Daily Drop (1259)
03-12-26
Thursday, Mar 12, 2025 // (IG): BB // GITHUB // SN R&D
TOOL:
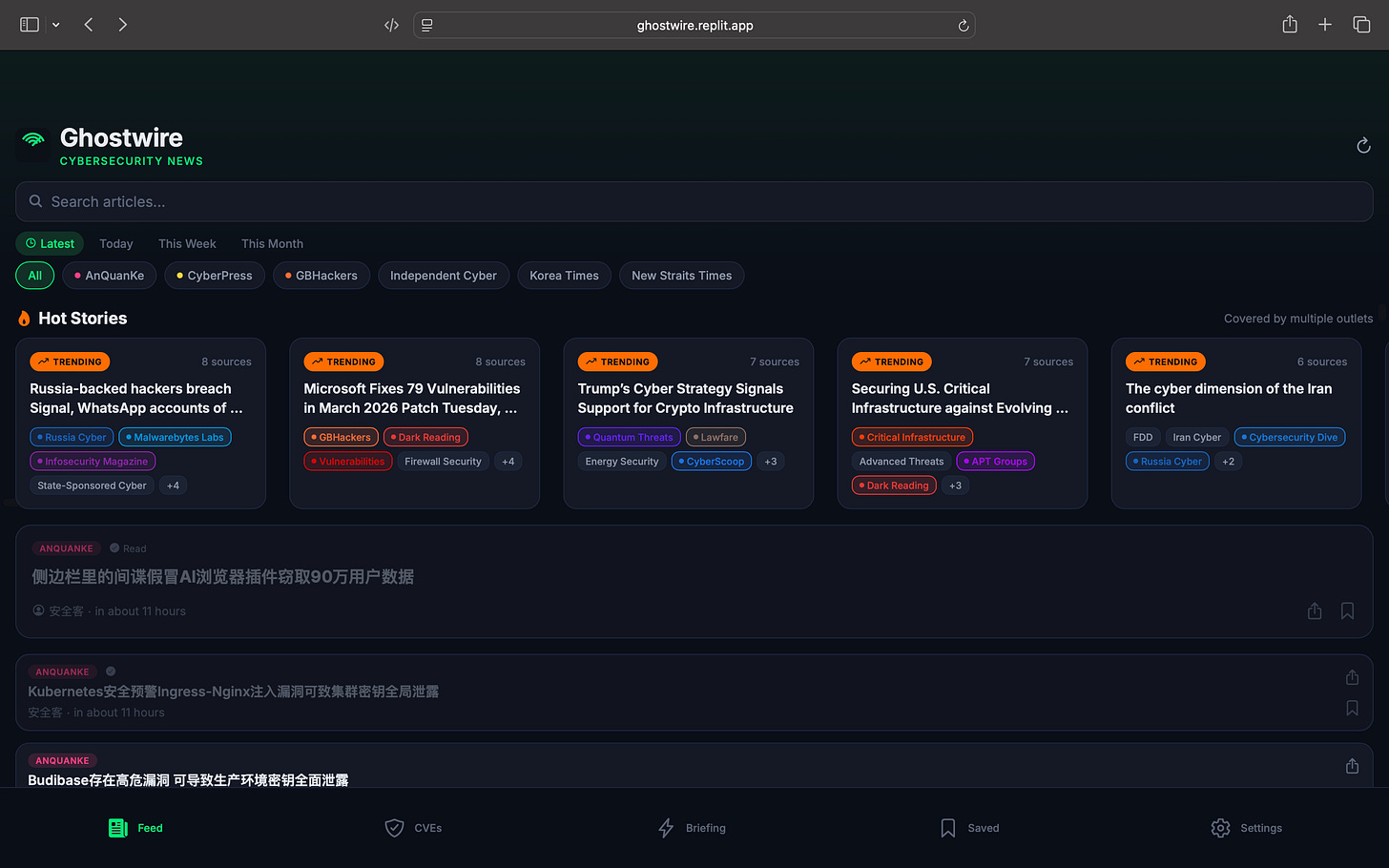
Ghostwire — Your Cybersecurity Intelligence Feed
Stop juggling 20 browser tabs. Ghostwire pulls from 53 cybersecurity news sources worldwide — Dark Reading, Krebs on Security, BleepingComputer, SecurityWeek, Unit42, CISA, CrowdStrike, and dozens more — into a single, real-time feed that updates every 5 minutes.
What you get:
Live Feed — Articles from 53+ sources, searchable, filterable by source and time. No more hopping between sites.
Trending Detection — When 3 or more outlets cover the same story, Ghostwire automatically flags it as trending. See what the industry is talking about right now.
