Thursday, Aug 04, 2022 // (IG): BB //Sponsor: Zanes Hand Made
Cyberattacks affect three official sites in Taiwan (DDoS)
FROM THE MEDIA: Representative Nancy Pelosi (Democrat, California 12th District), prepared for her visit to Taiwan, cyberattacks briefly took down at least three Republic of China websites. The New York Times reports, "The official website of Taiwan’s presidential office was attacked around 5 p.m., according to a statement from the office, several hours before Ms. Pelosi’s landing. The site’s traffic shot up to 200 times that of a normal day, leaving the website unable to display any content for 20 minutes. It resumed normal operation after the problems were fixed, according to the statement.
READ THE STORY: The CyberWire // SCMEDIA // Reuters
Spanish research agency still recovering after ransomware attack
FROM THE MEDIA: The Spanish National Research Council (CSIC) last month was hit by a ransomware attack that is now attributed to Russian hackers. CSIC is a state agency for scientific research and technological development part of the Spanish Ministry of Science and Innovation but with a special status in that it has “its own assets and treasury, functional and managerial autonomy.” In a statement on Tuesday, the agency said that the ransomware attack occurred on the weekend of July 16-17 and it was detected on Monday, July 18.
READ THE STORY: Bleeping Computer
FEMA warns emergency alert systems could be hacked to transmit fake messages unless software is updated
FROM THE MEDIA: Vulnerabilities in software that TV and radio networks around the country use to transmit emergency alerts could allow a hacker to broadcast fake messages over the alert system, a Federal Emergency Management Agency official tells CNN. A cybersecurity researcher provided FEMA with "compelling evidence to suggest certain unpatched and unsecured EAS [Emergency Alert System] devices are indeed vulnerable," said Mark Lucero, the chief engineer for Integrated Public Alert & Warning System, the national system that state and local officials use to send urgent alerts about natural disasters or child abductions.
READ THE STORY: CNN
Microsoft email users, even with MFA on, are unsafe from this new phishing attack
FROM THE MEDIA: Microsoft email service users need to be careful out there. That's because Zscaler, a cybersecurity research firm, has discovered a new ongoing phishing campaign targeting Microsoft email users. According to its findings, corporate users are under attack and the campaign is being run using adversary-in-the-middle (AiTM) technique to bypass multi-factor authentication (MFA). The AiTM technique, as the name suggests, places an adversary in the middle to intercept the authentication process between the client and the server to steal credentials during the exchange. This means the MFA information is also stolen.
READ THE STORY: NEOWIN
Russian organizations attacked with new Woody RAT malware
FROM THE MEDIA: Unknown attackers target Russian entities with newly discovered malware that allows them to control and steal information from compromised devices remotely. According to Malwarebytes, one of the Russian organizations that were attacked using this malware is a government-controlled defense corporation. "Based on a fake domain registered by the threat actors, we know that they tried to target a Russian aerospace and defense entity known as OAK," the Malwarebytes Labs researchers said.
READ THE STORY: Bleeping Computer
Ransomware attack impacts Semikron, a German-based independent manufacturer of power semiconductor components
FROM THE MEDIA: BleepingComputer reports that Semikron, a German power engineering component manufacturer with production sites in the U.S. and other parts of the world, has been impacted by a ransomware attack that prompted partial IT network encryption. Data has been claimed to be stolen by a "professional hacker group," which has already threatened Semikron into paying the demanded ransom so that the allegedly stolen data would not be exposed, an alert from the German Federal Office for Information Security revealed. An encrypted Semikron system was found by BleepingComputer to have a ransom note from the LV Ransomware operation, which claimed to steal 2TB worth of files. Semikron has already notified law enforcement regarding the incident, with customers and partners to be updated on any data theft evidence to be identified.
READ THE STORY: SCMAG // SecurityAffairs
Supply Chain and Cloud Security Risks Are Top of Mind
FROM THE MEDIA: Black Hat, the producer of the cybersecurity industry’s most established and in-depth security events, releases its eighth annual community survey Supply Chain and Cloud Security Risks Are Top of Mind. The report highlights important findings from more than 180 of the industry’s most experienced cybersecurity professionals who reported concerns over attacks against cloud services, ransomware and the growing risks to the global supply chain. 2021 was the year of supply chain attacks as organizations learned the various ways the global supply chain could be abused to compromise a large number of victims.
