Daily Drop (1271)
04-03-26
Friday, Apr 03, 2026 // (IG): BB // Ghostwire
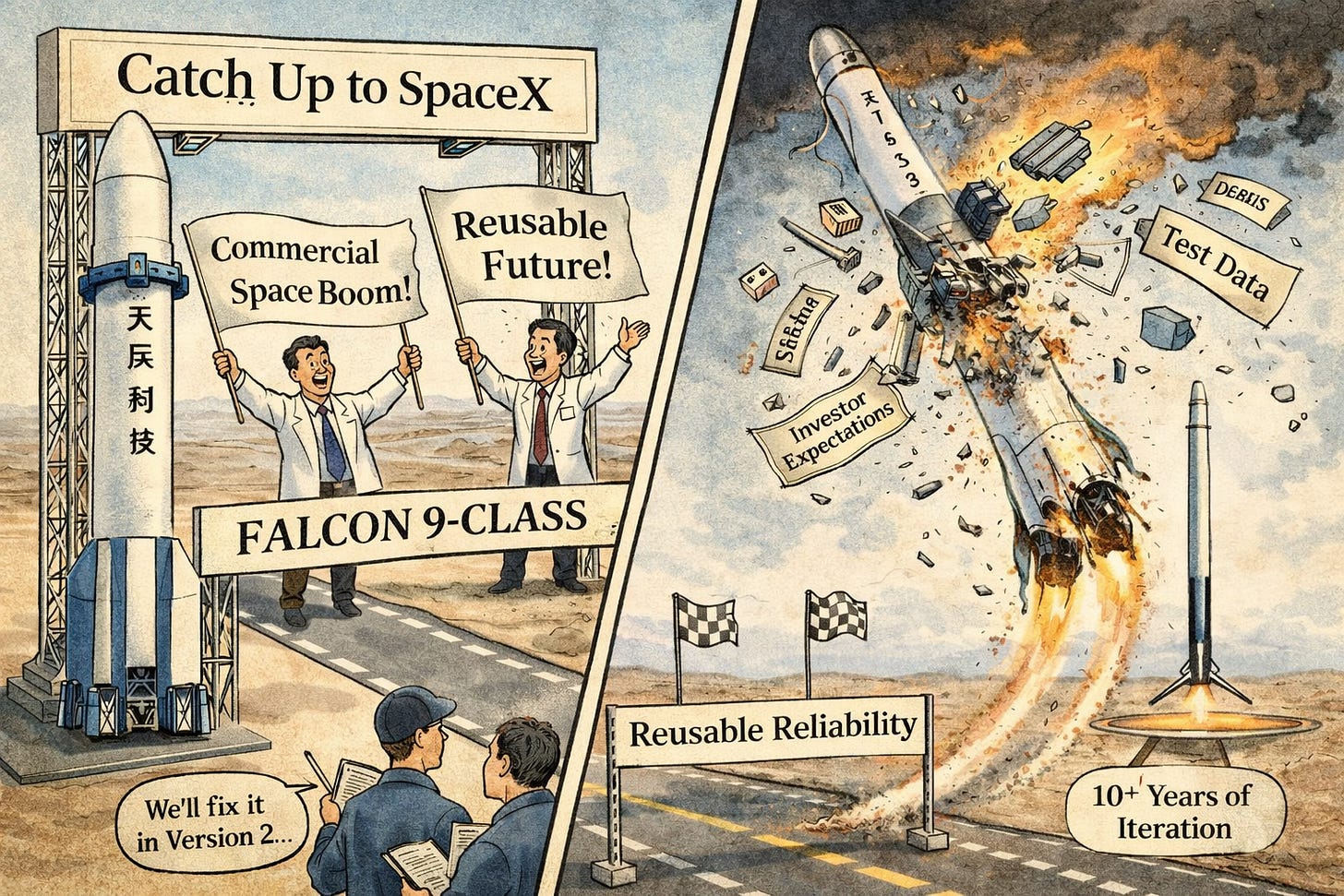
Space Pioneer’s Tianlong-3 Rocket Fails on Debut As Predicted: Setback for Commercial Reusable Launch Ambitions
Bottom Line Up Front (BLUF): China’s commercial heavy-lift rocket Tianlong-3 suffered a failure during its first launch, marking a setback for Space Pioneer and the country’s push toward reusable, Falcon 9–class launch capabilities. While unlikely to derail broader momentum, the incident highlights ongoing reliability gaps in China’s rapidly expanding private space sector.
