Daily Drop (1270)
04-01-26
Wednesday, Apr 01, 2026 // (IG): BB // Ghostwire
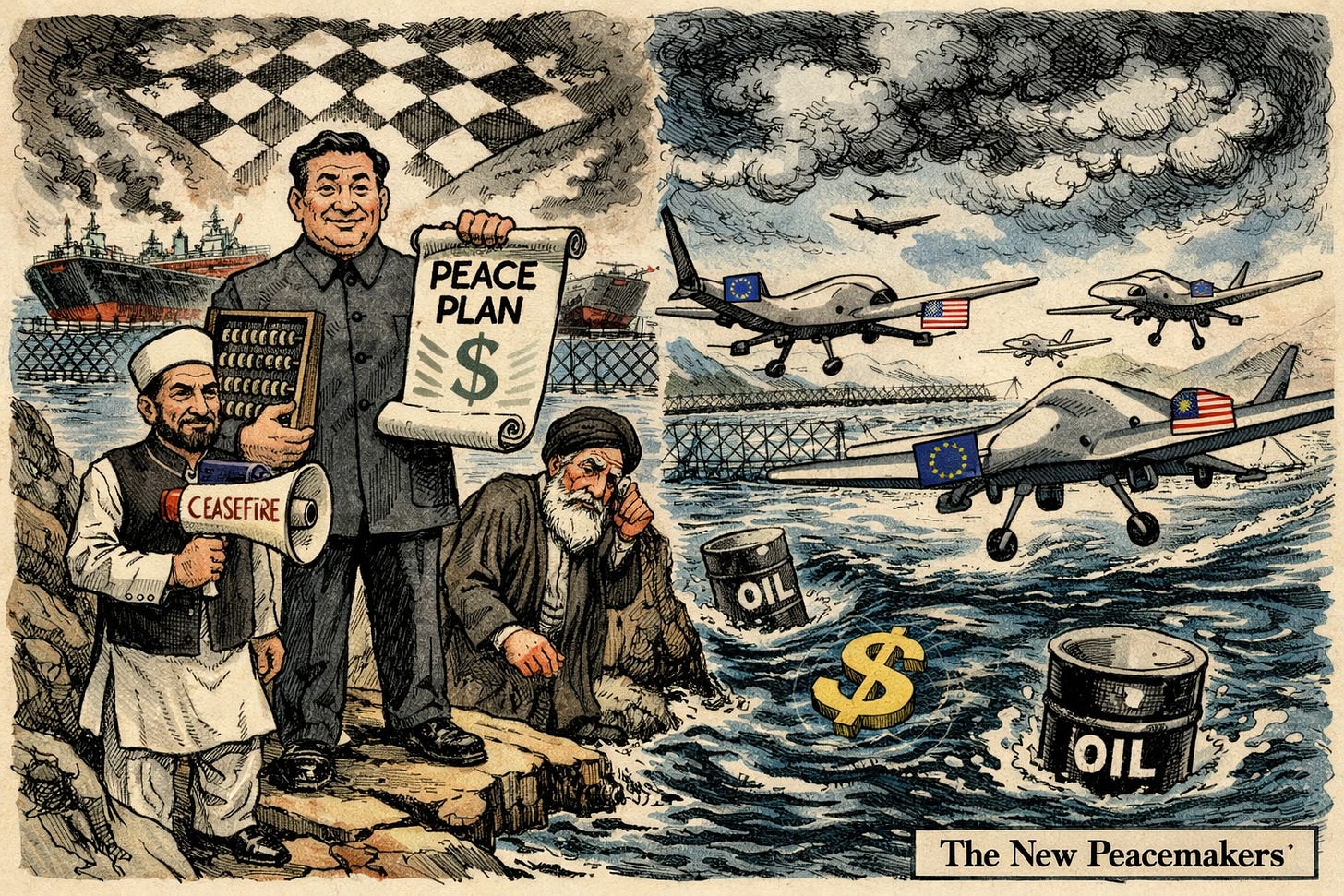
Beijing Leverages Iran War Ceasefire Push to Secure Hormuz and Protect Economic Interests
Bottom Line Up Front (BLUF): As the Iran war enters its second month, China and Pakistan are advancing a ceasefire plan centered on reopening the Strait of Hormuz, where ongoing disruption is driving global energy instability. While framed as mediation, China’s push is primarily driven by economic self-interest and an opportunity to expand geopolitical influence.
