Monday, Sept 12, 2022 // (IG): BB //Sponsor: VetSec
I'm reminded of 'The Early Bird", 'cept your posts are seemingly on semantically-enhanced steroids. - 2600hz
Multiple ransomware campaigns linked to Iranian threat actor DEV-0270
FROM THE MEDIA: Security researchers at tech giant Microsoft have linked multiple ransomware campaigns to DEV–0270 (also known as Nemesis Kitten), widely considered a subgroup of Iranian actor PHOSPHORUS. According to a new write–up by Microsoft, threat actor conducts various malicious network operations on behalf of the Iranian government. Microsoft also hypothesized that some of DEV-0270’s attacks might be a form of moonlighting for personal or company-specific revenue generation based on the threat actor’s geographic and sectoral targeting.
READ THE STORY: TEISS
APT groups use spam emails to launch attacks — Kaspersky
FROM THE MEDIA: Based on the data from cybersecurity solutions firm Kaspersky, 24% of email users in the Asia Pacific received malicious spam mail, which the company blocked. Other findings on spam mail landscape were presented during Kaspersky’s cybersecurity weekend held recently. Malicious spam is not a technologically complex attack, but when done with sophisticated social engineering techniques, it poses a severe threat to individuals and enterprises alike.
READ THE STORY: Back End News
Why The Future Of Cyber Operations Will Be Covert
FROM THE MEDIA: Current cyber conflict looks very similar to traditional conflict models. The difference from traditional power dynamics offered by the cyber domain, however, is the asymmetrical advantage of technology for would-be actors. This new element of national power allows weaker actors to “punch above their weight” in competition or conflict with Great Powers in a unipolar or multipolar world. John Arquilla describes this new environment as an “information revolution” that “implies the rise of cyber war, in which neither mass nor mobility will decide outcomes.
READ THE STORY: Daily Guardian
Albania blamed Iran for a new cyberattack that hit computer systems used by the state police on Friday
FROM THE MEDIA: Last week, the Albanian Prime Minister announced that Albania interrupted diplomatic ties with Iran and expelled the country’s embassy staff over the massive cyber attack that hit the country in mid-July. The cyberattack hit the servers of the National Agency for Information Society (AKSHI), which handles many government services. Most of the desk services for the population were interrupted, and only several important services, such as online tax filing, were working because they are provided by servers not targeted in the attack. Albania reported the attack to the NATO Member States and other allies.
READ THE STORY: Security Affairs
Montenegro wrestles with massive cyberattack, Russia blamed
FROM THE MEDIA: At the government headquarters in NATO-member Montenegro, the computers are unplugged, the internet is switched off and the state's main websites are down. The blackout comes amid a massive cyberattack against the small Balkan state which officials say bears the hallmark of pro-Russian hackers and its security services. The coordinated attack that started around Aug. 20 crippled online government information platforms and put Montenegro's essential infrastructure, including banking, water and electricity power systems, at high risk.
READ THE STORY: WRAL
Top Iranian hackers exposed by opposition outlet
FROM THE MEDIA: The identities of five top Iranian hackers behind large-scale cyberattacks across the world were revealed by opposition outlet Iran International. The exposed are leaders of Iran's Islamic Revolutionary Guard Corps' cyber wing. Among them, Amid Reza Lachkarian, 61, who is the commander of the cyber unit of the Iranian paramilitary organization. According to the information relayed, he is likely to be behind the order to attack Western ships and cyberattacks damaging the distribution of fuel in 2021. The four other officials, whose identities were disclosed by the Saudi-funded news site, are believed to be behind the most publicized cyber attacks attributed to Iran in recent months.
READ THE STORY: i24
CyberCube: Russia’s Sovereign Internet Creates Security Risks With Implications for Cyber (Re)Insurance While War in Ukraine Develops
FROM THE MEDIA: A sovereign Russian internet could lead to cyber criminal safe havens, greater confidence that large-scale attacks can be carried out without consequences, and intelligence blindspots, according to a new report published today by cyber risk analytics expert CyberCube. William Altman, CyberCube’s Principal Cyber Security Consultant, said: “A Russian sovereign internet has several potential implications for cyber activity. Rival nations will find it more difficult to acquire cyber threat intelligence on threat actors operating from inside Russia, and might resort to more drastic measures to achieve this goal, potentially causing collateral damage.
READ THE STORY: Business Wire
Hackers found a new way to sneak malware into your computer using Minecraft updates — here’s how you can stay safe
FROM THE MEDIA: The video game industry has become one of the biggest beneficiaries of the pandemic as millions of people picked up the habit of playing video games to escape the isolation and boredom of the COVID-19 lockdowns.
