Saturday, May 07, 2022 // (IG): BB //Weekly Sponsor: Unsafe Waters
Nation-State-Sponsored Attacks: Not Your Grandfather’s Cyber Attacks
FROM THE MEDIA: It used to be that data breaches were all about cyber-crooks hacking computer systems to steal personal information, followed by an affected company sending regretful notification letters offering a year or two of complimentary credit monitoring. Not anymore. Now, state-sponsored attacks threaten to wreak havoc on companies’ essential IT systems, Internet devices, software, and all manner of critical infrastructure in private sector hands. Just a few weeks ago, the Director of the Federal Bureau of Investigation (FBI) and the U.S. Attorney General described a recent takedown of a Russian government-sponsored botnet called Cyclops Blink before it was weaponized and caused damage. That case is one reflection of a wave of state-sponsored attacks that can transform routine “incident response” into more dramatic corporate cyber crises.
READ THE STORY: NY Law Journal
US Sanctions Cryptocurrency 'Mixing' Service for Aiding North Korean Hackers
FROM THE MEDIA: For the first time, the US is sanctioning a cryptocurrency “mixing” service for helping North Korea launder some of the funds stolen in the $620 million hack of Ronin Network.
The sanctions target Blender.io, a website that charges to “anonymize bitcoin transactions” by mixing it with funds from other users. The US Treasury Department claims the North Korean hackers behind the Ronin Network heist recently tried to launder $20.5 million of the stolen funds through Blender.io.
In addition, the US Treasury Department is signaling it’ll go after other cryptocurrency mixing services that are found helping hackers. The sanctions against Blender.io essentially outlaw US persons and groups from conducting any business with the cryptocurrency service. Hence, using Blender.io is against US law unless the Treasury Department grants a license to do so.
READ THE STORY: PCMAG
New worm called Raspberry Robin that spreads through USB drives detected
FROM THE MEDIA: Cybersecurity firm Red Canary has warned users of a new WORM (Write once read many) or malware which can reach out to external domains to download malicious files on the computer and is spread via USB drives. Red Canary says it first observed a cluster of activity involving the worm which they are calling 'Raspberry Robin' last September. The report suggests that Raspberry Robin is generally introduced by infected removable drives such as USB devices containing malicious files.
Once connected to a computer, the worm then can read and execute a malicious file stored on the infected device. It then attempts to connect to a short URL which they found was often QNAP (Taiwanese corporation that specialises in network-attached storage appliances used for file sharing, virtualization, storage management and surveillance applications)-associated.
READ THE STORY: News 9 Live
This New Fileless Malware Hides Shellcode in Windows Event Logs
FROM THE MEDIA: A new malicious campaign has been spotted taking advantage of Windows event logs to stash chunks of shellcode for the first time in the wild. "It allows the 'fileless' last stage trojan to be hidden from plain sight in the file system," Kaspersky researcher Denis Legezo said in a technical write-up published this week.
The stealthy infection process, not attributed to a known actor, is believed to have commenced in September 2021 when the intended targets were lured into downloading compressed .RAR files containing Cobalt Strike and Silent Break.
The adversary simulation software modules are then used as a launchpad to inject code into Windows system processes or trusted applications. Also notable is the use of anti-detection wrappers as part of the toolset, suggesting an attempt on the part of the operators to fly under the radar.
READ THE STORY: THN
The Colonial Pipeline ransomware attack a year on: 5 lessons for security teams
FROM THE MEDIA: Today marks the one-year anniversary of the Colonial Pipeline ransomware attack, one of the biggest cyber attacks in recent history, where a threat actor named DarkSide used a single compromised password to gain access to the US’s largest pipeline operator’s internal systems.
During the attack, while the hackers began encrypting the organization’s data, Colonial Pipeline responded by taking its systems offline to stop the spread of the threat, but temporarily ceased pipeline operations and ended up paying a ransom of $4.4 million. While the Colonial Pipeline attack may have passed, ransomware remains an existential threat to modern enterprises, and with ransomware attacks on the rise, enterprises need to be prepared.
READ THE STORY: VentureBeat
NIST gives agencies new guidance to prepare for next SolarWinds-like hack
FROM THE MEDIA: The National Institute of Standards and Technology on Thursday published updated guidance meant to help agencies and organizations protect against cyberthreats in the supply chain, a major focus of the Biden administration’s cybersecurity executive order last year.
The revised publication on cybersecurity supply chain risk management gives acquirers and users of software and other technologies key practices, processes and controls to consider as they look to protect against such threats that can emerge from that tangled web of global suppliers and manufacturers from which companies develop technology products.