Analyst Comments: This is a stumble, not a derailment. China’s commercial space ecosystem is moving fast—arguably too fast in some cases—and Tianlong-3 was positioned as a serious competitor to Falcon 9–style reusable launch systems. A failed maiden flight isn’t unusual in rocketry, but it does reinforce the gap between ambition and execution. The more telling detail is context: this follows a 2024 test incident where the rocket unintentionally lifted off during a static fire. That points to deeper engineering and quality control challenges, not just bad luck. When you’re trying to scale reusable launch systems, precision matters—and right now, China’s commercial players are still maturing.
READ THE STORY: Xinhua // Spacenews
Beijing’s “Teapot” Refineries Blunt Iran War Oil Shock, But Not for Long
Bottom Line Up Front (BLUF): China is mitigating the global oil disruption caused by the Iran conflict by leveraging small independent “teapot” refineries, sanctioned crude imports, and large stockpiles. While this strategy provides short-term insulation, structural limits—rising prices, constrained supply routes, and reliance on gray-market logistics—mean Beijing’s buffer is finite.
Analyst Comments: Following the Iran conflict and the disruption of the Strait of Hormuz—through which roughly 20% of global oil flows—China has leaned heavily on independent “teapot” refineries to sustain imports of discounted Iranian and Russian crude. These smaller refineries, primarily based in Shandong province, account for about a quarter of China’s refining capacity and specialize in processing sanctioned oil purchased at below-market rates. They operate alongside a broader strategy that includes stockpiling reserves (estimated at ~1.2 billion barrels) and using shadow fleets to bypass sanctions. However, analysts note that many current supplies were secured before the conflict escalated, and future imports are expected to decline as Middle Eastern supply routes remain disrupted and prices rise. Teapot refiners are already reducing purchases due to shrinking margins and higher costs.
READ THE STORY: Aljazeera
Cyber-Kinetic Convergence in Iran Conflict: Digital Operations Now Embedded in Warfare
Bottom Line Up Front (BLUF): The ongoing U.S.-Israel-Iran conflict marks a shift where cyber operations are fully integrated into kinetic warfare—supporting targeting, disruption, and psychological pressure. Civilian infrastructure and commercial systems are increasingly part of the battlespace, expanding risk well beyond traditional military targets.
Analyst Comments: Cyber operations in the U.S.-Israel-Iran conflict are being used directly to support military targeting, including leveraging connected camera systems for intelligence gathering and battle damage assessment. Iran-linked actors have conducted disruptive and psychological operations against civilian-adjacent targets, including healthcare organizations and individuals tied to defense sectors, using tactics such as data wiping, credential compromise, and doxxing. The conflict has also seen the physical disruption of digital infrastructure, including drone activity affecting cloud services in the Gulf, signaling that data centers and cloud environments are now part of the kinetic threat landscape.
READ THE STORY: Forbes
Handala Claims Breach of Israeli Defense Contractor: Supply Chain Compromise Exposes Sensitive Military Systems
Bottom Line Up Front (BLUF): Iran-linked threat group Handala claims to have breached Israeli defense contractor PSK Wind Technologies, exposing sensitive operational data, facility layouts, and technical schematics tied to IDF command and control systems. The incident highlights the growing effectiveness of supply chain attacks against hardened military targets.
Analyst Comments: Handala claims to have breached PSK Wind Technologies, a contractor involved in Israeli military command and control systems, gaining access to large volumes of sensitive internal data. Leaked materials reportedly include images of command centers, operational documents, and detailed schematics of communications infrastructure, raising concerns about both intelligence exposure and physical security risks. The group—linked to Iran’s Ministry of Intelligence—has previously conducted large-scale cyber operations, including destructive attacks and data leaks targeting Western and Israeli entities.
READ THE STORY: CyberPress
CBP Facility Codes Exposed via Public Quizlet Sets: Insider Data Leak Highlights OPSEC Gaps
Bottom Line Up Front (BLUF): Sensitive U.S. Customs and Border Protection (CBP) facility information—including gate access codes and operational details—was publicly exposed through Quizlet flashcards, likely created for training purposes. The incident underscores persistent insider risk and poor operational security (OPSEC), where convenience and informal learning tools create unmonitored data leakage paths.
