Monday, July 11, 2022 // (IG): BB //Weekly Sponsor: The Fintel Brief
Defending Aircraft Networks Against Cybersecurity Breaches
FROM THE MEDIA: The aviation industry is both vast and complex. More than 45,000 flights and 2.9 million passengers travel through U.S. airspace every day, requiring high-tech tools and extensive communications networks. All of that data and complexity makes the sector a prime target for cybercriminals. Worryingly, only 49% of non-governmental organizations have fully adopted NIST security standards. As attacks against critical infrastructure and rapidly digitizing industries rise, the aviation industry must reevaluate its standards.
READ THE STORY: Tripwire
Defense Firm Said U.S. Spies Backed Its Bid for Pegasus Spyware Maker
FROM THE MEDIA: A team of executives from an American military contractor quietly visited Israel numerous times in recent months to try to carry out a bold but risky plan: purchasing NSO Group, the cyber hacking firm that is as notorious as it is technologically accomplished.
The impediments were substantial for the team from the American company, L3Harris, which also had experience with spyware technology. They started with the uncomfortable fact that the United States government had put NSO on a blacklist just months earlier because the Israeli firm’s spyware, called Pegasus, had been used by other governments to penetrate the phones of political leaders, human rights activists and journalists.
READ THE STORY: The New York Times
Ignitis Group hit by DDoS attack as Killnet continues Lithuania campaign
FROM THE MEDIA: Lithuanian energy supplier Ignitis Group has been hit with its “biggest cyberattack in a decade.” The group suffered numerous distributed denial of service (DDoS) attacks over the weekend as part of an ongoing campaign by pro-Russia hacking group Killnet against targets in Lithuania, which has supported Ukraine during the war. Ignitis, which serves 1.7m customers in Lithuania, described the attack as “the biggest cyberattack [it has faced] in a decade”. It said: “Strong DDoS attacks [are] causing disruptions to the operation of group websites and the availability of electronic services.”
READ THE STORY: TechMonitor
Russian ‘Hacktivists’ Are Causing Trouble Far Beyond Ukraine
FROM THE MEDIA: Lithuania started on June 20. For the next 10 days, websites belonging to the government and businesses were bombarded by DDoS attacks, overloading them with traffic and forcing them offline. “Usually the DDoS attacks are concentrated on one or two targets and generate huge traffic,” says Jonas Sakrdinskas, acting director of Lithuania’s national cybersecurity center. But this was different. Days before the attacks started, Lithuania blocked coal and metal from being moved through its country to the Russian territory of Kaliningrad, further bolstering its support for Ukraine in its conflict with Russia.
READ THE STORY: Wired
Four Chinese Online Freight Firms Summoned by Authorities
FROM THE MEDIA: China’s Ministry of Transport has formally summoned four domestic online freight corporations on July 8, namely Huolala, Full Truck Alliance, GOGOX and Didi Freight. With the emergence of online freight platforms, a new network of information communication has been established, increasing the matching rates between cars and goods. However, problems have gradually emerged, too. Some drivers have reported that platforms took a cut in transactions at both ends and some value-added orders were to be taken a cut again from the drivers’ end, although the platform already has the standard 11% rebate on the transaction.
READ THE STORY: Pan Daily
Reconciliatory dragon: Easing tech crackdown for strategic reasons
FROM THE MEDIA: Under “Surveillance Capitalism”, digital technology monitor, analyze, and categories user behavior. Technology companies have demonstrated the ability to modify user behavior to suit commercial objectives. States are not aloof to such developments. PRISM demonstrated voluntary cooperation by the United States (US) technology companies with the National Security Agency (NSA). The program conducted global mass data surveillance. The PRC also leverages private technology companies to extract massive foreign data. PRC’s technology products feature backdoors. The National Intelligence Law (NIL) obligates companies to assist PRC authorities in foreign intelligence work.
READ THE STORY: ORF
Why China’s Massive Data Leak Is So Chilling
FROM THE MEDIA: An unidentified person claimed to have accessed a massive Shanghai police database and was hawking its contents—23 terabytes of sensitive information including names, ID numbers, addresses and even detailed criminal case information—for the price of 10 Bitcoins, or about $200,000. It’s unclear how the breach happened. According to some reports, the data had been left more or less exposed since last year. Multiple security researchers who analyzed a small sample of the personal data being sold have said it appears authentic.
