Daily Drop (1282)
04-22-26
Wednesday, Apr 22, 2026 // (IG): BB // Ghostwire
CISA Flags Actively Exploited Cisco SD-WAN Manager Flaws
Bottom Line Up Front (BLUF): CISA has added three Cisco Catalyst SD-WAN Manager vulnerabilities to its Known Exploited Vulnerabilities catalog after confirming active exploitation in the wild. The affected platform sits at the center of enterprise traffic routing and policy enforcement, so a successful compromise can hand attackers deep control over network operations. This is not an edge-case bug story. If an exposed SD-WAN Manager is vulnerable, the blast radius could be the whole environment.
Analyst Comments: Management planes are always high-value, and SD-WAN infrastructure is especially sensitive because it touches routing, segmentation, policy, and visibility across distributed networks. The reported flaw chain is what makes this more serious: one issue leaks information, another can overwrite system files and raise privileges, and a third exposes credentials in recoverable form. That is enough to turn a management appliance into an attacker control point. Once that happens, the problem is no longer just patching a box. It becomes a trust problem for the network fabric behind it.
READ THE STORY: CyberPress
UK Spy Agency Points to China as the Most Persistent Cyber Threat
Bottom Line Up Front (BLUF): UK’s National Cyber Security Centre is warning that China remains the most significant long-term cyber threat to the United Kingdom. That fits the broader pattern: Beijing-linked operations are typically less about smash-and-grab disruption and more about sustained espionage, infrastructure access, and strategic positioning. For defenders, the takeaway is not panic. It is that cyber risk tied to state actors should be treated as a standing condition, not an occasional headline.
Analyst Comments: Chinese cyber operations are usually concerning because of their patience, scale, and targeting discipline. The threat is not just data theft. It is the slow accumulation of access across government, telecom, academia, defense, supply chain, and critical infrastructure environments. That kind of activity often blends into normal network noise until it is too late. The real challenge for defenders is that long-duration espionage campaigns do not always trigger the same urgency as ransomware or disruptive attacks, even though the strategic damage can be worse.
READ THE STORY: The Register
Terrarium Sandbox Flaw Lets Attackers Break Out and Run as Root
Bottom Line Up Front (BLUF): A critical flaw in Cohere AI’s open-source Terrarium sandbox can let attackers escape the intended Python execution boundary and run arbitrary commands as root on the host process. Tracked as CVE-2026-5752 and rated 9.3 CVSS, the bug stems from JavaScript prototype chain traversal in the Pyodide environment, turning a tool meant to safely run untrusted code into a potential breakout path. Because the project is no longer actively maintained, defenders should assume there may be no reliable upstream fix coming.
Analyst Comments: Terrarium, a Python sandbox developed by Cohere AI and deployed in Docker to run untrusted code, contains a critical vulnerability that allows arbitrary code execution through a JavaScript prototype chain traversal in the Pyodide WebAssembly environment. CERT/CC said successful exploitation can let an attacker break out of the sandbox, execute system commands as root within the container, access sensitive files like /etc/passwd, reach other services on the container network, and potentially escalate further. The flaw does not require special privileges or user interaction, though it does require local access. Researcher Jeremy Brown discovered and reported the issue. Because Terrarium is no longer actively maintained, the article says a patch is unlikely, leaving users to rely on mitigations such as disabling user code submission, segmenting networks, restricting access, monitoring container behavior, and hardening surrounding infrastructure.
READ THE STORY: THN
CastleRAT and ChainShell Signal a Modular Malware Pairing Defenders Should Watch
Bottom Line Up Front (BLUF): CastleRAT and ChainShell appear to be a modular malware pairing, with one component handling execution or payload delivery and the other providing remote access. The bigger takeaway is familiar: attackers keep using flexible, multi-stage toolsets that are easier to adapt and harder to detect. For defenders, the real concern is the behavior around delivery, persistence, and command-and-control.
Analyst Comments: One component handles execution or payload chaining, the other maintains remote access and operator control. That gives threat actors room to swap infrastructure, change payloads, and adapt mid-operation without rebuilding the whole kill chain. Defenders should assume anything described this way may support phishing-led access, scripted execution, privilege escalation, lateral movement, or follow-on payload delivery. The smart move is to focus less on the malware branding and more on the behaviors: unusual parent-child process chains, script interpreters spawning network activity, persistence changes, outbound C2 traffic, and signs of credential access.
