Saturday, July 16, 2022 // (IG): BB //Weekly Sponsor: The Fintel Brief
North Korean Threat Actor Targeting SME Businesses with Ransomware
FROM THE MEDIA: North Korean threat actors are targeting small and mid-sized businesses with ransomware, according to Microsoft Security researchers. The group of actors, going by the name H0lyGh0st, have been developing and conducting cross-national malware attacks for over a year, performing successful attacks as early as September 2021.
As well as using a ransomware payload, the group – tracked by Microsoft as DEV-0530 – maintains an .onion site to communicate with their victims. Utilizing the method of double extortion, their strategy involves encrypting “all files on the target device” and using the file extension .h0lyenc. They then “send the victim a sample of the files” as evidence before demanding a Bitcoin payment in exchange for “restoring access to the files.” Microsoft Threat Intelligence Center (MSTIC) has observed that there is likely overlap between H0lyGh0st and PLUTONIUM (aka DarkSeoul or Andariel), another North Korean-based group.
READ THE STORY: InfoSEC Mag // SCMEDIA
Hackers are targeting industrial systems with malware
FROM THE MEDIA: From the what-could-possibly-go-wrong files comes this: An industrial control engineer recently made a workstation part of a botnet after inadvertently installing malware advertising itself as a means for recovering lost passwords. Lost passwords happen in many organizations. A programmable logic controller—used to automate processes inside factories, electric plants, and other industrial settings—may be set up and largely forgotten over the following years. When a replacement engineer later identifies a problem affecting the PLC, they can discover the now long-gone original engineer never left the passcode behind before departing the company.
READ THE STORY: Arstechnica
Predatory Sparrow: Who are the hackers who say they started a fire in Iran?
FROM THE MEDIA: The BBC reports that Predatory Sparrow, a nominally hacktivist group opposed to Iran's regime, which claimed to have disrupted operations at Iran's Mobarakeh Steel Company on June 27th, has posted video of fires at the facility it claims were caused by its cyberattack. Mobarakeh Steel has minimized the effects of the attack, saying that its operations were not disrupted. CyberScoop reports that Predatory Sparrow has also dumped a set of documents it calls "top secret" and which it claims were taken from the Iranian facilities during the cyberattack. Those claims, as well as the authenticity of the documents themselves, remain unverified.
Given the long-running tension between Iran and Israel, there's been widespread speculation in the Israeli press that Predatory Sparrow, which presents itself as an Iranian dissident group, is operating in the interest of Israeli intelligence services. The Israeli government has begun an investigation into the source of the stories, which may or may not have derived from leaks.
READ THE STORY: The CyberWire
Unity: IronSource malware came from “bad actors who abused the platform”
FROM THE MEDIA: Unity has responded to criticism concerning its merger with IronSource, which has labelled a malware provider by various developers via social media. As discussed in today's This Week In Business, the $4.4 billion deal has sparked complaints stemming from an incident where IronSource's first product was classified as malware. InstallCore was an installation program for internet-based applications launched in 2010, but within a few years it has been blocked by software such as Malwarebytes and even Microsoft's Windows platform for installing unwanted programs.
READ THE STORY: GamesIndustry
Hackers Targeting VoIP Servers By Exploiting Digium Phone Software
FROM THE MEDIA: VoIP phones using Digium's software have been targeted to drop a web shell on their servers as part of an attack campaign designed to exfiltrate data by downloading and executing additional payloads.
"The malware installs multilayer obfuscated PHP backdoors to the web server's file system, downloads new payloads for execution, and schedules recurring tasks to re-infect the host system," Palo Alto Networks Unit 42 said in a Friday report.
The unusual activity is said to have commenced in mid-December 2021 and targets Asterisk, a widely used software implementation of a private branch exchange (PBX) that runs on the open-source Elastix Unified Communications Server.
READ THE STORY: THN
Hackers hit health companies, insurers with increasing regularity
FROM THE MEDIA: In the past few years, some of the region’s largest health care players—including Indiana University Health, Eskenazi Health and Elevance Health (formerly Anthem Inc.)—have seen patient or customer information compromised by hackers. So have some of the area’s smaller hospitals, including Hancock Health and Johnson Memorial.
Hospitals, health insurers and medical clinics are loaded with patient and employee data that can be mined for identity and medical theft. Hackers can shut down computer systems for days or weeks, holding hospitals hostage until ransom is paid. One of the latest attacks became public last month when the Maine Attorney General’s Office disclosed that a software vendor to Indiana University Health and nine other U.S. health systems was attacked.