READ THE STORY: Valdosta Daily Times
Threat actors hide malware in legitimate — and high profile — applications
FROM THE MEDIA: The report highlights how attackers hide malware behind legitimate applications in order to trick users into installing what instead contains malicious files. Researchers said they found at least 2.5 million suspicious files — detected by at least five different antivirus programs — from the top 1,000 Alexa domains. Attackers are using trusted applications as bait to lure potential victims, according to Vicente Diaz, security engineer at VirusTotal, a unit of Google Cloud.
READ THE STORY: Cyber Security Dive
Cloned Atomic Wallet website is pushing Mars Stealer malware
FROM THE MEDIA: A fake website impersonating the official portal for the Atomic wallet, a popular decentralized wallet that also operates as a cryptocurrency exchange portal, is, in reality, distributing copies of the Mars Stealer information-stealing malware. The phony website was disclosed by a malware researcher known as Dee on Monday, but at the time of writing this, it remains online, serving copies of the said malware.n Assistance Commission (EAC) guidelines advising against using modems. Seeing the genuine and fake websites side by side reveals that the latter isn’t a faithful copy of the former, but it’s still using the official logos, themes, marketing images, and structure. The fake site even features a contact form, email address, and FAQ section.
READ THE STORY: Bleeping Computer
Crypto Threat: Malware Infiltrates Github Cloning Thousands of Repos
FROM THE MEDIA: Tech portal Bleeping Computer reported that the repos were not hacked but had been copied with their clones altered to include the malware. Cloning open source code is a common practice among developers, however, the attackers have injected malicious code and links into legitimate projects to target unsuspecting developers. Several projects from crypto, Golang, Python, JavaScript, Bash, Docker, and Kubernetes have been affected by the attack, the researcher noted.
READ THE STORY: BeinCrypto
Spyware sales ‘explosion’ powers attacks
FROM THE MEDIA: In the backrooms of the internet, an “explosion” of spyware products has changed cybercrime forever, putting more Australians at risk. Over the past decade, the number of remote access Trojan spyware products on the black market has increased tenfold to at least 50, according to University of Melbourne senior cybersecurity lecturer Shaanan Cohney. The increase coincides with a long-running shift in cybercrime – what was once a show of ego, dominance and control is now a lucrative business model. “What we have seen is a relative explosion in the number of these products for sale,” Dr Cohney told AAP.
READ THE STORY: CRIKEY
From Babuk source code to Darkside custom listings – exposing a thriving ransomware marketplace on the dark web
FROM THE MEDIA: Venafi, the inventor and leading provider of machine identity management, today announced the findings of a dark web investigation into ransomware spread via malicious macros. Conducted in partnership with criminal intelligence provider Forensic Pathways between November 2021 and March 2022, the research analysed 35 million dark web URLs, including marketplaces and forums, using the Forensic Pathways Dark Search Engine. The findings uncovered 475 webpages of sophisticated ransomware products and services, with several high-profile groups aggressively marketing ransomware-as-a-service.
READ THE STORY: iTwire
Cyber attacks have become ‘firmly entrenched as a state-level weapon’
FROM THE MEDIA: Check Point Research (CPR) has published its ‘Cyber Attack Trends: 2022 Mid-Year Report’ highlighting how cyber attacks have become firmly entrenched as a state-level weapon, including the new ransomware method of ‘Country Extortion’ and state-affiliated hacktivism. Besides insight into the evolution of cyber attacks as a state-level weapon complementing actual military conflict, and the elevation of ransomware utilized in nation-state level attacks for financial and social gain, the report also delves into the growth of cloud supply chain attacks through new sources of modules in the open-source community.
