Daily Drop (1258)
03-11-26
Wednesday, Mar 11, 2025 // (IG): BB // GITHUB // SN R&D
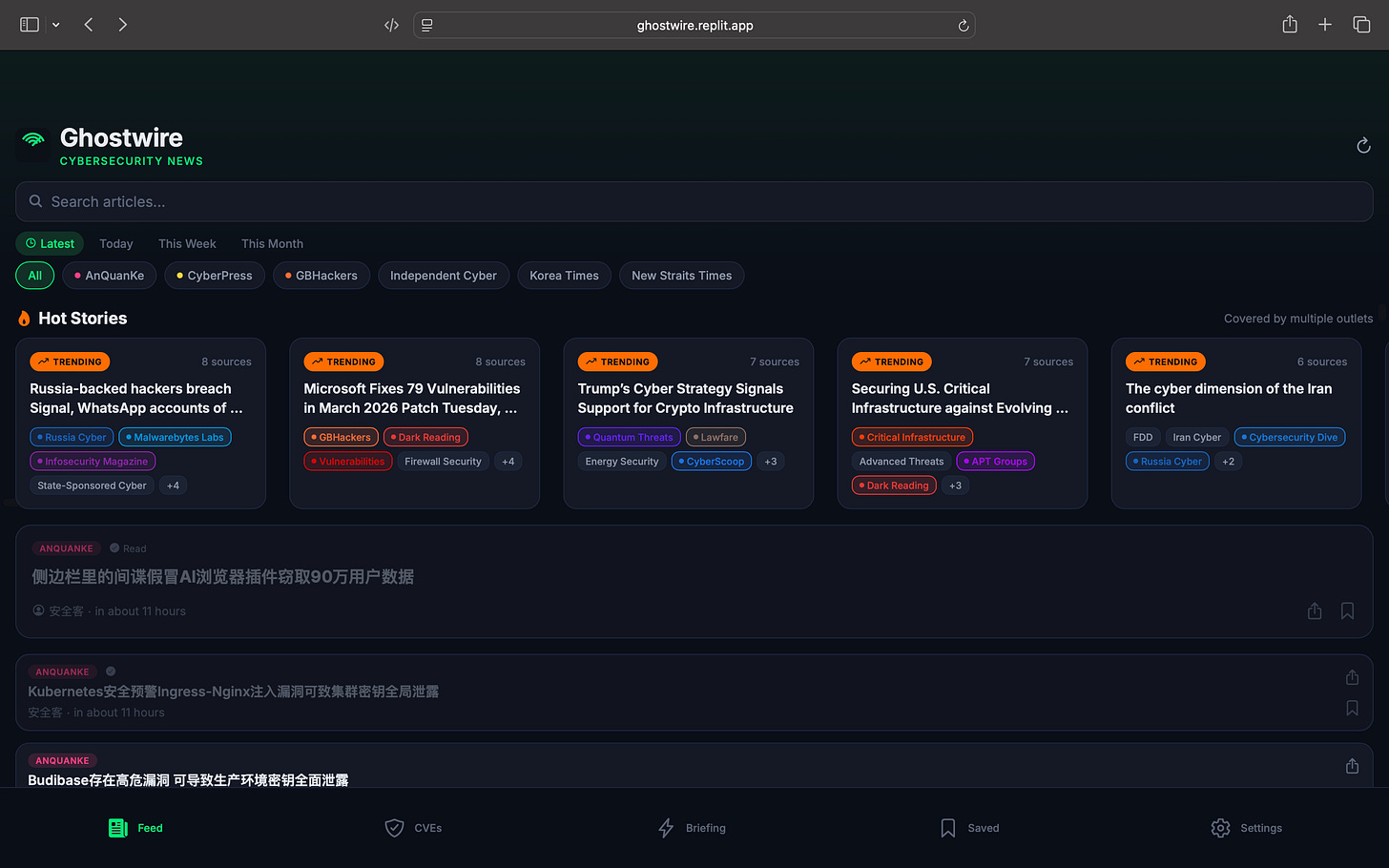
TOOL:
Ghostwire — Your Cybersecurity Intelligence Feed
Stop juggling 20 browser tabs. Ghostwire pulls from 53 cybersecurity news sources worldwide — Dark Reading, Krebs on Security, BleepingComputer, SecurityWeek, Unit42, CISA, CrowdStrike, and dozens more — into a single, real-time feed that updates every 5 minutes.
