Daily Drop (1242)
02-08-26
Sunday, Feb 08, 2025 // (IG): BB // GITHUB // SN R&D
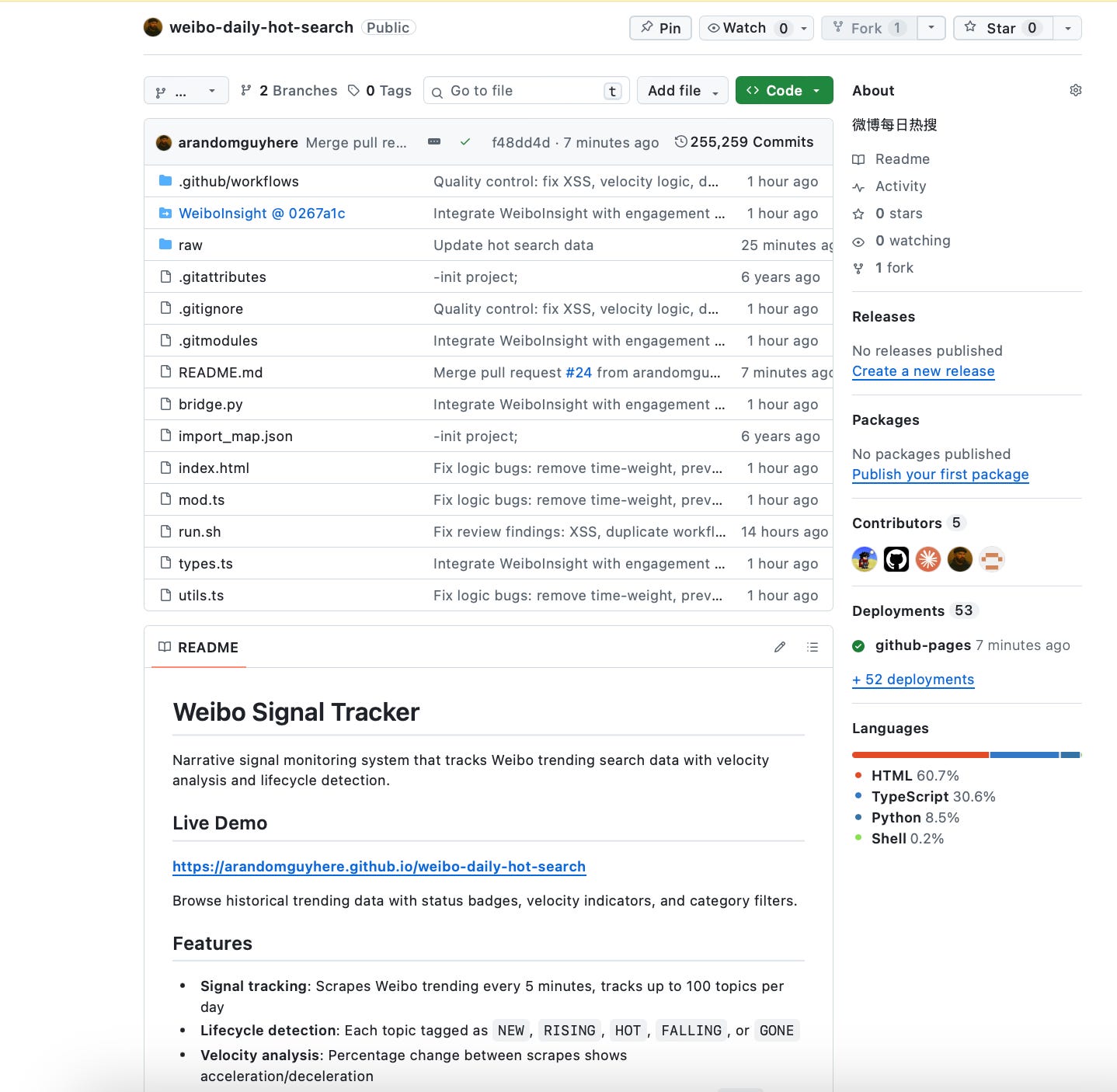
TOOL:
Weibo Signal Tracker
Narrative signal monitoring system that tracks Weibo trending search data with velocity analysis and lifecycle detection.
