Daily Drop (1281)
04-21-26
Tuesday, Apr 21, 2026 // (IG): BB // Ghostwire
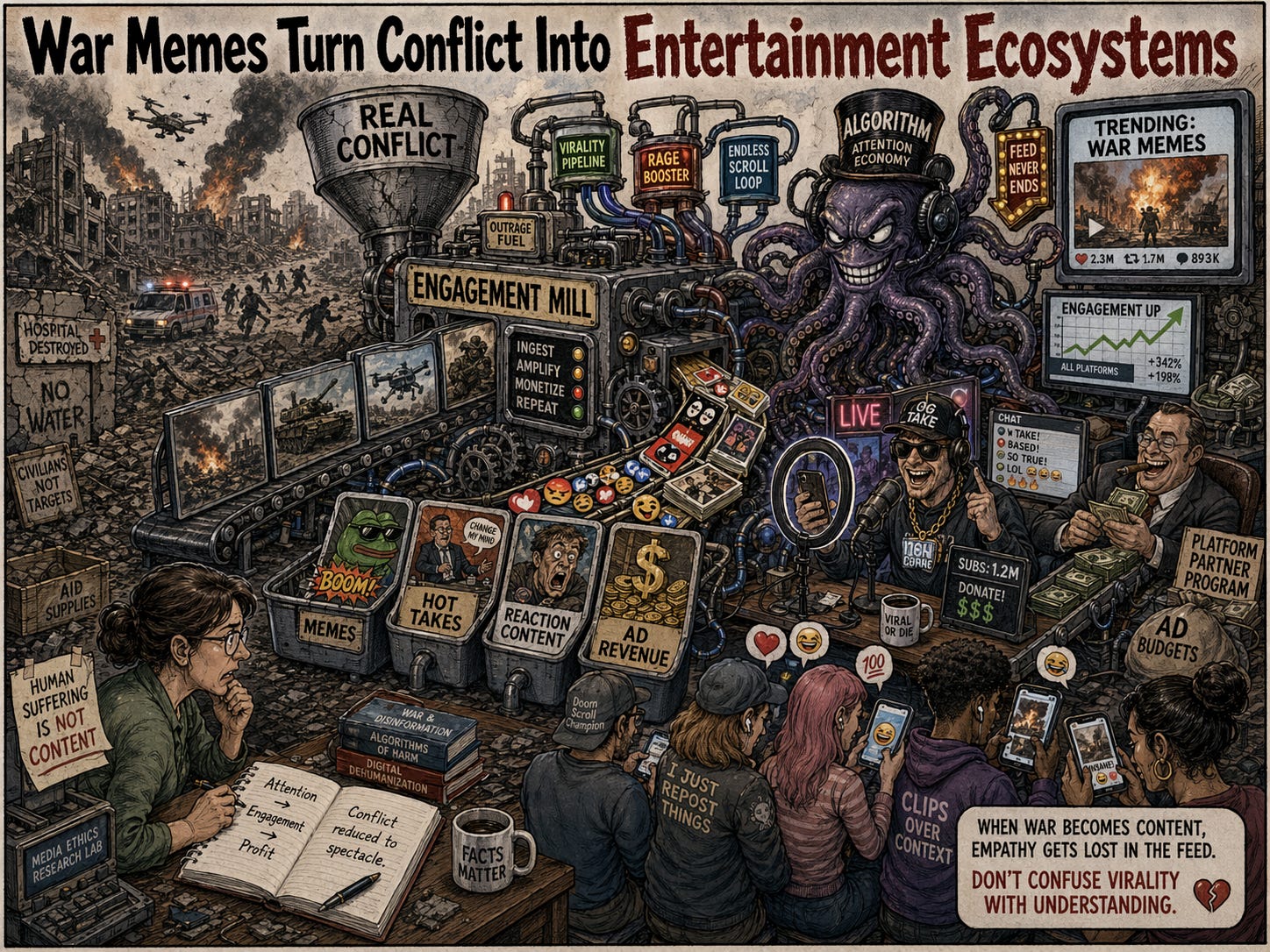
War Memes Turn Conflict Into Entertainment Ecosystems
Bottom Line Up Front (BLUF): WIRED argues that war memes are doing more than helping people cope—they are turning conflict into fast, shareable content stripped of history, consequence, and context. The result is a familiar social media pattern: jokes and ironic posts spread faster than facts, propaganda blends into entertainment, and users walk away feeling informed without actually understanding the conflict. For analysts, the point is not that dark humor exists. It is that platform incentives now industrialize it.
