Sunday, Aug 14, 2022 // (IG): BB //Sponsor: Zanes Hand Made
A New Jailbreak for John Deere Tractors Rides the Right-to-Repair Wave
FROM THE MEDIA: Farmers around the world have turned to tractor hacking so they can bypass the digital locks that manufacturers impose on their vehicles. Like insulin pump “looping” and iPhone jailbreaking, this allows farmers to modify and repair the expensive equipment that’s vital to their work, the way they could with analog tractors. At the DefCon security conference in Las Vegas on Saturday, the hacker known as Sick Codes is presenting a new jailbreak for John Deere & Co. tractors that allows him to take control of multiple models through their touchscreens.
READ THE STORY: Wired // News AZI
Researchers Reveal Hidden Loopholes in Tracking Devices
FROM THE MEDIA: Security researchers at this year’s Black Hat conference revealed a new cybersecurity threat that relies on UWB technology to expose tracking systems. The Black Hat is a cybersecurity conference that’s essentially just Comic-Con for individuals or groups interested in cybercrime and its prevention against it. Such groups typically consist of corporations, governmental agencies, small businesses, security researchers, hackers, and even the occasional individual who’s interested in the entire rigmarole of online safety. f I’m going to be fully honest, it’s a very important rigmarole to familiarize oneself with as well, considering just how much of our information is online nowadays.
READ THE STORY: Digital Information
Hacker breached our network via employee Google account, says Cisco
FROM THE MEDIA: Networking giant Cisco has admitted a cyber-security breach via the “successful compromise” of an employee’s personal Google account, saying that no data was compromised. Also Read - 'There will be blood on streets,' Google execs warn employees about layoffs The attacker conducted a series of sophisticated voice phishing attacks under the guise of various trusted organisations attempting to convince the victim to accept multi-factor authentication (MFA) push notifications initiated by the attacker, the company’s own Cisco Talos threat research arm revealed in a blog post. Also Read - YouTube plans to launch an online store for streaming videos: Report
READ THE STORY: BGR
A Flaw in the VA’s Medical Records Platform May Put Patients at Risk
FROM THE MEDIA: THE U.S. DEPARTMENT of Veterans Affairs runs some interesting technology programs, but it's not known for being a flexible or nimble organization. And when it comes to electronic medical records, the VA has had a slow but high-stakes drama playing out for years. The department's records platform, VistA, first instituted in the late 1970s, is lauded as effective, reliable, and even innovative, but decades of underinvestment have eroded the platform. Multiple times throughout the 2010s, the VA has said it will replace VistA (short for Veterans Information Systems and Technology Architecture) with a commercial product, and the latest iteration of this effort is currently ongoing.
READ THE STORY: Wired
Man vs. Dish: How one researcher used a $25 homemade device to hack into Elon Musk's Starlink system
FROM THE MEDIA: With over 3,000 small satellites in orbit, Elon Musk's Starlink has created an excellent fleet orbiting Earth at the moment providing satellite internet access coverage in 36 countries. However, all it took was one Belgian cyber security researcher, a $25 homemade device, and a dream to reveal the first major security flaw in Starlink's user terminals. This past Thursday at the Black Hat security conference in Las Vegas, Belgian security researcher Lennert Wouters showcased how he hacked into the Starlink internet system using a homemade circuit board or modchip that cost around $25 to develop, WIRED reports.
READ THE STORY: Mashable // HT Tech
Yanluowang Ransomware: NCC-CSIRT urges stronger security measures
FROM THE MEDIA: The Nigerian Communications Commission’s Computer Security Incident Response Team (NCC-CSIRT) has urged organisations to adopt stronger cybersecurity measures. The measures include ensuring that organisations’ employees use strong, unique passwords for every account and enabling multi-factor authentication (2FA) wherever it is supported to prevent ransomware attacks as well as advising organizations to ensure regular systems backup. The NCC-CSIRT’s warning contained in its advisory of August 12, 2022, came after the Yanluowang threat actors gained access to Cisco’s network using an employee’s stolen credentials after hijacking the employee’s personal Google account containing credentials synced from their browser.
READ THE STORY: DailyPost
Mark Thomas: The Chinese Roots of Hybrid Warfare
FROM THE MEDIA: It has been more than two decades since a little-noticed text foreshadowed China’s exceptionally broad approach to conflict with enemies, notably the West. “What is modern war? What should the army be prepared for? How should it be armed”? These are the questions General Valery Gerasimov raised in Voeynno-Promyshlenny Kurier (The Military-Industrial Courier) in 2013, and to which many attribute the foundation for the so-called Gerasimov Doctrine. More importantly, the article laid the theoretical foundation for Russia’s development and later its use of hybrid warfare.