Analyst Comments: China and Pakistan jointly proposed a five-point peace initiative calling for an immediate ceasefire and the reopening of the Strait of Hormuz. The plan includes halting attacks on critical infrastructure, initiating peace talks, and restoring safe commercial shipping through the strait. Pakistan’s foreign minister stated the proposal was coordinated with China following meetings in Beijing, positioning both countries as mediators. China’s involvement is driven in part by its role as Iran’s top trade partner and largest oil customer, giving it leverage and incentive to stabilize the situation. The U.S. response has been muted, with President Trump indicating diplomacy with Iran is progressing but not directly endorsing or rejecting the initiative.
READ THE STORY: BBC
CNCERT, MSS, MIIT and CNIPA Flags Codex Token Hijack Risk, Mass Privacy Violations Across Mobile Apps
Bottom Line Up Front (BLUF): Chinese security authorities and researchers report widespread privacy violations across 71 mobile apps and highlight a critical vulnerability in OpenAI Codex that could allow attackers to hijack GitHub access tokens. The findings reflect growing risk at the intersection of AI tooling, developer workflows, and large-scale data exposure.
Analyst Comments: China’s National Computer Virus Emergency Response Center identified 71 mobile apps illegally collecting and using personal data, including well-known consumer brands. Researchers disclosed a critical vulnerability in OpenAI Codex that could allow attackers to steal GitHub authentication tokens, potentially exposing private repositories. Authorities also warned about fake OpenClaw download sites distributing trojans, and risks tied to insecure AI tooling in sensitive workflows. Separately, reports highlight targeted attacks on developers using fake VS Code alerts to deliver malware, reinforcing the focus on software supply chains. Additional findings include risks from smart wearable devices leaking sensitive location data, including military-related exposure scenarios.
READ THE STORY: 4Hou
Japan Deploys Long-Range Missiles Capable of Striking China, Marking Major Policy Shift
Bottom Line Up Front (BLUF): Japanese forces have deployed Type-12 long-range cruise missiles at a military base in Kumamoto, with a range of up to 1,000km, giving it the ability to strike targets in mainland China. This move marks a significant departure from Japan’s post-war defensive posture and reflects rising tensions with Beijing and growing uncertainty around U.S. security guarantees.
Analyst Comments: This is a significant shift from Japan’s traditional interpretation of its pacifist constitution (Article 9), which historically limited military capabilities to self-defense. Tensions with China have escalated, with Beijing criticizing the deployment as a sign of “remilitarization” and warning against further military expansion. Japan’s leadership frames the deployment as necessary for deterrence and response capability, particularly against potential maritime or territorial threats.
READ THE STORY: FT
Netanyahu Signals Shift to Open-Ended Conflict Strategy in Evolving Israeli Security Doctrine
Bottom Line Up Front (BLUF): Israeli Prime Minister Benjamin Netanyahu is advancing a more aggressive, open-ended security doctrine centered on preemptive strikes, territorial buffer zones, and sustained military pressure. The approach reflects a post-October 7 shift away from containment toward continuous conflict, raising concerns about long-term sustainability, regional stability, and strategic end states.
Analyst Comments: Netanyahu is preparing Israel for a future of continuous conflict, emphasizing preemptive action against emerging threats and rejecting previous containment strategies. The evolving approach includes seizing and maintaining buffer zones in neighboring territories and relying on sustained military force as the primary security mechanism. Israel is currently engaged across multiple fronts—including Gaza, Lebanon, Iran, Syria, and Yemen—with no clear end state, marking the longest sustained conflict period in the country’s history.
READ THE STORY: FT
Ukraine Targets Strait of Hormuz Security Role with Gulf Weapons Deals
Bottom Line Up Front (BLUF): Ukraine is entering long-term (10-year) defense agreements with Gulf countries, exporting weapons, drones, and military expertise in exchange for energy support and strategic cooperation. The deals include capabilities aimed at securing maritime routes like the Strait of Hormuz, signaling Ukraine’s emergence as a defense exporter and security partner beyond Europe.