Analyst Comments: This is a media literacy problem as much as a culture problem. Gallows humor during wartime is nothing new, but algorithms changed the scale, speed, and purpose of it. A joke that once stayed inside a community now becomes a global reaction format in minutes, usually detached from the people actually living through the event. That opens the door for a pretty ugly mix of desensitization, false confidence, and propaganda disguised as irony. The most important point here is that repeated exposure is not the same thing as understanding. People can recognize the meme, repeat the headline, and still have no real grasp of the conflict underneath it. That is exactly the kind of environment information operations thrive in.
READ THE STORY: Wired
Fermi America’s Boardroom Shake-Up Deepens Doubts Around Trump-Branded Datacenter Project
Bottom Line Up Front (BLUF): The Register reports that Fermi America’s already shaky effort to build a massive AI datacenter and energy campus in West Texas just took another hit, with its CEO quitting abruptly and its CFO stepping aside days later. The company is still chasing power equipment, still looking for an anchor hyperscaler tenant, and now trying to calm investors while rebranding the effort as “Fermi 2.0.” For anyone tracking AI infrastructure buildouts, this looks less like momentum and more like a project struggling to prove it is real at scale.
Analyst Comments: This is what overpromised infrastructure starts to look like when reality shows up. A 17 GW vision tied to nuclear, gas, solar, AI, national security, and Trump branding was always going to need serious execution discipline and serious customers. Right now, it appears to have neither locked in. The executive churn matters, but the bigger red flag is that the company still seems to be selling ambition more than delivery. When a project this large is dealing with leadership exits, customer uncertainty, equipment constraints, and a stock down more than 80 percent from its high, the story is no longer just about growth pains. It is about whether the thing can actually get off the ground in the way it was pitched.
READ THE STORY: The Register
Over 800 Android Apps Targeted in PIN-Stealing Trojan Campaign
Bottom Line Up Front (BLUF): Researchers say four Android banking trojan campaigns are targeting more than 800 apps by abusing overlays, Accessibility permissions, and sideloaded fake apps to steal PINs, credentials, and authentication data. The real problem is not just malware scale. It is how effectively these operators are turning legitimate Android features into surveillance and account-takeover tools.
Analyst Comments: This is classic mobile banker tradecraft, but scaled and polished. Attackers are not relying on exotic exploits here. They are using permission abuse, fake app workflows, cloned overlays, and social engineering because that still works. Accessibility remains one of the most dangerous permissions on Android when users grant it to untrusted apps, and overlay abuse keeps giving malware authors a reliable way to capture PINs and steer user interaction. The fact that these campaigns span banking, crypto, and social platforms tells you the actors are chasing whatever accounts can be monetized fastest. For defenders, this is another reminder that mobile security failures are often permission-governance failures first.
READ THE STORY: TechRepublic
WhatsApp Metadata Exposure Raises Fresh Privacy Concerns
Bottom Line Up Front (BLUF): WhatsApp may expose user metadata even though message content is protected by end-to-end encryption. That matters because even if nobody can read the messages themselves, metadata can still show who talked to whom, when they talked, and how often. For security teams, the takeaway is simple: encrypted messages do not automatically mean private communications.
Analyst Comments: End-to-end encryption protects message content, but it does not hide everything around it. Metadata can still be valuable for tracking behavior, mapping relationships, and building a pretty detailed picture of user activity. That is not a small gap. In some cases, metadata is enough on its own to support surveillance, targeting, or profiling. For enterprises, this is another reminder that consumer messaging apps are not built to solve every privacy problem. Strong encryption helps, but it should not be mistaken for full operational privacy.
READ THE STORY: DR
Security Expert Demonstrates That VPNs Still Matter: Encrypted DNS and TLS Don’t Hide Browsing History
Bottom Line Up Front (BLUF): New research highlighted by Cybernews argues that VPNs conceal a broader slice of user web activity than transport-layer protections like HTTPS/TLS or encrypted DNS alone. The core point is straightforward: TLS encrypts content in transit and encrypted DNS obscures lookups, but neither fully hides destination metadata from network observers. For defenders, this is less a revelation than a reminder that privacy controls operate at different layers—and threat models matter.
