Daily Drop (1291)
05-05-26
Tuesday, May 05, 2026 // (IG): BB // Ghostwire
Verified-Affected Distribution List Expands as TechCrunch Reports Late-March Disclosure Timeline
Bottom Line Up Front (BLUF): TechCrunch coverage of CVE-2026-31431 (”Copy Fail”) confirms the Linux kernel local privilege escalation is being exploited in the wild, with the federal patching deadline of May 15 reaffirmed. New operational details from this reporting include the disclosure timeline — disclosed to the Linux kernel security team in late March, patched after roughly a week — and verified-affected distributions per Theori: Red Hat Enterprise Linux 10.1, Ubuntu 24.04 (LTS), Amazon Linux 2023, and SUSE 16. DevOps engineer Jorijn Schrijvershof independently confirmed the exploit also works on Debian, Fedora, and Kubernetes (which relies on the Linux kernel), describing the bug as having an “unusually big blast radius” affecting “nearly every modern distribution.”
Analyst Comments: Zack Whittaker reports the copy.fail disclosure site frames the vulnerability as a single short Python script that “roots every Linux distribution shipped since 2017.” Beyond the previously documented attack vectors (SSH access, malicious CI jobs, container footholds), TechCrunch flags supply chain compromise of an open-source developer’s account as an additional delivery mechanism — malicious actors hacking into a developer’s account and planting code that triggers the vulnerability could compromise a large number of devices in a single operation. Microsoft’s chained-exploit framing is preserved: the bug is not remotely exploitable on its own but becomes highly impactful when combined with an internet-deliverable vulnerability for initial access. The data-center-blast-radius framing is articulated explicitly: a successful compromise of a single server could give attackers access to every application, server, and database of numerous corporate customers on that machine, with potential lateral movement to other systems on the same network. Patch availability across the broader Linux distribution ecosystem remains incomplete; the fix has been applied upstream but has not fully propagated to all distributions, leaving any system on an affected kernel at risk.
READ THE STORY: TC
FBI Cyber Division Steps Up Pace Against North Korea, Iran, and Russia as AI-Boosted Attacks Surge 90%
Bottom Line Up Front (BLUF): Maggie Miller reports in POLITICO’s Weekly Cybersecurity (May 4, 2026) that FBI Cyber Division Assistant Director Brett Leatherman, in a wide-ranging interview, said the bureau is adapting strategies and taking bolder enforcement actions in response to AI-boosted cyberattacks that rose nearly 90% last year. Top priorities include North Korean operatives posing as remote IT workers and conducting cryptocurrency theft to fund the regime, Iran-linked hackers scaling up attacks during the Iran war (including the recent takedown of websites operated by Iranian group Handala), and a fourth joint sequenced operation disrupting a Russian GRU-linked hacking campaign that compromised thousands of US home Wi-Fi routers for espionage and potential critical infrastructure targeting.
Analyst Comments: Leatherman framed the operational posture as “Cyber is border-agnostic. We have to treat it that way, and we have to move at the speed of cyber,” citing the recent Russian router-compromise disruption, China-linked router operation warnings, the extradition of a suspected Chinese hacker last week, and the DOJ’s Scam Center Strike Force established earlier this year to counter Southeast Asian cyber-fraud compounds. The Cyber Division operates almost two dozen law enforcement attachés in US embassies including Five Eyes partner countries to support joint operations. Separately, Handala claimed Saturday to have hacked former Biden-era Iran envoy Robert Malley’s email and X accounts, uploading approximately 150,000 emails and posts; the International Crisis Group (where Malley is former president) said it is “working to establish the exact details,” and Malley did not respond. Securonix published a Monday report on the VENOMOUS#HELPER campaign — fake SSA-themed phishing against 80+ organizations in the US, Europe, and Latin America since mid-2025, characterized as a likely “ransomware precursor operation targeting the Western economic bloc,” with Sophos having reported on the same activity in late March.