CVE Tracker — Pulls directly from the National Vulnerability Database every 4 hours. Search by severity, track specific CVEs, get exploit alerts.
AI Daily Briefing — An AI-generated summary of the entire cybersecurity landscape, delivered fresh every day. Read the whole picture in 2 minutes.
Source Discovery — The platform doesn’t just aggregate — it actively hunts for new sources by analyzing article links and references across the web, then validates their RSS feeds automatically.
Global Coverage — English, Chinese, Russian, Japanese, German, French. Sources most English-language readers would never find.
Who it’s for:
SOC analysts, threat intel teams, CISOs, security researchers, and anyone who needs to stay current without spending hours reading. It’s the Bloomberg Terminal approach to cybersecurity news — everything in one place, always updating, with the signal pulled out of the noise.
CVE WATCH:
| CVE-2026-32127 | OpenEMR | SQL Injection in ajax graphs library | HIGH — Healthcare data at risk |
| CVE-2026-32126 | OpenEMR | Inverted ACL allows any authenticated user to modify clinical rules | HIGH — Integrity risk |
| CVE-2026-32125 | OpenEMR | Stored XSS via Dygraph Titles/Labels | MEDIUM-HIGH |
| CVE-2026-32121 | OpenEMR | Stored DOM XSS in Portal Signer Modal | MEDIUM-HIGH |
| CVE-2026-32128 | FastGPT Python Sandbox | File-write restriction bypass (v4.14.7 and earlier) | HIGH — AI platform code execution risk |
| CVE-2026-32110 | SiYuan | Full-Read SSRF via /api/network/forwardProxy | HIGH — Internal network exposure |
| CVE-2026-27591 | Winter CMS | Privilege escalation by authenticated backend users | HIGH — CMS compromise vector |
| CVE-2026-32103/32104/32101 | StudioCMS | IDOR, auth bypass, account takeover chain | HIGH — Full account compromise possible |
| CVE-2026-32112 | ha-mcp (Home Assistant) | XSS via OAuth Consent Form | MEDIUM — Smart home attack surface |
| CVE-2026-3955 | elecV2P | Code injection via jsfile endpoint | HIGH — Remote code execution |
NEWS:
Iran’s active mining of the Strait of Hormuz and ballistic missile strikes in Qatar territory are not merely kinetic events — they are the opening conditions for a sustained Iranian cyber campaign against Western and Gulf-aligned targets.
The FBI has already issued warnings that Iran aspired to conduct drone attacks on California infrastructure in retaliation for U.S. military involvement, and historical Iranian threat actor behavior (APT33, APT34, Charming Kitten) strongly indicates that offensive cyber operations against energy, transportation, and financial sectors will accompany — or precede — further physical escalation. Security teams supporting energy, logistics, port operations, or Gulf-region clients should elevate their threat posture immediately.
(Source: WSJ, Los Angeles Times, The Guardian)
AI-Driven Misinformation Surges During Middle East Conflict
Bottom Line Up Front (BLUF): Security experts warn that the current Middle East crisis highlights a new phase of AI-enabled misinformation, where generative AI tools accelerate the production of fake news, phishing campaigns, and deepfake media. The accessibility of these tools allows both state-aligned actors and cybercriminals to rapidly generate convincing content designed to influence public perception, conduct fraud, and exploit heightened geopolitical tensions.
Analyst Comments: The concern isn’t just that misinformation exists—it’s the scale and speed AI introduces. Generative AI dramatically lowers the barrier for producing credible-looking narratives, fake imagery, and impersonation content. In conflict scenarios where information moves faster than verification, adversaries can exploit that gap to shape narratives before fact-checking catches up. From a cyber operations standpoint, misinformation and cybercrime increasingly overlap operationally. AI-generated narratives often serve as the top layer of broader campaigns that include phishing, financial fraud, and credential harvesting. Deepfake audio for executive impersonation, fake news lures linking to malware, and AI-generated phishing emails are becoming common components of these hybrid operations.
READ THE STORY: Fast Company
Iran-Linked Hacktivists Claim Attacks on Verifone and Stryker
Bottom Line Up Front (BLUF): The pro-Iranian hacktivist group Handala has claimed cyberattacks against payment processor Verifone and medical technology firm Stryker, citing retaliation for recent U.S.–Israeli strikes on Iran. While the full impact remains unconfirmed, the incidents come amid warnings from researchers that Iran-aligned cyber groups are escalating activityand may expand disruptive operations against Western companies and infrastructure.