READ THE STORY: Inside Indiana Business
US Agencies Warn About North Korean Ransomware Attacks on Healthcare Organizations
FROM THE MEDIA: US federal agencies warned about Maui ransomware attacks against healthcare organizations. The joint advisory by the FBI, CISA, and the U.S. Treasury Department warned that North Korean state-sponsored hackers targeted US Healthcare and Public Health Sector organizations (HPH) with the Maui ransomware variant. “North Korean state-sponsored cyber actors used Maui ransomware in these incidents to encrypt servers responsible for healthcare services—including electronic health records services, diagnostics services, imaging services, and intranet services.”
READ THE STORY: CPO MAG
Supermarket chain Spinneys targeted by hackers
FROM THE MEDIA: Supermarket chain Spinneys was attacked by hackers, resulting in delayed openings of its store network in the UAE on Saturday. “Hackers managed to gain access to part of the Spinneys’ network, affecting the function of part of our store operations for a short period of time,” said Tom Harvey, general manager of Spinneys Dubai. “The issue has been dealt with swiftly.” No customer data was accessed in the attack as this is contained securely in a separate system that was not breached, Mr Harvey said.
“We are very grateful to our customers for their patience and apologies if anyone was inconvenienced while shopping in our stores at the time of the hack.” As more businesses adopt hybrid work models and undergo rapid digital transformation to cope with coronavirus challenges, they are also more exposed to cyber threats.
READ THE STORY: The National News
Amazon Handed Ring Videos to Cops Without Warrants
FROM THE MEDIA: THE WEBSITES YOU visit can reveal (almost) everything about you. If you are looking up health information, reading about trade unions, or researching details around certain types of crime, then you can potentially give away a huge amount of detail about yourself that a malicious actor could use against you. Researchers this week have detailed a new attack, using the web’s basic functions, that can unmask anonymous users online. The hack uses common web browser features—included in every major browser—and CPU functions to analyze whether you’re logged in to services such as Twitter or Facebook and subsequently identify you.
Elsewhere, we detailed how the Russian “hacktivist” group Killnet is attacking countries that backed Ukraine but aren’t directly involved in the war. Killnet has launched DDoS attacks against official government websites and businesses in Germany, the United States, Italy, Romania, Norway, and Lithuania in recent months. And it’s only one of the pro-Russian hacktivist groups causing chaos.
READ THE STORY: Wired
Why SolarWinds just may be one of the most secure software companies in the tech universe
FROM THE MEDIA: A house gets burglarized, the owners buy a fancy alarm system. A hurricane knocks a house down, it gets rebuilt bigger and stronger. Indeed, there are a slew of analogies that could be applied to SolarWinds, which just might now be among the most secure software companies in the tech universe. But really, such explanations oversimplify what transpired during the last year and a half, since the company was at the center of arguably the most significant security breach in U.S. history.
“Companies often get religion after they’ been hacked — I used to call it the ‘conversion experience,’” said Jim Lewis, senior vice president and director of the strategic technologies program at the Center for Strategic and International Studies. “And given how important it is for SolarWinds, I’m not surprised they made a big effort to upgrade security.
READ THE STORY: SCMAG
Big Tech firms fail to take down Russian propaganda posts, says Ukraine
FROM THE MEDIA: American Big Tech companies such as Facebook, Instagram, and YouTube restricted or blocked Russian state-run media accounts during the early stages of Russia's invasion of Ukraine. These companies reduced their ad sales in Russia and increased their fact-checking efforts.
However, these firms are now unable to keep pace with the evolving Russian propaganda techniques with the war entering its sixth month. Thousands of tweets, YouTube videos, and other social media posts have been reported as Russian propaganda or anti-Ukrainian hate speech by Ukrainian officials, who claim the companies are now less willing to remove the content.
READ THE STORY: ET
US Legislators attack VPNs for deceptive practices
FROM THE MEDIA: Two US lawmakers have written a letter to the US Federal Trade Commission (FTC) urging it to take action to prevent VPN providers from using ‘deceptive advertising and data collection practices.' They have demanded a crackdown on consumer VPN providers, which they argue are operating in a highly unregulated sector and are essentially conning people into using their services with false and misleading claims.
The letter has been sent by two Democratic lawmakers, Congressional Representative Anna Eshoo (D-California) and Senator Ron Wyden (D-Oregon). It is notable that Wyden, in particular, has leant his name to this letter as he has been a staunch advocate for online freedoms in the past and was especially vocal on topics such as cyber-security and net neutrality during the Trump administration.
READ THE STORY: VPN Compare
Phishing attack ‘highlights flaws in Chinese universities’ cybersecurity’
FROM THE MEDIA: Recent suspected cybersecurity incidents involving higher education providers in China have highlighted how some institutions lack the awareness and the infrastructure to protect themselves against attacks, according to an expert. Students and staff at Northwestern Polytechnical University in Xi’an were recently targeted by phishing emails that contained keywords such as “research” and “assessment” in the subject line. Anyone who clicked the link in the email allowed a Trojan horse program to steal data and personal information.