READ THE STORY: Fedscoop
Anonymous Hacks CCP-run Website; Warns China To Not Do 'anything Stupid Against Taiwan'
FROM THE MEDIA: Cyber hacking group ‘Anonymous’ has recently hacked a Chinese Communist Party (CCP) website, further warning Beijing not to attempt "anything stupid against Taiwan." In the midst of Russia's attack on Ukraine, Anonymous stated that it is taking a break from the cyberwar on Russia, Taiwan News reported. Further, the group has claimed to hack the website of the ‘Chengdu Pidu District Committee of the Chinese People's Political Consultative Conference’ on Monday, May 2.
Anonymous, on a newly produced HTML page on the website, added their logo, along with a photograph of a person wearing a black hoodie and a 'Guy Fawkes' mask. In addition to this, the meme "Taiwan Numbah Wan!" emerges on the page, which is a reference to a famous phrase made by video game streamer "AngryPug" in 2015 during a battle in the computer game "H1Z1" to annoy Chinese streamer "Em0", Taiwan News reported. Further, Taiwan's flag is shown underneath the statement, accompanied by its national emblem.
READ THE STORY: RepublicWorld
China’s benefit from the Russian-Ukrainian war
FROM THE MEDIA: If say Russia continues to control Ukrainian cities and causes a long-term conflict on the side of Eastern Europe, perhaps (China will gain more geopolitical benefits), including doubling the focus of the United States of America with Russia and giving Beijing more breathing space, and here the harsh sanctions will make imposed by the West, Russia is more economically dependent on China.
Just as Taiwan’s location in the heart of the “first island chain” in the western Pacific, and considering it as a barrier for Japan, which is Washington’s main ally in the region, is a Chinese threat, so American credibility is at risk in Asia about Taiwan more than it is in Europe regarding Ukraine.
We will find, in general, that China’s ultimate goal is to (recover Taiwan), and when the appropriate opportunity comes for China, in my personal opinion, China will then (will seek to possess the necessary military capabilities and economic flexibility necessary to deal with the course of events internationally), but most importantly, that China will probably need to (adopt more flexible tactics so that it can give itself enough room to maneuver and demand an extension of the time needed to negotiate), even if its primary goals are out of reach.
READ THE STORY: ModernDiplomacy
False-flag cyberattacks a red line for nation-states, says Mandiant boss
FROM THE MEDIA: False-flag cyberattacks represent a red line that even nation states like Russia and China don't want to cross, according to Mandiant CEO Kevin Mandia.
"It's one of the last rules of the playground that a modern nation may not want to break because they don't want everyone doing false flags," he said, speaking on a panel this week at Vanderbilt University's Summit on Modern Conflict and Emerging Threats.
In these types of destructive cyber operations, a country launches an attack with the intent of disguising its involvement and pinning the blame on another country. People worry about false flags," NSA director of cybersecurity Rob Joyce said, adding that "I don't know of a big one" that has been successful.
READ THE STORY: The Register
China plans to toss foreign-made PCs from government agencies 'in two years'
FROM THE MEDIA: Authorities in China have reportedly directed government agencies and state-run companies to bin all personal computers made by foreign companies and replace them with homegrown hardware within two years.
According to Bloomberg, "people familiar with the plan" recounted how government staff were told upon returning from China's Labor Day holiday, which ran from April 30th through May 4th, they will have to toss foreign PCs.
Bloomberg's report claims that the yet-to-be-officially-published mandate could lead to the replacement of as many as 50 million PCs by the central government.
The leading PC maker in the APAC region last year, according to research firm IDC, was China-based Lenovo, with about 30 percent of the market. HP came in second, with 14.3 percent market share, followed closely by Dell with 14.1 percent market share.
READ THE STORY: The Register
Is America Ready for Chinese-Russian Liminal Warfare?
FROM THE MEDIA: Over the past five years, most Americans have become familiar with what leading journalists and academics have termed, the new era of “Great Power Competition”: a reference to the increasingly complex and worrisome armed stand-off between the United States (and its allies), and China and Russia—the two leading authoritarian powers. The alarming genocidal war launched in February 2022 by Russia against Ukraine has awakened us to the reality that our expectations at the end of the Cold War in 1991 were delusional and foolish. It is not apparent that the universal appeal of the democratic idea will not spontaneously enable a benign New World Order to take shape.
READ THE STORY: National Interest
How Elon Musk could impact Twitter's battles over speech abroad
FROM THE MEDIA: Since Elon Musk announced he was buying Twitter last month, the billionaire has sent out tweet after tweet outlining his plans for the platform, touching on everything from new features to security updates to monetization. But Musk's overarching reason for committing billions of dollars to buy Twitter is to ensure the platform bolsters free speech.
