Wednesday, Sept 28, 2022 // (IG): BB // Sponsor: Buy me a whiskey
Chilean Court System Hit With Ransomware Attack
FROM THE MEDIA: The event is the latest cyber disruption affecting the South American country. The nation’s consumer protection agency was hit by a ransomware attack that started on Aug. 25 (see: Chile Consumer Protection Agency Hit by Ransomware Attack) and just days ago, hundreds of thousands of emails hacked from the military’s Joint Chiefs of Staff were published online. The judicial system on Monday attributed the spread of the Cryptolocker Trojan inside its network to a phishing email opened on Sunday night. It affected computers operating Windows 7 and loaded with McAfee antivirus, reaching just 1% of court system computers, said court administration official Zvonimir Koporcic. “We are changing the antivirus,” he said.
READ THE STORY: SN
Ransomware and the Severe Impact on K-12 Public Schools
FROM THE MEDIA: Similar to most industries during the pandemic, K-12 public schools have been heavily targeted by threat actors with the shift to a remote operating environment. K-12 public schools are a $760 billion sector that serves more than 50 million students at over 100,000 schools across the United States. School districts manage a wide set of IT infrastructure, software, and associated users, including students, faculty, and administration. Unfortunately, most do not have a dedicated cybersecurity team to handle security issues.
READ THE STORY: Security Boulevard
Disinformation is a scourge on public discourse
FROM THE MEDIA: GENEVA (Callaway Climate Insights) — The digital age has ushered in an era of unprecedented connectivity, allowing people across the world to share ideas and opinions in almost real time. It has also been characterized by the spread of disinformation. This is clear when examining nearly all the major issues facing the world today. For instance, the rise of the Internet and digital technologies brought the promise of greater democratization by providing an unprecedented ability to share information. Today’s reality, however, more resembles the digital dystopia that the World Economic Forum’s Global Risks Report warned of nearly a decade ago. In many countries, online disinformation purposefully created and curated abroad is circulating freely, undermining those countries’ political stability.
READ THE STORY: SN
Metador, a never-before-seen APT targeted ISPs for about 2 years
FROM THE MEDIA: SentinelLabs researchers uncovered a never-before-seen threat actor, tracked as Metador, that primarily targets telecommunications, internet service providers, and universities in several countries in the Middle East and Africa. The experts pointed out that the attack chains employed by the threat actors are designed to bypass native security solutions while deploying malware platforms directly into memory. The attackers are highly aware of operations security, they are able to manage carefully segmented infrastructure per victim, and were observed quickly deploying intricate countermeasures in the presence of security solutions.
READ THE STORY: SN
Turnabout is Fair Play? LockBit Ransomware Builder Leaked to Public by “Disgruntled Developer”
FROM THE MEDIA: LockBit has emerged as the biggest player in the “ransomware as a service” (RaaS) market in the past year. But the group may now be on the ropes as its newly revamped LockBit Ransomware Builder, the tool used to both build ransomware executables and decrypt locked files, is now available to the public via what the group claims is a “disgruntled developer.” LockBit ransomware will undoubtedly be copied and used by other threat actors in the near term, putting the group’s business at risk. But the leak of the ransomware builder also gives security researchers valuable insights into bolstering the ability of cyber defenses to detect it and into decrypting locked files.
READ THE STORY: CPO
Hackers super-charged by malware, crypto
FROM THE MEDIA: Number-crunchers are urging the federal government, businesses and insurers to fix the gaps in cyber protection that are costing the Australian economy billions of dollars. Risk experts at the Actuaries Institute on Wednesday released research that showed the vulnerability of organizations, from small firms to large corporates. “Sitting back and doing nothing shouldn’t be an option when cyber attacks cost the Australian economy $33 billion last financial year,” institute president Annette King said. The report’s lead author Win-Li Toh found only one in five (20 per cent) of small to medium enterprises have cyber insurance, compared with up to 70 per cent for larger organizations.
READ THE STORY: MichaelWest Media
It’s time to prepare for the rise of hacktivism (and its side effects)
FROM THE MEDIA: In this new era of cyber warfare, “knowing thy enemy” is more complicated than ever before. While the private sector continues to experience a cyber skills gap characterized by a lack of specialized talent, the barrier to entry for cybercriminals and attackers is at an all-time low. As geopolitical tensions play out in cyberspace, it can be impossible to distinguish between nation-state-sanctioned actors and non-sponsored criminals.