READ THE STORY: Politico
Microsoft Defender Flagged Two Legitimate DigiCert Root Certificates as Malware in Widespread False Positive Incident
Bottom Line Up Front (BLUF): On May 3, 2026, Windows admins and SOC analysts began seeing widespread Microsoft Defender alerts for “Trojan:Win32/Cerdigent.A!dha” that flagged two DigiCert root certificates — DigiCert Assured ID Root CA (thumbprint 0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43) and DigiCert Trusted Root G4 (thumbprint DDFB16CD4931C973A2037D3FC83A4D7D775D05E4) — as malicious, with Defender quarantining root certificate entries from Windows trust stores in some cases. Per BleepingComputer, the issue followed an April 30 Defender signature update. Microsoft’s fix is to update Defender Security Intelligence to version 1.449.430.0 or later, after which Microsoft Q&A moderators confirmed the detection no longer occurred.
Analyst Comments: Censys’s Alex Gartner walks through the SOC triage path on the incident. The two flagged hashes resolve in Censys’s certificate dataset (15 billion+ records) to legitimate DigiCert root CAs — both self-signed, CA basic constraints set, certificate-signing and CRL-signing usage, no revocation, and trusted across major root stores (DigiCert Assured ID Root CA in Microsoft/Apple/NSS; DigiCert Trusted Root G4 in Microsoft/Apple/NSS/Chrome). A Censys host query against certificate validation chains found roughly 2,100 currently online hosts using these certificates in ordinary public TLS validation paths, confirming these are not signals of suspicious infrastructure but core trust anchors. Gartner uses the incident to make a broader operational point about how certificates differ from typical EDR malware indicators: a .cer/.crt/.der/.pem file doesn’t execute, doesn’t spawn processes, doesn’t inject into memory — it’s structured trust data, and its security implications come from what trust decisions it enables (rogue roots, stolen code-signing certs, certs tied to phishing/C2/adware/TLS-interception infrastructure). For a SOC analyst working through the incident, the operationally useful questions are what trust decision the cert affects, where on the endpoint it was found, and who put it there. The article frames the broader analyst burden honestly: “every alert has to be treated seriously until the evidence says otherwise,” and external authoritative certificate-context sources (Censys, Certificate Transparency logs, root-store validation status) prevent analysts from mistaking legitimate trust anchors for compromise indicators when EDR signatures misfire.
READ THE STORY: censys
VENOMOUS#HELPER Phishing Campaign Weaponizes SimpleHelp and ScreenConnect RMM Tools, Hits 80+ Organizations Since April 2025
Bottom Line Up Front (BLUF): Securonix researchers tracking VENOMOUS#HELPER report a phishing campaign active since at least April 2025 that has hit more than 80 organizations primarily in the US plus Western Europe and Latin America, weaponizing two legitimately signed commercial RMM tools — SimpleHelp and ScreenConnect — instead of traditional malware to maintain persistent control over compromised systems. The dual-tool architecture ensures continued access even if defenders detect and remove one of the two. Securonix has not formally attributed the activity, assessing it as “consistent with a financially motivated Initial Access Broker (IAB) or ransomware precursor operation targeting the Western economic bloc.”
Analyst Comments: Jai Vijayan reports the attack chain begins with phishing emails impersonating the US Social Security Administration and prompting victims to download a “statement”; clicking through directs them to phishing pages hosted on legitimate but previously compromised websites, where the downloaded executable installs both RMM tools. Securonix observed the operator using each tool for a different purpose: SimpleHelp as the primary channel for scripts, automated tasks, surveillance, and continuous system monitoring, and ScreenConnect for interactive desktop control. The attacker tracks cursor movement to identify when users are away from their machines, enabling hands-on activity at opportune times, and compromised systems show “literally hundreds of background actions in a short time frame” including network connectivity, user activity, and security tool checks. Aaron Beardslee, Securonix manager of threat research, told Dark Reading the campaign appears targeted at “higher tier employee’s personal emails with the hope those individuals would open their personal email on company devices,” with some evidence suggesting attacker interest in individuals with access to organizational cryptocurrency assets. The article cites broader context from Huntress: a 277% year-over-year increase in RMM tool misuse in 2025, with RMM tools appearing in nearly a quarter of all incidents, while traditional hacking tool use dropped 53% over the same period — a documented shift toward trusted-software attack vectors. Beardslee’s mitigation framing emphasizes “cyber paranoia” combined with endpoint logging into a strong SIEM/EDR platform to surface unusual behavior including unauthorized RMM installation, application whitelisting that “can stop these attacks outright,” and network monitoring as a detection layer — with the caveat that none of these help when users fall for lures on personal devices.