What you get:
Live Feed — Articles from 53+ sources, searchable, filterable by source and time. No more hopping between sites.
Trending Detection — When 3 or more outlets cover the same story, Ghostwire automatically flags it as trending. See what the industry is talking about right now.
CVE Tracker — Pulls directly from the National Vulnerability Database every 4 hours. Search by severity, track specific CVEs, get exploit alerts.
AI Daily Briefing — An AI-generated summary of the entire cybersecurity landscape, delivered fresh every day. Read the whole picture in 2 minutes.
Source Discovery — The platform doesn’t just aggregate — it actively hunts for new sources by analyzing article links and references across the web, then validates their RSS feeds automatically.
Global Coverage — English, Chinese, Russian, Japanese, German, French. Sources most English-language readers would never find.
Who it’s for:
SOC analysts, threat intel teams, CISOs, security researchers, and anyone who needs to stay current without spending hours reading. It’s the Bloomberg Terminal approach to cybersecurity news — everything in one place, always updating, with the signal pulled out of the noise.
NEWS:
Microsoft Patch Tuesday Lands With 83 Fixes — No Actively Exploited Zero-Days for First Time in Six Months
Bottom Line Up Front (BLUF): Microsoft’s March 2026 Patch Tuesday addressed 83 vulnerabilities across its product stack, marking the first update in six months without an actively exploited zero-day. Six flaws were flagged as more likely to be exploited, and several Office vulnerabilities could enable remote code execution via malicious documents, reinforcing the continued risk posed by common collaboration tools.
Analyst Comments: The absence of an actively exploited zero-day is a welcome break after several months of aggressive exploitation cycles. That said, the patch set still includes multiple privilege-escalation bugs and Office RCE paths that attackers routinely weaponize in phishing campaigns.
READ THE STORY: CyberScoop
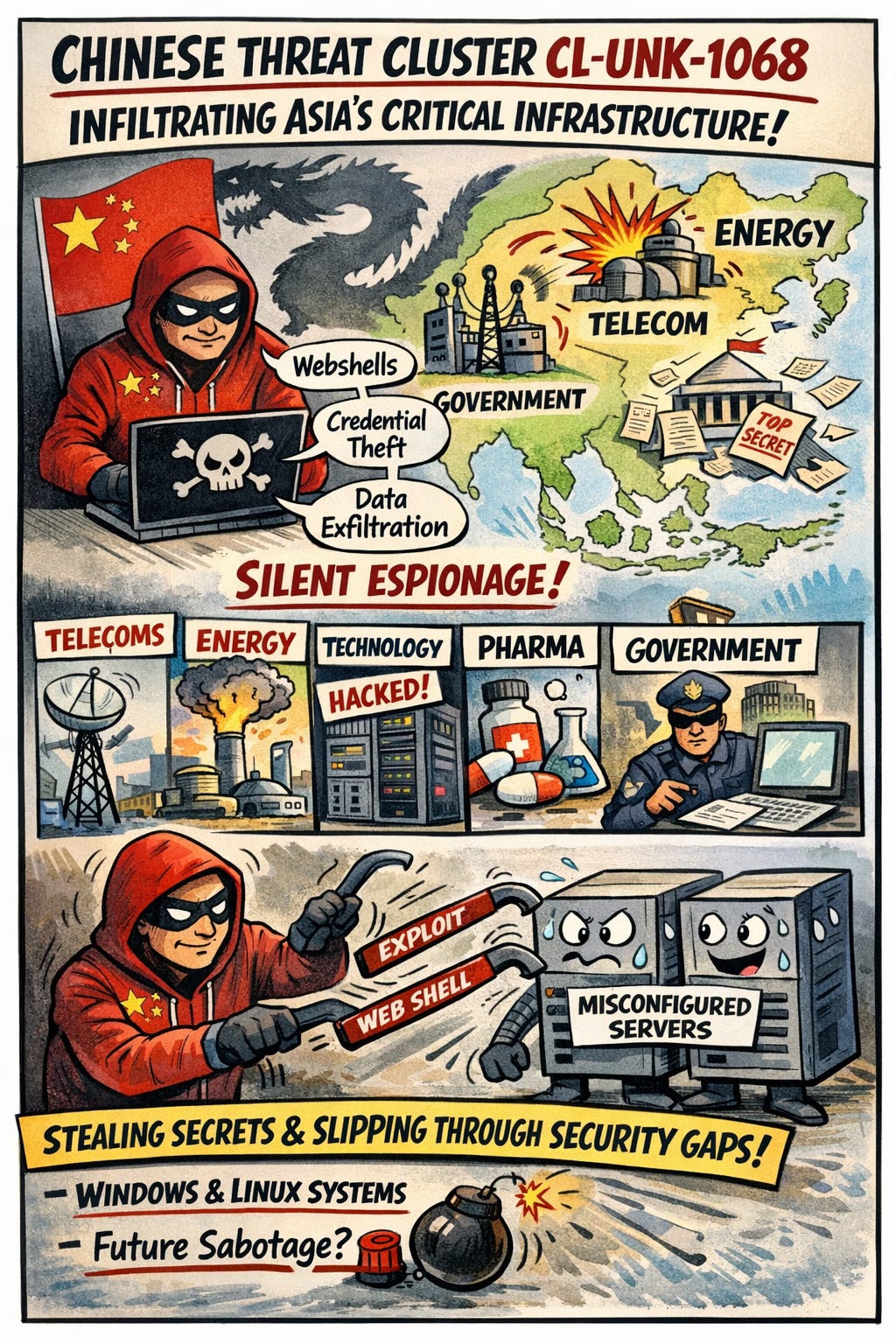
CL-UNK-1068 Targets Asian Critical Infrastructure in Long-Running Espionage Campaign
Bottom Line Up Front (BLUF): A previously untracked threat cluster, CL-UNK-1068, has been quietly infiltrating critical infrastructure and government organizations across South, Southeast, and East Asia for several years. The group exploits misconfigured web servers to deploy webshells, enabling credential theft, lateral movement, and data exfiltration. The tooling and victimology strongly point toward state-aligned cyber espionage linked to Chinese interests, though researchers have not issued a formal attribution.