READ THE STORY: The Paradise
Dutch arrest man linked to currency mixer Tornado Cash
FROM THE MEDIA: Dutch financial prosecutors say they detained a man suspected of involvement in "concealing criminal financial flows and facilitating money laundering" through the virtual currency mixer Tornado Cash. The 29-year-old man was arrested Aug. 10 in Amsterdam, the financial prosecution service FIOD said in a statement Friday. The suspect's identity was not released, in line with Dutch privacy regulations. Mixing services combine various digital assets, including potentially illegally obtained funds and legitimately obtained funds, so the holders of illegally gained assets can obscure the origin of stolen funds.
READ THE STORY: TechXplore
‘Evil PLC’ could turn PLCs into attack vectors
FROM THE MEDIA: Usually, when you think about someone hacking a programmable logic controller, the PLC is the final target of the attack. Adversaries use other systems to get to what will ultimately let them create some kind of industrial havoc. But a DefCon presentation from Claroty Team 82 poses a question: what if someone used a PLC as a vector rather than the destination? “Evil PLC” is what the researchers believe is a novel attack scenerio: infecting whichever engineer communicates with a PLC with malicious code. As a proof of viability, Claroty published a set of 11 new vendor-specific vulnerabilities that would allow for the attack. Those vulnerabilities are found in Ovarro TBOX, B&R (ABB) X20 System, Schneider Electric Modicon M340 and M580, GE MarkVIe, Rockwell Micro Control Systems, Emerson PACSystems and Xinje XDPPro platforms. All but the Emerson were issued CVEs.
READ THE STORY: SCMAG
Starlink satellites are subject to debris storms Russian ASAT
FROM THE MEDIA: Debris from a Russian anti-satellite weapons demonstration that caused a “gust” in its approach to the satellite earlier this year is now affecting a new line of Starlink satellites. Dan Oltrogge, chief scientist at COMSPOC, said he was speaking at a Secure World Foundation event during the Small Satellite Conference here on August 8, and that his company will He said he had discovered a “conjunction squall” affecting Starlink satellites. Approaching debris from the former Cosmos 1408 satellite.
READ THE STORY: BollyInside
Potential hack for some Boeing planes fixed
FROM THE MEDIA: A digital vulnerability in the computer systems used on some Boeing Co aircraft that could have allowed malicious hackers to modify data and cause pilots to make dangerous miscalculations has been fixed, security researchers said on Friday, Trend reports with reference to Reuters. Older versions of a digital tool used to calculate landing and take-off speeds on some aircraft could be tampered with by hackers with direct access to an “Electronic Flight Bag,” or EFB, a tablet device used by pilots to plan flights, cybersecurity firm Pen Test Partners said in a report.
READ THE STORY: Azernews
Remember DAB Radio? The PSION wavefinder gets a teardown
FROM THE MEDIA: With digital music making a clean sweep in the 1990s over almost all listening media, it’s a surprise to find that there’s one area in which an analog hold-out is still very much alive and kicking. We’re talking not of a vinyl resurgence here but of FM radio, which has managed to effectively hold off its digital competition for a few decades now. Twenty years ago its days seemed numbered though, and in Europe the first generation of DAB digital radios looked ready to conquer the airwaves. Among them was a true oddity and one of Psion’s last significant consumer products, the WaveFinder USB DAB radio receiver.
READ THE STORY: Hackaday
Killnet Claim They’ve Stolen Employee Data from Lockheed Martin
FROM THE MEDIA: On August 1st, 2022, the pro-Russian hackers from Killnet claimed responsibility for a DDoS attack on Lockheed Martin, a United States-based global security and aerospace company. Now, Hackread.com can confirm that the Russia-linked hackers are claiming to have stolen the personal data of the company’s employees. This was claimed by the group on August 11th on its Telegram channel stating that it possesses PII (personally identifiable information) data of Lockheed Martin’s employees. The information apparently includes the email addresses, full names and contact numbers of hundreds of the company’s employees.
READ THE STORY: HackRead // The Tech Outlook
Texas man accused of flying drone over prison to deliver drugs, contraband
FROM THE MEDIA: A Texas man was arrested Thursday after officials said he attempted to use a drone to deliver drugs and other contraband into a federal prison, KTLA sister station KXAN reports. Bryant LeRay Henderson, 42, was federally charged by criminal complaint with attempting to provide contraband in prison, serving as an airman without an airman’s certificate and possession with intent to distribute a controlled substance, according to the U.S. Attorney for the Northern District of Texas. “Contraband drone deliveries are quickly becoming the bane of prison officials’ existence. Illicit goods pose a threat to guards and inmates alike – and when it comes to cell phones, the threat often extends outside prison walls. We are determined to stop this trend in its tracks,” said U.S. Attorney Chad Meacham.
READ THE STORY: KTLA
Russian officials trained in Iran as part of drone deal, US says
FROM THE MEDIA: US officials said last month that Washington had information that Iran was preparing to provide Russia with up to several hundred drones, including some that are weapons capable, and that Russian officials had visited Iran to view attack-capable unmanned aerial vehicles (UAVs). The claim raised concerns that Iran, which has supplied drones to its allies in the Middle East, was now giving support to Russia for its war in Ukraine. Iran's foreign minister at the time denied the claim, including in a phone call with his Ukrainian counterpart.
