Daily Drop (1256)
03-07-26
Saturday, Mar 07, 2025 // (IG): BB // GITHUB // SN R&D
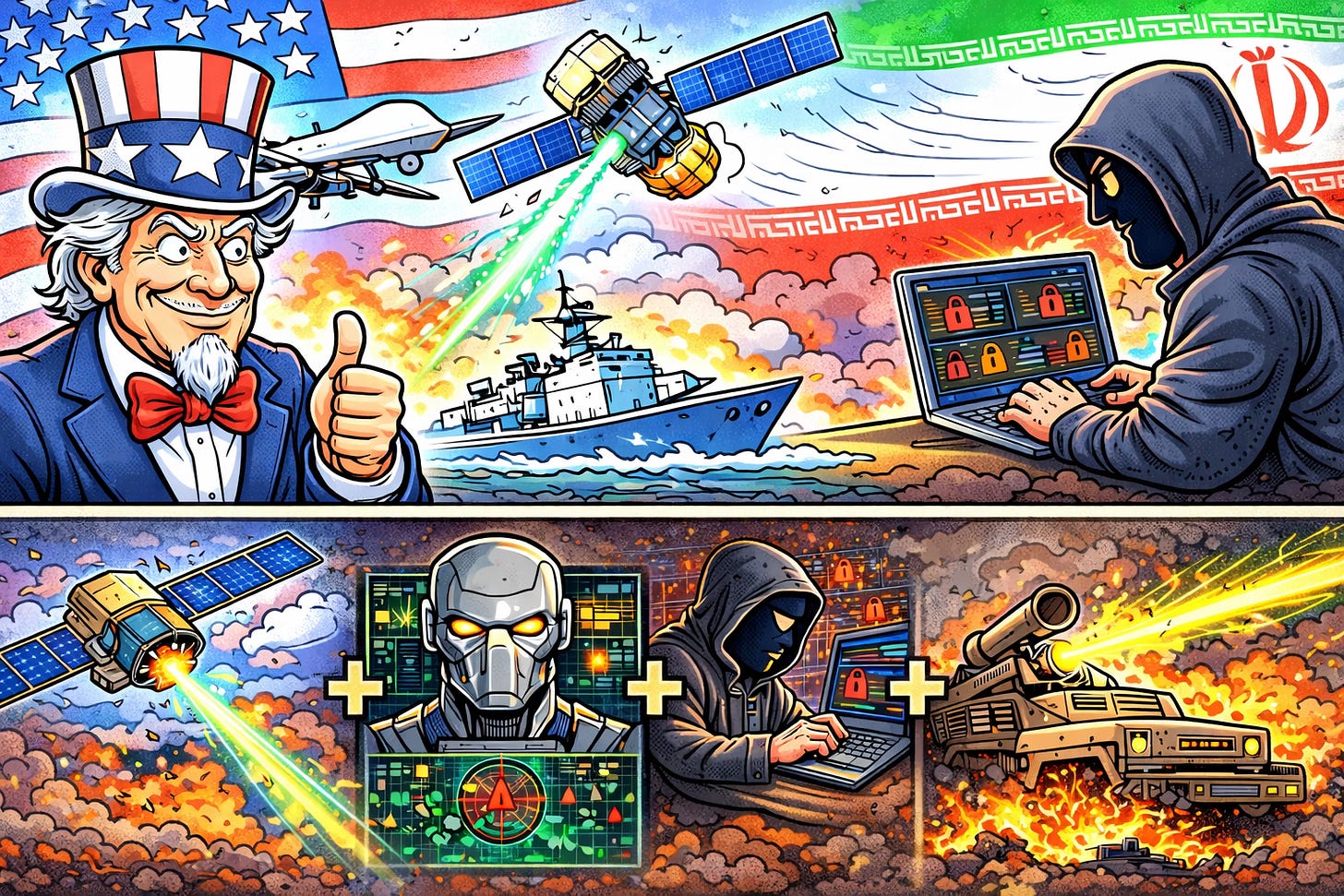
U.S. Uses AI, Satellites, and Cyber Operations to Disrupt Iran’s Military in Ongoing Conflict
Bottom Line Up Front (BLUF): The United States and its allies are employing a technology-centric warfare model against Iran, combining satellite surveillance, AI-driven targeting, cyber operations, and directed-energy weapons to degrade Tehran’s military capabilities. Early phases of the campaign reportedly identified over 1,000 targets within 24 hours, while cyber attacks disrupted Iranian command, communications, and air-defense networks before kinetic strikes began.