Analyst Comments: This fits a broader pattern: insider-driven leaks via low-friction platforms (Quizlet, GitHub, Google Docs) continue to bypass traditional security controls because they don’t look like “attacks.” They’re just users trying to do their jobs more easily. That’s exactly why they’re dangerous. From an adversary perspective, this is gold. Even partial validation of facility layouts, terminology, or procedures can support physical intrusion, social engineering, or impersonation. Pair this with OSINT and you can start building a pretty detailed operational picture.
READ THE STORY: Wired
Qilin Ransomware Deploys Advanced EDR Killer: Capable of Disabling 300+ Security Tools
Bottom Line Up Front (BLUF): Qilin ransomware operators are deploying a highly sophisticated multi-stage loader that disables over 300 EDR solutions before executing payloads. By abusing legitimate signed drivers and advanced syscall evasion techniques, the malware blinds endpoint defenses, enabling near-unrestricted post-compromise activity.
Analyst Comments: What makes this dangerous isn’t just the kill capability—it’s how early it happens in the chain. The EDR killer is deployed before the main payload, meaning most traditional detection never even gets a chance to fire. If this executes successfully, you’re effectively blind. The use of legitimate signed drivers is the real problem. This isn’t exploiting a vulnerability—it’s abusing trusted components to get direct access to physical memory and kernel structures. That gives attackers the ability to unregister callbacks, kill processes, and bypass protections in ways that are extremely difficult to detect from user space.
READ THE STORY: Talos
Phorpiex Botnet Evolves Into Multi-Function Threat Platform: Powers Ransomware, Sextortion, and Crypto Theft
Bottom Line Up Front (BLUF): The long-running Phorpiex (Trik) botnet has evolved into a resilient, multi-purpose cybercrime platform delivering ransomware, sextortion campaigns, and cryptocurrency theft at scale. Its hybrid C2/P2P architecture and modular payload delivery make it highly durable and difficult to disrupt.
Analyst Comments: Phorpiex isn’t new—but it’s gotten smarter. What used to be a spam botnet is now a full-service delivery platform for cybercrime. The key shift is architecture. Moving to a hybrid C2 + peer-to-peer model means takedowns are far less effective. Even if you kill central servers, infected nodes keep the network alive. That’s a big deal operationally—it turns disruption into a whack-a-mole problem.
READ THE STORY: GBhackers
TP-Link Archer NX Routers Expose Critical Auth Bypass: Unauthenticated Firmware Takeover Risk
Bottom Line Up Front (BLUF): TP-Link has patched a critical authentication bypass (CVE-2025-15517) affecting Archer NX-series routers that allows unauthenticated attackers to perform privileged actions, including firmware uploads. Combined with additional flaws, successful exploitation could lead to full device compromise and persistent network access.
Analyst Comments: This is the kind of vulnerability that quietly turns into a botnet problem if left unpatched. Pre-auth access to router management functions—especially firmware upload—is about as bad as it gets in consumer networking. Even if exploitation isn’t widespread yet, the pattern is well established. TP-Link devices have been repeatedly targeted (Quad7 botnet, prior KEVs), and attackers actively scan for exposed management interfaces. Once weaponized, this becomes low-effort, high-scale compromise—perfect for botnets, traffic interception, or persistence inside home and small business networks.
READ THE STORY: BleepingComputer
Venom Stealer Turns ClickFix Lures Into Persistent Data Theft: Continuous Credential and Crypto Harvesting at Scale
Bottom Line Up Front (BLUF): A new malware-as-a-service platform, Venom Stealer, is combining ClickFix social engineering with persistent post-infection data harvesting, enabling continuous credential theft and cryptocurrency wallet compromise. Unlike traditional infostealers, it maintains long-term access and ongoing exfiltration, significantly increasing impact per infection.
Analyst Comments: The ClickFix delivery is the real enabler here. It shifts execution to the user—meaning fewer traditional detection opportunities. No exploit chain, no obvious dropper behavior—just a user pasting a command into Run or Terminal. That bypasses a lot of EDR logic built around process ancestry and exploit detection. But the standout feature is persistence with intent. Monitoring browser credential stores every 30 seconds means even post-incident recovery actions (like password resets) get neutralized. That’s a nasty feedback loop: the more a victim tries to recover, the more data gets harvested.