READ THE STORY: DR
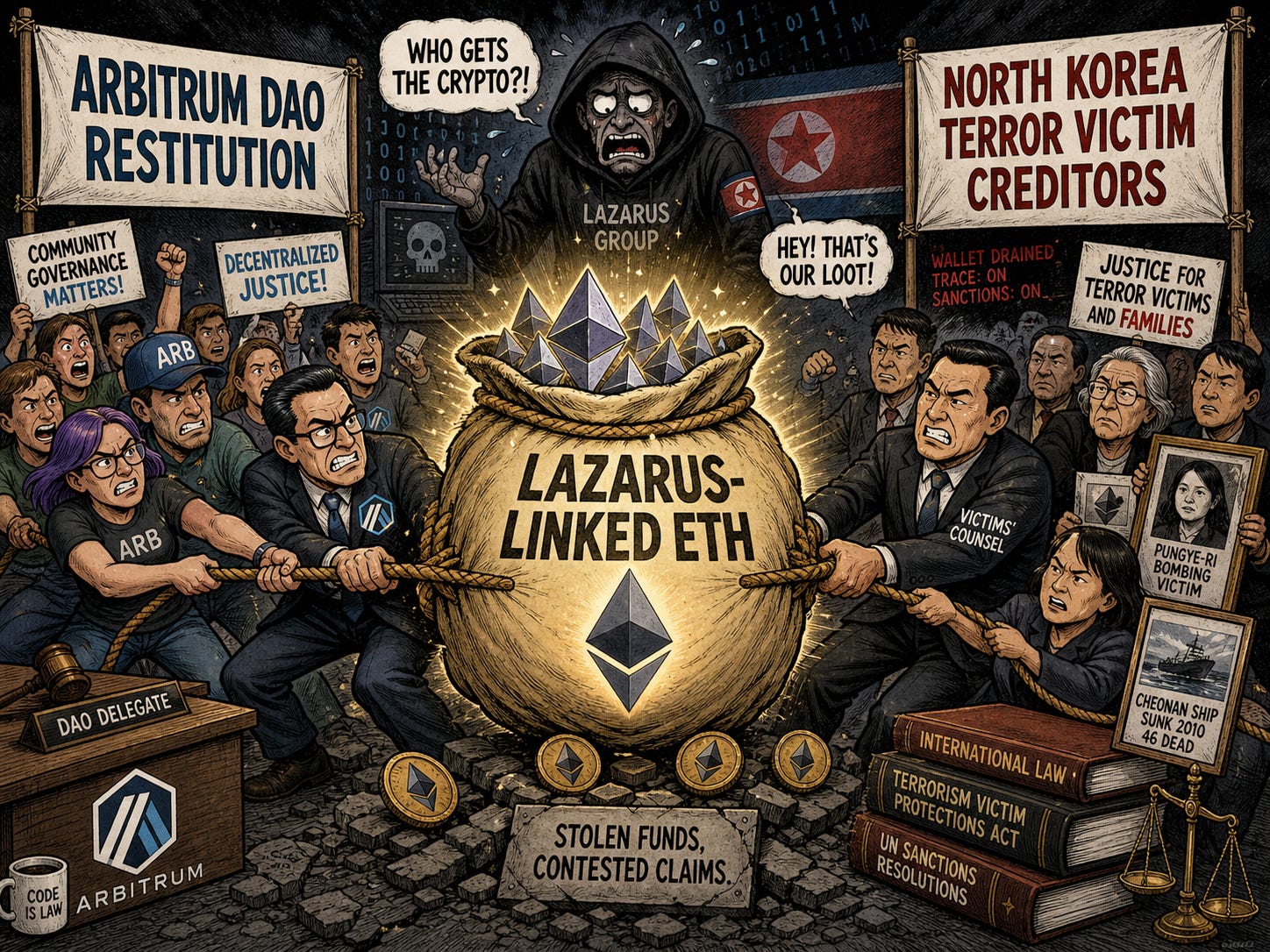
Lazarus-Linked ETH Caught Between Arbitrum DAO Restitution and North Korea Terror Victim Creditors
Bottom Line Up Front (BLUF): A federal court in the Southern District of New York issued an order on May 1, 2026 freezing 30,766 ETH (approximately $71 million) currently held by Arbitrum’s Security Council, complicating the Arbitrum DAO’s plan to compensate victims of last month’s $292 million Kelp DAO attack. The freeze was obtained by creditor lawyers representing victims of older North Korean state-sponsored attacks, who argue that ETH allegedly stolen by Lazarus Group constitutes property linked to the North Korean regime and is therefore subject to seizure under US laws targeting state sponsors of terrorism. Over 99% of votes so far support the Arbitrum community’s “DeFi United” proposal (voting opened April 30) to use the frozen funds to restore rsETH token backing, but the new court order creates legal risk for DAO participants implementing the plan.
Analyst Comments: Portalcripto reports the lawsuit was filed by Gerstein Harrow LLP on behalf of American citizens connected to the case of Reverend Kim Dong-shik, who was kidnapped and killed by North Korean agents — a single case that resulted in a settlement of approximately $330 million, with additional cited cases bringing the total claim to more than $877 million before accrued interest. The legal theory rests on classifying Lazarus Group as an extension of the North Korean state, which would justify asset seizure under US terrorism-sponsor frameworks. The DeFi United proposal envisions transferring the frozen funds to a multi-sig portfolio managed by ecosystem participants (including Aave Labs and other platforms) to