Daily Drop (1297)
05-13-26
Wednesday, May 13, 2026 // Buy Bob a Coffee // Ghostwire
The Iran War's Forgotten Front: Global Food Insecurity and the Limits of U.S. Aid
Bottom Line Up Front (BLUF): Sam Vigersky argues that nine weeks of Operation Epic Fury have produced a cascading global hunger crisis while U.S. humanitarian response has collapsed. The anchoring numbers: $25 billion in Pentagon costs versus $49 million in State Department humanitarian spending (510:1); a proposed $200 billion war supplemental with zero humanitarian allocation; and $5.4 billion already appropriated to State's new Bureau for Disaster and Humanitarian Response sitting unspent. Downstream effects include 1.24 million Lebanese in acute hunger (up 42% in six months), WFP projections of 45 million additional people facing acute food insecurity if the war runs through June, third-year famine in Sudan, terminated U.S. support to Afghanistan, Somalia, and Yemen, and Strait of Hormuz disruption forcing aid supply chains onto vastly longer routes. Vigersky calls for a UN-coordinated Hormuz humanitarian corridor, reinstated aid to the three terminated recipients, and aggressive deployment of the appropriated $5.4 billion.
Analyst Comments: This is advocacy from a credentialed practitioner — Vigersky was senior humanitarian advisor to the U.S. ambassador to the UN — and the framing reflects the aid-policy community’s perspective. That doesn’t undercut the data, which traces to IPC classifications, WFP projections, and UN appeal figures that are independently sourced. But the policy frame (that the binding constraint is U.S. political will rather than operational access or recipient-country governance) is one legitimate lens among several. The unspent $5.4 billion is the piece’s strongest data point — money appropriated by Congress for exactly this purpose, sitting in a bureau created as the “center of excellence” for complex humanitarian response, during a textbook trigger event. The 2003 Iraq comparison ($2.5 billion in early appropriations, roughly $4.5 billion in 2026 dollars) is well-chosen because it isolates the policy break from operational reality: the U.S. has done this before, recently, under a Republican administration, during a war it was actively prosecuting. The 510:1 ratio and Easter-candy comparison are rhetorically sharp but framing rather than analysis — military and humanitarian budgets aren’t substitutes, and consumer spending isn’t a meaningful baseline.
READ THE STORY: CFR
What Does SOUTHCOM's New Autonomous Warfare Command Herald?
Bottom Line Up Front (BLUF): In a War on the Rocks podcast with Ryan Evans, SOUTHCOM commander Gen. Frank Donovan lays out the rationale for the command's newly established Autonomous Warfare Command. The aim is to move drones and autonomous systems beyond tactical experimentation and tie them to strategic effect across the Western Hemisphere — disrupting cartel networks now designated as foreign terrorist organizations, deepening cooperation with regional partners, and expanding SOUTHCOM's ability to see, decide, and act across a region defined by maritime expanse, dense littorals, and limited persistent ISR.
Analyst Comments: This is a primary-source conversation with the combatant commander, which gives it real value but also means it reads as command-level messaging rather than independent assessment. Donovan is making the case for a capability his command just stood up, so the framing leans toward coherence over institutional friction. The choice of SOUTHCOM as the home for an Autonomous Warfare Command is itself the story. SOUTHCOM has historically been the lowest-priority geographic combatant command for force allocation, with chronic ISR, lift, and platform shortfalls. Standing up an autonomy-focused command there reflects two converging shifts: the cartel FTO designations have elevated SOUTHCOM’s mission into the counter-terrorism authorities and funding space, and autonomous systems offer a way to generate coverage across maritime and jungle terrain that crewed platforms cannot economically sustain. The featured image — a Sail drone Voyager USV during Operation Windward Stack — signals that maritime autonomous surface vessels are central to the concept, consistent with the Replicator-era push toward attritable, distributed sensing in under covered waters.
