Daily Drop (1296)
05-12-26
Tuesday, May 12, 2026 // Buy Bob a Coffee // Ghostwire
Apple’s May 2026 Security Release Fixes 84 CVEs Across iOS and macOS, Including AI-Assisted Kernel Vulnerability Discovery
Bottom Line Up Front (BLUF): Apple released a major proactive security update covering iOS, iPadOS, macOS, watchOS, tvOS, and visionOS, fixing roughly 84 unique CVEs across platforms. The release includes multiple kernel vulnerabilities, sandbox escapes, WebKit flaws, Wi-Fi code execution bugs, and network-facing mDNSResponder issues. Most notably, Apple credited Calif.io “in collaboration with Claude and Anthropic Research” for discovering a macOS kernel integer overflow vulnerability, marking one of the clearest public examples yet of AI-assisted kernel vulnerability discovery entering mainstream defensive security workflows.
Analyst Comments: Security researchers have used automation and symbolic tooling for years, but Apple explicitly crediting Claude and Anthropic Research on a kernel vulnerability changes the conversation. We are now seeing both sides of the AI security race materialize simultaneously: offensive AI-assisted exploit development and defensive AI-assisted vulnerability discovery. The important nuance is that this was not a toy bug in an obscure parser. CVE-2026-28952 is a macOS kernel integer overflow. That means AI-assisted research is now contributing to discovery inside one of the most security-sensitive layers of a major operating system. Separate WebKit credits involving Nicholas Carlini and Claude reinforce that this is not a one-off experiment.
READ THE STORY: Cyber Centre (Canada)
Belgium Adopts New National Cyber Crisis Response Plan Under NIS2 Framework
Bottom Line Up Front (BLUF): Belgium formally adopted a revised national cyber crisis response plan through Royal Decree, replacing its 2017 framework to better align with modern cyber threats, NIS2 requirements, and EU-level crisis coordination. The updated framework establishes national procedures for managing major cyber incidents affecting critical sectors, public administration, healthcare, and other nationally significant infrastructure.
Analyst Comments: The important detail here is not just that Belgium updated a response plan—it embedded the framework into national law and explicitly tied it to NIS2 obligations and civil security authorities. European governments increasingly view cyber incidents as national crisis management problems rather than isolated IT security events. That changes who gets involved during major incidents: not just CERT teams and CISOs, but emergency management agencies, national security bodies, regulators, infrastructure operators, and cross-border EU coordination mechanisms.
READ THE STORY: Cyber Centre (Belgium)
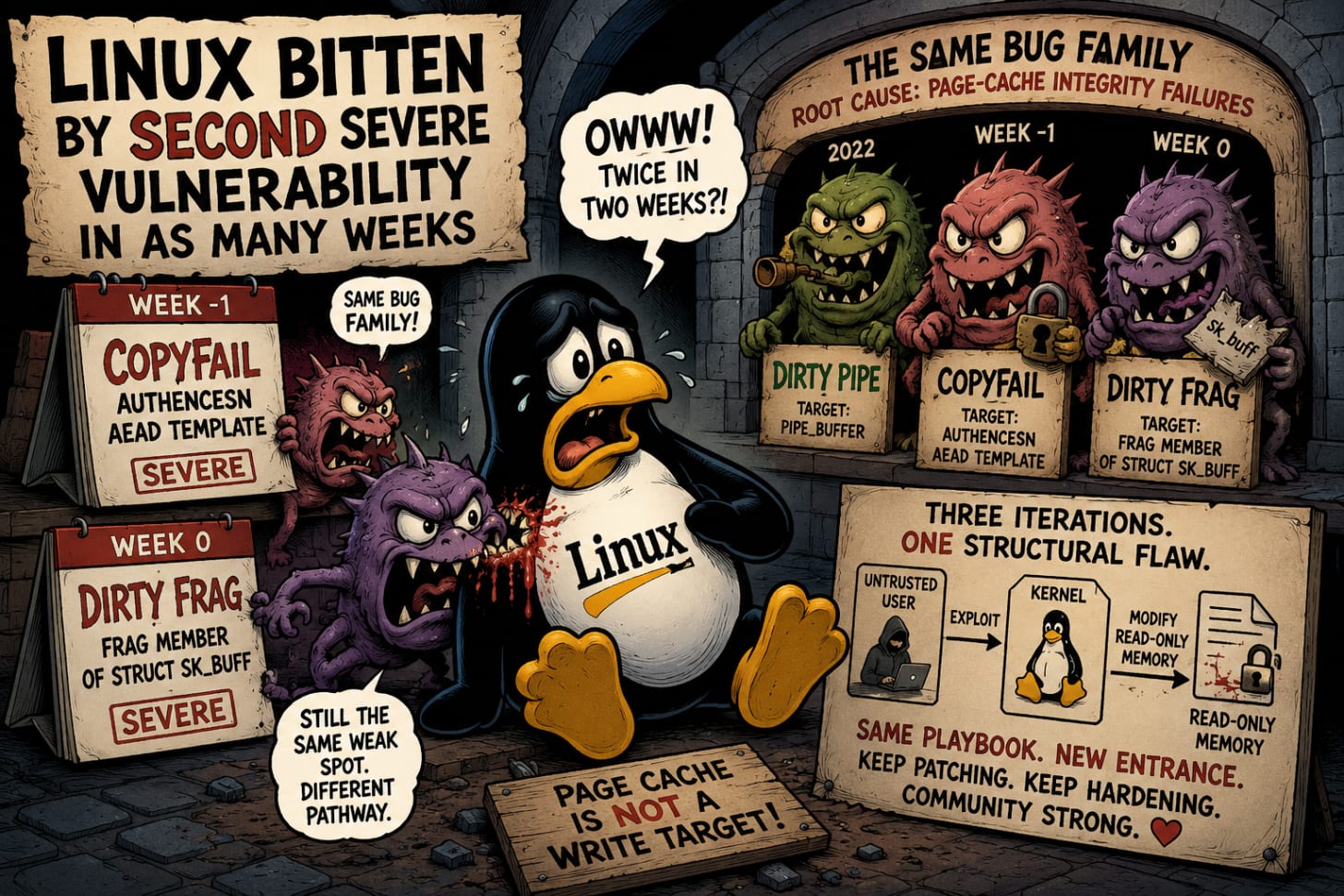
Linux bitten by second severe vulnerability in as many weeks