READ THE STORY: SEC MAG
China Claims: US, the largest disinformation propagator, constantly labels other countries
FROM THE MEDIA: What is particularly ironic is that the US, being the largest disinformation propagator, has constantly labeled other countries and slung mud at them. The US is the one who has created a colossal number of sham accounts, yet it keeps asking social media platforms to remove the accounts of Chinese users. The US is the one who has manipulated public opinion, yet it keeps labeling Chinese media outlets as “state-affiliated” accounts. The US is the one who has applied a gloomy filter to paint China in a negative light, yet it keeps accusing China of turning public sentiment against the US.
READ THE STORY: SN
Browser-based HEAT attacks putting CISOs on the hot seat
FROM THE MEDIA: As employee usage of SaaS applications and other cloud-based services rapidly explode, the web browser has become an increasingly popular point of entry for attackers looking to secretly breach an endpoint before ultimately moving laterally into the network. Highly Evasive Adaptive Threats, or HEAT attacks, exploit browsers — leveraging their tools and features to circumvent traditional security measures (e.g. static analysis, web gateways, sandboxes and filtering) and then compromise credentials or deliver ransomware and other malicious programs. At an InfoSec World conference session in Orlando on Monday, Niko Papez, senior manager of cybersecurity at Menlo Security, warned attendees about the growing danger surrounding these campaigns.
READ THE STORY: SCMAG
Australia asks FBI to help ID source of giant data
FROM THE MEDIA: Attorney general Mark Dreyfus yesterday revealed the FBI was asked to help identify the entities involved in the attack, which saw Optus leak data describing over ten million account holders. Data suspected to have been accessed included drivers license details, passport numbers, email addresses and phone numbers. Optus, owned by Singaporean mega-telco Singtel, disclosed the breach last Thursday.
READ THE STORY: SN
American Airlines Data Breach Linked to a Phishing Campaign Exposed Sensitive Customer and Employee Personal Information
FROM THE MEDIA: Hackers gained access to sensitive customer and employee personal information after compromising American Airlines in a data breach attributed to a phishing campaign. The company filed a data breach notification letter with Montana’s State Attorney General’s Office on September 16, disclosing that the breach was discovered in July, approximately two months earlier. American Airlines also notified customers, adding that only a small number was affected and the data had not been misused.
READ THE STORY: CPO
Trafficking Data: China’s Pursuit of Digital Sovereignty
FROM THE MEDIA: The Diplomat author Mercy Kuo regularly engages subject-matter experts, policy practitioners, and strategic thinkers across the globe for their diverse insights into U.S. Asia policy. This conversation with Dr. Aynne Kokas – associate professor of Media Studies at the University of Virginia; C.K. Yen Chair at the Miller Center for Public Affairs, and author of the forthcoming book “Trafficking Data: How China is Winning the Battle for Digital Sovereignty” (Oxford, November 2022) – is the 337th in “The Trans-Pacific View Insight Series.” Explain China’s politics of data governance and pursuit of cyber sovereignty.
READ THE STORY: SN
Agent Tesla RAT Delivered by Quantum Builder With New TTPs
FROM THE MEDIA: Zscaler ThreatLabz has observed a campaign that delivers Agent Tesla, a .NET based keylogger and remote access trojan (RAT) active since 2014, using a builder named “Quantum Builder” sold on the dark web. This campaign features enhancements and a shift toward LNK (Windows shortcut) files when compared to similar attacks in the past. Quantum Builder (aka “Quantum Lnk Builder”) is used to create malicious shortcut files. It has been linked to the Lazarus Group APT due to shared TTPs and source code overlaps, but we cannot confidently attribute this campaign to any specific threat actor. In this campaign, threat actor use Quantum Builder to generate malicious LNK, HTA, and PowerShell payloads which then deliver Agent Tesla on the targeted machines.
READ THE STORY: Security Boulevard
Fast Company shuts website after hack sends 'obscene' Apple News notifications
FROM THE MEDIA: U.S. business and media publication Fast Company said it shut down its website on Tuesday evening after the site was hacked and sent "obscene and racist" notifications to Apple users via the iPhone maker's Apple News service. News publishers using the Apple News aggregation app can connect their digital publishing tools to Apple News to send push notifications to Apple customers who subscribe to the publisher's channel. Fast Company said hackers broke into those publishing tools. Hackers sent two "obscene and racist push notifications" about a minute apart, Fast Company said in a tweet, adding it had suspended the Apple News feed until the situation was resolved.