Since then, the gaming industry has been expanding rapidly, and the number of video game-related cyberthreats and attacks has significantly risen in recent months, research has revealed.
READ THE STORY: Business Insider
New Linux Malware Discovered, Targets Internet-of-Things Devices and Servers
FROM THE MEDIA: Researchers at the AT&T Alien Labs have discovered a new strain of Linux malware that is extremely hard to detect and affects both traditional servers and Internet-of-things devices, which are typically less secure than your average computer (via Ars Technica). The malware, dubbed “Shikitega,” is delivered through a multistage infection chain and uses polymorphic encoding to slip under the radar of antivirus technologies and other defences. In addition, Shikitega also hosts its command-and-control servers on recognizable cloud services to appear legitimate.
READ THE STORY: IC
Cisco confirms Yanluowang ransomware leaked stolen company data
FROM THE MEDIA: Cisco has confirmed that the data leaked yesterday by the Yanluowang ransomware gang was stolen from the company network during a cyberattack in May. On September 11, 2022, the bad actors who previously published a list of file names from this security incident to the dark web, posted the actual contents of the same files to the same location on the dark web. The content of these files match what we already identified and disclosed. Our previous analysis of this incident remains unchanged-we continue to see no impact to our business, including Cisco products or services, sensitive customer data or sensitive employee information, intellectual property, or supply chain operations.
READ THE STORY: Bleeping Computer
Cyber espionage actions are hampering closer China-U.S. ties
FROM THE MEDIA: China condemns the cyberattacks carried out by the U.S. against China's Northwestern Polytechnical University and asks to provide justification and immediately to cease any illegal actions. According to reports, the U.S. launched over 10,000 times cyber attacks against China and stole crucial technical data. In recent years, Chinese corporations have produced reports accusing U.S. agencies of cyberattacks on Chinese assets. Notably, a Trojan horse malware alleged to have been installed by the National Security Agency of the U.S. has been discovered in hundreds of crucial information systems in China, which may have already leaked.
READ THE STORY: CGTN
Western Balkans Urged to Prepare for Uptick in Cyber-Attacks
FROM THE MEDIA: The countries of the Western Balkan countries can expect an increase in cyber-attacks in the future and should prioritize online account and data security, Canada-based ransomware expert Brett Callow told BIRN in the wake of an unprecedented ransomware attack on government servers in Montenegro. A major part of the state’s digital infrastructure was forced offline in Montenegro in two cyber-attacks since August 22. That followed an attack on government servers in neighboring Albania in mid-July, which the government this week blamed on Iran. Kosovo also reported an unsuccessful assault on the cyber network of state institutions in early July.
READ THE STORY: Balkan Insight
The Merge: a blockchain revolution or just more hype
FROM THE MEDIA: At the Blockchain Futurist Conference in Toronto in early August, Ethereum co-founder Vitalik Buterin stood before an excitable audience to deliver some big news. “The Merge is coming,” he told the crowd, “this effort that we have been working on for basically the last eight years . . . Ethereum will finally become a proof-of-stake system . . . Yay!” The audience cheered. If there is one thing the crypto community has in good supply, it’s promises. In the relatively short history of digital assets — starting with bitcoin in 2009 — evangelists have trailed a list of innovations that, they say, could solve inflation, revolutionize business, or provide a financial lifeline to people living under authoritarian regimes around the world.
READ THE STORY: FT
Chaos continues as district tries to recover from systems hack
FROM THE MEDIA: A full week after the cyber attack that forced LAUSD to completely shut down all online systems, disruptions continue even as many students, teachers and administrators are able to access their accounts after many days of being locked out. Superintendent Alberto Carvalho confirmed that this unusual activity was a ransomware attack. On Friday, the Los Angeles Times reported that a cybercriminal syndicate operating out of Russia calling itself Vice Society claimed responsibility for the attacks, but LAUSD would not confirm this information. The FBI is investigating. District officials are not certain if personal data was compromised.
READ THE STORY: The Mirror
Making Hacking Futile – Quantum Cryptography
FROM THE MEDIA: The Internet is filled with highly sensitive data. In general, sophisticated encryption techniques guarantee that such material cannot be intercepted and read. However, in the future, high-performance quantum computers could break these keys in a matter of seconds. It is therefore fortunate that quantum mechanical approaches offer not just new, far faster algorithms, but also very effective cryptography. Quantum key distribution (QKD), as the jargon says, is safe against attacks on the communication channel but not against attacks or manipulations of the devices themselves.
READ THE STORY: SciTech Daily
Bad bots are coming at APIs! How to beat the API bot attacks?