recover Kelp DAO losses. Investigator ZachXBT characterized the creditor action as “a predatory American law firm with a purely malicious strategy,” and developer banteg argued the DAO could ignore the court decision on grounds that the funds have proven origin and belong to direct victims of the Kelp DAO attack. The case raises two operationally significant precedents: individual responsibility for DAO participants implementing votes that conflict with court orders, and a framework for international creditors to lay claim to traceable cryptocurrency assets associated with state-linked threat actors. The substantive tension is between two legitimate victim populations — Kelp DAO depositors who lost $292 million in a recent attack, and families of older North Korean state-sponsored victims who hold court-validated but unenforced judgments — both with claims on the same frozen ETH.
READ THE STORY: Bitget
Palantir Reports 84% YoY US Government Revenue Growth as Iran War Doubles Maven Targeting System Usage
Bottom Line Up Front (BLUF): Palantir reported Q1 2026 quarterly revenue of $1.63 billion (up 85% year-over-year, with $1.28 billion from US customers) on its earnings call, with US government spending growing 84% year-over-year to $687 million — a 20% increase from the prior quarter — as Department of Defense usage of Palantir’s Maven targeting system doubled in four months following the start of the Iran War. The company raised full-year guidance to at least $7.65 billion, approximately $470 million above prior guidance. CTO Shyam Sankar told investors “Maven met its moment across real world events in Q1,” and the company has surged resources from its commercial business to support defense industrial base production and sustainment demand.