Analyst Comments: This is a useful correction to a common misunderstanding. A lot of users hear “HTTPS” or “encrypted DNS” and assume their browsing is effectively private from the local network, ISP, or other middleboxes. It is not. TLS protects payloads; DoH/DoT protects DNS queries; neither prevents an observer from inferring plenty from IP connections, SNI-related leakage in some scenarios, traffic timing, packet sizes, and destination patterns. A VPN shifts that visibility away from the local network and ISP by tunneling traffic to the VPN provider, but that is a trust transfer, not magic invisibility. From a security standpoint, the takeaway is practical: VPNs can materially improve privacy against local or access-network surveillance, but they do not eliminate endpoint risk, browser fingerprinting, account tracking, or provider-side logging exposure. Anyone pitching VPNs as a total privacy solution is overselling it.
READ THE STORY: Cybernews
Swiss Privacy Goes Global: Proton VPN Grows Coverage to 145 Countries
Bottom Line Up Front (BLUF): Proton VPN has expanded its network to roughly 20,000 servers across 145 countries, giving it the widest geographic coverage among the VPN providers CNET tested. The company says the expansion is aimed at improving access in countries where censorship, surveillance, and online restrictions are common.
Analyst Comments: CNET reported that Proton VPN expanded its network over the past two weeks to approximately 20,000 servers in 145 countries, adding new locations in Lebanon, Nicaragua, Gabon, Papua New Guinea, Kyrgyzstan, and the Democratic Republic of the Congo. According to the article, that gives Proton the broadest worldwide country coverage of any VPN provider CNET has tested, exceeding NordVPN’s 135-country footprint, ExpressVPN’s 105-country reach, and Surfshark’s 11-country presence. Proton executive David Peterson said the expansion supports the company’s stated mission of maintaining open internet access in places where online freedom is restricted or under threat.
READ THE STORY: CNET
Next.js Developer Vercel Warns of Customer Credential Compromise After Context.ai Breach
Bottom Line Up Front (BLUF): Vercel disclosed a security incident involving unauthorized access to internal systems that resulted in the compromise of credentials for a limited subset of customers. The company traced the intrusion to a Vercel employee’s use of Context.ai, where a compromised OAuth token and overly broad permissions appear to have enabled access into Vercel’s Google Workspace and downstream environments.
Analyst Comments: The core issue is not just that Context.ai got hit. It is that one third-party AI workflow, paired with permissive OAuth consent and weak enterprise guardrails, created a bridge into Vercel’s internal environment. That is the real lesson here. This looks less like an advanced intrusion and more like a stacked access-control failure across vendors, identity, and cloud admin hygiene. Expect more incidents like this as AI tools continue to accumulate cross-platform privileges faster than most organizations can govern them.
READ THE STORY: The Register
Indonesia Suspends Game Rating System After Alleged Leak of Developer Credentials and Unreleased Titles
Bottom Line Up Front (BLUF): Indonesia has paused its game rating system, IGRS, after allegations that it exposed roughly 1,000 developer email addresses and footage of unreleased games. Even if parts of the claim are still being investigated, the incident is a reminder that government-run digital platforms can create the same credential exposure and pre-release content risks seen in poorly secured private-sector systems.
Analyst Comments: A government platform tied to game publishing and classification apparently became a source of developer credential exposure and unreleased content leakage, which is the kind of breach that can damage trust fast even if the technical impact turns out narrower than first claimed. The bigger issue is governance. Systems that collect publisher data, preview assets, and contact information tend to be treated like admin portals rather than sensitive targets, right up until someone shows otherwise. If the allegations hold, this is a pretty clean example of weak access control turning a compliance platform into a leak source.
READ THE STORY: The Register
Microsoft Releases Emergency Updates to Fix Windows Server Issues
Bottom Line Up Front (BLUF): Microsoft has issued out-of-band updates to address multiple Windows Server problems introduced by the April 2026 security updates, including failed installation of KB5082063 on Windows Server 2025 and LSASS crashes that can send domain controllers into reboot loops. For defenders and admins, this is an availability and operational stability issue first, but anything that destabilizes domain controllers immediately raises incident-response noise and authentication risk across enterprise environments.
Analyst Comments: When domain controllers start crashing and rebooting after updates, teams lose time fast trying to separate bad patches from malicious activity, especially when LSASS is involved. The good news is Microsoft moved with OOB updates instead of letting admins sit in the blast radius. The bad news is this adds to a growing pattern where patch deployment on critical Windows infrastructure now carries enough operational risk that many teams are forced into cautious rollout cycles even for important fixes. If you run domain controllers or Server 2025 in production, this is not optional housekeeping. It needs validation and remediation now.