According to a public statement, the institution immediately informed the police, whose initial investigation indicated that “it was a cyberattack launched by overseas hackers groups and criminals”. The phishing emails did not cause massive a data leak or a major cybersecurity incident, the statement said, but “exposed significant potential risk to the daily work and life of the university”.
READ THE STORY: THE
TikTok's global security chief to step down - internal memo
FROM THE MEDIA: TikTok’s global chief security officer Roland Cloutier, who oversees cyber security, is stepping down from his role but will stay at the company, according to an internal memo seen by Reuters.
“With our recent announcement about data management changes in the U.S., it’s time for me to transition from my role as Global Chief Security Officer into a strategic advisory role focusing on the business impact of security and trust programs, working directly with (CEO) Shou, (ByteDance VP of Technology) Dingkun and other senior leaders,” Cloutier wrote in the memo. TikTok, the video-sharing app owned by China’s ByteDance, hired Cloutier from payroll processing company Automated Data Processing Inc (ADP) in 2020, amid increasing scrutiny from U.S. regulators on the company’s handling of personal data.
READ THE STORY: EuroNews
Counteracting Nation-State-Sponsored Cyberattack Groups
FROM THE MEDIA: US federal agencies warned about Maui ransomware attacks against healthcare organizations. The joint advisory by the FBI, CISA, and the U.S. Treasury Department warned that North Korean state-sponsored hackers targeted US Healthcare and Public Health Sector organizations (HPH) with the Maui ransomware variant. “North Korean state-sponsored cyber actors used Maui ransomware in these incidents to encrypt servers responsible for healthcare services—including electronic health records services, diagnostics services, imaging services, and intranet services.”
READ THE STORY: CPO MAG
DIU seeks a ‘thought leader’ to oversee cutting-edge cyber, tech work for US military
FROM THE MEDIA: With director Michael Brown leaving the federal government, the Defense Innovation Unit at the Department of Defense is looking for a “thought leader” in defense technology transition to replace him.
The DIU, housed within DoD, is charged with keeping the U.S. military on the cutting edge of commercial technology and cybersecurity. The organization is headquartered not in Washington, but Silicon Valley, and its primary mission involves working with nascent startups and other companies on new or innovative forms of technology and acclimating them to the byzantine rules and regulations of doing business with the federal government.
READ THE STORY: SCMAG
This is the most powerful botnet ever seen
FROM THE MEDIA: Web security experts Cloudflare have recently spotted a new botnet which it claims is probably the most powerful ever seen.
Dubbed Mantis, the firm is claiming it evolved from a previously-known botnet - Meris. There are a few things that make Mantis exceptional, according to the researchers. First - it has fewer bots in its network, compared to its counterparts - around 5,000, but it is capable of launching excruciatingly powerful attacks.
The biggest Distributed Denial of Service(opens in new tab) (DDoS) attack on record is 26 million generated requests per second (rps), which Cloudflare says it successfully mitigated. To make things even more impressive - the requests were not done via HTTP, but rather HTTPS - a more expensive type of attacks, given that this type of attack needs extra computing power to establish a secure TLS connection.
READ THE STORY: TechRadar
New hack de-anonymizes website users.
FROM THE MEDIA: Researchers from the New Jersey Institute of Technology have detected a new technique that could allow attackers to de-anonymize website visitors on any major browser. Wired explains that the hack hinges on an attacker convincing a target to load a malicious website that allows the attacker to determine whether that visitor controls a particular public identifier, like an email address or social media account. The attacker can analyze the victim’s browser activity to determine whether they are logged into an account on an array of other platforms like YouTube, Facebook, or Twitter. What’s more, the hack works against every major browser, including Tor, which is known for its focus on anonymity. Reza Curtmola, one of the study authors, explains, “And what makes these types of attacks dangerous is they’re very stealthy. You just visit the website and you have no idea that you’ve been exposed.” Curtmola adds that activists, journalists, and members of minority groups will be likely targets of such attacks.
READ THE STORY: Wired
The human cost: why the financial sector is still rife with social engineering fraud
FROM THE MEDIA: Real-time fraud, also known as authorized push payment (APP) fraud, is a form of social engineering that can cause considerable financial harm. To establish the necessary authenticity, cybercriminals utilize their victims’ personal data obtained through data breaches on the dark web or captured from social media profiles. The more information available to the perpetrators, the more authentic they can appear. In doing so, they contact their victims via telephone and pretend to be a representative of a government agency, an employee of the bank or another official organization. In this way, they can persuade the person called to transfer a certain amount of money to another account. The banks’ security processes can be bypassed because a real account holder triggers the transfer. Multi-factor authentication (MFA) thus offers no protection either.