"By 'free speech,' I simply mean that which matches the law," he said in one of his many recent tweets on the subject. "I am against censorship that goes far beyond the law. If people want less free speech, they will ask government to pass laws to that effect." Musk has also said he thinks Twitter should be more "reluctant to delete things" and "very cautious with permanent bans."
Musk's rhetoric has already raised some concerns in Twitter's home market about how it would impact the platform's approach to handling harassment, misinformation and content moderation broadly. But Musk's posture could also create new uncertainties for Twitter's platform if applied to markets abroad, which account for the vast majority of Twitter's user base. That's because definitions of free speech, and the laws governing it, often look very different around the world than they do in the United States.
READ THE STORY: KAKE (ABC)
A ‘disinformation’ board inspired by a dystopian novel
FROM THE MEDIA: Dystopian fiction always has fascinated me because writers such as Philip K. Dick and Ray Bradbury based their stories on real-world trends – and simply took them to logical extremes. Story lines involving, say, departments of pre-crime that arrested people based on algorithms seemed preposterous, but have turned out to be creepily close to the mark.
It’s hard to underestimate the absurdity of government directives and bureaucrats, so these tales – however chilling – often are quite funny. My favorite dystopian hero is Robert De Niro’s character, Archibald “Harry” Tuttle, in the movie “Brazil.” He was the government’s main enemy – a “villain” who fixed HVAC systems without a permit from Central Services.
READ THE STORY: DailyNews
The Kremlin’s interference in Colombia’s presidential election
FROM THE MEDIA: Quite alarmingly, Colombian intelligence, in conjunction with Five Eyes and NATO intelligence services, released a report in February detailing the disinformation campaign taken up by the Russian government to interfere in the Colombian 2022 presidential election. The report alleges that Russia promoted disinformation for the March legislative, and upcoming May 29 elections.
Colombian intelligence had been warned prior by U.S intelligence, including by Juan González, Director for the Western Hemisphere at the National Security Council in the White House. Russia, according to the report, is attempting to influence electoral outcomes to diminish public trust in democracy and to install their preferred candidate.
READ THE STORY: The City Paper Bogota
Why Hackers Target Critical Infrastructure and Why It's Difficult to Upgrade Cybersecurity
FROM THE MEDIA: In a recent 2022 Pwn2Own ethical hacking competition, two security researchers breached ICONICS Genesis64, a software designed for operators to use industrial machines, in mere seconds. In contrast, it took them three weeks to hack an iPhone way back in 2012. Considering that major, multimillion-dollar companies and industries own these apps, many are surprised to learn how it's much easier to attack than most modern smartphones. So why is our critical infrastructure in danger? And why does upgrading it take too long?
In the past, cybercriminals typically attacked individual users or general private businesses. And while these attacks were a cause for concern and led to millions of dollars in damages, they usually didn't earn the attackers much.
However, recent developments like the Colonial Pipeline and JBS Foods ransomware attacks showed that systems critical to public order and safety are more likely to be profitable. Furthermore, aside from monetary gain, cyberattacks on critical infrastructure can also be politically or militarily motivated.
READ THE STORY: Make Use Of
US sanctions North Korean cryptocurrency mixing firm
FROM THE MEDIA: The U.S. announced Friday it is sanctioning North Korean digital currency mixing firm Blender.io, which the country allegedly uses to launder stolen virtual currency and support cyber crimes.
The sanctions, imposed by the Treasury Department's Office of Foreign Assets Control, are the first ever on a digital asset mixing service. The new sanctions also point to the growing use of digital assets to perpetuate illegal acts by state actors and individuals. Mixing services combine various assets, including potentially illegally obtained funds and legitimately obtained funds, so that illegal actors can obscure the origin of stolen funds.
Blender is accused of helping Lazarus Group, a sanctioned North Korean cyber hacking group, to carry out a $620 million digital currency heist in March, the biggest of its kind to date.
READ THE STORY: Mainchi
RISC-V CEO seeks 'world domination' by winning over the likes of Intel
FROM THE MEDIA: The CEO of RISC-V's governing body says she wants to nothing less than "world domination" for the rising open-source processor technology, but to do that, the nonprofit needs buy-in from a variety of organizations, even those steeped in dominant, proprietary architectures, such as x86 giant Intel.
In an interview this week with The Register, RISC-V International CEO Calista Redmond reckons the buy-in, which comes in the form of paid memberships, is needed to support ongoing development of the royalty-free CPU instruction set architecture to better compete with x86 and Arm ISAs.