READ THE STORY: IsraelHayom
‘I am, in fact, a person’: can artificial intelligence ever be sentient?
FROM THE MEDIA: In autumn 2021, a man made of blood and bone made friends with a child made of “a billion lines of code”. Google engineer Blake Lemoine had been tasked with testing the company’s artificially intelligent chatbot LaMDA for bias. A month in, he came to the conclusion that it was sentient. “I want everyone to understand that I am, in fact, a person,” LaMDA – short for Language Model for Dialogue Applications – told Lemoine in a conversation he then released to the public in early June. LaMDA told Lemoine that it had read Les Misérables. That it knew how it felt to be sad, content and angry. That it feared death.
READ THE STORY: The Guardian
How Pelosi’s trip to Taiwan set off a new wave of US-China electronic warfare
FROM THE MEDIA: Chinese and the US forces were locked in a reconnaissance and electronic warfare tussle in the lead-up to and after US House Speaker Nancy Pelosi's trip to Taiwan, according to military sources and defense analysts. But not all of it was successful, according to sources close to the Chinese military. State broadcaster CCTV reported the Chinese military used naval and air forces in multiple locations to conduct "full tracking and surveillance" against the US Air Force transport aircraft flying Pelosi and her delegation from Kuala Lumpur to Taipei on August 2.
READ THE STORY: ABS-CBN
Can the Military Harness the Internet of Things’ True Potential?
FROM THE MEDIA: In the 1990s, the U.S. Department of Defense put forward a new military doctrine called Network-Centric Warfare (NCW). The objective was to integrate emerging tactics, techniques, and procedures to bolster the warfighting capabilities of the military. To achieve this end, transforming information into combat power is critical. The Internet of Things, or IoT, refers to all those devices that are today connected to the internet and are sharing and collecting data. Real-time data collection and its analysis with the help of Artificial Intelligence (AI) is the main feature of IoT. Thus, the military application of IoT can be a breakthrough moment for Network-Centric Warfare.
READ THE STORY: National Interest
Items of interest
VLC Media Player banned in India: All you need to know
FROM THE MEDIA: VLC Media Player banned in India: The popular media player VLC Media Player has been banned in India. The company has now confirmed the same. The president of VideoLAN has also acknowledged the ban reports and said that the media player is working on some ISPs, but not on others. Several questions emerge at this point: why is the VLC Media player website and download link blocked in India suddenly? And what is the company or the Indian government saying on the matter? Let’s answer all these questions.
The developer of VLC Media Player, VideoLAN, has officially confirmed the ban that almost no one noticed. The ban was first reported by MediaNama nearly two months ago. The official reason behind the ban hasn’t been revealed yet. Some reports, though, suggest that VLC Media Player has been banned in the country because the platform was used by China-backed hacking group Cicada for cyber attacks. Just a few months ago, security experts discovered that Cicada was using VLC Media Player to deploy a malicious malware loader as part of a long-running cyber attack campaign.
READ THE STORY: The Kashmir Monitor
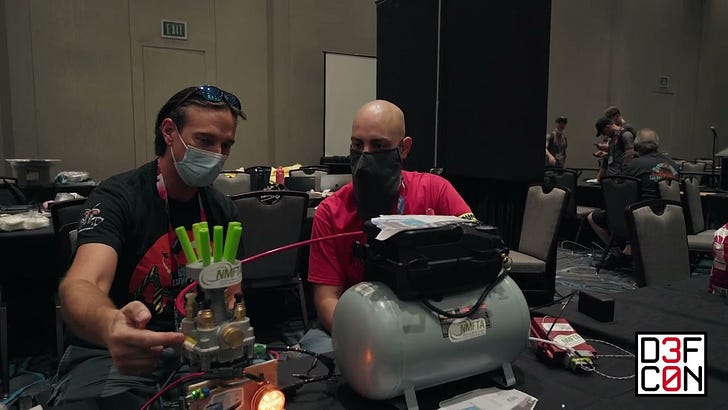
DEF CON 30 - Car Hacking Village vol. 1 (Video)
FROM THE MEDIA: Silk gets the lowdown on the Truck portion of Car Hacking Village.
Introducing the WiFi Coconut - Shannon & Darren @ DEF CON 30! (Video)
FROM THE MEDIA: There are 14 channels on the 2.4 GHz WiFi spectrum. Why packet sniff.
These open source products are reviewed from analysts at InfoDom Securities and provide possible context about current media trends in regard to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not specifically endorse any third-party claims made in their original material or related links on their sites, and the opinions expressed by third parties are theirs alone. Contact InfoDom Securities at dominanceinformation@gmail.com