NOTE:
This is the second severe Linux local privilege escalation vulnerability in two weeks. CopyFail dropped the week prior; Dirty Frag dropped this week. Both belong to the same bug family as Dirty Pipe (2022) — flaws in the kernel’s handling of page caches that allow untrusted users to modify read-only memory. Dirty Pipe targeted pipe_buffer. CopyFail attacked the authencesn AEAD template. Dirty Frag goes after the frag member of struct sk_buff. Three iterations of the same structural attack pattern against page-cache integrity, each one targeting a different kernel pathway.
The kernel’s page-cache subsystem keeps producing usable local-root primitives, and the patches keep being narrow fixes to specific call paths rather than structural hardening of the underlying memory model. For defenders running multi-tenant Linux, the operational question is no longer whether another one is coming. It is how to design under the assumption that local-root primitives in this class will continue to surface. The exploit pattern — splice() planting a reference to a read-only page-cache page into a writable kernel structure — is the recurring move. Hardening that pattern at the design level, rather than chasing each new CVE, is the structural defense conversation worth having.
Bottom Line Up Front (BLUF): A new Linux kernel privilege escalation vulnerability called Dirty Frag (CVE-2026-43284 and CVE-2026-43500) allows low-privilege users — including those inside virtual machines and containers — to gain root access on virtually every major distribution. Discovered by researcher Hyunwoo Kim, the exploit was leaked online three days ago, and Microsoft has reported signs of attackers experimenting with it in the wild. Patches are available for Debian, AlmaLinux, and Fedora.
Analyst Comments: Dirty Frag’s operational profile is what makes it dangerous: the exploit is deterministic, causes no crashes, and works reliably across distributions when both CVEs are chained. Either vulnerability alone is unreliable — CVE-2026-43284 (esp_input() on the IPsec ESP receive path) can be neutralized by AppArmor configurations that block untrusted namespace creation, and CVE-2026-43500 (rxkad_verify_packet_1() on RxRPC) is moot on distributions that don’t load rxrpc.ko by default. Chained, the two exploits give attackers root from any toehold: a separate exploit, web shell, container escape, or compromised low-privilege account. Hardened Kubernetes environments with default security settings are partially insulated per Wiz, but virtual machines and shared multi-tenant Linux environments are the high-risk profile. The fact that exploit code leaked before distributions could ship patches turns this from coordinated disclosure into a zero-day window. Patch immediately where available; reboot is required.