READ THE STORY: Bleeping Computer
Claude Desktop Pre-Authorizes Browser Access Without Consent, Prompting Privacy and Security Concerns
Bottom Line Up Front (BLUF): The Register reports that Anthropic’s Claude Desktop for macOS installs Native Messaging manifest files that modify how Chromium-based browsers interact with local executables, including for browsers not yet installed on the device. The core issue is not a flashy exploit but a trust-boundary violation: silent cross-application configuration changes and pre-authorized browser integration create security, privacy, and potential regulatory risk.
Analyst Comments: Calling this “spyware” is arguable. Calling it a bad security pattern is not. A desktop app quietly planting integration hooks for other vendors’ browsers, without clear opt-in, is exactly the sort of behavior that gets security teams angry and regulators interested. The technical risk is straightforward: pre-positioned bridges from browser extensions into local executables expand attack surface, especially when prompt injection and extension abuse are already established concerns. Even if Anthropic intended this as product convenience, the implementation reads like a consent failure and a trust failure. That matters just as much as the legal debate.
READ THE STORY: The Register
Serial-to-IP Devices Hide Thousands of Old and New Bugs, Raising OT Risk at the Network Edge
Bottom Line Up Front (BLUF): Forescout researchers found 20 new vulnerabilities in widely used serial-to-IP converters and estimate that the same device class is burdened with thousands of additional known flaws across outdated software stacks. These converters sit in the middle of industrial environments translating legacy machine communications into Ethernet traffic, which makes them a high-value target and a dangerous single point of failure when exposed or compromised.
Analyst Comments: These devices, also called serial device servers or serial-to-Ethernet converters, translate communications between legacy industrial machinery and modern IP networks and are widely used in SCADA and other OT environments. Forescout estimated that more than 10 million such devices may be deployed worldwide, with tens of thousands exposed on the public internet. Among the new findings, the EDS5000PS reportedly contained five remote code execution vulnerabilities, including two critical flaws rated CVSS 9.8 and three additional high-severity issues that require authentication.
READ THE STORY: DR
Researchers Detect ZionSiphon Malware Targeting Israeli Water, Desalination OT Systems
Bottom Line Up Front (BLUF): Darktrace identified a new malware strain, ZionSiphon, built to target Israeli water treatment and desalination environments by scanning OT-relevant services and attempting sabotage of chlorine and pressure controls. The current sample appears incomplete, but the tradecraft matters: it shows continued experimentation with politically motivated ICS malware that blends propagation, persistence, and industrial protocol abuse.
Analyst Comments: Even unfinished OT malware deserves attention when it is this specific. ZionSiphon is not just generic destructive code with political messaging slapped on top; it includes geographic targeting, environmental checks tied to water infrastructure, and protocol logic for Modbus, DNP3, and S7comm. That points to intent that goes beyond hacktivist theater. The fact that some functions appear broken does not make this harmless. It makes it early. Defenders in critical infrastructure should treat this as a warning shot: threat actors are still iterating on ICS-specific sabotage tooling, and removable-media propagation is a reminder that older intrusion paths still matter in segmented environments.
READ THE STORY: THN
Hackers Exploit CVE-2024-3721 to Deploy Nexcorium Malware on TBK DVRs
Bottom Line Up Front (BLUF): Attackers are exploiting CVE-2024-3721, an OS command injection flaw in TBK DVR devices, to deploy Nexcorium, a new Mirai-based botnet variant designed for DDoS operations. The campaign shows the same old IoT problem in action: exposed devices, weak defaults, and slow patching still give threat actors an easy path to mass compromise.
Analyst Comments: Threat actors do not need sophistication when internet-facing IoT gear remains under-patched and protected by default credentials. The addition of multi-architecture payloads, persistence mechanisms, and fallback propagation through older Huawei-targeting exploits suggests the operators are focused on scale and durability, not stealth. For defenders, the real issue is asset exposure and hygiene: if TBK DVRs or similar embedded systems are still reachable and unmanaged, they are low-effort botnet fuel.
READ THE STORY: CyberPress
LayerZero Ties KelpDAO Exploit to Lazarus Subgroup TraderTraitor
Bottom Line Up Front (BLUF): LayerZero says early indicators link the April 18 KelpDAO exploit to TraderTraitor, a subgroup of North Korea’s Lazarus Group, making it the largest DeFi theft disclosed so far in 2026. According to the company, the attack did not exploit the LayerZero protocol directly but instead targeted trust in the transaction verification path by poisoning downstream RPC infrastructure relied on by its DVN.