FROM THE MEDIA: API or Application Programming Interface is a de facto building block for modern-day applications, necessary for both building and connecting applications and websites. But APIs are poorly protected and have become one of the prime targets for attacks, especially bot attacks. 75% of login attempts from API (Application Programming Interfaces) endpoints are malicious – according to perimeterx. Hackers systematically use bots for malicious login attempts.
READ THE STORY: HelpNetSecurity
Tornado Cash Mixer Users Sue US Treasury After Sanctions
FROM THE MEDIA: In response to sanctions, six users of Tornado Cash, the crypto mixer service, are suing the United States Treasury. They’re also suing Treasury Secretary Janet Yellen, among other officials. The United States Treasury hit Tornado Cash with heavy sanctions in early August. Allegedly, the decentralized application facilitated the laundering of $7 billion in cryptocurrency. Coinbase security analyst Tyler Almeida and Ethereum protocol developer Preston Van Loon are critical plaintiffs in the case. Almeida allegedly used the service to make crypto donations to Ukrainian defense efforts amid Russia’s invasion.
READ THE STORY: BoldTV
Russia To Install Powerful Electronic Warfare System To Defend Its Warships From Drone & Missile Attacks
FROM THE MEDIA: As per the sources within the Russian military, cited by Izvestia, the new EW systems will be installed in standard 40-foot sea containers and can be easily mounted on the deck of various surface ships of the Russian Navy, including auxiliary vessels like tugboats, transports, and others. According to Izvestia, these protective containers should reliably cover ships and vessels from enemy missiles and drones by jamming their electronics. The Russian military sources told Izvestia that the Project 22160 series patrol ships would be the first set of platforms within the Russian Navy to receive the new electronic warfare system.
READ THE STORY: The EurAsian Times
Ukraine Claims Its Southern Offensive Was A 'disinformation Campaign' To Trick Russia
FROM THE MEDIA: A day after Russia’s Defence Ministry announced that it was pulling back troops from two areas in Ukraine’s eastern Kharkiv region amid a strong counteroffensive by Ukrainian forces, a senior Kyiv official said they publicised a disinformation campaign to distract Russian forces. While speaking to The Guardian, former national security advisor turned press officer for the Bohun brigade of Ukraine’s special forces, Taras Berezovets, said the operation of a special disinformation process helped Ukrainian forces to distract Russia from the real one. According to the senior official, this helped Ukrainian forces to prepare in the Kharkiv region.
READ THE STORY: Republic World
American Planes Patrolling Afghanistan’s Airspace Raise Questions
FROM THE MEDIA: After two decades of military presence in Afghanistan, the United States of America ended its 20-year mission of fighting against terrorism in the country and completely withdrew its military and coalition forces on August 2021. Despite complete withdrawal, but the US air patrol continues in Afghanistan’s airspace. Taliban had promised the United States in the Doha Agreement of cutting ties with al-Qaeda and other terrorist groups, but the presence Ayman al-Zawahiri, the leader of al-Qaeda in Kabul, turned the American and international community’s doubt into surety that Taliban group has not cut off ties with terrorist networks, but has enabled ground for their regrouping and reemergence in Afghanistan.
READ THE STORY: Hasht e Subh
Qii.AI and Skydio Enter Technology Partnership to Advance AI for Automated Infrastructure Inspections
FROM THE MEDIA: Qii.AI, the provider of digital inspection software for infrastructure, announced today that it is partnering with Skydio, the leading U.S. drone manufacturer and world leader in autonomous flight, to make drone-powered inspection more efficient and effective for customers across North America. Drones are powerful and cost-effective tools for inspection, and autonomy is the key to deploying these solutions for safe and reliable operation. Skydio’s adaptive scanning software, Skydio 3D Scan™, extends the company’s groundbreaking autonomous flight engine with advanced artificial intelligence (AI) skills that automate photographic data collection and mapping tasks ranging from infrastructure asset inspection to crime and accident scene reconstruction.
READ THE STORY: SUAS News
Boffins build microphone safety kit to detect eavesdroppers
FROM THE MEDIA: Scientists from the National University of Singapore and Yonsei University in the Republic of Korea have developed a device for verifying whether your laptop microphone is secretly recording your conversations. The researchers – Soundarya Ramesh, Ghozali Suhariyanto Hadi, Sihun Yang, Mun Choon Chan, and Jun Han – call the device TickTock. That may suit a lab project but would obviously invite a trademark lawsuit from a similarly named social media company were commercialization ever considered.