READ THE STORY: Ars Technica
Sandboxie Escape Flaws Allow Sandboxed Apps to Reach SYSTEM-Level Code Execution
Bottom Line Up Front (BLUF): Researchers disclosed four vulnerabilities in Sandboxie and Sandboxie-Plus versions 1.17.2 and earlier that defeat the software's core isolation function. The most severe, CVE-2026-34459, is a stack-based buffer overflow in the background proxy service that leaks uninitialized memory, bypasses ASLR, and enables full SYSTEM-level code execution when chained with other flaws. A second flaw (CVE-2026-34458) allows configuration injection through unfiltered formatting characters, providing a secondary sandbox-escape path. Patches are in version 1.17.5.
Analyst Comments: Sandbox escapes are operationally significant because they invalidate the entire trust assumption the tool was deployed for. Users running Sandboxie are typically detonating untrusted binaries, browsing high-risk content, or doing malware analysis specifically because they assume the host is protected. A bug chain that takes that assumption from "isolated container" to "full SYSTEM execution" is the worst-case outcome for the software's intended use. The ASLR-bypass primitive in CVE-2026-34459 is the load-bearing piece — exploit reliability against modern Windows depends on defeating address randomization, and a sandboxed-process information leak provides exactly that. CVE-2026-34527 (entropy reduction from 160 to 80 bits in stored passwords) is the quietest of the four but deserves attention because it weakens credential protection across every Sandboxie install, not just those targeted by an active sandbox escape. Anyone using Sandboxie in a malware analysis or untrusted-execution workflow should treat 1.17.2 and earlier as breach-equivalent until updated.
READ THE STORY: Cyber Press
iOS 26.5 Brings Default End-to-End Encrypted RCS Messaging Between iPhone and Android
Bottom Line Up Front (BLUF): Apple released iOS 26.5 with end-to-end encryption for Rich Communication Services (RCS) messages between iPhone and supported Android devices, the first cross-platform mobile messaging encryption available by default outside dedicated secure messengers. E2EE is enabled automatically for new and existing conversations on both platforms when carriers and Google Messages support it, indicated by a lock icon in chats. The capability is delivered via the GSMA RCS Universal Profile and built on cross-industry standards rather than a proprietary protocol. The same release patches 50+ CVEs in iOS and iPadOS.
Analyst Comments: This is the first time the default SMS-equivalent channel between iPhone and Android users has been encrypted at the device level. For two decades, cross-platform messaging between the two ecosystems has been the unencrypted gap that drove users to Signal, WhatsApp, and Telegram for any conversation that mattered. Now that gap closes by default — without requiring users to install anything, change apps, or know what end-to-end encryption is. The practical impact is larger than the technical story. Most people will not notice the change, which is the point. The threat-model implication is more interesting for defenders: insider threat investigations, legal discovery, and certain authorized surveillance workflows that previously assumed SMS-equivalent visibility into iPhone-to-Android communication now have to factor in E2EE coverage on the dominant cross-platform channel. The GSMA-standard delivery matters too — this is not Apple-only or Google-only encryption, but an industry baseline. That makes it harder for any single government or carrier to roll back, and easier for the next generation of secure-by-default capabilities (cross-platform attachments, encrypted group chats, encrypted business messaging) to follow the same path.
READ THE STORY: THN
ELECOM Wireless Router and Access Point Vulnerabilities Include Unauthenticated RCE and Auth Bypass (JVN#03037325)
Bottom Line Up Front (BLUF): JPCERT/CC disclosed seven vulnerabilities across more than 20 ELECOM wireless LAN router and access point models. The most severe are CVE-2026-40621 (missing authentication on specific URLs, CVSS 9.8) and CVE-2026-42062 (unauthenticated OS command injection via the username parameter, CVSS 9.8) — either allows full device takeover from the network with no credentials. Two additional flaws permit authenticated OS command injection (CVE-2026-35506, CVSS 7.2) and hard-coded cryptographic key abuse in configuration backups (CVE-2026-25107). ELECOM's vendor status as of disclosure is listed as "Vulnerable." Firmware updates are available from ELECOM.