Analyst Comments: AI systems embedded in platforms like Project Maven ingest enormous volumes of intelligence—from satellites, drones, and signals intercepts—and compress the “kill chain” from hours or days to minutes. Cyber operations appear to have played a preparatory battlefield role, targeting Iranian sensor networks, communications infrastructure, and command systems. By blinding and isolating air-defense and missile units before the first aircraft launched, the operation likely reduced the effectiveness of Iranian retaliation.
READ THE STORY: WION
Russia Allegedly Shared Intelligence With Iran That Could Target U.S. Military Assets
Bottom Line Up Front (BLUF): U.S. intelligence officials say Russia may have provided Iran with intelligence that could help target American military assets in the Persian Gulf, including warships, aircraft, and regional bases. While there is no evidence Moscow is directing Iranian operations, the intelligence sharing marks the first indication of potential Russian involvement in the ongoing U.S.–Israel conflict with Iran, raising concerns about broader geopolitical escalation.
Analyst Comments: Over the past several years, the relationship has grown from diplomatic coordination into practical military cooperation, particularly after Iran supplied Russia with Shahed drones and other weapons used in Ukraine. Providing targeting or situational intelligence to Iran would effectively represent reciprocal support, allowing Moscow to indirectly pressure the United States while avoiding direct confrontation. This kind of intelligence sharing also fits Russia’s broader strategy of asymmetric competition with the West, where proxy relationships and deniable assistance allow influence without formal alliance commitments.
READ THE STORY: EURONEWS // FT
Iran Strikes Gulf Energy Infrastructure, Raising Global Recession Concerns
Bottom Line Up Front (BLUF): Iran’s expanding missile and drone strikes across the Gulf energy sector and regional infrastructure—including targets in Qatar, Saudi Arabia, Iraq, and Azerbaijan—are disrupting global oil and LNG markets. With 20% of the world’s oil transiting the Strait of Hormuz and major LNG facilities temporarily halted, analysts warn that prolonged conflict could drive global energy shortages, spike prices, and trigger a broader economic downturn.
Analyst Comments: Energy infrastructure is one of the most effective strategic pressure points in modern conflict. Iran’s strikes appear aimed less at decisive military gains and more at economic disruption and geopolitical leverage. By targeting LNG terminals, refineries, and shipping routes, Tehran can influence global commodity prices, supply chains, and political pressure on Western governments without directly confronting U.S. or Israeli forces at scale.
READ THE STORY: EURONEWS
Middle East War Puts Big Tech’s Gulf Investments at Risk
Bottom Line Up Front (BLUF): The expanding conflict between Iran and the U.S.–Israel coalition is threatening trillions of dollars in technology and AI infrastructure investments across the Persian Gulf, including major projects by Amazon, Microsoft, Nvidia, and Oracle. Iranian drone strikes have already damaged cloud infrastructure in the UAE and Bahrain, raising concerns about the long-term security of tech operations in a region that has become central to global AI expansion.
Analyst Comments: For the past decade, Gulf states have aggressively pursued a strategy of economic diversification away from oil, using sovereign wealth funds to attract Western tech firms to build data centers, AI compute hubs, and cloud infrastructure. The region offers advantages including cheap energy, large investment capital, and pro-business regulatory environments, making it attractive for hyperscale AI infrastructure. The current conflict introduces a new category of risk: geopolitical exposure of critical digital infrastructure. Data centers and cloud facilities were historically treated as civilian commercial assets, but the war demonstrates how they can become indirect strategic targets—especially when they support Western technology ecosystems.
READ THE STORY: FT
US State Laws Push Age Checks Into Operating Systems, Creating Headaches for Open Source
Bottom Line Up Front (BLUF): Several U.S. states are advancing legislation that would require operating systems to collect and share users’ age information with app stores and developers. Bills in California, Colorado, and New York could force OS vendors to verify or store age data beginning as early as 2027, shifting age verification from individual apps to the device level. Open-source operating systems may struggle to comply, with some projects already considering geographic bans to avoid legal exposure.
