Leiden Institute of Advanced Computer Science (Soufian El Yadmani, Robin The, Olga Gadyatskaya) discovered thousands of repositories on GitHub that offer fake proof-of-concept (PoC) exploits for multiple vulnerabilities. The experts analyzed PoCs shared on GitHub for known vulnerabilities discovered in 2017-2021, some of these repositories were used by threat actors to spread malware. The experts pointed out that public code repositories do not provide any guarantees that any given PoC comes from a trustworthy source.
READ THE STORY: Security Affairs
Social engineering attacks anybody could fall victim to
FROM THE MEDIA: Social engineering – also known as human hacking – is an expression that encompasses a number of methods and vectors attackers use to manipulate targets into giving away or providing access to sensitive information, or generally performing actions that are against their best interest. To effectively perform social engineering attacks, attackers exploit vulnerabilities in how humans react to specific situations.
READ THE STORY: HelpNetSecurity
Telegram hackers stealing accounts with fake ‘gift’
FROM THE MEDIA: Telegram hackers are tricking the social media’s users in the Kingdom into handing over account details through the “Gift 74/100 Free Premium” link which then exposes other personnel details to the fraudsters especially access to financial information. Department of Information and Communications Technology Security director Ou Phannarith said yesterday that hackers recently developed phony links with an animated Gif that appears as an original Telegram message but is used to steal Telegram accounts.
READ THE STORY: Khmer Times
Singapore sales portal hacked, leaving two million customers exposed to cyber fraud
FROM THE MEDIA: The breach was disclosed by the company to a local media news site TODAY on October 21. According to the news outlet, Carousell attributed the breach to the previous week, leaving 1.95 million customers’ mobile phone numbers and email addresses exposed. However, a post on hacker platform BreachForums dated October 12, two days before Carousell says the breach took place, appears to claim that the company was infiltrated as far back as May. The hacker post also says 2GB of information was accessed, with a taster file of user data uploaded to the forum for potential buyers, who were quoted the data haul at a rate of “$1,000/5 copies.”
READ THE STORY: Cybernews
Byting back: The EU’s digital alliance with Latin America and the Caribbean
FROM THE MEDIA: For much of the past decade, the European Union has done little to halt the rise of Chinese and Russian influence in Latin America and the Caribbean. The value of the region’s trade with the EU grew from €185.5 billion in 2008 to €225.4 billion in 2018, but that with China increased tenfold in the same period. Twenty-one countries in the region are now members of China’s Belt and Road Initiative.
READ THE STORY: ECFR
United States initiative checkmates China in Pacific Islands to open the door for a Chinese naval base
FROM THE MEDIA: After the March 2022 news leak that Beijing was working on a secret deal with the Solomon Islands to open the door for a Chinese naval base, American initiatives in the Pacific islands have checkmated China. The Americans approached the Pacific islanders without any discrimination and were also very accommodating of their concerns. This starkly contrasted with Beijing's attitude, which was of a big brother and vindictive, to say the least, reported the policy research group Poreg.
READ THE STORY: The Sentinel
Researchers Find New Use For Starlink But Elon Musk May Not Be Pleased
FROM THE MEDIA: Elon Musk's Starlink is an incredibly ambitious project; it aims to bring high-speed internet to every corner of the globe through its web of satellites operating in low-Earth orbit. This is good news for people in rural areas or developing countries, where installing the infrastructure high-speed fiber internet requires may be cost-prohibitive. As recently as 2017, over 20 million Americans lacked access to high-speed internet — which is around 30% of the country's rural population (via Inc). Those users either had to make do with an incredibly slow dial-up connection or just go without.
READ THE STORY: Slashgear
Iran to Supply Domestically-Made Gas Turbines to Russia
FROM THE MEDIA: Iran is currently capable of producing "85% of the equipment needed in the gas business" on its own, Reza Noushadi told the Iranian oil ministry's Shana news agency on Sunday. Iran was able to sign the contract with Moscow because to this ability, he continued, but did not reveal exactly when the transaction was made or when the turbines will arrive in Russia. Russian officials have so far not commented on Noushadi’s statements. The development comes as the sanctions policies of the US and its allies have hit industry ties between Russia and its Western equipment suppliers, RT reports.