Analyst Comments: The combination of unauthenticated RCE and unauthenticated authentication bypass on consumer and small-business wireless infrastructure is the worst-case profile for edge devices. CVE-2026-40621 and CVE-2026-42062 together give a network-adjacent attacker the ability to take over the affected devices without any prerequisite — no phishing, no credential theft, no chained exploit needed. ELECOM is a major Japanese networking vendor with deep penetration in the SOHO and SMB market across Japan and other Asian markets, which means the addressable attack surface is substantial. The pattern matters beyond this specific advisory. Edge networking devices (routers, access points, VPN concentrators, firewalls) have become the dominant initial-access vector for state-aligned actors in 2024-2026, replacing the phishing-led intrusion model that dominated the prior decade. Volt Typhoon's prepositioning campaign, the PAN-OS CVE-2026-0300 incident, and Ivanti EPMM CVE-2026-6973 all share the same shape: unauthenticated or authenticated-via-default-credentials access to internet-exposed edge infrastructure. ELECOM gear with these CVEs fits that pattern. Any organization running ELECOM equipment in their environment should treat the affected models as compromised until patched, particularly devices reachable from outside the local network. ShadowServer-style scanning will likely surface exposed ELECOM admin interfaces within days of public disclosure.
READ THE STORY: JVN
OpenAI Launches Daybreak: AI-Powered Vulnerability Detection With Tiered Access Controls
Bottom Line Up Front (BLUF): OpenAI announced Daybreak, a cybersecurity initiative combining Codex Security, specialized GPT-5.5 cyber models, and a tiered access framework called Trusted Access for Cyber. The platform analyzes codebases, identifies attack paths, validates vulnerabilities in isolated environments, and recommends patches for human review. Partners include Cloudflare, Cisco, CrowdStrike, Palo Alto Networks, Oracle, Zscaler, and Fortinet. A separate limited-preview model, GPT-5.5-Cyber, is restricted to authorized workflows including penetration testing, controlled red teaming, and advanced validation exercises. Standard GPT-5.5 remains generally available; access to higher-tier capabilities requires verification.
Analyst Comments: The substantive design choice in Daybreak is the access-tier framework, not the underlying AI capability. Frontier models capable of automated vulnerability discovery have existed for over a year; the harder question has always been who gets to use them and under what oversight. OpenAI is answering that question with a verification-and-permissioning layer (Trusted Access for Cyber) that creates explicit gates for malware analysis, secure code review, patch validation, vulnerability triage, and red teaming. Standard users get the default model; verified defenders get fewer refusals and stronger cyber assistance; authorized workflows get GPT-5.5-Cyber. The partner list reads as a direct competitive response to Anthropic's Mythos rollout — every major enterprise security vendor is now picking a frontier-model alignment, and OpenAI is moving from "general-purpose model with some cyber refusals" to "governed enterprise platform with cyber-specific tiers." The strategic question this raises for defenders: which AI provider's access framework does your organization want to inherit? The choice now determines not just model capability but who can verify your team's identity, what workflows get unblocked, and what telemetry the provider receives about your defensive operations. That decision is starting to look more like choosing a cloud provider than choosing a developer tool. The other thing worth watching is the implicit signal that GPT-5.5-Cyber exists at all — OpenAI confirming a less-restricted model variant for authorized cyber workflows is the same architectural admission Anthropic made with Mythos. The unrestricted variants are real; the access controls are the new product.
READ THE STORY: FP
Checkmarx Jenkins Plugin Compromised in Third TeamPCP Supply-Chain Attack Since March
Bottom Line Up Front (BLUF): TeamPCP published a backdoored version of the Checkmarx Jenkins Application Security Testing (AST) plugin to the Jenkins Marketplace on May 9, 2026 (version 2026.5.09), using credentials stolen during the March Trivy supply-chain compromise. The malicious plugin delivered credential-stealing malware. Checkmarx confirmed the threat actor maintained access to its GitHub repositories for at least a month before this latest incident. Users should ensure they are running version 2.0.13-829.vc72453fa_1c16 (December 17, 2025) or earlier.