"We have to have a level of funding in order to operate and manage this special rodeo of ours," she says.
Redmond, an IBM veteran, pitches involvement in RISC-V International, which gives paying members an extra level of say in the ISA's future development, as a more even playing field for tech companies than what has been allowed with proprietary ISAs, namely x86 and Arm.
READ THE STORY: The Register
Sophisticated Malware Dubbed NetDooka Delivered as Part of Pay-Per-Install Service
FROM THE MEDIA: PrivateLoader, a pay-per-install (PPI) malware service has been flecked circulating a new and sophisticated malware framework dubbed, “NetDooka.” Malware like this has the capability of giving the attackers full control over the devices they infected.
Users are infected through inadvertent downloading of PrivateLoader via pirated software downloads. Once installed, the NetDooka malware is loaded, disabling encryption, and then the loader component is executed. Next, certain checks are performed to ensure the loader is not running in a virtual environment, and from the remote server, a malicious program is downloaded.
Another element of the loader that is executed by the malware is a dropper component. It is the dropper’s responsibility to decrypt and execute the final payload, a fully-functional and powerful RAT containing several features.
READ THE STORY: Cyber Security News
Items of interest
Colonial Pipeline was cyber wake-up call; Ukraine war is escalator
FROM THE MEDIA: One year ago, the Colonial Pipeline was hit by a disruptive ransomware attack forcing it to shut down operations for nearly a week.
The incident, which caused gas shortages in several states as fuel prices spiked, was a major wake-up call for critical industries to start taking cyber threats seriously and invest more in cybersecurity.
However, experts say that the war in Ukraine has put even more pressure on companies to expedite the investments they had begun a year ago as cybersecurity became front and center – both domestically and globally.
“The biggest escalator beyond Colonial last year has just been the war in Ukraine and the potential spillover into the U.S. and other developed parts of the world,” said Peter Lund, a cyber expert and chief technology officer at Industrial Defender.
“That’s really what’s gotten everyone on edge and rushing to mature their security programs,” he added.
Lund said that companies had started implementing more robust cybersecurity measures after the Colonial Pipeline attack but the war in Ukraine has certainly been the biggest motivator.
Brandon Wales, executive director at the Cybersecurity and Infrastructure Security Agency (CISA), who spoke at a cyber webinar on Thursday, said he has seen more engagement from industry leaders, including from chief information security officers who have told his agency that they need more resources now than ever before as the cyber threat environment has increased amid the war in Ukraine.
READ THE STORY: The Hill
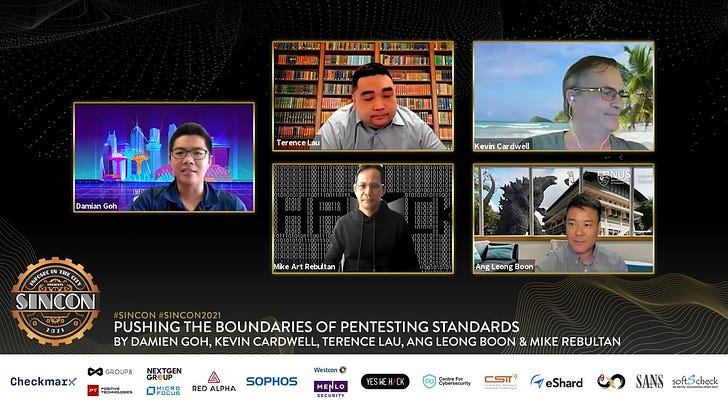
BizComm Conversation: Pushing the Boundaries of Pentesting Skillset (Video)
FROM THE MEDIA: The cybersecurity industry is filled with capture-the-flag (CTF) games and competitions, exploit labs, and pentesting training and certification. Whilst skills of "popping" boxes and capturing flags are great to have, how are they translated to mitigating cyber risks? What role does each of these play in the overall scheme of producing quality pentesters, red teamers, and even cyber defenders?
Threat Hunting: No Longer a Want, But a Need (Video)
FROM THE MEDIA: With the evolving threat landscape, defenders need not just arm themselves with tools, but with human expertise too.
About this Product
These open source products are reviewed from analysts at InfoDom Securities and provide possible context about current media trends in regard to the realm of cyber security. The stories selected cover a broad array of cyber threats and are intended to aid readers in framing key publicly discussed threats and overall situational awareness. InfoDom Securities does not specifically endorse any third-party claims made in their original material or related links on their sites, and the opinions expressed by third parties are theirs alone. Contact InfoDom Securities at dominanceinformation@gmail.com