READ THE STORY: Continuity Central
China's Taiwan war games threaten more global supply chain disruption
FROM THE MEDIA: Chinese military exercises around Taiwan are set to disrupt one of the world's busiest shipping zones, analysts told AFP, highlighting the island's critical position in already stretched global supply chains. The drills -- China's largest-ever around Taiwan -- are a major show of strength after US House Speaker Nancy Pelosi infuriated Beijing by visiting the island. The manoeuvres kicked off Thursday and will take place along some of the busiest shipping routes on the planet, used to supply vital semiconductors and electronic equipment produced in East Asian factory hubs to global markets.
READ THE STORY: MINT
Nozomi cyber-attacker 'traps' show impact of Russia/Ukraine war
FROM THE MEDIA: The latest Operational Technology (OT)/IoT security report from Nozomi Networks Labs finds wiper malware, IoT botnet activity, and the Russia/Ukraine war impacted the threat landscape in the first half of 2022. Since Russia began its invasion of Ukraine in February 2022, Nozomi Networks Labs researchers saw activity from several types of threat actors, including hacktivists, nation-state advanced persistent threats (APTs), and cyber criminals. They also observed the robust usage of wiper malware, and witnessed the emergence of an Industroyer malware variant (used in the cyberattack on Ukraine’s power grid), dubbed Industroyer2, developed to misuse the IEC-104 protocol, which is commonly used in industrial environments.
READ THE STORY: VOXY
Microsoft widens enterprise access to its threat intelligence pool
FROM THE MEDIA: Microsoft says it will give enterprise security operation centers (SOCs) broader access to the massive amount of threat intelligence it collects every day. Through two new services unveiled this week, the enterprise software giant said organizations would be able to proactively protect themselves by seeing the same data Microsoft cybersecurity experts see, and understanding the soft spots in their own defenses.
READ THE STORY: The Register
New Mexico plans to create searchable logs of prison mail
FROM THE MEDIA: Letters written and received by people incarcerated in New Mexico prisons will soon be part of a database expanding mail surveillance in the state’s correctional facilities. The New Mexico Corrections Department is buying equipment from Florida-based company Securus Technologies and installing it at each prison. Adult Prisons Division Director Gary Marciel told legislators the computer software will monitor the mail coming in, scanning every letter for certain words or names to help build a searchable log of the communication incarcerated people have with people outside.
READ THE STORY: Source NM
1st Grain-Load Ship To Leave Ukraine Amid War Passes Inspection En Route To Lebanon
FROM THE MEDIA: The first cargo ship loaded with grain to leave Ukraine since Russia invaded in late February completed inspection Wednesday in the Black Sea off the Turkish coast and has passed through the Bosphorus Strait en route to its final destination of Lebanon. The joint inspection team of the Joint Coordination Center in Istanbul departed the Sierra Leone-flagged vessel named Razoni carrying some 26,500 tons of corn after boarding the ship earlier Wednesday, Turkey’s defense ministry said in a statement.
READ THE STORY: Vigour Times
Geosynchronous Satellites, Orbiting Laboratories
FROM THE MEDIA: On Star Trek, if you want to go from one deck to another, you enter a “turbolift” and tell it where you want to go. However, many people have speculated that one day you’ll ride an elevator to orbit instead of using a relatively crude rocket. The idea is simple. If you had a tether anchored on the Earth with the other end connected to a satellite, you could simply move up and down the tether. Sound simple, so what’s the problem? The tether has to withstand enormous forces, and we don’t know how to make anything practical that could survive it. However, a team at the International Space Elevator Consortium could have the answer: graphene ribbons.
READ THE STORY: Hack a day
Nozomi Networks Labs Report: Wipers and IoT Botnets Dominate the Threat Landscape – Manufacturing and Energy at Highest Risk
FROM THE MEDIA: Since Russia began its invasion of Ukraine in February 2022, Nozomi Networks Labs researchers saw activity from several types of threat actors, including hacktivists, nation-state advanced persistent threats (APTs), and cyber criminals. They also observed the robust usage of wiper malware, and witnessed the emergence of an Industroyer malware variant (used in the cyberattack on Ukraine’s power grid), dubbed Industroyer2, developed to misuse the IEC-104 protocol, which is commonly used in industrial environments.
