Daily Drop (1292)
05-06-26
Wednesday, May 06, 2026 // (IG): BB // Ghostwire
China-Nexus Actors Shift to Large-Scale Covert Networks of Compromised SOHO Routers and IoT Devices, NCSC and 13 Allied Agencies Warn
Bottom Line Up Front (BLUF): The UK’s National Cyber Security Centre and 13 allied agencies warned that China-nexus cyber actors are increasingly using large-scale covert networks built from compromised SOHO routers, IoT devices, and smart devices to route attack traffic. The tactic gives operators low-cost, deniable infrastructure that masks origin, complicates attribution, and bypasses static defenses. Volt Typhoon and Flax Typhoon were cited as examples of groups using this model.
Analyst Comments: This is not just another botnet story. The operational problem is that traffic from these networks often looks legitimate because it originates from real residential broadband connections. That undercuts IP blocklists, reputation-based filtering, and location-based access controls. The NCSC’s warning on “IOC extinction” matters: indicators disappear quickly because nodes are constantly refreshed and shared across groups. Defenders should treat covert infrastructure as a persistent adversary layer, not disposable noise. Priority actions include baselining remote-access traffic, monitoring VPN and edge-device connections, using machine certificates where feasible, and actively hunting upstream with NetFlow.
FROM THE MEDIA: Professional Security Magazine reported that the joint advisory was issued by the NCSC, CISA, NSA, FBI, ASD’s ACSC, Canada’s Cyber Centre, Germany’s BfV, BND and BSI, Japan’s NCO, NCSC-NZ, Spain’s CCN, Sweden’s NCSC-SE, and the US Department of Defense Cyber Crime Center. The advisory notes that China-nexus groups increasingly rely on covert networks created and maintained externally by Chinese information security companies. Integrity Technology Group was specifically called out in 2024 for managing infrastructure used by Flax Typhoon.
READ THE STORY: Professional Security Mag
North Korea's APT37/ScarCruft Trojanizes Yanbian Gaming Platform with First-Documented Android Variant of BirdCall Backdoor in Multiplatform Supply Chain Attack
Bottom Line Up Front (BLUF): The Record reports that ESET attributed a supply-chain compromise of Chinese gaming site sqgame[.]net to North Korea-aligned APT37, also tracked as ScarCruft and Reaper. The attackers trojanized Android card games serving ethnic Koreans in China’s Yanbian Korean Autonomous Prefecture, delivering the first documented Android variant of APT37’s BirdCall backdoor. The malware collects contacts, SMS messages, call logs, media files, documents, private keys, screenshots, and ambient audio.
Analyst Comments: The targeting is the story. APT37 did not just compromise a random gaming site; it compromised a niche platform serving a community tied to North Korean defectors, refugees, and people of interest to Pyongyang. That turns a trusted community resource into an espionage collection point. The Android development work also shows maturation: multiple versions, background persistence tricks, cloud-based C2, and selective microphone capture between 7 PM and 10 PM local time. Defenders supporting at-risk Korean diaspora communities should treat sideloaded APKs as high-risk, even when they come from familiar regional platforms.
FROM THE MEDIA: Jonathan Greig reported that the Windows attack chain used a malicious update package hosted at xiazai.sqgame.com[.]cn, with a patched mono.dll loader delivering RokRAT and BirdCall before replacing itself with a clean copy. On Android, the attackers repackaged legitimate game APKs by modifying AndroidManifest.xml to route execution through the backdoor before launching the original game. C2 infrastructure used legitimate cloud providers including Zoho WorkDrive, pCloud, and Yandex Disk, with Zoho observed in this campaign.