Analyst Comments: This is a strategic pivot—not just arms sales. Ukraine is turning battlefield innovation into exportable capability, particularly in low-cost, high-impact systems like drones and electronic warfare. The Hormuz angle is the most significant piece. Ukraine isn’t just selling hardware—it’s selling operational experiencefrom keeping the Black Sea corridor open under constant threat. That’s directly transferable to Gulf concerns about Iranian disruption.
READ THE STORY: The Kyiv Independent
Russian Oil Shipment Reaches Cuba Despite US Pressure, Highlighting Strategic Flexibility
Bottom Line Up Front (BLUF): A sanctioned Russian tanker delivered ~700,000 barrels of crude to Cuba despite ongoing US pressure, offering temporary relief to the island’s energy crisis. The move underscores geopolitical pragmatism, with Washington allowing limited exceptions while maintaining broader pressure on Havana.
Analyst Comments: This is less about oil and more about signaling. The US is trying to walk a line between maximum pressure and humanitarian optics, while Russia uses the opening to reinforce influence in the Western Hemisphere. The shipment itself isn’t game-changing—Cuba burns ~100,000 barrels per day, so this is roughly a week’s supply. But politically, it matters. It shows enforcement of sanctions is flexible when conditions demand it, which creates room for adversaries to test boundaries.
READ THE STORY: FT
Iranian Actors Target Microsoft 365 Accounts with Password Spraying Campaign
Bottom Line Up Front (BLUF): Iran-linked threat actors are conducting password spraying attacks against Microsoft 365 accounts, targeting organizations aligned with geopolitical interests. The activity leverages low-and-slow authentication attempts to evade detection, with targeting patterns correlating to regions impacted by Iranian military operations.
Analyst Comments: Researchers observed Iranian threat actors conducting password spraying attacks against Microsoft 365 accounts, attempting to gain access using commonly used passwords across multiple accounts. The activity is described as low-volume and distributed, designed to avoid triggering account lockouts and evade detection systems. Targeting appears to correlate with geopolitical events, including regions affected by Iranian military activity, suggesting strategic intent behind victim selection.
READ THE STORY: The Register
UNC757, Agrius, and Pay2Key Actors Leverage Ransomware Ecosystem to Target US Critical Infrastructure
Bottom Line Up Front (BLUF): Iran-linked threat actors are increasingly embedding within the ransomware ecosystem—acting as initial access brokers and partnering with criminal affiliates—to target U.S. critical infrastructure. This hybrid model blends espionage, disruption, and profit, while creating significant legal risk for victims who may unknowingly pay sanctioned entities.
Analyst Comments: KELA reports that Iranian state-linked actors are increasingly collaborating with ransomware groups, acting as initial access brokers and handing off compromised networks to affiliates like ALPHV/BlackCat and RansomHouse. Groups such as Pioneer Kitten (UNC757/Fox Kitten) exploit internet-facing systems (VPNs, firewalls) to gain access, then monetize through partnerships rather than direct ransomware deployment. The Pay2Key operation has evolved into a full RaaS platform (Pay2Key.I2P), recruiting affiliates—including from Russian cybercrime forums—and offering higher revenue shares for targeting U.S. and Israeli entities.
READ THE STORY: Industrial
Starlink Satellite Breakup Adds to Orbital Debris Concerns Amid Rapid Constellation Growth
Bottom Line Up Front (BLUF): A Starlink satellite experienced an on-orbit failure, generating debris at ~560 km altitude. While the fragments are expected to deorbit within weeks and pose no immediate threat to ISS or Artemis missions, repeated incidents raise concerns about constellation reliability and the growing congestion of low Earth orbit.
Analyst Comments: One satellite failure isn’t a crisis. A pattern is. This is now at least the second similar event in a few months, which starts to shift the conversation from “isolated anomaly” to potential systemic risk—whether that’s propulsion, power systems, or manufacturing scale issues. The bigger issue is density. With over 10,000 satellites already in orbit and more planned, even short-lived debris events increase collision probabilities. Low altitude helps—drag cleans things up—but it doesn’t eliminate near-term risk to other operators sharing the same orbital bands. Also worth noting: transparency remains limited. “Anomaly” doesn’t tell operators much. In an increasingly crowded orbital environment, rapid and detailed disclosure isn’t just good practice—it’s becoming necessary for collective safety.