READ THE STORY: Bloomberg
Ukrainian cultural artifacts are at risk during the Russian invasion, but digitizing them may offer some protection
FROM THE MEDIA: During the Russian invasion of Ukraine, the possibility of a cyberwar has been a constant threat. The consequences of a breach extend far beyond a threat to national security. They extend and threaten cultural and artistic production — galleries, libraries, archives, museums and universities must be protected.
The invasion of Ukraine has been a hybrid war fought with traditional kinetic weapons alongside cyberattacks. The prelude to the war included widespread attacks on Ukrainian organizations. While there were early reports about the underwhelming performance of Russia’s fabled cyber capabilities, the brutal reality of war does not easily match the precise planning required to stage a cyberattack.
READ THE STORY: The Conversation
FBI director warns China espionage is greatest threat to US and allies
FROM THE MEDIA: FBI director Christopher Wray often uses US speeches and congressional testimony to warn about Chinese espionage, but in a rare move last week he took his message to the UK to raise global awareness of the threat. In an interview in London, Wray called for a continued focus on China even though America and its allies are heavily invested in responding to Russia’s invasion of Ukraine. “We want to make sure that this [China] threat, which in many ways is the greatest, broadest, most comprehensive, long-term threat that we and our allies face, stays top of mind,” Wray told the Financial Times.
READ THE STORY: FT
Ukraine horror: Russian hackers 'gain access' to front-line plans in worrying twist to war
FROM THE MEDIA: The news comes as Russian forces advance in eastern Ukraine, with the weekend seeing intense shelling and missile fire rock the town of Siversk. However, new information suggests the war is not being solely fought at a conventional level as cyber-warfare continues to play its role in the so-called “special operation” in Ukraine. The latest case of Russian cyber-warfare comes from a group named RaHDIt, and a pro-Moscow unit in Ukraine named Beregini. The pair claim to have obtained secret operational documents about the plans and actions of the Ukrainian army, as well as the current situation on the front line of the conflict.
READ THE STORY: Express
Pro-Russia Group Claims It Hacked Official Congress Website
FROM THE MEDIA: A pro-Russia group claimed responsibility for hacking the official website for the U.S. Congress late Thursday, replacing the page with a photo of President Joe Biden looking “puzzled,” Fox News reported. The group “Killnet” claimed it hacked the website, causing it to shut down for about 45 minutes Thursday evening, according to Fox News. Users who tried to access congress.gov were either given an ‘Error 522’ or ‘Connection timed out’ notice, and the page also showed a pop-up image of President Biden giving a puzzled facial expression, according to CNN.
READ THE STORY: NT
EDF cyber security ‘shortfalls’ see energy giant placed under further monitoring
FROM THE MEDIA: FRENCH Power Giant EDF is being scrutinized by the UK’s Office for Nuclear Regulation (ONR) after it identified shortfalls in the firm’s cyber security defenses. Following a number of routine inspections over the past year, the regulator said it had found “shortfalls in governance, risk and compliance and certain technical controls” at EDF and that it was putting the company under “enhanced attention”, The Telegraph reported. EDF is upgrading its IT systems and a restructuring its internal security department, which reportedly contributed to the increased monitoring.
READ THE STORY: CITY A.M.
Cyber Sewage Attack? Hackers Show How Easy It Is to Flood Israel
FROM THE MEDIA: Hackers have discovered that the sewer system in the Israeli coastal town of Or Akiva is completely exposed on the web, without any basic protection. Israeli cyber researchers say that many industrial systems in Israel and abroad are exposed to similar hacks – which allow hackers to gain access, take over systems and cause physical damage.
On Thursday, hackers published a photo showing the graphic interface of the sewage pump control system in Or Akiva. An examination revealed the interface was completely undefended and did not even require a password and the website did not use the Hypertext Transfer Protocol Secure.
READ THE STORY: Haaretz
Why India-Israel Cyber Partnership Worries Pakistan & China
FROM THE MEDIA: In a recent seminar hosted by a Pakistan-based think tank, it was highlighted yet again that Islamabad is concerned with growing India-Israel cyber cooperation. The discussants stressed greater Iran-Pakistan cooperation in cybersecurity, information technology (IT), and telecom domains, to benefit from mutual experiences, and mutual threat perceptions. This is not the first instance when concern over the India-Israel partnership has been aired in Pakistan. In July 2021, the Foreign Office Islamabad released a statement raising “serious concern over media reports about India allegedly eavesdropping on foreigners, including PM Imran Khan, using Israeli spyware Pegasus”.