READ THE STORY: The Record
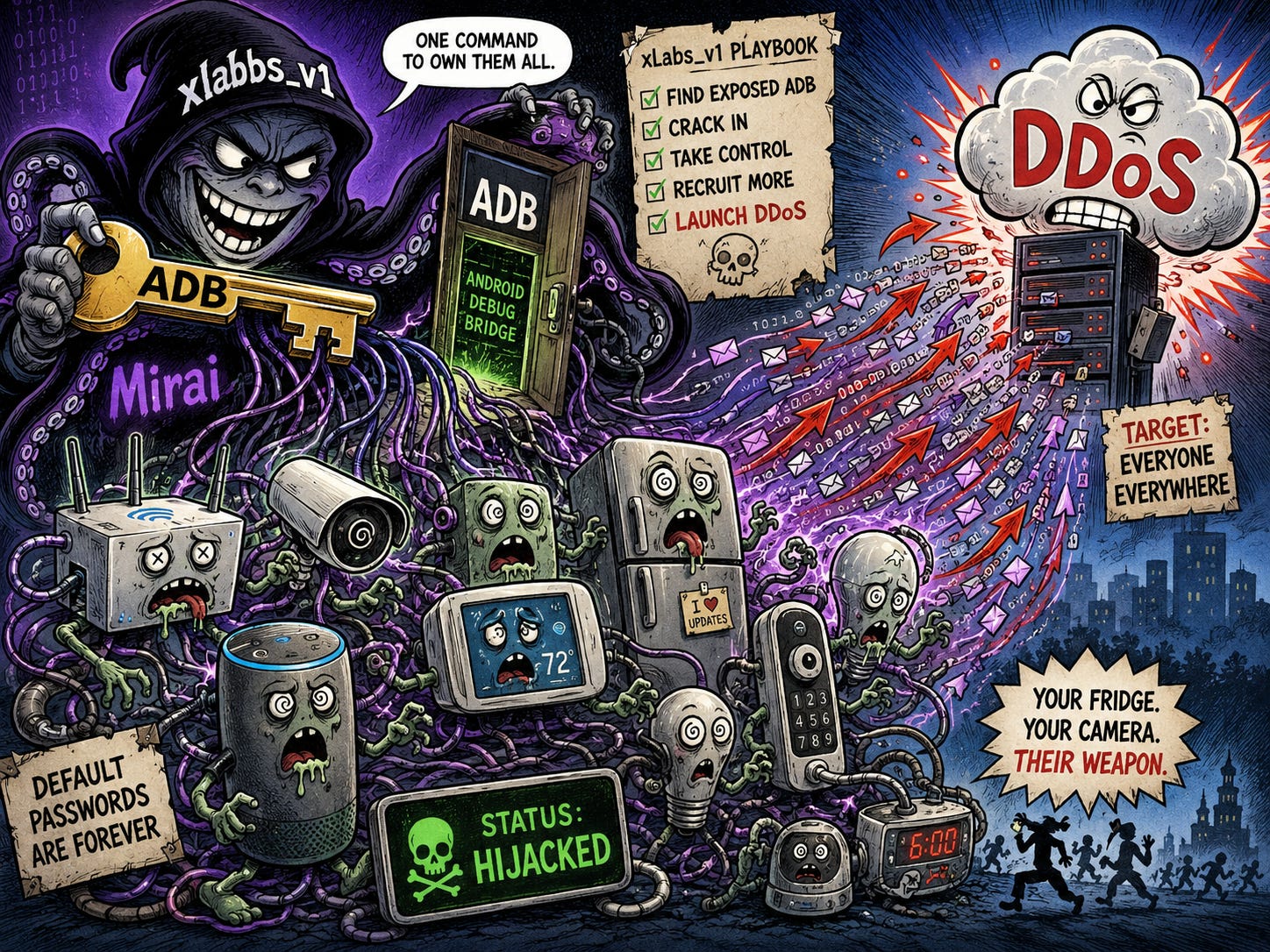
Mirai-Based xlabs_v1 Botnet Targets Exposed Android Debug Bridge for Game-Server DDoS
Bottom Line Up Front (BLUF): The Hacker News reports that researchers at Hunt.io uncovered a Mirai-derived botnet called xlabs_v1 that targets Internet-exposed Android Debug Bridge services on TCP port 5555. The botnet is built for DDoS-for-hire activity, especially against game servers and Minecraft hosts, and supports 21 flood variants across TCP, UDP, and raw protocols. Targeted devices include Android TV boxes, set-top boxes, smart TVs, routers, and other IoT hardware with exposed or default-enabled ADB.