READ THE STORY: GBhackers
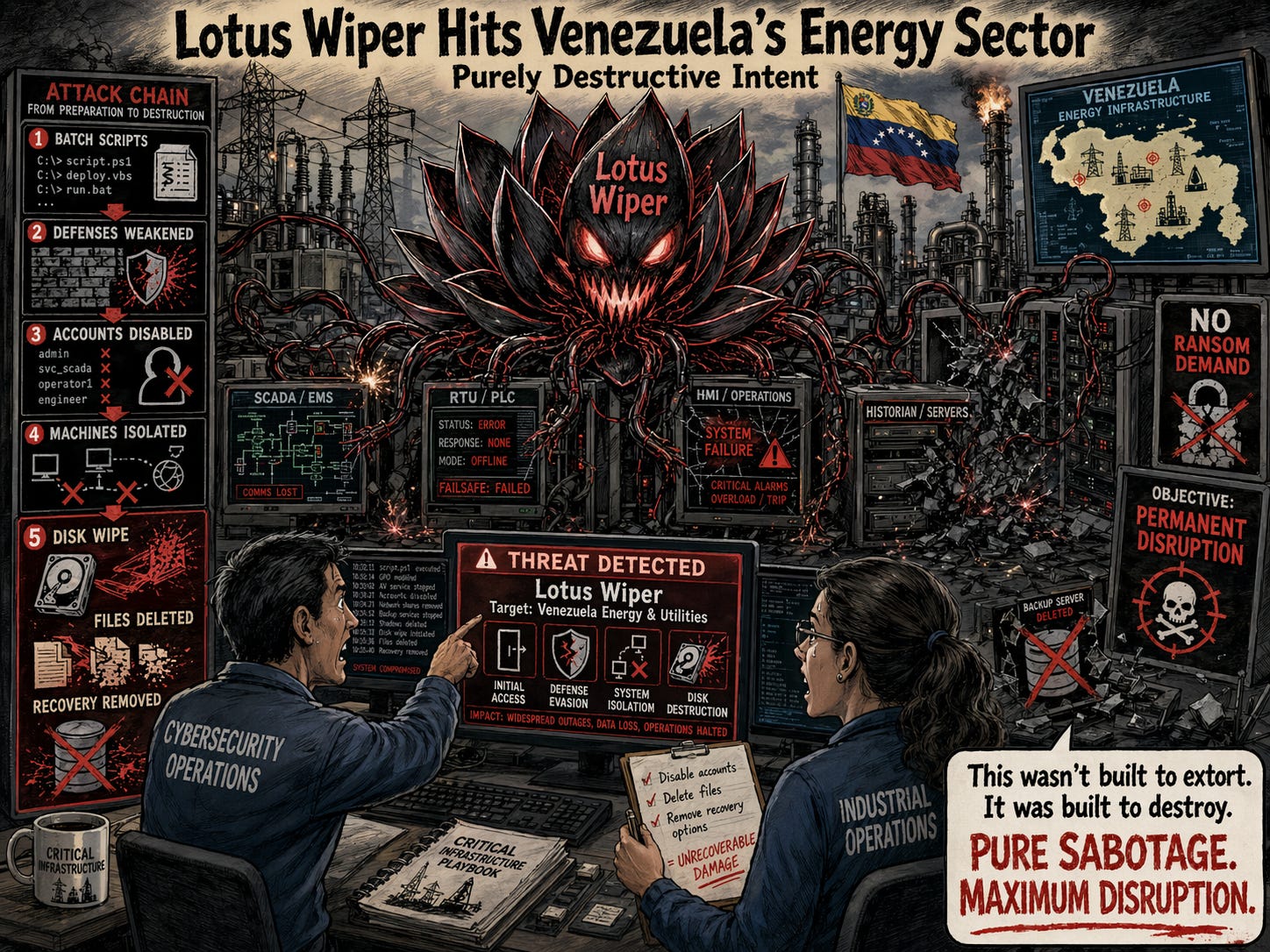
Lotus Wiper Hits Venezuela’s Energy Sector With Purely Destructive Intent
Bottom Line Up Front (BLUF): A highly destructive wiper dubbed Lotus Wiper was used against organizations in Venezuela’s energy and utilities sector, with the malware built to permanently destroy systems rather than extort money. According to Kaspersky’s analysis cited by Security Affairs, the attackers first used batch scripts to weaken defenses, disable accounts, isolate machines, and prepare the environment before launching a final payload that wiped disks, deleted files, and removed recovery options. This was not ransomware with a political paint job. It was a deliberate disruption operation aimed at making affected systems unrecoverable.