READ THE STORY: Modern Diplomacy
India: CERT-In takes steps to safeguard key infrastructure from hackers across border
FROM THE MEDIA: Being the nation's premier cyber agency, CERT-In was formed in 2004 under IT Act, 2000 Section (70B), under the IT Ministry. Since then, the nature of cyber attacks has changed drastically, especially in the last couple of years in the pandemic, and countries like China, North Korea, Pakistan and others are busy supporting armies of hackers who aim to target India. CERT-In reported more than 2.12 lakh cybersecurity incidents in January-February this year -- compared to more than 14.02 lakh incidents for 2021. Replying to a question in the Rajya Sabha in March, Minister of State for Electronics and IT, Rajeev Chandrasekhar revealed these figures, without specifying the origin of the cyber attacks.
READ THE STORY: Socialnews XYZ
Canada telecom execs summoned after wide service outage
FROM THE MEDIA: The federal industry minister said Sunday he is summoning telecom executives following an outage at Rogers Communications Inc. that disrupted mobile and Internet services across Canada, hampering several crucial services. In a statement, Francois-Philippe Champagne said he would meet with Tony Staffieri, Rogers' chief executive officer, and other telecom leaders to discuss improving ''the reliability of networks across Canada.″ He called the failure "unacceptable." The widespread disruption, which began Friday morning and lasted at least 15 hours, paralyzed communications across sectors including health care, law enforcement and the financial industry. Many 911 services couldn't receive incoming calls, several hospitals reported services affected, and debit card transactions were paused.
READ THE STORY: TechXplore
How data on a billion people may have leaked from a Chinese police dashboard
FROM THE MEDIA: Details have emerged on how more than a billion personal records were stolen in China and put up for sale on the dark web, and it all boils down to a unprotected online dashboard that left the data open to anyone who could find it. More than 23TB of details apparently stolen from the Shanghai police was put up for sale on the underground Breach Forums by someone with the handle ChinaDan for 10 Bitcoin ($215,000 at time of writing). The data collection included names, addresses, birthplaces, national ID numbers, cellphone numbers, and details of any related police records.
READ THE STORY: The Register
BlackCat (aka ALPHV) ransomware is increasing stakes up to $2.5 million in demands
FROM THE MEDIA: The notorious cybercriminal syndicate competes with Conti and Lockbit 3.0. They introduced an advanced search by stolen victim’s passwords, and confidential documents leaked in the TOR network. Resecurity (USA), a Los Angeles-based cybersecurity company protecting Fortune 500 companies, has detected a significant increase in the value of ransom demand requests by the notorious Blackcat ransomware gang. According to experts, the notorious cybercriminal syndicate actively competes with Conti and the updated Lockbit 3.0, and recently introduced a search by stolen victim’s passwords, and confidential documents leaked in the TOR network.
READ THE STORY: HelpNetSecurity
Ransomware Attack Hits French Telecoms Firm
ANALYST NOTE: Annnnnd another one - is the current attack on CIKR a trend?
FROM THE MEDIA: French telecoms operator La Poste Mobile has alerted customers that their data may have been compromised in a ransomware attack that targeted the company’s administrative and management systems on July 4.
The attack, believed to have been carried out by the LockBit ransomware group, took the company’s systems offline as it attempted to minimize damage. Seven days later, its website is still offline and visitors are greeted by a statement in French telling customers to be wary of targeted cyber-attacks.
“Our initial analysis shows that our servers, which are essential to the operation of your mobile line, have been well protected. However, it is possible that files on the computers of La Poste Mobile employees have been affected. Some of these files may contain personal data,” said the statement.
READ THE STORY: InfoSec Mag
Nichirin-Flex USA Ransomware Attack
FROM THE MEDIA: Nichirin-Flex USA, the U.S. subsidiary of Japanese automotive hose manufacturer Nichirin, has been impacted by a ransomware attack. The attack occurred recently, and the company reacted as soon as it detected the unauthorized access on its network and moved operations into manual mode. Looking into the Nichirin-Flex USA security incidence for Digital Journal is Craig MacDonald, Vice President of Product Management at BackBox.