Analyst Comments: This is classic Mirai economics with a gaming-sector twist: find exposed consumer devices, weaponize their bandwidth, and sell the output as a service. xlabs_v1 is not technically elite, but it does not need to be. Exposed ADB on port 5555 remains low-hanging fruit, especially across cheap Android-based devices that ship insecurely or are never patched. The bandwidth-profiling routine is the most interesting operational detail because it turns each infected device into a metered commodity. Operators are not just building a botnet; they are sorting inventory for price-tiered DDoS sales. Defenders should block public ADB exposure, scan for TCP/5555, isolate unmanaged IoT, and treat unexpected outbound Speedtest-style activity as a possible botnet enrollment signal.
FROM THE MEDIA: Hunt.io found the malware after identifying an unauthenticated exposed directory on a Netherlands-hosted server at 176.65.139[.]44. The bot receives commands from xlabslover[.]lol and includes multi-architecture builds for ARM, MIPS, x86-64, and ARC. Its bandwidth profiler opens 8,192 parallel TCP sockets to the nearest Speedtest server, runs for 10 seconds, and reports measured throughput and geolocation back to the panel. The bot lacks persistence, suggesting operators re-infect devices through the same ADB channel when needed. It also includes a “killer” subsystem to terminate competing malware and monopolize upstream bandwidth. The threat actor appears to use the moniker “Tadashi.”
READ THE STORY: THN
Censys Finds 31,000+ Internet-Exposed Password Manager Interfaces
Bottom Line Up Front (BLUF): Censys ARC found more than 31,000 Internet-accessible password manager instances across Bitwarden, Vaultwarden, Passbolt, Psono, and Teampass. Vaultwarden dominated the dataset, representing 62% of observed interfaces. While these tools are designed to be web accessible, Censys found meaningful exposure risk: more than 1,700 Vaultwarden instances — roughly 9% of instances where a version could be obtained — may be running versions vulnerable to two critical CVEs from early 2025.
Analyst Comments: Password managers are supposed to reduce risk, but an exposed, outdated, or misconfigured vault can quickly become a crown-jewels liability. The key nuance here is that exposure alone does not equal compromise — Bitwarden, Vaultwarden, Passbolt, Psono, and Teampass all support web access by design. The real concern is the long tail: stale versions, abandoned installers, exposed admin panels, and government-associated deployments sitting on the public Internet. The Vaultwarden finding matters most because CVE-2024-55225 can allow user impersonation, including administrator impersonation, which becomes especially dangerous in organization vaults where attacker access to key material may expose shared secrets.
FROM THE MEDIA: Censys reported that Germany led observed password manager exposure at 22.9%, followed by the United States at 19.6% and France at 10.8%. Hosting patterns mirrored that distribution, with Hetzner, AWS, and OVH representing 22.7% of observations. Censys also found that self-hosted patching behavior was better than expected: 65% of Vaultwarden instances were running a release no older than roughly five months, while 64% of Bitwarden instances were running a version no older than roughly six months. Additional findings included 55 Passbolt installers ready to be configured, 35 exposed Psono Admin Panels, and 20 distinct TLS certificate subject DNs containing *.gov domains on hosts running Internet-accessible password manager interfaces.
READ THE STORY: Censys
CISA Adds ConnectWise ScreenConnect and Microsoft Windows Vulnerabilities to KEV Catalog
Bottom Line Up Front (BLUF): CISA added two actively exploited vulnerabilities to its Known Exploited Vulnerabilities catalog on April 28, 2026: CVE-2024-1708, a ConnectWise ScreenConnect path traversal vulnerability, and CVE-2026-32202, a Microsoft Windows protection mechanism failure vulnerability. Federal Civilian Executive Branch agencies are required to remediate KEV-listed vulnerabilities by CISA’s assigned due dates under Binding Operational Directive 22-01, and CISA is urging all organizations to prioritize patching because these flaws are confirmed attack vectors.