Analyst Comments: The pre-wipe staging matters as much as the payload itself: the attackers appear to have understood the environment, used native tools to break normal administration and recovery paths, and then deployed a wiper designed to finish the job. That points to preparation, not smash-and-grab opportunism. The targeting also matters. When destructive malware shows up in the energy sector, the concern is no longer just data loss. It is service disruption, loss of visibility, delayed restoration, and the possibility that the malware deployment is only one part of a broader campaign.
READ THE STORY: Security Affairs
Mustang Panda Expands LOTUSLITE Campaigns Beyond Policy Targets
Bottom Line Up Front (BLUF): Mustang Panda is using an updated LOTUSLITE backdoor in campaigns aimed at India’s banking sector while also targeting South Korean and U.S. policy circles tied to Korean peninsula and Indo-Pacific issues. The malware remains focused on espionage, not smash-and-grab crime, with remote shell, file operations, and session control delivered through an evolving toolset that researchers say is still being actively refined. The notable shift is not just the malware update. It is the broadening target set.
Analyst Comments: The campaign starts with a malicious CHM file containing a legitimate executable, a rogue DLL, and an HTML lure that prompts the victim to click “Yes.” That interaction silently pulls down JavaScript from cosmosmusic[.]com, which then extracts and runs the malware through DLL side-loading. The updated LOTUSLITE DLL, named dnx.onecore.dll, communicates over HTTPS with the dynamic DNS domain editor.gleeze[.]com and supports remote shell access, file operations, and session management. Researchers said the same infrastructure and tradecraft also turned up in artifacts targeting South Korean diplomatic and policy-linked individuals, as well as U.S. policy circles involved in Korean peninsula affairs and Indo-Pacific security discussions.
READ THE STORY: THN
Mythos Hype Is Real Enough — Just Not for the Reasons People Think
Bottom Line Up Front (BLUF): Early third-party analysis suggests Mythos is a real step forward in offensive cyber capability, but not the instant game-changer the hype cycle makes it sound like. The bigger story is the trendline: frontier models are getting steadily better at vulnerability discovery, multi-step attack planning, and chaining weaknesses together. That does not mean every attacker suddenly gets elite capability overnight. It means defenders should stop treating AI-assisted exploitation as a future problem.
Analyst Comments: It cites the UK AI Security Institute’s testing, which found Mythos continuing a multi-year trend of improving model performance on cybersecurity tasks, including strong results on expert-level CTF problems and partial success on a 32-step enterprise attack simulation called “The Last Ones.” The write-up also highlights a practical constraint raised by commentator Drew Breunig: Mythos may require enormous token budgets to achieve those top-end results, turning some of the offensive-versus-defensive balance into a question of who can afford to run the model hard enough. A third perspective, from Aisle, argues that smaller and cheaper models may still handle narrower security subtasks effectively, even if they cannot match Mythos end to end. The overall takeaway is that Mythos may be overhyped as a singular breakthrough, but the broader trend it points to is very real and worth taking seriously.
READ THE STORY: HABR
French Government Portal Breach Could Expose Data on Millions of Citizens
Bottom Line Up Front (BLUF): French authorities have confirmed a breach involving the National Agency for Secure Documents, the government body behind the portal used for passports, national ID cards, driver’s licenses, and vehicle registration. According to the reporting, attackers accessed extensive account and identity data, with threat intelligence estimates suggesting the impact could reach up to 19 million people. Even if portal access itself was not directly compromised, this is still a serious exposure because the stolen data is exactly the kind that fuels phishing, identity fraud, and follow-on social engineering.
Analyst Comments: The compromised system supports major citizen services, including identity cards, passports, vehicle registration certificates, and driver’s licenses. According to the article, attackers extracted personal and professional account records containing login IDs, account identifiers, names, email addresses, phone numbers, birth details, postal addresses, and identity verification information. Authorities said supplementary files and uploaded document attachments were not exposed, and the leaked data does not directly allow access to portal accounts. The agency reported the incident to CNIL, briefed ANSSI, referred the matter to the Paris public prosecutor, and began notifying affected citizens. Researchers quoted in the piece warned that the exposed data could be used in highly targeted phishing and smishing campaigns impersonating official services.