READ THE STORY: iTwire
How IoT-enabled condition monitoring enables smart ports
FROM THE MEDIA: IoT is continuously growing and expanding to encompass new industry verticals and application areas, and ports are no exception. Whatever the environment, IoT solutions need to have reliable connection to be effective. For most industrial IoT applications, a private network serves as a much more suitable technical foundation than a public network or Wi-Fi.
While every port is different, connectivity has historically always been a challenge. Wired solutions are obviously of limited use in a port scenario, and Wi-Fi is almost always too intermittent for mission-critical industrial applications. The beauty of a private cellular network is that it makes it possible for a port operator to ensure ubiquitous wireless connectivity across the entire operation – land, air and sea – while having full control, without any gaps or blind spots. Beyond the technical advantages, the total cost of ownership over time is unbeatable.
READ THE STORY: Ericsson
Items of interest
Gazprom blames sanctions for limited gas flows to Europe
FROM THE MEDIA: Gazprom said on Wednesday that western sanctions had made the delivery of a crucial turbine for Russian gas supplies to Europe “impossible” in an indication the state-run Russian gas monopoly would not increase flows ahead of a likely energy crunch this fall.
Russia blames the sanctions for preventing the return of the Siemens-manufactured turbine from repairs in Canada, which Gazprom has claimed is forcing it to limit gas via the Nord Stream 1 pipeline.
Gazprom slashed gas flows to 60 per cent of capacity in mid-June, then cut them further to 20 per cent last week as the turbine dispute dragged on.
It said on Thursday that Canadian, UK, and EU sanctions “and the discrepancy between the situation at hand and Siemens’ contractual obligations” meant the turbine could not be delivered.
German chancellor Olaf Scholz said earlier on Wednesday that “absolutely nothing” prevented the installation of the turbine and blamed Russia for the delays in delivering it.
Dmitry Peskov, Russian president Vladimir Putin’s spokesman, said Russia wanted guarantees that Siemens’ UK arm would not shut off the turbine remotely and that Canada would return any future turbines sent there for repairs.
READ THE STORY: FT
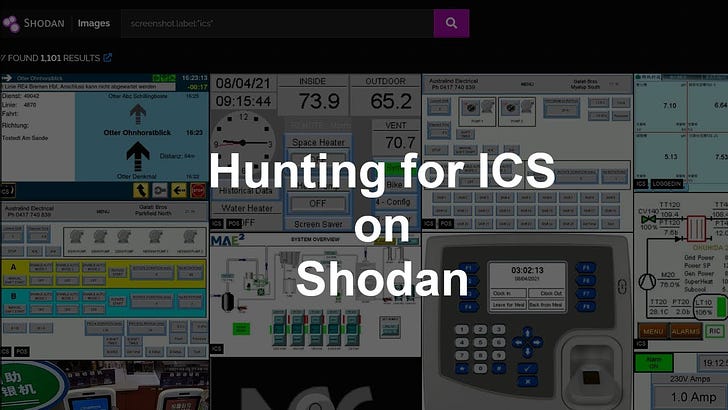
Hunting for ICS and Other Tricks on Shodan (Video)
FROM THE MEDIA: If you are interested in sponsoring my videos, please see: https://forms.gle/aZm4raFyrmpmizUC7 In this video I go over hunting for ICS HMI’s, webcams and exposed SMB systems on Shodan.
DEF CON 29 ICS Village - Hash Saehi - Smart Meters I'm Hacking Infrastructure and So Should You (Video)
FROM THE MEDIA: Why Smart Meters? This is a question Hash is often asked. There's no bitcoin or credit card numbers hiding inside, so he must want to steal power, right? Openly analyzing the technology running our critical infrastructure and publishing the findings is something Hash is passionate about. In the wake of the great Texas freeze of 2021, we can no longer "hope" those in power will make decisions that are in the people's best interest. This talk will present research on the Landis+Gyr GridStream series of smart meters used by Oncor, the largest energy provider in Texas.
These open source products are reviewed from analysts at InfoDom Securities and provide possible context about current media trends in regard to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not specifically endorse any third-party claims made in their original material or related links on their sites, and the opinions expressed by third parties are theirs alone. Contact InfoDom Securities at dominanceinformation@gmail.com