According to MacDonald the cybersecurity incident provides a textbook example of how to organise a cyberattack, with some of the flaws within institutions being exposed. He states: “This attack on Nichiren-Flex USA, a subsidiary of Japan-based Nichiren, is a perfect example of how cyberattacks can go beyond their initial target and affect other vital aspects of the supply chain. In this case, the target is a manufacturer of motorcycle and car parts that is critical to distribution, creating supply chain delays in production and fulfilment.”
READ THE STORY: Digital Journal
The importance of maintaining effective machine-identity security
FROM THE MEDIA: In some high-profile security incidents, such as those experienced by SolarWinds and Kaseya, the software supply chain was leveraged as a conduit for attacks due to machine-identity and code-signing mismanagement. During the past two years, the COVID-19 pandemic has added further complexity to the use of machine identities. A rapid shift to the cloud, remote work practices, increased reliance on Internet of Things (IoT) devices, and mobility have all served to change the enterprise IT landscape. Unfortunately, however, in many cases security became an afterthought. It’s become clear that robust machine-identity management is now a crucial tool for organizations racing to catch up and protect their corporate assets
READ THE STORY: ITwire
Items of interest
Top Threats You Need to Know to Defend Your Cloud Environment
FROM THE MEDIA: As organizations move critical applications and data to the cloud, these resources have come under increasing attack. Adversaries view cloud environments as soft targets and continue to refine tactics and tradecraft to exploit the vulnerabilities and misconfigurations within them.
Though this attack trend was underway before the COVID-19 pandemic, the need to support mostly remote, distributed workforces increased organizations’ reliance on cloud resources — which in turn amplified adversaries’ focus on exploiting the cloud. Attackers were circling throughout 2021, often attempting to compromise cloud infrastructure and assets by exploiting misconfigurations and stolen user credentials.
In “Protectors of the Cloud: Combating the Rise in Threats to Cloud Environments,” we outline common attack vectors adversaries use to breach cloud environments, including credential theft, vulnerability exploitation, abuse of cloud service providers, exploitation of misconfigured image containers, and use of cloud services for hosting malware and command and control.
READ THE STORY: CrowdStrike
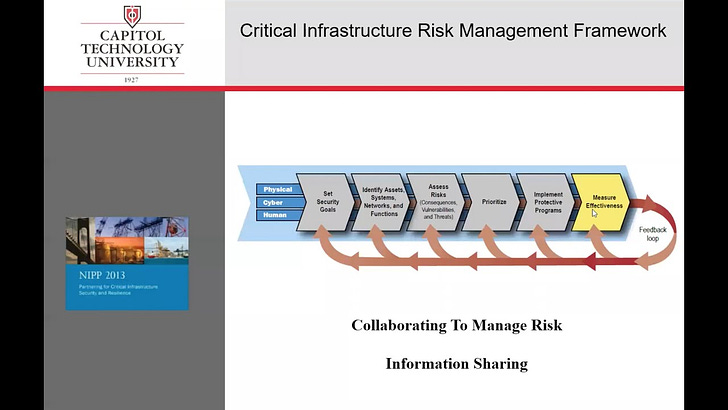
Critical Infrastructure 101 (Video)
FROM THE MEDIA: In this lecture on Critical Infrastructure, Dr. Martin discusses the importance of industrial control systems and strategies to protect them from cyberthreats, acts of terrorism, extreme weather and more. He explores our interdependent urban environments and details the 16 Critical Infrastructure Sectors. Finally, he provides an overview of current Security and Assessment Activities.
Can the United States Curb the Threat From Cyberspace?(Video)
FROM THE MEDIA: Cyberattacks dominated U.S. headlines in 2021, sowing panic and chaos and exacting a huge financial toll on governments, businesses, and citizens alike. As the problem gets worse, policymakers are struggling to respond. What is the United States’ cyberstrategy getting wrong? And what is at stake if the country fails to mount a better defense against this unrelenting threat?
These open source products are reviewed from analysts at InfoDom Securities and provide possible context about current media trends in regard to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not specifically endorse any third-party claims made in their original material or related links on their sites, and the opinions expressed by third parties are theirs alone. Contact InfoDom Securities at dominanceinformation@gmail.com