READ THE STORY: War on the Rocks
The Missing Navies: The Hormuz Crisis and the Limits of America's Indo-Pacific Partnerships
Bottom Line Up Front (BLUF): Jean-Loup Samaan argues that the closure of the Strait of Hormuz is fundamentally an Asian crisis — over 80% of Hormuz-transiting crude and LNG goes to Asia, 95% of Japan's oil imports and 70% of South Korea's come from the Persian Gulf, the Philippines declared a national energy emergency in March, and Seoul deployed a $17 billion supplementary budget — yet Asia is almost entirely absent from coalition discussions on reopening the waterway. When President Trump urged South Korea to join the U.S.-led mission after a Korean vessel was fired on May 4, Seoul replied it would "review" the proposal. Samaan argues that an Asian-led mission would be both more militarily robust (Asian navies surpass European counterparts in submarines, surface combatants, maritime patrol aircraft, and especially mine warfare, where Japan's capability is among the strongest in any U.S. ally) and more politically effective at signaling neutrality, since most Asian partners have avoided taking sides and Iran has reportedly allowed Indian, Chinese, and Pakistani vessels to transit. The absence reflects diplomatic fragmentation, weak multilateral habits, and a preference for bilateral arrangements — India's solo Operation Urja Suraksha and China's direct deal with Tehran being the clearest examples. Samaan reads this as a failed dry run for the kind of coalition-building Washington would need in a Taiwan Strait or South China Sea contingency.
Analyst Comments: Samaan’s credentials — Middle East Institute at NUS, Atlantic Council, former NATO Defense College and French MoD — give him standing in both the Gulf maritime security and Indo-Pacific alliance debates, which is rarer than it sounds and matters for an argument that bridges the two regions. The strongest analytical move is the operational case for Asian naval contribution. The mine warfare point is the one that should land hardest with planners: reopening the Strait is fundamentally a mine countermeasures problem, and Japan’s JMSDF mine warfare fleet is genuinely among the most capable in the world, with institutional muscle going back to clearing Korean War-era mines. South Korea, Singapore, and Australia bring credible additional capability. The contrast with European navies, which have lost roughly a third of their principal surface combatants since the Cold War and are oriented toward Russia-focused air and land scenarios, is real and underappreciated in trans-Atlantic discussions of the mission. The neutrality argument is also well-constructed: Iran’s tolerance of Indian, Chinese, and Pakistani transit gives Samaan empirical grounding for the claim that an Asian mission would face lower escalation risk than a European one, which advocates of a French-led coalition tend to wave past.
READ THE STORY: War on the Rocks
Trump's China Trip Revives Debate on Global AI Guardrails
Bottom Line Up Front (BLUF): President Trump is expected to raise AI guardrails with Xi Jinping during this week's Beijing visit, with U.S. officials describing the goal as opening a possible channel of communication on AI matters. The framing is that both governments have a shared interest in preventing AI weaponization and rogue-system release, but neither has demonstrated it can sustain a productive dialogue or trust the other to abide by agreed norms. The visit comes amid contradictory U.S. signaling: export controls to slow Chinese AI progress, accusations last month that China runs "industrial-scale" campaigns to distill American models, and a monthlong White House back-and-forth on regulating frontier-model rollouts after a year of opposing such regulation. Notably absent from the 16-executive delegation accompanying Trump (Musk, Cook, others) are CEOs from leading AI firms. Former State Department official Melanie Hart (Atlantic Council) notes that Biden-era AI safety talks were used by Beijing primarily for intelligence collection, with non-technical foreign ministry representatives, and frames the trip as a test of whether future engagement will be substantive or symbolic — "we want to see the technical experts showing up at the table."
Analyst Comments: The Axios framing is accurate but soft on the central contradiction, which is worth surfacing more directly. Both governments are simultaneously developing AI-enabled offensive cyber capabilities and proposing to negotiate restraint around those capabilities. The piece notes Anthropic's November attribution of a Claude-automated Chinese espionage campaign against ~30 organizations and the NSA's testing of Mythos for offensive use, but treats this as background tension rather than the structural problem it actually is. Arms-control analogues are instructive: the nuclear, chemical, and biological weapons regimes that succeeded did so when both sides had concluded the capability was net-negative to possess (or when verification regimes made cheating costly). Neither condition holds for AI-enabled cyber operations today. Both Washington and Beijing currently assess offensive AI cyber as a strategic asset they are racing to develop, not a liability to constrain. That structural reality makes the "shared interest in guardrails" framing aspirational rather than operative.