READ THE STORY: Reuters
An Early History of Politically Motivated Hacking
FROM THE MEDIA: Years ago there was a “rise of hacktivism” paper at Georgetown, but it’s a PDF and mashes a lot of things together with no references. One of the curious bits in documenting these is the lack of any agreement on terminology, such as “patriot” hacking. Some say it’s defending one’s own country, yet of course that’s complicated. For example is a kid living in Holland with Russian parents who are from Iraq… going to identify along one or more of those lines?
READ THE STORY: Security Boulevard
Report: Russia Aims Iranian-Made Drones at Jews in Uman
FROM THE MEDIA: While thousands of Jews from across the world, and notably from Israel, marked Rosh Hashanah in Uman, media outlets in Ukraine reported on Tuesday that Russian forces deliberately launched at least 10 Iranian suicide drones of the Shahad-136 model over the city. According to the report, during the last few days, the military forces of Ukraine shot down more than ten drones, some of which were launched from the territory of the Crimean Peninsula and aimed at Uman. According to the assessment, Russia wanted to focus on Jewish religious sites with a large audience.
READ THE STORY: SN
Odesa: SSU dismantles criminal group of sanctioned ‘thief in law’ Antimos
FROM THE MEDIA: The SSU continues to fight against international organized crime, which is trying to infiltrate the ranks of Ukrainian law enforcement agencies. As a result of a special operation in Odesa, the SSU neutralized a powerful criminal group of the so-called Sukhumi-Kutaisi clan. Among the detained is a current employee of a law enforcement agency. The activities of the entire gang were coordinated by an influential criminal, ‘thief in law’ Antimos.
READ THE STORY: SSU
Indonesian activists deplore latest cyberattack as ‘assault on press freedom’
FROM THE MEDIA: Advocates have deplored a series of wide-ranging and coordinated cyberattacks against journalists and employees of the media company Narasi and have urged the police to act immediately. The attacks happened over the weekend against Narasi, which has reinforced its criticism of the government recently. Speaking at a virtual press conference held by the Alliance of Independent Journalists (AJI) on Monday, Narasi’s head of newsroom Laban Laisila said the attacks aimed to take control of the Telegram, Instagram, Facebook and Twitter accounts of its employees.
READ THE STORY: ANN
Lazarus Hacker Group Lures in Targets with Fake Job Offers
FROM THE MEDIA: A group of hackers based in North Korea called Lazarus has been using Windows and macOS malware to target unsuspecting victims through the Internet. The hacker group has been associated with other attacks. Lately, they have been targeting developers and artists in the crypto space. The Lazarus hacking group has been running a campaign called "Operation In(ter)ception" since 2020. Other than their previous attacks, they have their eyes set on Crypto.com- one of the world's leading cryptocurrency exchange platforms. Their goal is likely to steal digital assets and cryptocurrency.
READ THE STORY: iTECHPOST
Cyber Warfare Rife In Ukraine, But Impact Stays In Shadows
FROM THE MEDIA: Hackings, network sabotage and other cyber warfare campaigns are being intensely deployed by both sides as Russia's invasion of Ukraine grinds on, though the covert operations have not proved decisive on the battlefield -- at least so far. Western allies initially feared a tsunami of cyberattacks against Ukraine's military command and critical infrastructure, hindering its ability to resist the Russian forces pouring across its borders.
READ THE STORY: Barrons
Turkish Bayraktar vs Iran’s Suicide UAVs
FROM THE MEDIA: Iran appears to be transferring its armored vehicles to the border of Azerbaijan after new clashes erupted between Azerbaijani and Armenian troops on September 13 that claimed the lives of over 100 soldiers. The skirmish is the deadliest between the two countries since the Nagorno-Karabakh conflict in 2020. Videos show a column of armored vehicles reportedly belonging to Iran’s Revolutionary Guard Corps (IRGC) moving towards the Azerbaijani border. As per unconfirmed reports citing eyewitness accounts from the western part of Iran, the armored vehicles included tanks, armored combat vehicles, and large-caliber artillery. Apart from that, Iran’s drones are known to fly regularly in the area of the Azerbaijani-Iranian border.