Analyst Comments:O’Ryan Johnson reports CEO Alex Karp framed the company’s posture explicitly: “We 100 percent prioritize this nation’s security over any other variable” and “the only thing we will put above you is US national security. And by the way, we’re more than willing to do this when it is unpopular or when it’s popular.” Karp acknowledged that Palantir’s work spans clients accused of war crimes including aid worker targeting and lethal strikes on suspected drug boats, plus the Iran war which the article describes as having killed at least 13 American service members and wounded more than 300, with unknown Iranian casualties. Karp characterized public reaction as “nine tenths of the world loves us, one tenth of the world professionally hates us.” The earnings call also surfaced the company’s $484 million US Navy and Maritime Industrial Base deal centered on ShipOS, with Palantir-cited efficiency gains including bill-of-materials approval time dropping from 200 hours to 15 seconds, contract review cycle improvements of 73% to 575%, and monthly material planning time reduction of 94%. Sankar’s “demand on the defense industrial base to ramp production and sustainment has been so acute that we have surged resources from our commercial business” framing reflects the operational tempo behind the revenue acceleration.
READ THE STORY: The Register
Influential ChatGPT-in-Education Meta-Analysis Retracted After 504 Citations and Half a Million Readers
Bottom Line Up Front (BLUF): Springer Nature retracted a meta-analysis claiming OpenAI’s ChatGPT positively impacts student learning nearly a year after its May 6, 2025 publication in Humanities & Social Sciences Communications, citing “discrepancies in the meta-analysis” that “undermine the confidence the Editor can place in the validity of the analysis and resulting conclusions.” The retraction notice was posted April 22, 2026, but only after the paper accumulated 504 total citations (262 in Springer Nature peer-reviewed journals), nearly half a million readers, and a 99th-percentile attention score. Ars Technica reports the authors had not responded to correspondence regarding the retraction.
Analyst Comments: Jeremy Hsu reports the paper analyzed 51 prior studies and claimed ChatGPT had “a large positive impact on improving learning performance” plus moderately positive effects on learning perception and higher-order thinking. Ben Williamson, a senior lecturer at Edinburgh’s Centre for Research in Digital Education, told Ars the paper was treated on social media as “one of the first pieces of hard, gold standard evidence that ChatGPT, and generative AI more broadly, benefits learners,” but that the underlying methodology mixed “very poor quality studies” and findings from studies “that simply cannot be accurately compared due to very different methods, populations, and samples.” Williamson also questioned the feasibility of the dataset itself: ChatGPT was released in November 2022, and “it is not feasible that dozens of high-quality studies about ChatGPT and learning performance could have been conducted, reviewed, and published in that time.” Ilkka Tuomi of Meaning Processing Ltd. raised similar concerns at the time of publication, writing that such meta-analyses produce “numbers that look [like] science” while drawing conclusions from “incompatible and ill-defined outcomes.” Williamson surfaced the retraction publicly on Bluesky and LinkedIn after the notice received minimal initial attention, expressing concern that the “headline finding that ChatGPT helps learning performance might persist despite its retraction” given how widely the original was shared in stripped-down form. The article frames the broader context: educators adapting to AI-enabled cheating, vendor framing of chatbots as “study mode” tools, and at least one country reintroducing physical books and pen-and-paper instruction.
READ THE STORY: arsTECHNICA
Apache HTTP Server CVE-2026-23918 Patched: HTTP/2 Double-Free Enables RCE in Version 2.4.66
Bottom Line Up Front (BLUF): The Apache Software Foundation released Apache HTTP Server version 2.4.67 on May 4, 2026, patching CVE-2026-23918, a double-free vulnerability in HTTP/2 protocol handling that affects version 2.4.66 with HTTP/2 enabled. The flaw is triggered when a specific “early reset” command is sent through HTTP/2, causing the server’s memory management to free the same memory block twice. Apache rates the impact “Important,” with potential outcomes ranging from denial-of-service crashes to remote code execution that could give attackers full control of the affected server. The vulnerability was privately reported December 10, 2025 by Bartlomiej Dmitruk (striga.ai) and Stanislaw Strzalkowski (isec.pl) and fixed in source code the next day, though the public patch took until May 4, 2026 to ship.