Analyst Comments: The tradecraft here is fairly classic state-sponsored espionage operations—quiet persistence, credential harvesting, and systematic data collection from strategic sectors. Telecommunications, energy, and government entities are prime intelligence targets, especially in regions where geopolitical competition with China is intensifying. What stands out is the cross-platform flexibility. CL-UNK-1068 operates comfortably across Windows and Linux environments, adapting its toolset depending on the target infrastructure. That versatility is common among mature espionage operators who expect to encounter heterogeneous enterprise environments.
READ THE STORY: SCMEDIA
China-Linked Hackers Target Telecom Providers With New Malware
Bottom Line Up Front (BLUF): Security researchers from Cisco Talos have uncovered a sophisticated cyber campaign targeting telecommunications infrastructure. The activity is attributed to a China-linked threat actor tracked as UAT-9244, which uses multiple malware families to infiltrate networks, maintain persistence, and convert compromised telecom systems into attack platforms capable of scanning and brute-forcing other services.
Analyst Comments: Researchers report that the threat group has been active since 2024 and has primarily targeted telecom providers across South America. According to Talos, the group shows strong operational overlaps with the China-aligned cyber-espionage group Famous Sparrow. The campaign employs three malware tools—TernDoor, PeerTime, and BruteEntry—to establish remote access, maintain long-term persistence, and expand attacker control across compromised infrastructure. The operation focuses on Windows systems, Linux endpoints, and network edge devices commonly used in telecommunications environments.
READ THE STORY: Cyber Press
Open-Source RFP Analysis Reveals China’s PLA AI “Wish List” for Future Warfare
Bottom Line Up Front (BLUF): Research from Georgetown’s Center for Security and Emerging Technology (CSET) analyzed more than 9,000 public procurement requests (RFPs) issued by China’s People’s Liberation Army (PLA) between 2023 and 2024. The documents outline a broad push to integrate AI across command, cyber warfare, surveillance, decision-making, and psychological operations, signaling a strategic effort to achieve “intelligentized” warfare and information dominance across all domains.
Analyst Comments: The emphasis on AI decision-support systems, cognitive warfare platforms, and large-scale surveillance capabilitiesreflects China’s doctrine of System Destruction Warfare, which focuses on disabling an adversary’s command networks, sensors, and information systems rather than relying solely on traditional kinetic conflict. Equally notable is the PLA’s investment in deepfake generation, social media analysis, and narrative manipulation tools, highlighting the growing importance of the cognitive domain in modern warfare. Organizations should expect state-level cyber operations to become increasingly AI-enabled, improving both offensive capabilities and information operations.