Analyst Comments: In a post on X, LayerZero described the incident as a “highly sophisticated attack” engineered to manipulate or poison downstream RPC infrastructure by compromising a quorum of the RPC systems its DVN used to verify transactions. The company said the incident did not stem from an exploit in the protocol itself, the DVN, or key management. The report says the theft is now the largest DeFi loss of 2026, surpassing the $285 million Drift Protocol breach from April 1, which investigators also linked to North Korean state-backed actors. BeInCrypto also noted prior US government links between the same group and the February 2025 Bybit hack, and cited Chainalysis data showing North Korea-linked hackers stole a record $2.02 billion from crypto platforms in 2025, up 51% year over year. Market impact followed quickly: Aave’s total value locked reportedly fell by $8.45 billion over two days, while total DeFi TVL dropped from $99.497 billion to $86.286 billion, a decline of $13.21 billion.
READ THE STORY: Be in Crypto
Attackers Abuse QEMU Virtual Machines to Hide Credential Theft and Ransomware Staging
Bottom Line Up Front (BLUF): Threat actors are increasingly using QEMU virtual machines as covert attack containers, running credential theft, tunneling, lateral movement, and ransomware staging inside guest environments that host-based security tools often cannot inspect. Recent campaigns tracked by Sophos as STAC4713 and STAC3725 show this tradecraft maturing into a repeatable playbook that gives attackers stealth, persistence, and a cleaner path to domain compromise and ransomware deployment.
Analyst Comments: Instead of fighting EDR head-on, the attacker brings a lightweight hypervisor and works from inside a hidden guest OS where visibility drops off fast. That makes detection harder, containment slower, and forensics messier. The real concern is not QEMU itself. It is the operational model: covert VM deployment, stealth tunneling, credential access, AD theft, and ransomware prep all bundled into one workflow. Expect this to stick, especially among actors who already know how to live off the land and want a quieter staging area on compromised hosts.
READ THE STORY: GBhackers
JanaWare Ransomware Hits Turkish Users via Tailored Adwind RAT
Bottom Line Up Front (BLUF): A regionally targeted ransomware campaign dubbed JanaWare is using a customized Adwind RAT to infect users in Turkey through phishing emails and Google Drive-hosted payloads. The operation is notable less for scale than for discipline: geofencing, polymorphic JAR files, and long-running low-visibility activity make it the kind of localized threat that can sit below the industry radar for years.
Analyst Comments: JanaWare appears built for volume inside a narrow geography, with ransom demands low enough to pressure home users and SMBs into paying quickly. The use of a customized Adwind variant, Turkish-only execution checks, and basic but effective evasion shows a practical operator mindset: stay local, stay noisy only where it counts, and avoid attracting broader scrutiny. The more interesting takeaway is the geofencing. Threat actors are getting better at shrinking their footprint to reduce analyst visibility, which means campaigns like this can remain active for years without becoming a major headline.
READ THE STORY: GBhackers
China-Linked Route Exposed After US Seizes Iran-Bound Ship With Suspected Dual-Use Cargo
Bottom Line Up Front (BLUF): U.S. forces seized the Iranian-flagged cargo vessel Touska in the Gulf of Oman while it was en route to Bandar Abbas, with officials investigating suspected dual-use cargo aboard. The ship’s recent transit through Chinese ports and Malaysia is drawing attention to the maritime trade routes Iran may still be using to sustain sensitive supply flows under pressure and blockade conditions.
Analyst Comments: If the reporting holds, the real significance is the route: Chinese port activity, transit through Southeast Asian waters known for opaque cargo handling, and a run toward Iran during an active U.S. maritime pressure campaign. That does not prove Chinese state involvement in this specific shipment, and the article does not establish that. But it does highlight how dual-use logistics can move through commercially plausible pathways that are hard to untangle in real time. The attempted transit despite a known blockade also suggests the cargo may have been viewed as operationally important.
READ THE STORY: FN
Protests From Japan of China’s Oil and Gas Projects in the East China Sea
Bottom Line Up Front (BLUF): Japan has formally protested what it says is a new Chinese structure tied to oil and gas development on the Chinese side of the East China Sea median line, an area where maritime boundaries remain unresolved. The dispute is not new, but continued unilateral development keeps raising the temperature in a region already strained by overlapping EEZ claims, the Senkaku dispute, and broader Taiwan-related tensions.