READ THE STORY: Tasnim News Agency
Russian-installed Kherson authorities form militia
FROM THE MEDIA: The Russian invasion of Ukraine that began on Feb. 24 continues, with casualties rising on both sides. Russian President Vladimir Putin has announced Russia's annexation of four partially occupied Ukrainian regions following referendums that Western nations called a "sham." Meanwhile, Ukrainian forces are mounting a strong counteroffensive against Russian troops, reclaiming territory lost when Moscow launched its invasion. Ukraine has managed to withstand the Russian onslaught with the help of Western military aid, but President Volodymyr Zelenskyy regularly calls on the world to do more. For all our coverage, visit our Ukraine war page.
READ THE STORY: Nikkei Asia
Russian media, officials spreading disinformation about Ukraine's plans to use 'dirty bomb'
FROM THE MEDIA: In Russia, propagandists and representatives of the authorities are spreading disinformation about Ukraine allegedly preparing to detonate a "dirty bomb." That's according to Radio Free Europe/Radio Liberty, Ukrinform reports. In particular, Russia's Minister of Defense, Sergei Shoigu, held phone calls with Defense Ministers Sebastien Lecornu of France, Hulusi Akar of Turkey, and Ben Wallace of Britain. According to Russia's Ministry of Defense, in all three conversations, Shoigu "expressed concern" in connection with the alleged possible use of a "dirty bomb" by Ukraine.
READ THE STORY: UKRINFORM
Items of interest
Proxy Wars and 21st Century Merchants Of Death
FROM THE MEDIA: The conflict in Ukraine is, by any definition, a “proxy war.” But it is being fought entirely differently by the US, the West and Russia. The US and the West are waging a traditional proxy war that FDR used to aid Great Britain persevere against Nazi Germany prior to Pearl Harbor and the CIA in Afghanistan after the 1979 Soviet invasion. Ultimately, the Afghan Mujahedin were able to force the Soviets to withdraw using the weaponry supplied by the US, particularly Stinger Missiles.
Ukraine is being supplied with the military wherewithal and support to defend itself against Russia. Whether enough weaponry to eject Russia from all the occupied territories will be provided is unclear. The expectation is that Russian forces will be so badly bloodied that at some stage that war will end to Ukraine’s advantage. But expectations are not always met.
READ THE STORY: Daily Times (PK)
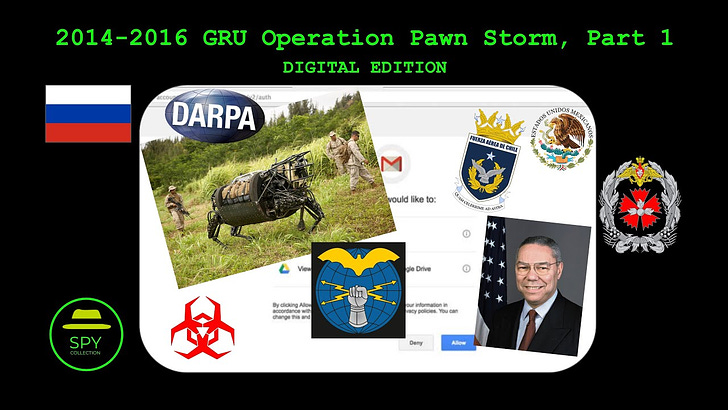
Russian GRU 2014-2016 Cyber-Espionage Operation Pawn Storm (Video)
FROM THE MEDIA: Throughout 2014-2016 the Military Unit 26165, also known as 85th Main Special Service Center (GTsSS), of the Russian GRU conducted a very high amount of cyber-espionage operations against a wide variety of targets, ranging from governments and military entities, to private companies and individuals of interest. This part 1 presents a handful of those cases from a historical context to demonstrate the modern history of cyber-enabled espionage operations.
Russian GRU 2014-2016 Cyber-Espionage Operation Pawn Storm, Part 2 (Video)
FROM THE MEDIA: Throughout 2014-2016 the Military Unit 26165, also known as 85th Main Special Service Centre (GTsSS), of the Russian #GRU conducted a very high amount of cyber-espionage operations against a wide variety of targets, ranging from governments and military entities, to private companies and individuals of interest. This part 2 presents five (5) of those cases from a historical context to demonstrate the modern history of cyber-enabled espionage operations.
These open source products are reviewed from analysts at InfoDom Securities and provide possible context about current media trends in regard to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not specifically endorse any third-party claims made in their original material or related links on their sites, and the opinions expressed by third parties are theirs alone. Contact InfoDom Securities at dominanceinformation@gmail.com