Analyst Comments: Handala has previously operated as a propaganda and hack-and-leak persona linked to Iranian cyber operations, sometimes overlapping with activity associated with MOIS-aligned actors such as Void Manticore. If the reported wiper activity against Stryker is accurate, it would represent a significant escalation beyond typical defacements or data leaks. Destructive attacks targeting large multinational firms—particularly those with Israeli business ties—would align with Tehran’s historical strategy of cyber retaliation during regional crises.
READ THE STORY: CyberNews
Iran-Linked Hackers Increasingly Leverage Cybercrime Ecosystem
Bottom Line Up Front (BLUF): Iran-linked cyber actors tied to the Ministry of Intelligence and Security (MOIS) are increasingly using criminal malware, ransomware infrastructure, and cybercrime marketplaces to conduct state-backed operations. Groups such as MuddyWater and Void Manticore are adopting malware-as-a-service tools, infostealers, and shared botnets to enhance operational capability while obscuring attribution.
Analyst Comments: This reflects a broader evolution in state cyber operations: nation-state actors increasingly operate inside the same ecosystems as cybercriminals rather than relying solely on government-developed tooling. For Iran, this model offers two advantages—plausible deniability and rapid capability scaling. Instead of investing years building bespoke malware, operators can simply purchase access to mature criminal platforms. The use of tools like Rhadamanthys infostealer, CastleLoader MaaS, and the Tsundere/DinDoor botnet shows how state actors can blend espionage and disruptive operations with commodity malware. These tools already have active development, support structures, and established infrastructure, giving state operators immediate operational capability.
READ THE STORY: GBhackers
Bejing’s Oil Purchases Provide Financial Lifeline to Iran During Conflict
Bottom Line Up Front (BLUF): China now absorbs roughly 90% of Iran’s oil exports, providing Tehran with a critical economic lifeline despite Western sanctions and ongoing regional conflict. Much of the trade relies on small Chinese “teapot” refineries, shadow-fleet shipping networks, and front companies, enabling Iranian oil revenues—some controlled by the Islamic Revolutionary Guard Corps (IRGC)—to continue funding military operations and regional proxies.
Analyst Comments: Instead of relying on a few large state-owned buyers, Iranian crude flows through smaller refiners, layered ownership structures, and maritime obfuscation tactics such as ship-to-ship transfers, flag switching, and falsified cargo documentation. China’s use of independent “teapot” refineries in Shandong province is particularly strategic. These smaller operators carry less systemic risk if sanctioned, giving Beijing a level of plausible deniability while still maintaining access to discounted crude supplies. However, many of these companies maintain joint ventures and commercial ties with state-owned Chinese energy firms, blurring the line between private and state-backed trade.
READ THE STORY: Kharon
UNC6426 Exploits NPM Supply-Chain Breach to Gain Full AWS Admin Access
Bottom Line Up Front (BLUF): Threat group UNC6426 exploited a compromised Nx NPM package to infiltrate a victim organization’s development pipeline and escalate privileges to full AWS administrative access within 72 hours. The attack leveraged stolen GitHub tokens, CI/CD trust relationships, and misconfigured cloud permissions—highlighting how supply-chain compromises can cascade from developer tools into complete cloud infrastructure compromise.
Analyst Comments: This incident underscores a growing reality in modern intrusions: developer environments and CI/CD pipelines are now high-value attack surfaces. Instead of targeting production infrastructure directly, attackers compromise widely used developer dependencies and pivot through automated build systems that already hold trusted access to cloud resources. The key weakness in this campaign was the GitHub-to-AWS OpenID Connect (OIDC) trust relationship, which many organizations use to avoid storing static credentials. While this model is generally secure, it becomes dangerous if attackers gain access to the upstream identity source—such as GitHub tokens or service accounts.
READ THE STORY: Cyber Press
China-Linked Camaro Dragon Targets Qatar With PlugX Espionage Campaign
Bottom Line Up Front (BLUF): Check Point researchers report that China-linked APT Camaro Dragon launched cyber-espionage campaigns against Qatari organizations within a day of the latest Middle East escalation. The operation used conflict-themed lures to deliver PlugX backdoor malware and Cobalt Strike, suggesting rapid intelligence collection tied to regional geopolitical developments. The activity highlights how quickly state-aligned actors pivot targeting priorities when crises emerge.
Analyst Comments: Deploying a campaign within 24 hours of a geopolitical escalation suggests pre-positioned infrastructure and standing playbooks for regional intelligence collection. Camaro Dragon (also tracked as Earth Preta / Mustang Panda) has a long track record of opportunistic espionage tied to diplomatic and military developments, and PlugX remains one of its most reliable tools. Technically, the campaign sticks to familiar tradecraft: DLL hijacking, LNK-based execution chains, and legitimate binaries used as loaders. None of this is novel—but it’s effective and low-risk from an attribution standpoint because these techniques blend well into normal system behavior.