READ THE STORY: Axios
TeamPCP Open-Sources Shai-Hulud Worm on GitHub
Bottom Line Up Front (BLUF): Security firm Ox spotted two repositories on Tuesday with a note reading “Shai-Hulud: Open Sourcing The Carnage. Is it vibe coded? Yes. Does it work? Let results speak. Change keys and C2 as needed. Love - TeamPCP.” Fork counts rose during reporting from 1 and 31 to 5 and 39, with Ox warning that “independent threat actors have already begun modifying it and expanding its reach.” A GitHub user named “agwagwagwa” has already added FreeBSD support via pull request, and Ox notes thematic overlap (cat-themed repos) suggesting possible group affiliation. Shai-Hulud targets npm packages, harvests AWS/GCP/Azure/GitHub credentials, exfiltrates them to new GitHub repos, and publishes poisoned code to propagate; failed infections sometimes trigger local environment wipes. The repositories have been live at least 12 hours without GitHub intervention.
Analyst Comments: The MIT License choice is not casual — it's the license most aggressively designed to encourage forks, modifications, and commercial reuse without attribution or copyleft constraints. TeamPCP is explicitly inviting downstream actors to build variants ("Change keys and C2 as needed") rather than gating capability behind affiliate programs or revenue-sharing arrangements that typify ransomware-as-a-service operations. The strategic logic for the operator is worth thinking about: they either believe they've extracted maximum value from the existing tooling and are seeding chaos for its own sake, are attempting to muddy attribution by flooding the ecosystem with variants, or are signaling a pivot to a successor capability while keeping the old one alive as a distraction. The "vibe coded" line — slang for AI-assisted code generation — suggests the worm's authors view the underlying engineering as low-effort to reproduce, which fits a scenario where they've moved on to something more capable.
READ THE STORY: The Register
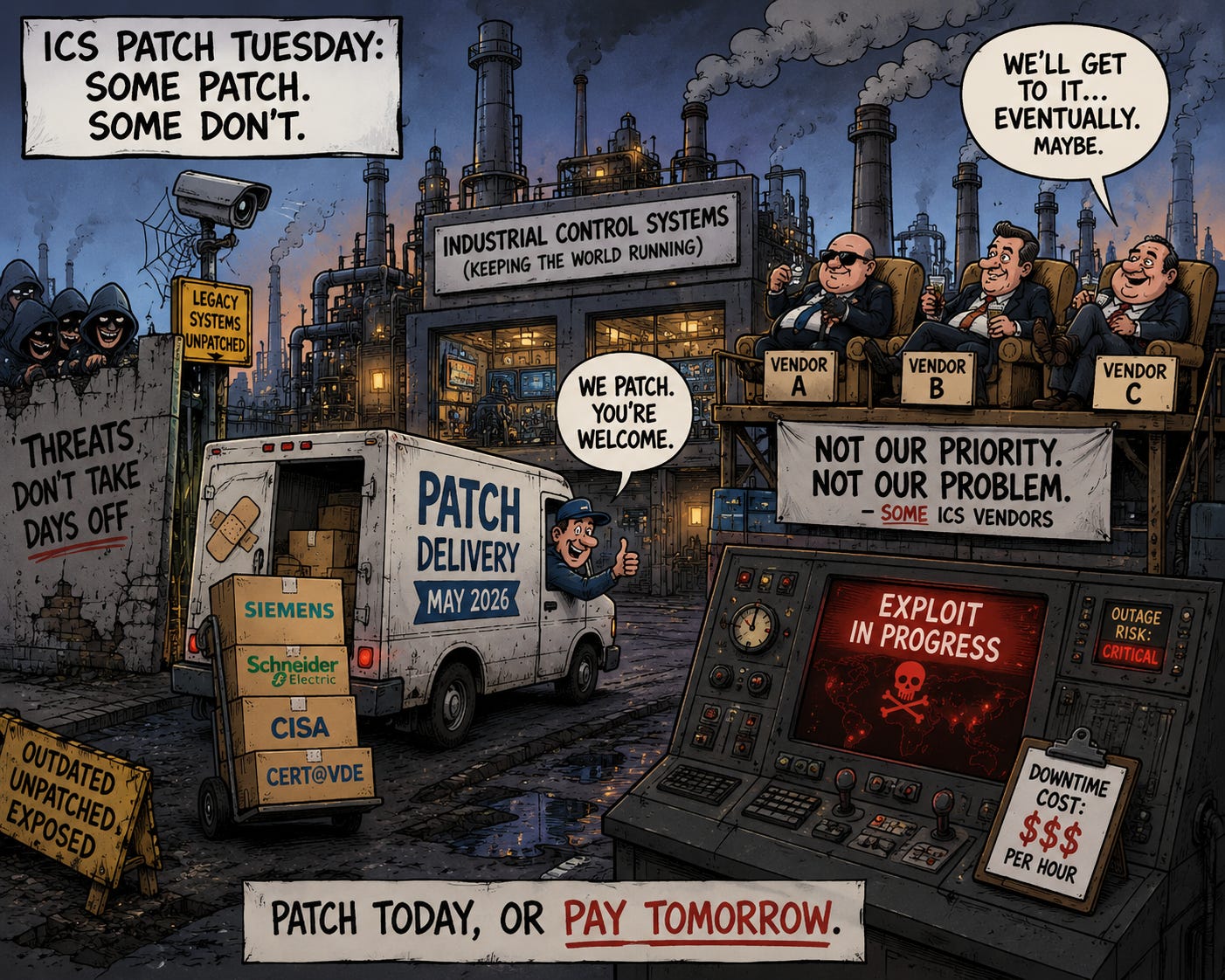
ICS Patch Tuesday: New Advisories From Siemens, Schneider, CISA