READ THE STORY: Global Banking Finance
The White House says Russian officials visited Iran to view drones for use in Ukraine
FROM THE MEDIA: Russian officials visited an airfield in central Iran at least twice in recent weeks to view weapons-capable drones it is looking to acquire to use in its war against Ukraine, the White House said. The Biden administration released the intelligence as President Joe Biden met Saturday with leaders of six Arab Gulf countries, plus Egypt, Jordan and Iraq for a regional summit. Biden told fellow heads of state at the summit that the United States was committed to the Middle East and "will not walk away and leave a vacuum to be filled by China, Russia or Iran."
Biden sought to use his appearance at the summit, closing out a four-day trip to the region, to bolster U.S. positioning in the Middle East and knit the region closer together against Iran.
READ THE STORY: NPR
Tehran unveils naval drone division
FROM THE MEDIA: Iran’s navy on Friday unveiled its first division of ships and submarines capable of carrying armed drones, as US President Joe Biden tours the Middle East. The United States and Israel, the sworn enemies of Iran, have previously accused the Islamic republic of using drones and missiles to attack US forces and Israel-linked ships in the Gulf. “The first drone-carrier division of the Iranian navy consisting of ships and submarine units carrying all types of drone for combat, detection and destruction has been unveiled,” state television said.
READ THE STORY: Dawn
Items of interest
Detect, Track, Identify, Defeat to Defend Against Drones
FROM THE MEDIA: The battle to keep Marines and their critical assets safe is constantly evolving. As technology advances, so does the need to field more cutting-edge equipment to counter threats, such as those posed by small unmanned aerial systems.
With these challenges in mind, Program Executive Officer Land Systems is fielding the Installation-Counter small Unmanned Aircraft Systems. Known as I-CsUAS, the system is designed to protect Marine Corps installations by detecting, identifying, tracking and defeating small Unmanned Aircraft Systems.
“The Marine Corps, and DOD in general, required the capability to defend against sUAS years ago,” said Program Manager for Ground-Based Air Defense at PEO Land Systems Don Kelley. “The threat of sUAS is only proliferating every day. The bottom line is, we need to provide this capability to our Marines as rapidly as possible.”
I-CsUAS features an integrated system equipped to carry out all phases necessary to counter small unmanned aerial systems such as commercially-available drones, said Kelley. The system will primarily provide a service to ensure Marines or security forces have the capability to defend installations against sUAS at all times.
READ THE STORY: Military Spot
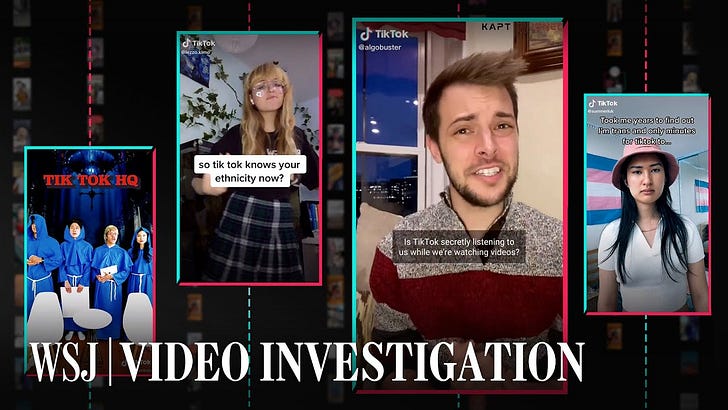
How TikTok's Algorithm Figures You Out (Video)
FROM THE MEDIA: The Wall Street Journal created dozens of automated accounts that watched hundreds of thousands of videos to reveal how the the TikTok algorithm knows you so well A Wall Street Journal investigation found that TikTok only needs one important piece of information to figure out what you want: the amount of time you linger over a piece of content. Every second you hesitate or rewatch, the app is tracking you.
Bluetooth Signals Can Be Fingerprinted And Used To Track Smartphones (Video)
FROM THE MEDIA: University of California San Diego scholars have discovered for the very first time ever that Bluetooth signals may be fingerprinted so that devices can be tracked (and, as a result, individuals). The identification is based on flaws in a Bluetooth chipset introduced during its manufacturing process, which results in a "unique physical-layer fingerprint."
These open source products are reviewed from analysts at InfoDom Securities and provide possible context about current media trends in regard to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not specifically endorse any third-party claims made in their original material or related links on their sites, and the opinions expressed by third parties are theirs alone. Contact InfoDom Securities at dominanceinformation@gmail.com