Analyst Comments: The double-free pattern is well-understood as a memory corruption class that frequently escalates from crash-only DoS to control-flow hijacking and code execution depending on heap state and exploit sophistication. Apache’s “Important” severity rating sits one tier below “Critical” in their classification, reflecting both the existence of mitigation paths (HTTP/2 can be disabled as a stopgap) and the absence of public exploitation evidence in this disclosure window. Mitigation guidance: update to 2.4.67 immediately; review server access and error logs for unusual HTTP/2 traffic patterns or unexpected server crashes that could indicate exploitation attempts; temporarily disable HTTP/2 if patching is not immediately feasible; and review network security configurations for defense-in-depth coverage. The disclosure-to-public-patch window of nearly five months between the December 10 private report and May 4 release is unusually long for a vulnerability with confirmed RCE potential, though the article does not address why Apache delayed the public release after fixing the source code in December.
READ THE STORY: GBhackers
Microsoft Details Code-of-Conduct-Themed AiTM Phishing Campaign Against 35,000 Users in 26 Countries; Q1 2026 Email Threat Landscape Hits 8.3 Billion Detections
Bottom Line Up Front (BLUF): Microsoft Defender Security Research Team and Microsoft Threat Intelligence disclosed a multi-stage credential-theft campaign observed April 14-16, 2026, targeting more than 35,000 users across over 13,000 organizations in 26 countries — 92% of targets in the US — using "code of conduct" review-themed lures combined with legitimate email delivery services to direct victims through CAPTCHA gates and adversary-in-the-middle (AiTM) phishing pages that harvest Microsoft credentials and tokens in real time, bypassing MFA. Top targeted sectors: healthcare and life sciences (19%), financial services (18%), professional services (11%), and technology and software (11%). Q1 2026 email threat data shows 8.3 billion total phishing threats detected, with QR code phishing the fastest-growing vector (146% increase from 7.6 million in January to 18.7 million in March) and credential harvesting the goal of the vast majority of attacks.
Analyst Comments: Ravie Lakshmanan reports the campaign uses "polished, enterprise-style HTML templates with structured layouts and preemptive authenticity statements" with display names including "Internal Regulatory COC," "Workforce Communications," and "Team Conduct Report," and subject lines like "Internal case log issued under conduct policy" and "Reminder: employer opened a non-compliance case log." Each message opens with a notice claiming the email was "issued through an authorized internal channel" with attachments "reviewed and approved for secure access" — preemptive authenticity framing designed to defuse user suspicion. PDF attachments contain links that initiate the credential harvesting flow, routing victims through CAPTCHA and intermediate pages before reaching the AiTM endpoint, with mobile and desktop targets receiving different final destinations. The broader Q1 2026 picture: nearly 80% of phishing was link-based with HTML and ZIP files dominating payloads, malware delivery declined to 5-6% by quarter-end, and BEC attacks totaled 10.7 million across the quarter. Two notable Q1 campaigns: a February 23-25 campaign sending 1.2 million messages to 53,000+ organizations in 23 countries using 401(k)/payment/invoice lures with SVG attachments routing through CAPTCHA to fake sign-in pages, and a March 17 campaign with 1.5 million messages to 179,000+ organizations in 43 countries using HTML attachments accounting for 7% of all malicious HTML observed that month — with infrastructure linked to Tycoon 2FA primarily, plus Kratos (formerly Sneaky 2FA) and EvilTokens. Following March's coordinated disruption operation against Tycoon 2FA, Microsoft observed the operators shifting away from Cloudflare hosting toward alternative platforms with comparable anti-analysis protections. Kaspersky separately documented attackers abusing Amazon Simple Email Service via leaked AWS access keys to bypass SPF, DKIM, and DMARC checks, framing the technique as "leveraging infrastructure that both users and security systems have grown to trust" rather than building dubious mail infrastructure from scratch.data strictly on demand, until Microsoft changes its architectural stance.