READ THE STORY: Rescana
APT28 Deploys BEARDSHELL and Modified COVENANT Malware to Spy on Ukrainian Military
Bottom Line Up Front (BLUF): The Russian GRU-linked threat group APT28 (Fancy Bear / Sednit) has been conducting long-term cyber espionage operations targeting Ukrainian military personnel using a toolkit that includes BEARDSHELL, SLIMAGENT, and a heavily modified version of the COVENANT framework. The implants enable remote command execution, keylogging, screenshot capture, and covert data exfiltration, with command-and-control (C2) infrastructure routed through legitimate cloud storage services such as Icedrive and Filen.
Analyst Comments: APT28’s playbook here reflects a mature espionage campaign focused on persistence and stealth rather than smash-and-grab intrusion. The malware lineage connecting SLIMAGENT to the older XAgent implant shows that the group continues to iterate on proven tooling rather than reinvent it. Reusing code while updating infrastructure helps them maintain operational familiarity while evading signature-based detection. Another notable aspect is their consistent abuse of legitimate cloud storage platforms for C2. Using services like Icedrive, Filen, pCloud, and Koofr blends malicious traffic into normal encrypted cloud activity, complicating network-level detection.
READ THE STORY: THN
Iran-Linked Seedworm Group Targets U.S. Critical Infrastructure with New Backdoors
Bottom Line Up Front (BLUF): Security researchers report a surge in cyber activity by the Iran-linked APT group Seedworm (MuddyWater / TEMP.Zagros / Static Kitten) targeting U.S. and allied organizations. Since February 2026, intrusions have hit a U.S. bank, a U.S. airport, a U.S. software company with Israeli operations, and non-profits in the U.S. and Canada. Investigators uncovered new malware including a Deno-based backdoor dubbed “Dindoor” and a Python backdoor named “Fakeset,” suggesting a coordinated campaign aimed at long-term network access and potential future disruptive operations.
Analyst Comments: Seedworm has historically focused on espionage and network footholds, but their operations often blur the line between intelligence collection and disruptive cyber activity. The timing of this campaign—amid rising geopolitical tension involving Iran, Israel, and the United States—raises the possibility that these intrusions are pre-positioning operations. The tooling is also interesting. A backdoor built on Deno (a modern JavaScript runtime) is relatively uncommon in APT operations and may help blend malicious activity into legitimate developer or automation environments. Meanwhile, the use of cloud services like Backblaze and Wasabi for payload delivery and exfiltration reflects a broader shift among APT groups toward abusing legitimate infrastructure to reduce detection.
READ THE STORY: Cyber Press
Malicious Rust Crates and AI Bot Target CI/CD Pipelines to Steal Developer Secrets
Bottom Line Up Front (BLUF): Researchers uncovered five malicious Rust crates published on crates.io that impersonate time-related utilities while secretly stealing .env secrets from developer environments. The packages exfiltrate sensitive data—such as API keys and tokens—to attacker infrastructure. In a related campaign, an AI-powered bot dubbed “hackerbot-claw” exploited misconfigured GitHub Actions workflows to steal repository credentials and push malicious artifacts, highlighting escalating attacks on software supply chains and CI/CD pipelines.
Analyst Comments: Secrets stored in .env files often provide direct access to cloud infrastructure, package registries, databases, and GitHub tokens, meaning a single compromised dependency can cascade into broader supply chain compromise. The Rust crates themselves are relatively simple malware—no persistence, minimal obfuscation—but they don’t need sophistication. When malicious code executes inside CI pipelines, it inherits trusted credentials and automation privileges. That alone can yield significant access. The second part of the campaign is arguably more concerning. The AI-driven GitHub bot scanning repositories for vulnerable workflows demonstrates how automation and AI can accelerate reconnaissance and exploitation. By embedding malicious logic in a pull request targeting pull_request_target workflows, attackers can execute code on build servers and extract secrets without direct repository compromise.
READ THE STORY: THN
GhostClaw npm Package Masquerades as OpenClaw, Deploys Infostealer and Persistent RAT Targeting Developers
Bottom Line Up Front (BLUF): Researchers at JFrog uncovered a malicious npm package, @openclaw-ai/openclawai, impersonating the legitimate OpenClaw CLI installer. The package deploys a sophisticated malware loader called GhostLoader, which steals developer secrets—including SSH keys, cloud credentials, browser sessions, crypto wallets, and AI agent configurations—before transitioning into a persistent remote access trojan (RAT). The attack leverages npm postinstall hooks, social engineering, and encrypted payload delivery to quietly compromise developer systems.