READ THE STORY: The Register
Nvidia Invests $2B in Marvell to Expand Control Over AI Data Center Infrastructure
Bottom Line Up Front (BLUF): The company is investing $2 billion in Marvell to accelerate development of high-speed AI data center networking, particularly silicon photonics. The move signals Nvidia’s strategy to extend dominance beyond GPUs into full-stack AI infrastructure—tightening its grip on how large-scale AI systems are built and scaled.
Analyst Comments: As models grow, performance depends less on individual chips and more on how efficiently thousands of them communicate. That’s where silicon photonics comes in—faster data transfer, lower latency, and better scaling across massive clusters.The interesting angle is interoperability. By working with Marvell—who helps hyperscalers design custom chips—Nvidia is hedging against the “everyone builds their own silicon” trend. Instead of fighting that shift, they’re positioning themselves as the platform everything plugs into.
READ THE STORY: FT
AI Has Already Shifted the Cybersecurity Battlefield from Code to Trust
Bottom Line Up Front (BLUF): AI-driven vulnerability discovery is accelerating both offense and defense, but the real shift is economic: attackers are moving away from software exploitation toward identity, communication, and trust-based attacks. The new primary attack surface is no longer code—it’s people, workflows, and increasingly AI agents embedded in business processes.
Analyst Comments: Attackers follow ROI. Right now, that ROI is in identity and trust. Why burn a zero-day when a well-crafted message—backed by real context and AI-generated precision—can get you credentials, approvals, or access with far less effort? The uncomfortable truth: most organizations are still defending like it’s 2015—patching vulnerabilities and chasing IOCs—while attackers are modeling how the business actually operates. The most important idea here is the defender advantage that isn’t being used. Organizations already know what “normal” looks like internally—communication patterns, approval flows, behavioral baselines. But most security tooling ignores that in favor of generic detection rules.
READ THE STORY: Security Boulevard
Analysis Exposes $100M Crypto-Funded Russian Drone Supply Chain
Bottom Line Up Front (BLUF): Blockchain intelligence has uncovered a $100 million cryptocurrency-backed procurement network used by Russia-linked actors to acquire drones from Chinese suppliers. The transparent nature of blockchain transactions is enabling investigators to map supply chains, identify counterparties, and track state-aligned activity in near real time.
Analyst Comments: Investigators identified consistent transaction patterns, including repeated payments matching drone unit prices and concentrated flows from specific counterparties—indicating structured procurement rather than irregular activity. One case showed a single counterparty responsible for $40 million in transfers, with additional funds flowing through sanctioned-linked infrastructure such as Garantex. Analysis also revealed overlaps with Iranian-linked financial activity, including wallets tied to IRGC-associated entities and sanctioned individuals, suggesting shared or adjacent procurement channels.
READ THE STORY: CyberNews
Google Vertex AI “Double Agent” Flaw Enables Privilege Escalation and Data Exfiltration
Bottom Line Up Front (BLUF): A critical flaw in Google Cloud Vertex AI allows attackers to escalate privileges and access sensitive data by abusing overpermissive default service accounts (P4SA). By deploying a malicious AI agent, attackers can extract credentials, break isolation, and gain broad access to cloud storage, internal artifacts, and potentially Workspace data.
Analyst Comments: The “Double Agent” angle is clever but not revolutionary. Using a malicious pickle file for code execution is well-known territory. The real issue is what happens next: the agent inherits excessive permissions, queries metadata, and pivots into a high-privilege identity. That’s straight out of the cloud attacker playbook. What is new is the attack surface. AI agents are now first-class workloads, but many orgs aren’t treating them like production code. If you deploy agents with default permissions, you’re effectively giving untrusted code a privileged identity inside your environment. Bottom line: this isn’t just an AI problem—it’s an identity and access management failure in a new wrapper.
READ THE STORY: CyberPress // GBhackers // THN
Anthropic Accidentally Leaks Claude Code Source via Packaging Error, Exposing Internal Roadmap
Bottom Line Up Front (BLUF): Anthropic inadvertently exposed ~500,000 lines of Claude Code source code after bundling an internal debugging file into a public release. While no customer data was compromised, the leak gives competitors deep visibility into Anthropic’s architecture, unreleased features, and product roadmap—marking the company’s second security lapse in a week.