READ THE STORY: THN
Microsoft Edge Loads All Saved Passwords into Cleartext Memory at Startup; Microsoft Says "By Design"
Bottom Line Up Front (BLUF): Palo Alto Networks Norway disclosed at the BigBiteOfTech conference on April 29, 2026 that Microsoft Edge decrypts and loads every saved password into process memory as cleartext the moment the browser launches — not on-demand when a user visits a relevant website. Microsoft's official response classifies the behavior as "by design." A published proof-of-concept demonstrates that on shared computing environments such as terminal servers, an attacker with administrative rights can extract stored credentials from other users' running Edge processes, including users with currently disconnected sessions, as long as Edge is running in the background. The researcher (@L1v1ng0ffTh3L4N) tested every major Chromium-based browser and reports Edge is the only one operating this way.
Analyst Comments: Edge's at-startup eager decryption renders the browser's own re-authentication prompt (PIN or Windows password before viewing passwords in the built-in Password Manager UI) effectively theatrical, since the plaintext credentials already sit in process memory regardless of whether the UI prompt is satisfied. The PoC demonstrates a compromised admin account on a terminal server harvesting credentials for two separate user accounts running Edge in the background. Researcher published an educational tool on GitHub called "EdgeSavedPasswordsDumper" allowing security teams to verify the cleartext memory storage on their own systems. Operational implications are particularly acute for shared computing environments — terminal servers, Citrix/VDI deployments, multi-user workstations, jump hosts — where a single privileged compromise yields the password stores of every Edge user with the browser open. Recommended posture: enterprise users should avoid saving sensitive credentials in Edge directly and instead rely on dedicated third-party password managers that decrypt data strictly on demand, until Microsoft changes its architectural stance.
READ THE STORY: GBhackers
Items of interest
Trump’s Venezuela Strategy Tests the Limits of Regime Capture as Cuba Pressure Builds
Bottom Line Up Front (BLUF): War on the Rocks argues that the Trump administration’s capture of Nicolás Maduro and subsequent co-optation of Venezuela’s remaining regime may deliver short-term wins, but is unlikely to stabilize Venezuela, revive its oil sector, or restore democracy. The article frames the real strategic through-line as Cuba: severing Caracas-Havana ties and choking off subsidized fuel flows to push the Cuban regime toward collapse.
Analyst Comments: Charles Larratt-Smith writes that Trump’s administration has presented Maduro’s Jan. 3 capture as a foreign policy success and a model for other adversarial states, including Iran. But the article argues the Venezuela strategy faces major obstacles: degraded oil infrastructure, investor reluctance, the continued power of the post-Maduro ruling coalition, and the sidelining of Venezuela’s democratic opposition. The piece identifies Secretary of State and National Security Advisor Marco Rubio as a key driver of the Cuba-focused strategy, arguing that regime co-optation in Venezuela ruptures the Cuba-Venezuela lifeline while avoiding a second state-building project in the hemisphere.
READ THE STORY: War on the Rocks
Inside China’s Secret Spy Base in Cuba (Video)
FROM THE MEDIA: The Chinese Communist Party is operating a network of spy bases in Cuba just 90 miles off the coast of Florida. In July 2024 the Center for Strategic and International Studies published a a report outlining how they are growing a network of signals intelligence bases here. Similar to how the United States military runs intelligence gathering operations in Taiwan right near China - it appears like China is trying to turn the turntables back around.
OpenAI Codex Explained: The AI Revolutionizing How We Write Code (Video)
FROM THE MEDIA: IWhy is the relationship between the U.S. and Cuba so complicated? This video breaks down the history, the embargo, and what’s standing in the way of a resolution.
The selected stories cover a broad range of cyber threats and are intended to help readers frame key publicly discussed threats and improve overall situational awareness. InfoDom Securities does not endorse any third-party claims made in its original material or related links on its sites; the opinions expressed by third parties are theirs alone. For further questions, don’t hesitate to get in touch with InfoDom Securities at dominanceinformation@gmail.com.