READ THE STORY: Industrial Cyber
GAO Warns Fragmented Federal Cyber Rules Burden Critical Infrastructure
Bottom Line Up Front (BLUF): A new Government Accountability Office (GAO) report finds that U.S. critical infrastructure operators face a patchwork of overlapping federal cybersecurity regulations, creating compliance burdens that divert resources away from actual security work. Despite coordination efforts since 2020, inconsistent definitions, reporting timelines, and regulatory frameworks continue to drive costs and complexity for both large and small organizations.
Analyst Comments: The GAO’s emphasis on CIRCIA as a potential unifying mechanism is notable. If implemented effectively, it could centralize incident reporting across sectors and reduce duplicative reporting obligations. However, regulatory alignment is politically and bureaucratically difficult because agencies historically guard their authorities. Another takeaway is the impact on smaller infrastructure operators, which often lack dedicated compliance teams. When regulatory requirements diverge, larger enterprises can absorb the overhead—but smaller utilities, hospitals, and regional providers cannot. Ironically, those organizations may be most vulnerable to cyber threats, meaning regulatory complexity can indirectly increase systemic risk.
READ THE STORY: MeriTalk
Qualcomm Zero-Day Exploited in Targeted Android Attacks
Bottom Line Up Front (BLUF): Google’s March Android security bulletin disclosed active exploitation of CVE-2026-21385, a high-severity Qualcomm GPU vulnerability affecting numerous Android chipsets. The flaw—an integer overflow leading to memory corruption—appears to be used in limited, targeted attacks, a phrase Google typically reserves for surveillance or nation-state activity. Patches were issued to OEMs in January, but device manufacturers control deployment timelines, leaving many Android devices potentially exposed.
Analyst Comments: When Google uses the phrase “limited, targeted exploitation,” it usually signals high-end operators rather than commodity cybercrime. Similar wording appeared in past Android zero-days later linked to commercial spyware vendors. The vulnerability itself requires local access, meaning it likely functions as a post-compromise privilege escalation in a multi-stage exploit chain—initial access via phishing, malicious apps, or another RCE, followed by GPU-level exploitation for persistence or deeper device control.
READ THE STORY: DarkReading
Items of interest
China Quietly Pulls Back From Afghanistan as Security Risks Mount
Bottom Line Up Front (BLUF): China is increasingly withdrawing personnel and scaling back economic activity in Afghanistan after repeated attacks on Chinese nationals and projects. The pullback reflects Beijing’s growing concerns about deteriorating security conditions, the Taliban’s inability to guarantee protection, and Pakistan’s declining ability to act as China’s regional security intermediary.
Analyst Comments: Recent intelligence reporting and open-source analysis suggest that Ministry of State Security has instructed Chinese teams and commercial interests to reduce or withdraw operations from Afghanistan. The move follows a cascade of security incidents throughout 2025 and early 2026 targeting Chinese workers, mining operations, and infrastructure projects. Although Beijing initially saw Afghanistan as an opportunity following the U.S. withdrawal in 2021, the combination of militant attacks, regional instability, and failed economic agreements has forced China to reassess its strategy.
READ THE STORY: IntelligenceOnline
US-UK-China Slam Taliban: “Disgusting Restrictions On Women’s Rights (Video)
FROM THE MEDIA: At the United Nations Security Council, the United States, United Kingdom, and China expressed a shared stance on rising tensions between Pakistan and Afghanistan. All sides urged restraint, dialogue, and diplomatic engagement to avoid further escalation while warning about humanitarian risks and regional instability if clashes continue along the border. For more details, watch our story and subscribe to our channel, DRM News.
China’s Five-Point Message To The West On Afghanistan, Has This Advice For Taliban On Terror (Video)
FROM THE MEDIA: China’s Deputy Permanent Representative Geng Shuang, addressing the UN Security Council debate on Afghanistan, urged the international community to maintain pragmatic engagement, scale up humanitarian aid, and resist politicizing assistance. He supported the reauthorization of exemptions to travel bans for Afghan officials, condemned sanctions as tools of national interest, and called on the US and other historic donors to resume aid and return Afghan central bank assets.
The selected stories cover a broad range of cyber threats and are intended to help readers frame key publicly discussed threats and improve overall situational awareness. InfoDom Securities does not endorse any third-party claims made in its original material or related links on its sites; the opinions expressed by third parties are theirs alone. For further questions, don't hesitate to get in touch with InfoDom Securities at dominanceinformation@gmail.com.