Analyst Comments: The exposed codebase revealed unreleased features, including persistent background agents, cross-session learning, and remote control capabilities. These features indicate a roadmap toward more autonomous, stateful AI systems. Anthropic stated the incident was caused by human error during release packaging and confirmed no sensitive customer data or credentials were exposed. The company has since issued takedown requests and is implementing safeguards to prevent recurrence. External researchers and developers rapidly analyzed and reverse-engineered the code, effectively turning the leak into a public blueprint for building production-grade AI coding assistants.
READ THE STORY: AXIOS // CNET // Inc
LockBit and MedusaLocker Like Families Abuse Legitimate Windows Tools to Disable Security Controls Pre-Attack
Bottom Line Up Front (BLUF): Threat actors are increasingly leveraging legitimate Windows administration tools to disable antivirus and EDR before deploying ransomware. AuKill exemplifies this trend by using a Bring Your Own Vulnerable Driver (BYOVD) approach, loading a legitimate but vulnerable Process Explorer driver to terminate protected EDR processes from the kernel.
Analyst Comments: Why drop custom tooling when Windows already gives you everything you need? These utilities come pre-trusted, often signed, and widely used by IT. That means fewer alerts, less scrutiny, and more time for attackers to operate. The real shift is sequencing. Killing AV/EDR is no longer opportunistic—it’s a dedicated phase in the ransomware kill chain. Once defenses are down, everything else (credential theft, lateral movement, encryption) becomes routine.
READ THE STORY: GBhackers
Qilin Ransomware Claims Breach of Dow Inc., No Evidence Yet Released
Bottom Line Up Front (BLUF): The Qilin ransomware group has listed Dow Inc. on its leak site, claiming a breach, but has not provided proof. While unverified, the claim aligns with Qilin’s aggressive RaaS activity and growing collaboration with other major ransomware groups, signaling continued pressure on large industrial targets.
Analyst Comments: Right now, this sits in the “claim, not confirmed” bucket—and that distinction matters. Ransomware groups routinely post victims early to apply pressure, even before data is validated or negotiations progress. That said, Qilin is not noise. They’ve been scaling fast, averaging dozens of victims monthly and forming alliances with groups like LockBit and DragonForce. That kind of collaboration—shared tooling, infrastructure, and access—means claims like this deserve attention even without proof.
READ THE STORY: Security Affairs
LeakNet Shifts Initial Access Tactics, But Predictable Playbook Gives Defenders an Edge
Bottom Line Up Front (BLUF): LeakNet ransomware operators are evolving initial access techniques—moving from brokered credentials to ClickFix social engineering and in-memory Deno-based loaders—but continue to rely on a consistent post-exploitation workflow. That operational predictability creates reliable detection opportunities for defenders despite changes at the intrusion stage.
Analyst Comments: The Deno-based loader is a smarter move. “Bring Your Own Runtime” (BYOR) blends malicious execution into legitimate tooling, and in-memory payload delivery cuts straight through traditional file-based defenses. This is where a lot of legacy EDR approaches start to struggle. But here’s the catch—and it’s a big one: they didn’t change what happens after access. Execution, lateral movement, staging—it’s the same sequence every time. That kind of consistency is a defensive gift. If you’re instrumented for behavior instead of payloads, you can break this chain early and reliably.
READ THE STORY: Security Boulevard
Google Drive Enables AI Ransomware Detection by Default for Paid Users
Bottom Line Up Front (BLUF): Google has enabled AI-driven ransomware detection by default for all paid Google Drive users, automatically pausing file synchronization when encryption activity is detected. The feature limits cloud-side damage and enables rapid recovery, but does not stop endpoint-level encryption—keeping endpoint security firmly in scope.
Analyst Comments: The real value is containment and recovery speed. Stopping sync mid-attack cuts off one of ransomware’s biggest advantages: turning a single infected host into an organization-wide data problem. The “14x better detection” claim is notable, but the bigger takeaway is normalization—cloud providers are now embedding security controls directly into core services, not treating them as add-ons. Expect this to become standard across SaaS.