Analyst Comments: Moving age verification into the operating system layer fundamentally changes the trust and privacy model of personal computing. Instead of each service managing its own controls, the OS becomes a centralized identity and age attestation authority. That might simplify compliance for big commercial ecosystems like Apple and Microsoft, which already require user accounts and cloud integration.
READ THE STORY: The Register
OpenAI Launches Codex Security: AI Agent Automates Vulnerability Discovery and Patching
Bottom Line Up Front (BLUF): OpenAI has introduced Codex Security, a research-preview AI security agent designed to automatically detect, validate, and patch software vulnerabilities. The system analyzes entire code repositories to build context-aware threat models, significantly reducing false positives and triage noise. Early testing shows major improvements in accuracy while identifying hundreds of critical vulnerabilities across open-source projects.
Analyst Comments: Application security has long struggled with alert fatigue and low-quality findings from static analysis tools. Codex Security appears to target that exact pain point by combining repository context, sandbox validation, and exploit generation to verify whether a vulnerability is actually exploitable. If the reported numbers hold up—especially the 84% reduction in noise and 50% drop in false positives—this could meaningfully reduce the burden on AppSec teams.
READ THE STORY: Cyber Press
Anthropic’s Claude AI Finds 22 Firefox Vulnerabilities in Two Weeks
Bottom Line Up Front (BLUF): Anthropic researchers used the Claude Opus 4.6 AI model to identify 22 previously unknown vulnerabilities in Mozilla Firefox, including 14 high-severity flaws, during a two-week testing period. The bugs—most patched in Firefox 148—were discovered while scanning nearly 6,000 C++ files, demonstrating the growing effectiveness of AI-assisted vulnerability discovery in large codebases.
Analyst Comments: This is a clear signal that AI-assisted vulnerability research is moving from theory to operational capability. Large codebases like Firefox contain millions of lines of legacy code, and traditional manual auditing simply cannot keep pace. AI models that can explore thousands of files, reason about memory safety, and suggest crash conditions dramatically accelerate the discovery phase. However, the experiment also showed a critical limitation: finding vulnerabilities is much easier than weaponizing them. Claude successfully generated a working exploit only twice, even after hundreds of attempts and roughly $4,000 in compute credits. That gap matters. Vulnerability discovery tools could soon become common across both defensive teams and threat actors, but automated exploit generation still requires significant refinement.
READ THE STORY: THN
Anthropic Sues U.S. Government Over “National Security Risk” Designation
Bottom Line Up Front (BLUF): Anthropic CEO Dario Amodei and company have filed a lawsuit against the U.S. government after being labeled a “supply chain risk to national security” by the Department of Defense—an unprecedented designation for a U.S.-based company. The decision effectively blocks Anthropic from future military contracts and stems from the company’s refusal to allow its AI models to be used for fully autonomous weapons or mass domestic surveillance.
Analyst Comments: Their refusal to remove safety guardrails suggests the company wants to maintain strict limits on weaponization and domestic surveillance use cases. From the government’s perspective, those constraints may be seen as limiting operational flexibility in defense programs. The “supply chain risk” designation is significant because it’s typically applied to foreign vendors suspected of espionage or influence operations, not domestic companies. If upheld, the precedent could give the U.S. government a powerful tool to pressure technology firms into compliance with defense requirements.
READ THE STORY: The Register
Chinese-Linked Hackers Breach FBI Systems Holding Surveillance Metadata
Bottom Line Up Front (BLUF): Investigators suspect a China-linked threat actor—potentially the Salt Typhoon group—breached an FBI internal system containing metadata tied to U.S. surveillance orders. The compromised environment reportedly held call logs, IP addresses, and routing data linked to individuals under investigation. While the system did not store communication content, the exposure of surveillance metadata could reveal investigative targets and intelligence methods.
Analyst Comments: Access to surveillance metadata is a goldmine for counterintelligence. Even without message content, call records, IP logs, and routing data can map investigative priorities, identify confidential informants, or expose which foreign actors are under U.S. scrutiny. If a Chinese-linked group obtained sustained access, Beijing could use the data to warn assets, adjust espionage operations, or identify intelligence collection gaps.