READ THE STORY: CSN
OpenSSH 10.3 Fixes ProxyJump Injection Risk: Subtle Misconfigurations Could Enable Unauthorized Access
Bottom Line Up Front (BLUF): OpenSSH 10.3 patches a shell injection vulnerability in ProxyJump handling and fixes risky certificate validation behavior that could allow unintended broad authentication. While not easily exploitable in default setups, environments that dynamically construct SSH commands or rely on certificate authorities face elevated risk.
Analyst Comments: The ProxyJump issue is straightforward: if user/host values are dynamically built and not sanitized, you’ve got a command injection vector. That’s especially relevant in bastion/jump-host architectures where SSH commands are programmatically generated. The more interesting issue is the certificate behavior. Treating empty principals as a wildcard is the kind of edge case that sits quietly until someone misconfigures a CA—and then suddenly you’ve got unintended universal access. Fixing that closes a subtle but potentially severe access control gap. Dropping support for non-rekeying SSH implementations is less flashy but important. It signals continued tightening of protocol hygiene, and it may break legacy integrations—something ops teams should plan for.
READ THE STORY: Cryptika
React2Shell Actively Exploited: Pre-Auth RCE Compromises 700+ Next.js Servers in Mass Credential Harvesting Campaign
Bottom Line Up Front (BLUF): A critical React Server Components vulnerability (CVE-2025-55182, “React2Shell”) is being actively exploited in the wild, enabling unauthenticated remote code execution against Next.js applications. Over 700 servers were compromised in 24 hours, with attackers harvesting cloud credentials, API keys, and SSH access—indicating immediate, large-scale risk to exposed environments.
Analyst Comments: The key risk isn’t just initial access—it’s what comes next. Modern Next.js deployments are tightly coupled to cloud infrastructure, meaning a single exploit can expose AWS credentials, Kubernetes tokens, CI/CD secrets, and payment APIs. That turns a web bug into full environment compromise in minutes. The “no public PoC” narrative is misleading and dangerous. Active exploitation is already confirmed. Nation-state-linked activity suggests this was operationalized early, and given how easy this bug is to weaponize, broader threat actor adoption is essentially guaranteed. Bottom line: if your app was exposed and unpatched, you should be operating under assume breach conditions.
READ THE STORY: CyberPress
Items of interest
Intelligence That Doesn’t Influence Policy Is Effectively Ignored
Bottom Line Up Front (BLUF): Intelligence analysis only has value if it is timely, relevant, and aligned with the policy process. Policymakers operate under time constraints, competing priorities, and information overload—meaning most analysis is skimmed or ignored unless it directly informs decisions in progress.
Analyst Comments: The gap between intelligence and policy isn’t about capability—it’s about alignment. Analysts tend to optimize for completeness: fully sourced, polished, and strategically sound products. Policymakers, on the other hand, operate in compressed timelines, juggling multiple crises and inputs simultaneously. That mismatch means even strong analysis often arrives too late or lacks immediate applicability. The reality is that most policy is shaped before it reaches senior leaders. The real influence happens at the working level—where officials are drafting options, debating tradeoffs, and preparing recommendations. If analysis isn’t present at that stage, it’s largely irrelevant.
READ THE STORY: War On The Rocks
How Secret Intelligence Shapes Wars and Diplomacy (Video)
FROM THE MEDIA: Behind every major conflict and international agreement lies a layer of classified analysis, early warning assessments, and strategic intelligence. While armies move publicly and treaties are signed visibly, intelligence services operate quietly — shaping the decisions that determine war, deterrence, sanctions, and diplomacy.
Why Intelligent People Scare Society | Schopenhauer (Video)
FROM THE MEDIA: Why do intelligent people often feel isolated? Schopenhauer's philosophy reveals the harsh truth about society’s fear of deep thinkers. Watch to uncover the reality of intelligence and loneliness.
The selected stories cover a broad range of cyber threats and are intended to help readers frame key publicly discussed threats and improve overall situational awareness. InfoDom Securities does not endorse any third-party claims made in its original material or related links on its sites; the opinions expressed by third parties are theirs alone. For further questions, don't hesitate to get in touch with InfoDom Securities at dominanceinformation@gmail.com.