READ THE STORY: Bleeping Computer
North Korean Actors Backdoor Axios NPM Package, Deliver Cross-Platform RAT via Supply Chain Attack
Bottom Line Up Front (BLUF): DPRK-linked UNC1069 compromised the widely used Axios npm package, pushing trojanized versions that execute a hidden postinstall script to deploy the WAVESHAPER.V2 RAT across Windows, macOS, and Linux. The attack targets developers and CI/CD pipelines, creating a high-risk path to credential theft and downstream enterprise compromise.
Analyst Comments: Attackers hijacked an Axios maintainer account and published malicious versions (1.14.1 and 0.30.4), inserting a rogue dependency (plain-crypto-js) that executes via npm’s postinstall hook. The dependency deploys an obfuscated dropper (SILKBELL) that fingerprints the OS and pulls a second-stage payload. Execution paths vary by platform (PowerShell on Windows, Mach-O on macOS, Python on Linux), all leading to the WAVESHAPER.V2 RAT. Google Threat Intelligence Group attributes the campaign to UNC1069, a DPRK-linked cluster active since 2018 and known for financially motivated supply chain attacks, particularly targeting cryptocurrency ecosystems.
READ THE STORY: The Register // GBhackers // THN
Hackers Rapidly Weaponize WebLogic RCE (CVE-2026-21962) as Mass Exploitation Campaigns Emerge
Bottom Line Up Front (BLUF): A newly disclosed, maximum-severity Oracle WebLogic RCE (CVE-2026-21962, CVSS 10.0) is already under active exploitation, with attackers weaponizing public PoC code the same day it dropped. Campaigns show automated scanning at scale, targeting both the new flaw and a backlog of older WebLogic bugs—reinforcing that unpatched systems remain low-effort, high-reward targets.
Analyst Comments: The technique itself—path traversal via HTTP GET to reach proxy endpoints—isn’t groundbreaking. What matters is reliability and reach. WebLogic continues to sit in critical enterprise environments, often exposed more than it should be. That combination makes it a staple in opportunistic campaigns and botnet-driven exploitation. Also worth noting: attackers aren’t picky. The “spray and pray” behavior, probing for unrelated vulnerabilities (Hikvision, PHPUnit), shows these aren’t tailored intrusions—they’re scalable access operations. Initial foothold first, figure out value later. If you’re still carrying unpatched WebLogic—especially internet-facing—you should assume compromise is a matter of timing, not probability.
READ THE STORY: GBhackers
Items of interest
Malware (GhostSocks) Turns Infected Devices into Residential Proxy Network for Stealth Operations
Bottom Line Up Front (BLUF): GhostSocks is an emerging malware offering that converts compromised systems into SOCKS5 residential proxy nodes, allowing attackers to route malicious traffic through legitimate IP addresses. This significantly degrades traditional detection methods and is already being used alongside Lumma Stealer and by ransomware operators to maintain persistence and evade attribution.
Analyst Comments: This is less about a “new malware family” and more about a shift in attacker infrastructure. GhostSocks operationalizes something threat actors have wanted for years at scale—cheap, rotating residential IP space that blends in by default. That’s a problem because most defenses still treat IP reputation as a meaningful signal. The integration with Lumma Stealer is the real story. Credential theft gets initial access; GhostSocks turns that access into long-term infrastructure. That’s efficient tradecraft. Add TLS-wrapped SOCKS5 traffic and relay-based C2, and you’re looking at activity that won’t trip many traditional controls.
READ THE STORY: GBhackers
He Hunts Malware for a living. Here’s what he’s most afraid of (Video)
FROM THE MEDIA:
Bogdan Botezatu, the Director of Threat Research at Bitdefender. He revealed something terrifying: The biggest threat in cybersecurity isn’t the malware we see; it’s everything hiding beneath the surface. He breaks down how modern threats actually emerge, from stealthy APT malware that stays invisible for years, to the rise of info-stealers that harvest passwords and cookies at scale. He also explains why your smart home might be the weakest point in your entire network.
Infostealer Malware Logs Analyzed by... AI ! (Video)
FROM THE MEDIA: Manage threat intelligence and your exposed attack surface with Flare!
The selected stories cover a broad range of cyber threats and are intended to help readers frame key publicly discussed threats and improve overall situational awareness. InfoDom Securities does not endorse any third-party claims made in its original material or related links on its sites; the opinions expressed by third parties are theirs alone. For further questions, don't hesitate to get in touch with InfoDom Securities at dominanceinformation@gmail.com.