Analyst Comments: This is the third Checkmarx supply-chain incident in under two months, and the cause is the same each time: unrotated credentials from the March Trivy breach. TeamPCP left a public message on the about section — "Checkmarx fails to rotate secrets again" — which reads as taunt but also as accurate technical assessment. When a single credential compromise feeds three downstream incidents (modified KICS analysis tool on Docker/OpenVSX/VSCode, the LAPSUS$ private-repo data leak, now the Jenkins AST plugin), the issue is not adversary capability; it is hygiene. Checkmarx's positioning makes this particularly damaging — they sell application security testing tools, and the compromise pathway is the exact failure mode their product is supposed to detect in customer environments. The structural lesson for defenders is that supply-chain attackers no longer need new initial access for follow-on incidents. One credential set in TeamPCP's hands has produced compromises across npm (Shai-Hulud), Trivy, KICS, and now Jenkins AST. Anyone running CI/CD with the affected plugin version should assume credential exposure, rotate all secrets in the Jenkins environment, and hunt for lateral movement or persistence consistent with credential theft.
READ THE STORY: Bleeping Computer
Elastic Ships Interactive Security MCP App for Claude, VS Code, and Cursor
Bottom Line Up Front (BLUF): Elastic released a Security MCP App that brings interactive SOC dashboards into AI chat tools including Claude Desktop, Claude.ai, VS Code Copilot, and Cursor, built on the open MCP Apps extension to the Model Context Protocol. The app provides six interactive UIs covering the core SOC loop: alert triage, threat hunting, attack discovery, case management, detection rule tuning, and sample data generation. All actions write back to Elasticsearch and Kibana through standard APIs, preserving role-based access controls and audit trails.
Analyst Comments: This is the first vendor-shipped interactive UI inside an AI chat tool for security operations, and the design choice it makes is worth naming. Most MCP integrations return text summaries the analyst then acts on elsewhere; Elastic returns the workflow itself, rendered inline. The architectural distinction matters because the SOC loop — scan alerts, expand process tree, trace a parent-child chain, drag an entity onto an investigation graph — does not compress into text without losing the work. The MCP server runs locally on the analyst's machine and authenticates to Elasticsearch with the analyst's own API key, which keeps governance intact: the LLM gets compact summaries for reasoning, while full investigation data loads through the same server under existing RBAC. The broader signal for the agentic SOC discussion is that vendors are moving past "AI summarizes your dashboard" into "AI hands you the dashboard, in-conversation." That changes the integration assumption for every other security vendor. If Elastic ships an interactive case management UI in Claude Desktop, the baseline competitive expectation just moved. Worth watching whether CrowdStrike, SentinelOne, Palo Alto XSIAM, and Splunk follow the same pattern.
READ THE STORY: Elastic Security Labs
Operation HumanitarianBait Uses GitHub Releases and Fileless Python Malware to Evade Detection
Bottom Line Up Front (BLUF): Researchers uncovered a cyberespionage campaign dubbed “Operation HumanitarianBait” that uses phishing lures themed around Russian humanitarian aid requests to deploy a stealthy Python-based infostealer. The malware abuses GitHub Releases for payload delivery, executes largely in-memory, and establishes persistent remote access using legitimate remote administration tools.
Analyst Comments: This campaign is a good example of attackers blending legitimate infrastructure, fileless execution, and social engineering to stay below traditional detection thresholds. GitHub is doing double duty here: it acts as trusted infrastructure for payload staging while helping malicious traffic blend into normal developer and software-update activity. The infection chain is also designed specifically to frustrate automated analysis. Self-obfuscating PowerShell, memory-only execution, PyArmor-protected payloads, and dependency on the original lure file all reduce sandbox visibility and static-analysis effectiveness. The malware does not need sophisticated kernel exploits when the operational tradecraft already defeats many commodity defenses.
READ THE STORY: Cyber Press
Bangladesh Government Joins Have I Been Pwned’s Free Breach Monitoring Service
Bottom Line Up Front (BLUF): Bangladesh became the 43rd government onboarded to Have I Been Pwned’s free government service. The BGD e-GOV CIRT now has API access to monitor Bangladesh government domains for exposed email addresses in past and future data breaches.
Analyst Comments: The value here is not just breach lookup—it is continuous monitoring. For governments, especially those managing large distributed agencies, early visibility into exposed accounts can help prioritize password resets, MFA enforcement, phishing response, and identity-risk investigations.