Bottom Line Up Front (BLUF): The May 2026 Patch Tuesday cycle for industrial control systems is unusually thin, with only Siemens, Schneider Electric, CISA, and Germany's CERT@VDE publishing new advisories. Siemens leads with 18 advisories, including critical issues in Sentron 7KT PAC1261 Data Manager (device takeover), Simatic S7 PLC web server (XSS), Ruggedcom Rox (root command execution plus old third-party component flaws), ROS# (arbitrary file access), Simatic CN4100 (over 300 third-party component vulnerabilities), and Opcenter RDnL (missing authentication). High-severity RCE bugs were also patched in Simcenter Femap, Teamcenter, gPROMS Web Applications Publisher, and Ruggedcom Rox. Notably, Siemens flagged that its Ruggedcom APE1808 is affected by the recently disclosed Palo Alto Networks PAN-OS vulnerability currently being exploited in the wild, possibly by Chinese state-sponsored actors. Schneider Electric issued four advisories covering high-severity flaws in EcoStruxure Panel Server (sensitive information exposure), EasyLogic T150 and Saitel DP RTU (unauthorized file access), and several EasyLogic/PowerLogic/Easergy/EcoStruxure products (session hijacking). CISA published advisories covering ABB, Subnet Solutions, Fuji Electric, Maxhub, and Johnson Controls products. CERT@VDE addressed a medium-severity DoS flaw in Codesys Modbus.
Analyst Comments: The vendor participation gap is the part of this Patch Tuesday worth flagging. ICS Patch Tuesday cycles typically include advisories from a much broader vendor set — Rockwell Automation, ABB (directly), Honeywell, Mitsubishi Electric, Emerson, Yokogawa, and others routinely contribute. May 2026's narrow participation (effectively two vendors plus CISA aggregation) is anomalous. There are several possible readings: vendors are holding disclosures for coordinated release tied to ongoing CISA advisories, the geopolitical climate is pushing some vendors toward private notification rather than public disclosure, or this is simply a quiet month. None of these are reassuring, particularly given that ICS-targeting activity by Iran-linked groups (BAUXITE / Cyber Av3ngers) and Russia-aligned actors has continued through the spring.