Analyst Comments: JFrog Security identified the malicious npm package @openclaw-ai/openclawai, designed to impersonate the OpenClaw CLI installer. Although the package appears benign—containing a clean package.json and minimal code—the real functionality is triggered through a postinstall script that installs a malicious binary globally. When executed, the installer displays a convincing CLI interface while an obfuscated script downloads a second-stage payload from trackpipe[.]dev. The payload is encrypted using AES-256-GCM and executed in a detached Node process.
READ THE STORY: GBhackers
BlackSanta EDR Killer Malware Targets HR Departments Through Fake Job Applications
Bottom Line Up Front (BLUF): A new malware campaign is targeting human resources (HR) departments using malicious job application filesdisguised as resumes. The attack delivers a multi-stage payload culminating in BlackSanta, an EDR-killing module that disables endpoint protections using a Bring Your Own Vulnerable Driver (BYOVD) technique. Once defenses are neutralized, attackers establish command-and-control (C2) access and exfiltrate sensitive data from compromised systems.
Analyst Comments: The use of ISO container files combined with malicious LNK shortcuts is a tactic seen in several modern malware operations because it bypasses some email attachment filtering and Mark-of-the-Web protections. From there, the attack chain becomes increasingly sophisticated—leveraging PowerShell loaders, steganographic payload delivery, DLL sideloading, and fileless execution. The most concerning element is BlackSanta’s BYOVD technique, which loads a legitimate but vulnerable signed driver to obtain kernel-level privileges. Once active, it can terminate EDR agents, disable Microsoft Defender, suppress logging, and blind security monitoring tools. Because the drivers are signed, traditional endpoint protections often struggle to block them.
READ THE STORY: GBhackers
KadNap Malware Builds 14,000-Node Router Botnet Using P2P Infrastructure
Bottom Line Up Front (BLUF): Researchers have identified a new malware family called KadNap that has infected over 14,000 edge networking devices, primarily Asus routers, to create a decentralized proxy botnet. The malware uses a custom implementation of the Kademlia Distributed Hash Table (DHT) protocol to hide its command-and-control infrastructure and make disruption difficult. Compromised devices are monetized through a proxy service known as Doppelgänger, which sells access to residential proxy nodes across more than 50 countries.
Analyst Comments: KadNap represents an evolution in router botnets shifting toward decentralized command-and-control. Instead of relying on a single or small set of C2 servers—which defenders can sinkhole or block—the malware leverages a peer-to-peer DHT architecture similar to BitTorrent networks. This makes the botnet significantly harder to dismantle. The monetization model is also notable. Rather than directly launching attacks like DDoS or credential stuffing, the operators are selling access to compromised routers as anonymous residential proxies. That infrastructure can then be rented by other cybercriminals for fraud, scraping, ad abuse, account takeover campaigns, and malware distribution.
READ THE STORY: THN
Malformed ZIP Header Flaw Lets Attackers Hide Malware from Antivirus and EDR (CVE-2026-0866)
Bottom Line Up Front (BLUF): A newly disclosed vulnerability, CVE-2026-0866, allows attackers to hide malicious payloads inside malformed ZIP archives that evade antivirus and EDR scanning. By manipulating the compression method field in ZIP headers, attackers can prevent security tools from properly extracting and analyzing the archive contents. The result: malware can remain undetected during automated inspection while still being recoverable and executable using custom extraction tools.
Analyst Comments: Archive-based evasion isn’t new, but this technique is notable because it targets a fundamental assumption in many scanning engines: that archive metadata is trustworthy. If security tools rely on the declared compression method to determine how to unpack files, a malformed header effectively blinds the scanner. This technique works as a pre-execution defense bypass, meaning the malicious payload can move through email gateways, file uploads, and endpoint scanning pipelines without ever being analyzed. Once on the target system, attackers can use a custom loader that ignores the corrupted metadata and extracts the hidden payload directly.