READ THE STORY: SN
Is Anonymous’ cyber attack on Iran ‘hacktivism’ or a nuisance?
FROM THE MEDIA: The death of a 22-year-old woman, Mahsa Amini, has led to 11 days of unrest and 75 deaths, resulting in the largest defiance of the Islamic republic. The incident has opened a broader discussion about human rights worldwide, primarily considering women's status as second-class citizens. In response to heavy criticism, Iran has officially summoned British and Norwegian ambassadors to inquire regarding their "interventionist stance" on Iran's internal affairs.
READ THE STORY: The Post
Kaspersky uncovers new malicious malware NullMixer
FROM THE MEDIA: Kaspersky researchers have uncovered a new security threat, NullMixer, a malware stealing users credentials, address, credit card data, cryptocurrencies, and even Facebook and Amazon accounts. Trying to download cracked software from third-party sites, more than 47,500 users were attacked with NullMixer, able to spy on users, capturing any information they're entering on the keyboard, Kaspersky researchers discovered. NullMixer is actively distributed by cyber criminals via websites offering crack, keygen and activators for downloading software illegally. Such untrustworthy pages always pose a threat for users as instead of providing proper software, they infect victims' devices with malware, the researchers state.
READ THE STORY: Security Brief
Drone technology used to inspect Scotland’s sewers
FROM THE MEDIA: Scottish Water is pioneering the use of drones to inspect Scotland's sewers. The utility company said the technology replaces the need for workers to carry out inspections, will provide more accurate readings about conditions and will help reduce emissions. It carried out the UK's first drone inspection at a sewer on Bath Street, Glasgow in July. Similar inspections are expected to be rolled out in Glasgow, Edinburgh, Aberdeen and some rural areas.
READ THE STORY: BBC
Leaks in Undersea Gas Pipelines After Explosions Point to Sabotage, Officials Say
FROM THE MEDIA: Explosions under the Baltic Sea and the rupture of major natural gas pipelines from Russia to Germany appeared to be a deliberate attack, officials across Europe said on Tuesday, deepening uncertainty about European energy security amid soaring prices and fears of running short of fuel over the winter. Three separate leaks erupted from the Nord Stream 1 and 2 pipelines, which were already caught up in the conflict over Russia’s invasion of Ukraine, sending swirling streams of methane to the surface of waters off Denmark and Sweden. Top Polish and Ukrainian leaders blamed Moscow, while Russian state media suggested U.S. or Ukrainian involvement.
READ THE STORY: NY TIMES
Would-be Software Pirates Served Malware Through 'NullMixer'
FROM THE MEDIA: Would-be users of pirated software on Windows computers have a decent chance of downloading a slew of viruses courtesy of a malware dropper Kaspersky is calling NullMixer. Researchers with the Russian cybersecurity company say the company has blocked Nullmixer downloads from reaching nearly 48,000 users worldwide. Industry association BSA-The Software Alliance in 2018 estimated that unlicensed software accounts for 37 percent of software installed on personal computers, costing industry tens of billions of dollars in lost revenue. Users looking for a cheap shortcut could likewise get shortchanged since hackers have long salted with malware any software putatively meant for cracking licensed applications.
READ THE STORY: BankInfoSecurity
Tik-Tok and US Government Agree Upon A Deal On Data Security
FROM THE MEDIA: Tik-Tok considered to be one of the most popular apps in the world has the highest number of users in the United States of America has decided to come into an agreement with the country, in which the social media platform agreed to bring changes in its data security system. Reports bring out that the changes being brought into effect would take place without Tik-Tok’s parent firm ByteDance requiring to sell it. Reportedly, Tik-Tok’s parent company ByteDance had been asked by the US to strip the company of its powers since the year 2020 in the US.
READ THE STORY: TechStory
UN elections set to influence how nations shape the internet
FROM THE MEDIA: Elections to run technical UN bodies rarely garner much public attention. But when delegates from 193 countries choose the next secretary-general of the International Telecommunication Union in Bucharest’s Palace of Parliament on Thursday, there will be much more at stake than the symbolic figurehead of an arcane institution. Experts say the outcome of the election — which pits an American against a Russian — is likely to shape the extent to which nation states will be able to govern the internet.