Analyst Comments: KEV additions matter because they cut through the noise: CISA is not saying these bugs are theoretically dangerous; it is saying there is evidence of active exploitation. ConnectWise ScreenConnect remains a high-value target because remote monitoring and management platforms provide exactly what attackers want — trusted access, administrative reach, and a path into downstream environments. The Microsoft Windows protection mechanism failure also deserves priority treatment because local or post-exploitation bypasses often become force multipliers once attackers already have a foothold. Organizations should treat both vulnerabilities as patch-now items, validate exposure across managed service provider tooling and Windows fleets, and confirm remediation rather than relying on patch deployment assumptions.
FROM THE MEDIA: The agency reiterated that while BOD 22-01 applies only to Federal Civilian Executive Branch agencies, all organizations should use the KEV catalog as a vulnerability management priority list and reduce exposure through timely remediation of known exploited flaws.
READ THE STORY: Axios
VoidStealer Bypasses Chrome App-Bound Encryption by Grabbing Keys from Browser Memory
Bottom Line Up Front (BLUF): Dark Reading reports that the authors of the VoidStealer Trojan have found another way around Google Chrome’s App-Bound Encryption, a protection introduced in July 2024 to stop infostealers from harvesting cookies and other sensitive browser data on Windows. The technique targets the brief moment when Chrome decrypts protected data for legitimate use, then extracts the master key from browser memory. The bypass may also affect other Chromium-based browsers using ABE, including Microsoft Edge, Opera, Vivaldi, and Brave.
Analyst Comments: ABE raised the bar, but it did not end browser credential theft. VoidStealer’s method is a good reminder that defensive controls protecting data at rest still have to expose secrets during legitimate runtime operations. That window is where malware authors are now hunting. By attaching to Chrome as a debugger, pausing execution at the decryption point, and extracting the key directly from memory, VoidStealer sidesteps the intended protection without needing the older, noisier path of simply reading encrypted cookie stores from disk. For defenders, this pushes emphasis toward endpoint behavior: unauthorized debugging of browsers, suspicious process access to Chrome, memory inspection, and infostealer tradecraft around session-token theft.
FROM THE MEDIA: In practice, infostealers including Meduza Stealer, Whitesnake, Lumma Stealer, and Lumar have continued to harvest browser secrets despite ABE. VoidStealer’s approach differs by targeting Chrome while it decrypts data for normal use, exposing the master key in plaintext in memory long enough for malware attached as a debugger to capture it. Researchers have previously shown other ABE bypass paths, including fileless execution, process hollowing, direct system calls, and CyberArk’s C4 technique.
READ THE STORY: DR
Apache HTTP Server HTTP/2 Double-Free Flaw Patched as DoS Path Goes Trivial and RCE Becomes Plausible on Debian and Docker Defaults
Bottom Line Up Front (BLUF): MS-ISAC issued advisory 2026-044 on May 6, 2026 covering CVE-2026-23918, a double-free vulnerability in Apache HTTP Server 2.4.66's mod_http2 module triggered by a crafted HTTP/2 sequence that causes the same stream to be cleaned up twice, leading to memory corruption. The flaw carries a CVSS score of 8.8 and is classified as CWE-415 (double free). Successful exploitation produces denial of service via worker process crash with minimal effort, and in setups using APR with the mmap allocator — common on Debian-derived systems and the official Apache Docker image — the bug may also be exploited for remote code execution. Proof-of-concept code exists for both DoS and RCE outcomes, and Apache has released 2.4.67 as the patched version.
Analyst Comments: The DoS path is simple enough to matter immediately: one TCP connection and two HTTP/2 frames can crash a worker in common deployments. RCE is more conditional, but credible where APR-mmap conditions line up. The long gap between source fix and release is also operationally relevant, because vulnerable 2.4.66 deployments had months to accumulate. Internet-facing reverse proxies, web tiers, authentication front ends, and Docker-based Apache deployments should be prioritized. Where patching cannot happen quickly, disabling mod_http2 is the cleanest mitigation.
FROM THE MEDIA: CIS reported that the flaw is triggered when a client sends an HTTP/2 HEADERS frame followed immediately by RST_STREAM with a non-zero error code on the same stream, causing the same stream pointer to be cleaned up twice. Researchers said MPM prefork is not affected, but default multi-threaded mod_http2 deployments are exposed. Observed exploitation includes worker crashes and large-scale scanning for HTTP/2 endpoints.