READ THE STORY: The Register
TikTok users targeting migrants with misinformation
FROM THE MEDIA: Videos aimed at desperate migrants are making their way across social media platforms, including TikTok. One in particular shows a user telling Venezuelans they can migrate to the U.S. without getting a visa. “It broke my heart because you can see the hope coming through in these comments,” Adriana Rivera, who works for the Florida Immigrant Coalition, told NewsNation’s “Rush Hour” on Friday. Rivera called the claims in these videos outrageous, noting that the videos have now been seen and shared tens of thousands of times. Rivera went on to note that the U.S. already faces an overwhelming situation at its borders.
READ THE STORY: FOX 59
Ukraine forces tricked Russia with disinformation campaign
FROM THE MEDIA: The much-publicized Ukrainian southern offensive was a disinformation campaign to distract Russia from the real one being prepared in the Kharkiv region, Ukraine’s special forces have said, the media reported. Ukrainian forces are continuing to make unexpected, rapid advances in the north-east of the country, retaking more than a third of the occupied Kharkiv region in three days, The Guardian reported. Much of Ukraine’s territorial gains were confirmed by Russia’s defence ministry on Saturday.
READ THE STORY: SIASAT
North Korea’s fake missile defense batteries (probably) aren’t fooling anyone
FROM THE MEDIA: North Korea has set up at least nine mock surface-to-air missile (SAM) batteries around the country in recent years, analysis of satellite imagery shows, in what appears to be an attempt to fool enemies into attacking the fake airspace defense installations to improve the survivability of active SAMs. Four of these mock facilities are located in a line along the inter-Korean border, aligned with eight active SAM sites in the same region, while two more dummies “protect” the north-south air route into Pyongyang. The remaining sites are scattered around the country.
READ THE STORY: NKNEWS
‘Wildfire of disinformation’: how Chevron exploits a news desert
FROM THE MEDIA: The dire state of local journalism in the US has been well documented in recent years, as the closure of hundreds of local newspapers has created American “news deserts” where people struggle for information on local politics and happenings. It has also created openings for companies and political groups to swoop in, serving up a mixture of local news and propaganda, with the latest being Chevron, in Texas’ news starved – and oil-rich – Permian Basin. The launch of Chevron’s “Permian Proud” site, in August, was first reported by Gizmodo.
READ THE STORY: The Guardian
Items of interest
Russia is Burning all Sorts of Bridges
FROM THE MEDIA: Dmitry Medvedev, Russia’s former president, made headlines in early August when he published a lengthy statement that labeled Kazakhstan as an “artificial state” and warned Nur-Sultan of a Ukraine-like scenario. Unfortunately, rather than constructive and bridge-building, comments like these continue to create a divide between Russia and its allies.
Medvedev’s statement was made via his Vkontakte account to his 2.2 million followers, in which he accused Kazakhstan of carrying out a “genocide” against ethnic Russians who live in northern Kazakhstan via resettlement policies. Moreover, he warned that Russia would protect ethnic Russians and alluded to the current war in Ukraine. However, the statement was deleted days later, and Medvedev’s team issued another statement explaining that the account was hacked.
READ THE STORY: International Policy Digest
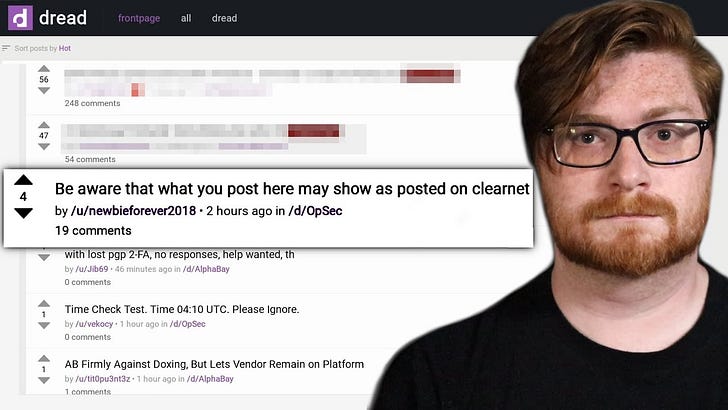
Navigating Tor Hidden Services (Video)
FROM THE MEDIA: Navigating TOR Hidden Services.
Setting Up Whonix for ANONYMOUS Tor Browsing (Video)
FROM THE MEDIA: Setting Up Whonix for ANONYMOUS Tor Browsing.
These open source products are reviewed from analysts at InfoDom Securities and provide possible context about current media trends in regard to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not specifically endorse any third-party claims made in their original material or related links on their sites, and the opinions expressed by third parties are theirs alone. Contact InfoDom Securities at dominanceinformation@gmail.com