READ THE STORY: Troy Hunt
Fake Claude Website Distributes "Beagle" Backdoor via DLL Sideloading Chain
Bottom Line Up Front (BLUF): Attackers are using a fake Claude website at claude-pro[.]com to distribute a trojanized 505 MB Windows installer that deploys a newly documented backdoor called Beagle. The infection chain abuses a signed G DATA updater (NOVupdate.exe) to sideload a malicious DLL (avk.dll) and an encrypted payload, then loads shellcode through the open-source DonutLoader to install the final implant. Sophos identified the campaign and noted the installer ships a working copy of Claude as camouflage to make the infection look like a normal application install. Related samples reuse the same XOR key against fake Trellix, CrowdStrike, and SentinelOne-themed lures.
Analyst Comments: The campaign is operationally interesting for two reasons. First, the lure economics — attackers do not need a software bug when public interest in AI tools is high enough to drive users to typo-squatted domains. Malvertising and poisoned search results carry the user to claude-pro[.]com; the user does the rest. Second, the camouflage of shipping a working Claude install alongside the implant is the move that pushes this past commodity malware. Most fake-installer campaigns deliver a broken or fake application that immediately tips off the user. Bundling a functional Claude experience inside the same MSI means the user gets what they thought they were downloading, the install completes normally, and the implant runs underneath. The DLL sideloading chain itself (signed updater + malicious DLL + encrypted payload) is well-worn PlugX-style tradecraft, but the wrapper is what makes the campaign effective at scale. The cross-brand expansion (Trellix, CrowdStrike, SentinelOne lures) suggests the operators are building a fake-brand-lure framework, not running a single Claude-themed campaign. Anyone running threat intelligence on typo-squatted security-brand domains should treat AI-tool brands as the same category now — Anthropic, OpenAI, Google AI, and their tools are high-value lure surfaces.
READ THE STORY: Cyber Press
Google Says Threat Actors Used AI to Develop Zero-Day Exploit Targeting Web Administration Tool
Bottom Line Up Front (BLUF): Google Threat Intelligence Group (GTIG) says it identified what it believes is the first known zero-day exploit developed with AI assistance for planned mass exploitation. The exploit targeted an unnamed open-source web administration platform and was designed to bypass two-factor authentication protections before Google disrupted the campaign prior to widespread abuse.
Analyst Comments: This is a milestone event in offensive AI operations—not because AI suddenly became an autonomous super-hacker, but because it appears to have materially accelerated vulnerability discovery and exploit development for a real-world zero-day campaign. The most important detail is the type of vulnerability involved. GTIG says the flaw was a semantic logic bug rather than classic memory corruption. That tracks with where current LLMs are strongest: understanding workflows, permissions, trust boundaries, authentication assumptions, and application logic. AI models are still inconsistent at producing advanced memory exploitation chains, but they are increasingly effective at identifying “this workflow should not behave this way” classes of vulnerabilities.
READ THE STORY: Bleeping Computer
Items of interest
Thousands of Vibe-Coded Apps Expose Corporate and Personal Data on the Open Web
Bottom Line Up Front (BLUF): RedAccess researchers found more than 5,000 publicly accessible AI-generated web apps built with platforms including Lovable, Replit, Base44, and Netlify. Roughly 40% reportedly exposed sensitive personal or corporate data, including medical information, financial records, strategy documents, chatbot logs, and customer details..
Analyst Comments: This is shadow IT with a launch button. The issue is not just buggy AI code; it is non-technical users deploying internet-facing apps without authentication, access controls, or security review. The parallels to exposed S3 buckets are obvious: vendors can blame user configuration, but insecure defaults and weak guardrails become a platform problem at scale. Expect attackers to mine these apps for credentials, customer data, internal documents, admin access, and phishing infrastructure.
READ THE STORY: Wired
Vibe Coding is a Trap (What Senior Devs See That You Don't) (Video)
FROM THE MEDIA: Are you falling for the "vibe coding" trend? In this video, we expose the truth behind vibe coding and reveal why it can be a trap for aspiring developers. You'll learn what is vibe coding, the hidden pitfalls, and what senior devs see that you don't.
The “vibe coding” mind virus explained… (Video)
FROM THE MEDIA: Let’s take a look at the latest craze in the programming world known as "vibe coding". Learn how to vibe code properly and look into the pros and cons of AI coding techniques.
The selected stories cover a broad range of cyber threats and are intended to help readers frame key publicly discussed threats and improve overall situational awareness. InfoDom Securities does not endorse any third-party claims made in its original material or related links on its sites; the opinions expressed by third parties are theirs alone. For further questions, don’t hesitate to get in touch with InfoDom Securities at dominanceinformation@gmail.com.