NEWS:
China Allegedly Develops Anti-Starlink Capabilities as Space Becomes a Contested Domain
Bottom Line Up Front (BLUF): Beijing is attempting to develop capabilities designed to disrupt or neutralize Starlink and similar satellite constellations, signaling serious preparation for conflict in space-enabled warfare. The effort reflects Beijing’s assessment that commercial satellite networks are now integral to military operations—and therefore legitimate targets in future conflicts.
Analyst Comments: Starlink’s role in Ukraine fundamentally changed how militaries view commercial space assets: they are no longer auxiliary—they are operational infrastructure. China’s response is logical from a military-planning perspective: if you can’t match the constellation, you find ways to blind, jam, spoof, or kinetically degrade it. What matters is the method, not the headline. China doesn’t need to “destroy Starlink” outright. Temporary disruption, regional denial, or selective degradation would be sufficient to complicate U.S. and allied operations while staying below the threshold of overt escalation. The broader implication is normalization of space as a contested warfighting domain, where private companies are now embedded actors whether they want to be or not.
READ THE STORY: Orbital Today
Indonesia Aligns with China on AI Regulation to Shape Global Governance Norms
Bottom Line Up Front (BLUF): There’s a strategic messaging layer here. While Western debates focus on runaway AI or labor disruption, China is presenting itself as a responsible manager of technological change. That narrative plays well in developing economies concerned about social stability. The risk for the U.S. and Europe is waking up to a standards environment already shaped by Chinese preferences—especially around surveillance, data sovereignty, and state oversight—before alternatives gain traction.
Analyst Comments: The regulations aim to prevent “total replacement” of human labor while maintaining government oversight of AI systems. The article notes that China views international coordination on AI rules as a way to export its governance model, particularly to developing nations. Indonesia’s participation adds regional legitimacy and could influence broader adoption of similar regulatory frameworks across Southeast Asia.
READ THE STORY: Econews
China’s Military Purge Clouds Signals on Peace, War, and U.S.–China Dialogue
Bottom Line Up Front (BLUF): Military purges are about control before they’re about corruption. When senior officers disappear from public view, it signals internal distrust—and potentially anxiety—at the top. For external observers, the problem isn’t knowing who was removed; it’s not knowing who now has Xi Jinping’s confidence or how insulated leadership is from bad news.
Analyst Comments: China has continued purging senior military officials, including figures linked to the Rocket Force and defense procurement. The removals have fueled speculation about corruption, factionalism, and President Xi Jinping’s tightening grip over the armed forces. The article notes that the timing of the purge coincides with U.S. efforts to stabilize military-to-military communications and reduce the risk of conflict. Analysts quoted by Reuters warn that leadership instability within the PLA could complicate Beijing’s strategic signaling and raise doubts about its ability to manage crises or negotiate from a position of institutional coherence.
READ THE STORY: Reuters
MIIT Issues 2026 Automotive Data Exit Security Guidelines, Tightening Cross-Border Controls
Bottom Line Up Front (BLUF): China’s Ministry of Industry and Information Technology (MIIT), alongside eight other government bodies, has issued the “Guidelines for Exit Security of Automobile Data (2026 Edition)”, significantly tightening rules governing cross-border transfers of automotive data. The guidelines formalize stricter approval thresholds, broaden the definition of “important data,” and reinforce China’s push for data localization and regulatory oversight across connected vehicle and autonomous driving ecosystems.
Analyst Comments: This is regulatory consolidation, not incremental policy. China is clearly signaling that automotive data—especially data tied to autonomy, vehicle networking, software updates, and perception systems—is now treated as strategic infrastructure. The scope goes well beyond personal information, explicitly capturing source code, algorithms, training data, vehicle identifiers, and real-time perception feeds.
READ THE STORY: Freebuf
APT-Q-27 Malware Campaign Signals Persistent, Low-Noise Espionage Activity
Bottom Line Up Front (BLUF): CyStack reports that APT-Q-27 is associated with a malware framework used in targeted espionage campaigns. The malware supports data collection, command-and-control communications, and persistence mechanisms designed to evade traditional security controls. The research highlights indicators of a well-resourced actor, including custom tooling, controlled infrastructure, and operational security practices that limit exposure. Victims appear to be selectively targeted, reinforcing assessments that the campaign is intelligence-driven rather than opportunistic.