READ THE STORY: GBhackers
Mozilla Says AI Like Mythos Will Shape the Future of Cyber Defense
Bottom Line Up Front (BLUF): Mozilla is reportedly arguing that models like Mythos will force defenders to rethink how security work gets done, as AI becomes more capable at finding weaknesses, chaining attack steps, and operating at machine speed. The core takeaway is hard to dispute: if offensive capability is getting cheaper and faster through AI, defensive workflows built around human bottlenecks are going to struggle. For security teams, the real issue is not one model. It is the direction of travel.
Analyst Comments: Based on the URL and headline, the piece appears to focus on how Mozilla views the longer-term security impact of advanced AI models such as Mythos. The likely argument is that increasingly capable models will not just help attackers but will also force defenders to change how they identify risk, validate exposure, and respond to threats. In practice, that usually means more emphasis on automated testing, faster remediation loops, stronger baseline hardening, and using AI for defensive tasks like code review, anomaly detection, vulnerability triage, and attack simulation. The broader implication is that organizations should stop treating AI-enabled cyber capability as hypothetical and start planning around it as an operational reality.
READ THE STORY: The Register
Asia’s Digital Supply Chain Is Creating a More Complicated Risk Environment
Bottom Line Up Front (BLUF): Asian organizations face a distinct supply chain security problem driven by cross-border regulations, uneven vendor maturity, tightly connected digital ecosystems, and growing reliance on AI. The issue is not just third-party risk in the usual sense. It is that companies often operate across multiple countries, each with different compliance standards, oversight models, and security baselines, while stitching together cloud services, data vendors, automation, and AI models into the same environment. That creates more exposure and less certainty about who is introducing risk.
Analyst Comments: In Asia, the complexity comes from operating in a region that is deeply interconnected commercially but far less uniform from a regulatory and security standpoint. Add AI to that mix and the problem gets worse fast. Every new model, plugin, API, or data dependency expands the trust chain. The part security teams need to take seriously is visibility. If you do not know who your vendors are, what technology they rely on, which country’s rules apply, or how those tools connect into your environment, you are not really managing supply chain risk. You are just hoping it behaves.
READ THE STORY: DR
Items of interest
1,370 Microsoft SharePoint Servers Exposed to Spoofing Risk
Bottom Line Up Front (BLUF): Microsoft SharePoint servers are reportedly exposed to spoofing attacks, pointing to another case where externally reachable enterprise infrastructure may be left open to abuse through weak configuration, incomplete hardening, or unaddressed flaws. If the reporting is accurate, the immediate concern is not just spoofing itself but what it enables next—credential theft, user deception, session abuse, or deeper access into trusted collaboration environments. For defenders, any internet-facing SharePoint instance deserves a hard look right now.
Analyst Comments: SharePoint keeps showing up in security reporting for a reason: it sits close to users, documents, identity workflows, and business-critical content. That makes even “limited” issues worth paying attention to. A spoofing problem on a collaboration platform is not just a branding or UI nuisance. In the right hands, it can become a delivery mechanism for phishing, fake trust signals, or user actions that look legitimate enough to get past initial skepticism. If this exposure really affects more than a thousand servers, the bigger lesson is familiar—organizations still leave core Microsoft infrastructure too visible and too trusted. That is a bad combination.
READ THE STORY: GBhackers
Microsoft SharePoint Zero-Day Is Already Being Exploited | CVE-2026-32201 Explained (Video)
FROM THE MEDIA: The flaw allows anonymous attackers to craft specially structured links that appear legitimate inside SharePoint environments. Once opened, these links render malicious content disguised as trusted documents, enabling phishing campaigns, redirects, and document manipulation.
Microsoft Copilot Is Exposing a Massive SharePoint Security Problem (Video)
FROM THE MEDIA: Years of oversharing across SharePoint and OneDrive are turning into a serious security risk in the age of AI. In this Techstrong TV interview, Andy Syrewicze, Technical Evangelist at Hornetsecurity, explains how Microsoft Copilot can surface sensitive files to users who were never intended to have access, exposing the hidden dangers of weak permissions, poor governance and unchecked data sprawl.
The selected stories cover a broad range of cyber threats and are intended to help readers frame key publicly discussed threats and improve overall situational awareness. InfoDom Securities does not endorse any third-party claims made in its original material or related links on its sites; the opinions expressed by third parties are theirs alone. For further questions, don't hesitate to get in touch with InfoDom Securities at dominanceinformation@gmail.com.