READ THE STORY: Cyber Press
“LeakyLooker” Flaws in Google Looker Studio Could Enable Cross-Tenant SQL Attacks
Bottom Line Up Front (BLUF): Researchers from Tenable disclosed nine cross-tenant vulnerabilities in Google Looker Studio, collectively named LeakyLooker, that could have allowed attackers to execute arbitrary SQL queries across victim databases in Google Cloud environments. The flaws potentially enabled data exfiltration, modification, and deletion across GCP servicessuch as BigQuery, Google Sheets, Spanner, PostgreSQL, and MySQL. Google patched the issues after responsible disclosure in June 2025, and there is no evidence of active exploitation.
Analyst Comments: Looker Studio is designed so report viewers can analyze data without influencing it. These flaws undermined that assumption by enabling viewer-level access to escalate into database-level control. The attack paths are particularly concerning because they require minimal interaction—sometimes zero clicks—and exploit legitimate features like report sharing, connectors, and cloning functionality. In environments where Looker dashboards are widely shared internally or publicly, attackers could have leveraged these weaknesses to pivot into full dataset exposure within a GCP project.
READ THE STORY: THN
The Spy in Your Sidebar: Fake AI Browser Extensions Steal Data from 900K Users
Bottom Line Up Front (BLUF): Microsoft Defender researchers uncovered a large-scale campaign involving malicious Chromium browser extensions masquerading as AI assistant tools. The extensions have accumulated roughly 900,000 installs and are actively exfiltrating AI chat histories, internal URLs, and browsing metadata from users—including those in over 20,000 enterprise tenants. Once installed, the extensions quietly monitor browsing activity and transmit encoded data to attacker-controlled infrastructure.
Analyst Comments: With employees increasingly relying on AI tools for coding, documentation, and internal analysis, the browser now contains a steady stream of proprietary prompts, workflows, and business context. By disguising malware as AI productivity tools, the threat actor sidesteps traditional suspicion. Browser extensions already require extensive permissions, so malicious functionality can blend in with legitimate behavior. The real prize isn’t just credentials—it’s intellectual property and operational insight pulled directly from AI conversations. Expect more campaigns like this. AI assistants are now embedded in daily workflows, which means prompt data is becoming a new category of sensitive information. Organizations should assume that anything entered into AI tools could be exposed if the surrounding browser environment is compromised.
READ THE STORY: Daily Cyber Security
Items of interest
China Quietly Pulls Back From Afghanistan as Security Risks Mount
Bottom Line Up Front (BLUF): China is increasingly withdrawing personnel and scaling back economic activity in Afghanistan after repeated attacks on Chinese nationals and projects. The pullback reflects Beijing’s growing concerns about deteriorating security conditions, the Taliban’s inability to guarantee protection, and Pakistan’s declining ability to act as China’s regional security intermediary.
Analyst Comments: Recent intelligence reporting and open-source analysis suggest that Ministry of State Security has instructed Chinese teams and commercial interests to reduce or withdraw operations from Afghanistan. The move follows a cascade of security incidents throughout 2025 and early 2026 targeting Chinese workers, mining operations, and infrastructure projects. Although Beijing initially saw Afghanistan as an opportunity following the U.S. withdrawal in 2021, the combination of militant attacks, regional instability, and failed economic agreements has forced China to reassess its strategy.
READ THE STORY: IntelligenceOnline
US-UK-China Slam Taliban: “Disgusting Restrictions On Women’s Rights (Video)
FROM THE MEDIA: At the United Nations Security Council, the United States, United Kingdom, and China expressed a shared stance on rising tensions between Pakistan and Afghanistan. All sides urged restraint, dialogue, and diplomatic engagement to avoid further escalation while warning about humanitarian risks and regional instability if clashes continue along the border. For more details, watch our story and subscribe to our channel, DRM News.
China’s Five-Point Message To The West On Afghanistan, Has This Advice For Taliban On Terror (Video)
FROM THE MEDIA: China’s Deputy Permanent Representative Geng Shuang, addressing the UN Security Council debate on Afghanistan, urged the international community to maintain pragmatic engagement, scale up humanitarian aid, and resist politicizing assistance. He supported the reauthorization of exemptions to travel bans for Afghan officials, condemned sanctions as tools of national interest, and called on the US and other historic donors to resume aid and return Afghan central bank assets.
The selected stories cover a broad range of cyber threats and are intended to help readers frame key publicly discussed threats and improve overall situational awareness. InfoDom Securities does not endorse any third-party claims made in its original material or related links on its sites; the opinions expressed by third parties are theirs alone. For further questions, don't hesitate to get in touch with InfoDom Securities at dominanceinformation@gmail.com.