READ THE STORY: CIS
Critical PAN-OS Authentication Portal Zero-Day Under Active Exploitation as Palo Alto Customers Wait a Week for First Patches
Bottom Line Up Front (BLUF): Palo Alto Networks has confirmed in-the-wild exploitation of CVE-2026-0300, a critical buffer overflow in the User-ID Authentication Portal (Captive Portal) service of PAN-OS that allows unauthenticated attackers to execute code with root privileges on PA-Series and VM-Series firewalls via specially crafted packets. The flaw carries a CVSS score of 9.3 when the portal is exposed to the public internet or untrusted networks, falling to 8.7 when access is restricted to trusted internal IP addresses. No patch is currently available; first software fixes are expected May 13, with a second wave around May 28. Cloud NGFW and Panorama appliances are not impacted.
Analyst Comments: Edge authentication services remain prime real estate for attackers, and this one has the right ingredients for rapid escalation: root execution, public exposure risk, and automatable exploitation. Palo Alto’s “limited exploitation” language suggests targeted activity for now, but that window can close quickly once researchers and adversaries converge on the bug. Customers should restrict Authentication Portal access to trusted zones immediately or disable it where not required. Waiting for patches while the service remains internet-exposed is a bad bet.
FROM THE MEDIA: Shadowserver identified more than 5,800 publicly exposed VM-Series firewalls, though not all may have the vulnerable portal configuration enabled. Researchers expect detection rules and honeypot activity to increase as attention builds around the vulnerability.
READ THE STORY: CS
Items of interest
Trump Administration Revives Frontier AI Safety Testing After Anthropic Withholds Claude Mythos
Bottom Line Up Front (BLUF): Ars Technica reports that the Trump administration signed agreements with Google DeepMind, Microsoft, and xAI to conduct government safety evaluations of frontier AI models before and after release, reversing its earlier rejection of Biden-era AI safety testing. The shift followed Anthropic’s decision not to release its Claude Mythos model due to concerns that advanced cybersecurity capabilities could be abused by malicious actors. The renamed Center for AI Standards and Innovation, formerly the U.S. AI Safety Institute, says it has completed roughly 40 evaluations and will use interagency expertise to assess national security risks.
Analyst Comments: This is a policy reversal with real security implications. The administration spent months framing AI safety testing as overregulation, then changed posture once a frontier model was withheld over cybersecurity misuse risk. That tells us the national security concern is no longer theoretical. The hard part is not getting labs to sign voluntary agreements; it is defining what “safe” means, who sets the standard, and whether evaluations can remain technical rather than political. Without published criteria, model testing risks becoming either performative oversight or a tool for political pressure. For defenders, the relevant takeaway is that advanced AI cyber capability is now being treated as a pre-release national security issue, not merely a product-risk question.
READ THE STORY: arsTECHNICA
Trump Admin Will Test New AI Models From Google, Microsoft And XAI Before Release Under New Deal (Video)
FROM THE MEDIA: The Commerce Department on Tuesday announced agreements with Google, Microsoft and Elon Musk’s xAI that will allow the Trump administration to review the company’s new AI models before they are publicly released, a reversal in Trump’s approach to the technology after a fallout with Anthropic.
‘Terrifying warning sign’: Anthropic delays AI model over security concerns (Video)
FROM THE MEDIA: Anthropic says Mythos (officially dubbed “Claude Mythos Preview”) is not ready for a public launch because of the ways it could be abused by cybercriminals and spies, according to Anthropic — a prospect that has prompted widespread concern in Washington and in Silicon Valley.
The selected stories cover a broad range of cyber threats and are intended to help readers frame key publicly discussed threats and improve overall situational awareness. InfoDom Securities does not endorse any third-party claims made in its original material or related links on its sites; the opinions expressed by third parties are theirs alone. For further questions, don’t hesitate to get in touch with InfoDom Securities at dominanceinformation@gmail.com.