READ THE STORY: Security Week
GemStuffer Abuses 150+ RubyGems to Exfiltrate UK Council Data
Bottom Line Up Front (BLUF): Socket researchers have identified a campaign dubbed GemStuffer in which over 150 RubyGems packages are being used not for malware distribution but as an exfiltration channel for data scraped from UK local government democratic services portals — specifically the public-facing ModernGov portals used by Lambeth, Wandsworth, and Southwark councils. The mechanics are deliberate: scripts fetch hardcoded council portal URLs, package the HTTP responses (committee meeting calendars, agenda items, linked PDFs, officer contact information, RSS feeds) into valid .gem archives, then publish those archives to RubyGems using embedded API credentials. Retrieval is trivial — an attacker runs gem fetch against the package name and version. Two variant techniques have been observed: one that creates a temporary credential environment under /tmp and uses the gem CLI, another that bypasses CLI entirely and POSTs the archive directly to the RubyGems API. The packages have little to no download activity and "repetitive, noisy, and unusually self-contained" payloads, indicating that mass developer compromise is not the goal. The campaign emerged as RubyGems temporarily disabled new account registration following a separate "major malicious attack" — Socket notes the two share an abuse pattern but does not confirm linkage. Socket assesses possibilities including registry spam, a proof-of-concept worm, an automated scraper misusing RubyGems as cloud storage, or a deliberate test of package registry abuse to "demonstrate capability against government infrastructure."
Analyst Comments: This is one of the more unusual supply-chain stories of recent months, less because of the immediate damage (modest, given the data is publicly accessible) and more because of what it signals about how attackers are reconceptualizing package registries. The standard threat model for npm, PyPI, and RubyGems treats them as distribution channels — adversaries publish malicious packages to compromise downstream developers who install them. GemStuffer inverts that model: the registry is being used as a free, anonymous, durable storage and retrieval layer with global CDN distribution, version control, and no abuse review at upload time. The package contents are the payload, but the targets aren't developers who install them — they're attackers who fetch them.
READ THE STORY: THN
Items of interest
Thousands of Vibe-Coded Apps Expose Corporate and Personal Data on the Open Web
Bottom Line Up Front (BLUF): RedAccess researchers found more than 5,000 publicly accessible AI-generated web apps built with platforms including Lovable, Replit, Base44, and Netlify. Roughly 40% reportedly exposed sensitive personal or corporate data, including medical information, financial records, strategy documents, chatbot logs, and customer details..
Analyst Comments: This is shadow IT with a launch button. The issue is not just buggy AI code; it is non-technical users deploying internet-facing apps without authentication, access controls, or security review. The parallels to exposed S3 buckets are obvious: vendors can blame user configuration, but insecure defaults and weak guardrails become a platform problem at scale. Expect attackers to mine these apps for credentials, customer data, internal documents, admin access, and phishing infrastructure.
READ THE STORY: Wired
Vibe Coding is a Trap (What Senior Devs See That You Don't) (Video)
FROM THE MEDIA: Are you falling for the "vibe coding" trend? In this video, we expose the truth behind vibe coding and reveal why it can be a trap for aspiring developers. You'll learn what is vibe coding, the hidden pitfalls, and what senior devs see that you don't.
The “vibe coding” mind virus explained… (Video)
FROM THE MEDIA: Let’s take a look at the latest craze in the programming world known as "vibe coding". Learn how to vibe code properly and look into the pros and cons of AI coding techniques.
The selected stories cover a broad range of cyber threats and are intended to help readers frame key publicly discussed threats and improve overall situational awareness. InfoDom Securities does not endorse any third-party claims made in its original material or related links on its sites; the opinions expressed by third parties are theirs alone. For further questions, don’t hesitate to get in touch with InfoDom Securities at dominanceinformation@gmail.com.