READ THE STORY: MEZHA
Anduril Founder Palmer Luckey Seeks $1B for Retro Console Startup
Bottom Line Up Front (BLUF): Palmer Luckey, founder of defense tech giant Anduril, is reportedly seeking funding for a new gaming venture—ModRetro—at a $1 billion valuation. The company aims to revive classic 1990s gaming hardware, starting with modernized versions of devices inspired by the Game Boy and Nintendo 64. The move reflects growing investor appetite for nostalgia-driven hardware and Luckey’s continued push to blend modern engineering with legacy platforms.
Analyst Comments: At first glance, a defense-tech billionaire building retro consoles sounds like a side hobby—but Luckey has a history of turning niche enthusiast projects into billion-dollar companies. Oculus started as a passion project for VR hobbyists before selling to Facebook for $2B. ModRetro appears to follow a similar pattern: start with hardware enthusiasts and retro gaming communities, then scale into a broader consumer market. The timing also matters. Retro gaming has quietly become a significant commercial niche. Collectors, emulation communities, and nostalgia-driven consumers are fueling demand for premium re-creations of classic hardware. If Luckey positions ModRetro devices as high-quality, hardware-accurate systems rather than cheap emulators, the company could dominate a category currently served by fragmented boutique manufacturers.
READ THE STORY: FT
Malicious Chrome Extension Impersonates imToken Wallet to Steal Crypto Seed Phrases
Bottom Line Up Front (BLUF): Researchers have uncovered a malicious Chrome extension masquerading as a developer tool that secretly impersonates the imToken cryptocurrency wallet to steal users’ private keys and seed phrases. The add-on redirects victims to a convincing phishing site that collects wallet recovery secrets, giving attackers immediate control of affected crypto funds.
Analyst Comments: Technically, the extension is designed to evade detection by keeping malicious logic off-device. Instead of directly stealing data, it acts as a redirector controlled via a remote configuration endpoint, allowing operators to change phishing infrastructure without updating the extension itself. This technique complicates automated scanning by browser stores and security tools. The use of Unicode homoglyphs—mixing visually identical Latin, Cyrillic, and Greek characters—adds another layer of deception. These tricks help bypass simple URL filters and trick users into trusting phishing pages that visually match legitimate domains.
READ THE STORY: GBhackers
China-Linked Hackers Use Malware Trio for Telecom Espionage
Bottom Line Up Front (BLUF): Cisco Talos researchers report that a China-linked espionage group, tracked as UAT-9244, has been targeting South American telecommunications providers since 2024 using three newly identified malware tools. The toolkit—TernDoor, PeerTime, and BruteEntry—is designed to maintain persistent access to telecom infrastructure, harvest credentials, and expand intrusions across networks. Researchers say the activity overlaps with known Chinese APT groups Famous Sparrow and Tropic Trooper, both long associated with strategic intelligence collection campaigns.
Analyst Comments: The tooling here shows a mature intrusion model. TernDoor handles Windows persistence and command execution, PeerTime extends reach into Linux-based infrastructure and embedded telecom systems, and BruteEntry converts compromised devices into distributed scanning nodes. That last piece is particularly interesting—it turns victim infrastructure into an operational relay network capable of discovering and compromising additional targets.
READ THE STORY: BankInfoSec
Iran-Linked MuddyWater Deploys Dindoor Malware Against U.S. Organizations
Bottom Line Up Front (BLUF): Security researchers report that Iran-linked APT group MuddyWater (Seedworm) launched a campaign in February 2026 targeting U.S. organizations, deploying a newly identified Dindoor backdoor across sectors including banking, aviation, nonprofits, and defense-related suppliers. The malware leverages the Deno runtime to execute JavaScript and TypeScript payloads, while additional tooling such as Fakeset and Rclone suggests both espionage and potential data exfiltration operations.
Analyst Comments: MuddyWater has long been one of Iran’s most consistent cyber operators, typically focusing on credential theft, espionage, and strategic network access rather than highly sophisticated zero-day exploitation. What stands out here is the use of the Deno runtime, which is still relatively uncommon in malware. That choice allows operators to run JavaScript or TypeScript payloads in a controlled environment, potentially simplifying cross-platform operations and evading some traditional detection patterns tuned for PowerShell or compiled binaries.