Analyst Comments: According to the report, the EEZ and continental shelf boundaries in the East China Sea have never been fully settled, and Japan has long opposed Chinese oil and gas development in the area until delimitation talks resume. The article notes that China and Japan reached an agreement in 2008 to cooperate on development of certain mineral resources, including the Shirakaba field, but the arrangement was never finalized. China has continued unilateral development since then, and Japan’s Ministry of Defense reportedly counts 22 Chinese offshore structures in the area. The report also places the dispute in the broader context of tensions over the Senkaku Islands and Taiwan, including Japan’s recent transit of the Taiwan Strait and Beijing’s sharp response.
READ THE STORY: Maritime-executive
ASML Just Got Hit by a New China Export Threat. Is This a Buying Opportunity or a Red Flag
Bottom Line Up Front (BLUF): A proposed U.S. bill, the MATCH Act, would tighten semiconductor export controls by not only restricting new ASML equipment sales to China but also cutting off servicing for existing systems. That matters because China has been one of ASML’s biggest revenue drivers, and service revenue is high-margin, sticky business that investors tend to treat as durable.
Analyst Comments: The real issue here is not whether ASML’s moat is broken. It is not. The company still dominates EUV lithography, and China still has no credible near-term replacement for that capability. The problem is that geopolitics keeps taking a larger bite out of the company’s China exposure, and this proposal goes after the installed base, not just future shipments. That is a much more serious escalation because it attacks recurring revenue and gradually degrades the usefulness of already deployed tools. For long-term investors, the strategic case for ASML remains intact. For everyone else, the message is simpler: China revenue is getting less stable, not more.
READ THE STORY: Fool
How Big of a Threat Is Mythos
Bottom Line Up Front (BLUF): Foreign Policy reports that Anthropic’s Claude Mythos Preview has reignited debate over offensive AI risk after the company said the model was capable of finding and exploiting zero-day vulnerabilities at scale and chose not to release it publicly. Instead, Anthropic is limiting access to a small group of major technology firms and critical infrastructure operators under an early-access program called Project Glasswing.
Analyst Comments: The headline risk here is not just that Mythos may be unusually capable. It is that the security industry now has to grapple with a model that appears to compress vulnerability discovery and exploitation into something faster, broader, and harder to control. Anthropic’s decision to restrict release suggests the company thinks the capability crosses a threshold from interesting to dangerous. That said, the article is still reporting Anthropic’s own claims, and those claims deserve scrutiny. AI vendors have every incentive to frame capability in dramatic terms. Even so, if a model can reliably surface zero-days across major operating systems and browsers, then the strategic question stops being whether offensive AI matters and shifts to who gets access first, defenders or attackers.
READ THE STORY: FP
Items of interest
China Signals Tighter Crackdown on VPNs and Other Internet Circumvention Tools
Bottom Line Up Front (BLUF): Reports of new internal notices and regulatory activity suggest China may be preparing a broader crackdown on VPNs, proxy services, and other tools used to access foreign websites beyond the Great Firewall. If enforcement tightens, the move would further restrict access to uncensored news, academic materials, and overseas platforms for ordinary Chinese internet users.
Analyst Comments: VPNs and related “airport” services matter because they punch holes in China’s information perimeter. The state can tolerate a lot, but not at scale, and especially not when circumvention becomes normalized among students, professionals, and ordinary users just trying to reach the wider internet. What stands out here is the convergence of signals: provider notices, telecom pressure, ministry involvement, and ideological framing from the Cyberspace Administration of China. None of that guarantees a sweeping new enforcement wave on its own, but together it looks less like isolated compliance noise and more like coordinated preparation.
READ THE STORY: Bitterwinter
China tightens VPN restrictions across the board (Video)
FROM THE MEDIA: The significance here is less any single fine or police visit and more the pattern: enforcement appears to be moving beyond VPN developers and sellers toward ordinary users, enterprises, and even people who help others bypass controls. The transcript describes fines for personal VPN use, police visits triggered by overseas services, telecom notices restricting outbound connectivity, and draft legal language that would broaden liability for providing circumvention support.
MIIT VPN Crack Down (Video)
FROM THE MEDIA: The Ministry of Industry and Information Technology urgently summons the three major telecom operators for a comprehensive VPN cleanup in China by 2026.
The selected stories cover a broad range of cyber threats and are intended to help readers frame key publicly discussed threats and improve overall situational awareness. InfoDom Securities does not endorse any third-party claims made in its original material or related links on its sites; the opinions expressed by third parties are theirs alone. For further questions, don't hesitate to get in touch with InfoDom Securities at dominanceinformation@gmail.com.