Analyst Comments: APT-Q-27 is playing the long game. The tooling and operational tempo point to an actor that prioritizes staying hidden, maintaining footholds, and collecting information incrementally. This isn’t smash-and-grab malware—it’s infrastructure designed to survive rotations, evade commodity detection, and blend into normal network behavior. What stands out is the discipline. Groups like this don’t need novel zero-days to be effective; they rely on careful targeting, selective deployment, and patience. For defenders, these campaigns are harder to spot precisely because they don’t generate obvious spikes in activity. The real risk is silent persistence—months or years of access that only surface after strategic damage is done.
READ THE STORY: CyStack
Ukraine Seeks Polish Support After Russian Strikes Hit Power Grid
Bottom Line Up Front (BLUF): Russia’s repeated targeting of Ukraine’s energy sector reflects a calculation that civilian hardship can still generate leverage, even after years of resilience and repair. While these attacks have failed to produce political collapse, they continue to impose real operational costs—diverting air defense assets, stretching repair crews, and forcing reliance on cross-border support.
Analyst Comments: Ukraine requested assistance from Poland after Russia launched a massive attack on Ukrainian energy infrastructure, causing widespread power outages. Ukrainian officials said the strikes targeted key grid facilities, disrupting electricity supplies across multiple regions. The article notes that Poland has previously provided technical and energy-related support to Ukraine and is seen as a critical partner in maintaining grid stability. The latest attack follows a pattern of Russian missile and drone strikes aimed at weakening Ukraine’s civilian infrastructure, particularly during periods of high energy demand.
READ THE STORY: France24
LocalGPT Enables Offline AI Use, Raising Both Privacy and Abuse Considerations
Bottom Line Up Front (BLUF): The tool emphasizes privacy, data ownership, and offline operation, making it attractive for organizations handling sensitive information. While LocalGPT has legitimate enterprise and research use cases, its lack of centralized oversight raises concerns about misuse. Security experts caution that offline AI tools could be leveraged to generate phishing content, analyze stolen data, or assist in exploit development without detection.
Analyst Comments: LocalGPT, a framework that allows large language models to run entirely on local systems, is gaining attention for enabling offline AI processing without sending data to external cloud services. While this improves data privacy and control, it also lowers barriers for malicious or sensitive use cases that would otherwise be constrained by provider safeguards.
READ THE STORY: CSN
China Hosts More Active Hacking Groups Than Any Other Country
Bottom Line Up Front (BLUF): China is home to more active hacking groups than any other country, according to new analysis, reinforcing its central role in the global cyber threat landscape. The ecosystem spans state-backed operators, contractors, and criminal groups, creating scale, resilience, and plausible deniability for sustained cyber operations.
Analyst Comments: What matters for defenders is volume and diversity. A crowded threat ecosystem means constant experimentation, faster tool evolution, and overlapping campaigns that complicate attribution. Even when individual groups burn infrastructure or tooling, the broader system absorbs the loss. Western responses still tend to focus on naming and shaming specific APTs, but that approach struggles against an environment designed for churn and deniability.
READ THE STORY: CN
PLA-Linked Supply Chain Attack Compromises Popular Open-Source Coding Application
Bottom Line Up Front (BLUF): A China-linked threat actor has targeted a widely used open-source coding application in a suspected supply chain attack, exposing developers and downstream environments to potential compromise. The operation underscores how developer tools remain a force-multiplier target for espionage-focused actors seeking quiet, scalable access.
Analyst Comments: These campaigns aren’t about burning access quickly; they’re about embedding quietly and waiting for downstream opportunities. The uncomfortable reality is that most organizations still treat open-source tooling as implicitly safe, even as it becomes one of the most contested attack surfaces.
READ THE STORY: ET
OpenClaw Integrates VirusTotal, Accelerating Automated Reconnaissance
Bottom Line Up Front (BLUF): The OpenClaw framework has added native VirusTotal integration, allowing users to automate file, hash, and indicator lookups during reconnaissance and targeting. The update improves efficiency for defenders and red teams—but also lowers friction for threat actors validating payloads and infrastructure at scale.
Analyst Comments: VirusTotal integration is a double-edged upgrade. For legitimate users, it speeds triage and enrichment. For attackers, it shortens the feedback loop between development and deployment—making it easier to test whether malware or infrastructure is “burned” before use. This reinforces a broader trend: open frameworks are quietly absorbing capabilities once reserved for bespoke tooling. As these features normalize, the distinction between red-team convenience and attacker enablement continues to blur. Defenders should assume faster iteration cycles on the adversary side and adjust detection strategies accordingly.