READ THE STORY: FT
Keys to thwarting insider threats
FROM THE MEDIA: Asia Pacific (APAC) countries spent an average of US$11.9 million ($17 million) to deal with an insider threat incident this year, according to the 2022 Ponemon Cost of Insider Threats report. Common insider threats include employee or contractor negligence, malicious insiders and credential theft. Shawn Thompson, senior manager for global insider risk services at the cybersecurity firm Mandiant, tells DigitalEdge more about insider threats and how APAC organizations can deal with them effectively.
READ THE STORY: The Edge
Russia's 'most-complex' disinformation push since Ukraine invasion taken down, Facebook owner says
FROM THE MEDIA: Russia's largest and most complex propaganda push since the war in Ukraine has been taken down, according to the owner of Facebook and Instagram. The sprawling disinformation network used hundreds of fake social media accounts and sham news websites to spread Kremlin spin about Ukraine, Meta said. It involved more than 60 websites designed to mimic legitimate news sites including The Guardian in the UK and Germany's Der Spiegel, which linked to disinformation about the war, and 1,600 fake Facebook accounts.
READ THE STORY: ABC AU
Tracking Chinese Online Influence in Central and Eastern Europe
FROM THE MEDIA: For over a decade, China has been working to build influence beyond its own borders. One region of particular concern for Beijing is Central and Eastern Europe. Through economic investment, diplomatic relationships, cultural bridge-building, and in particular disinformation and public diplomacy campaigns, Beijing has attempted to persuade and coerce governments, organizations, and media throughout the region. If the Chinese Communist Party (CCP) is able to build up its influence successfully, it would allow China to have an increasingly powerful input into policymaking across European and regional institutions via member states.
READ THE STORY: CEPA
Items of interest
How Falun Gong-backed media pushed Xi coup rumors' around the world. And Indians bought it
FROM THE MEDIA: The rumours of a coup in Zhongnanhai and Xi Jinping’s ‘house arrest’ dominated all trends on Twitter from 24 to 26 September. But at the heart of the rumours is a sprawling media ecosystem backed by the Chinese religious movement ‘Falun Gong’. Falun Gong considers the whole of the Chinese Communist Party a mortal enemy and evil. The Epoch Times and the New Tang Dynasty TV are part of the Falun Gong-backed media ecosystem, which provides news to the overseas Chinese community in the US, Canada, the UK, Australia, Europe, and Singapore.
READ THE STORY: The Print
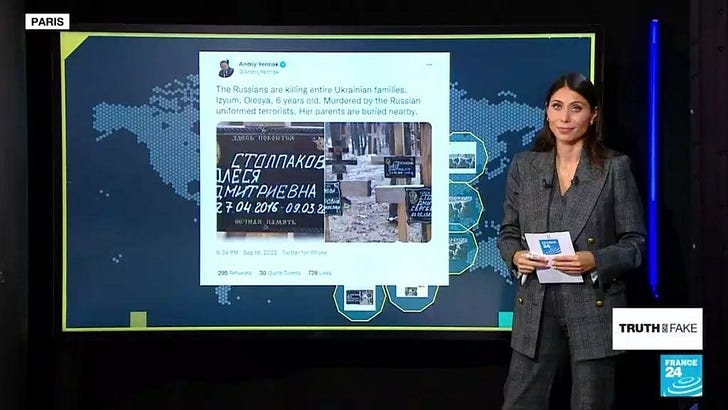
Debunking claims that Izium mass graves are Ukrainian propaganda (Video)
FROM THE MEDIA: Pro-Russian accounts on social media are falsely claiming that certain civilian graves found in Izium date from before the Russian occupation. In this edition of Truth or Fake, we debunk claims that the graves were staged by Ukrainian authorities.
What is propaganda? (Video)
FROM THE MEDIA: Propaganda is ubiquitous, and everyone uses propaganda. It's a kind of communication that makes a case for a goal, bypassing reason. Propaganda is a method to urge you to mobilize towards something while concealing from you things that you reasonably should think, should consider.
These open source products are reviewed from analysts at InfoDom Securities and provide possible context about current media trends in regard to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not specifically endorse any third-party claims made in their original material or related links on their sites, and the opinions expressed by third parties are theirs alone. Contact InfoDom Securities at dominanceinformation@gmail.com