READ THE STORY: Security Affairs // THN
Son of U.S. Contractor Arrested for Allegedly Stealing $46M in Cryptocurrency
Bottom Line Up Front (BLUF): Authorities arrested John Daghita, the son of a U.S. government contractor executive, in Saint Martin for allegedly stealing over $46 million in cryptocurrency tied to the U.S. Marshals Service. Investigators say the funds were linked to government-managed seized assets, including cryptocurrency from the 2016 Bitfinex hack, and that blockchain tracing helped identify wallets connected to Daghita’s online alias “Lick.”
Analyst Comments: This case highlights a persistent but often overlooked risk in digital asset management: insider access to government-controlled cryptocurrency wallets. Agencies such as the U.S. Marshals Service increasingly handle seized digital assets from cybercrime investigations, ransomware cases, and darknet markets. That creates a unique attack surface where individuals with operational proximity—even indirectly through contractors—can potentially exploit privileged knowledge or infrastructure.
READ THE STORY: SCMEDIA
U.S. Imposes Visa Restrictions on Rwandan Officials Over Congo Conflict
Bottom Line Up Front (BLUF): The United States has imposed visa restrictions on several senior Rwandan officials accused of supporting the M23 rebel group in eastern Democratic Republic of Congo (DRC). The move escalates U.S. pressure on Rwanda following earlier sanctions against Rwandan military officials, amid continued violence despite a U.S.-brokered peace agreement signed in December.
Analyst Comments: Washington’s decision signals increasing frustration with Rwanda’s alleged backing of M23, which the U.S., Congo, and U.N. investigators say has fueled instability in eastern DRC. The sanctions and visa bans appear designed to raise diplomatic costs for Kigali while avoiding direct economic measures against the broader Rwandan state. The conflict is strategically important beyond regional security. Eastern Congo holds vast reserves of critical minerals, including cobalt, coltan, and rare earth materials essential for electronics, batteries, and defense technologies. Control of territory in this region often translates into control over mineral supply chains, which explains why external powers—including the U.S., China, and regional actors—closely monitor the conflict.
READ THE STORY: ABC News
Items of interest
AI Labs Enter Cybersecurity Arena: OpenAI and Anthropic Launch Offensive Security Platforms
Bottom Line Up Front (BLUF): Between February and March 2026, major AI labs Anthropic and OpenAI simultaneously launched security-focused platforms capable of discovering software vulnerabilities at scale. Anthropic’s Claude Opus 4.6 reportedly identified more than 500 previously unknown high-severity vulnerabilities, while OpenAI released Codex Security, an AI system designed to autonomously analyze code, verify exploits in sandbox environments, and generate patches. The developments signal a shift toward AI-driven vulnerability discovery and automated security research, potentially reshaping the cybersecurity industry.
Analyst Comments: The security industry may be entering what researchers call “Fuzzing 2.0.” Traditional vulnerability discovery relies on techniques such as static analysis, fuzzing, or manual auditing. These methods largely depend on pattern matching or code coverage metrics. AI models, however, can reason about program logic, data flow, and algorithm behavior, allowing them to identify vulnerabilities that conventional fuzzers miss—even in codebases with high coverage.
READ THE STORY: Freebuf
FUZZING’24 Keynote: “Is ‘AI’ useful for fuzzing?” (Video)
FROM THE MEDIA: Discussion of AI and its applications to security seems unavoidable nowadays, and, alas, this keynote is no exception.
Fuzzing in the GenAI Era — Leonard Tang, Haize Labs (Video)
FROM THE MEDIA: Evaluation" is one of those concepts that every AI practitioner vaguely knows is important, but few practitioners truly understand. Is "eval" the dataset for measuring the quality of your AI system? Is "eval" the measure, the metric of quality? Is "eval" the process of human annotation and scoring? Or is "eval" a third-party dataset run once to benchmark a model?
The selected stories cover a broad range of cyber threats and are intended to help readers frame key publicly discussed threats and improve overall situational awareness. InfoDom Securities does not endorse any third-party claims made in its original material or related links on its sites; the opinions expressed by third parties are theirs alone. For further questions, don't hesitate to get in touch with InfoDom Securities at dominanceinformation@gmail.com.