READ THE STORY: THN
Microsoft Data Center Power Outage Disrupts Cloud Services
Bottom Line Up Front (BLUF): A power outage at a Microsoft data center caused service disruptions across multiple cloud-dependent platforms, highlighting the fragility of centralized infrastructure even among hyperscale providers. While outages are inevitable, the incident underscores the cascading impact of data center failures on downstream customers.
Analyst Comments: As organizations concentrate workloads in fewer cloud regions, the blast radius of physical or operational failures grows. Redundancy on paper doesn’t always translate to resilience in practice. For defenders and risk managers, this is a reminder that cloud risk isn’t limited to breaches. Power, cooling, and physical infrastructure remain single points of failure if architectures aren’t designed for regional independence. Expect regulators and large enterprises to scrutinize cloud resilience claims more closely as outages continue to hit critical services.
READ THE STORY: CSN
Rome’s La Sapienza University Remains Offline Following Cyberattack
Bottom Line Up Front (BLUF): Italy’s Sapienza University of Rome remains offline as administrators work to contain and remediate a recent cyberattack. The prolonged outage suggests a serious compromise affecting core systems, reinforcing higher education’s continued vulnerability to disruptive cyber incidents.
Analyst Comments: Universities sit at an uncomfortable intersection: open networks, valuable research data, and uneven security budgets. When an institution stays offline for days, it usually means defenders are prioritizing containment over availability—a sign they don’t yet trust the environment. The academic sector remains attractive to both ransomware operators and espionage-focused actors. Research institutions often hold sensitive intellectual property and government-linked projects but lack the segmentation and monitoring found in more regulated sectors. Expect attacks like this to continue unless higher education treats cyber resilience as a mission-critical function rather than an IT problem.
READ THE STORY: Security Affairs
State-Backed Hackers Target Signal Communications of Military Officials
Bottom Line Up Front (BLUF): Nation State-sponsored actors are actively targeting Signal communications belonging to military officials, aiming to access sensitive conversations rather than break the platform’s encryption itself. The activity relies on account compromise and endpoint access, reinforcing that secure messaging apps are only as safe as the devices and users behind them.
Analyst Comments: Targeting military officials’ Signal messages also highlights shifting intelligence priorities. Messaging platforms capture real-time decision-making, informal coordination, and context that never appears in official systems. For state actors, that insight is often more valuable than classified databases. Expect continued pressure on personal devices, social engineering, and cloud-linked backups as long as sensitive discussions live outside hardened environments.
READ THE STORY: CSN
GhostKatz Emerges as Physical-Memory–Based Alternative to Mimikatz
Bottom Line Up Front (BLUF): A new Windows credential extraction tool called GhostKatz has been publicly released, taking a fundamentally different approach from Mimikatz by extracting LSASS credentials directly from physical memory via vulnerable but legitimately signed kernel drivers. The technique bypasses many user-mode detection controls, highlighting persistent blind spots in modern Windows credential protection.
Analyst Comments: GhostKatz is not a Mimikatz replacement—it’s a divergence. As Microsoft has steadily hardened LSASS against user-mode dumping and debugging, attackers and researchers are shifting attention downward, toward the kernel and driver layer. GhostKatz reflects that shift clearly: instead of fighting endpoint controls head-on, it sidesteps them.
READ THE STORY: Freebuf
“Nmap Unleashed” Tool Lowers Barrier for Large-Scale Network Reconnaissance
Bottom Line Up Front (BLUF): A newly released tool dubbed “Nmap Unleashed” streamlines and automates advanced Nmap scanning, making large-scale network reconnaissance more accessible to low-skill actors. While framed as a productivity aid, the tool reduces friction for attackers conducting target discovery and pre-exploitation mapping.
Analyst Comments: Recon is where most intrusions begin, and automation is the force multiplier. Tools like this don’t introduce new techniques—they remove effort and judgment. That matters because it compresses the timeline from curiosity to action, especially for opportunistic attackers and initial access brokers. For defenders, the risk isn’t novelty but volume. When scanning becomes easier, noisier campaigns follow, often probing forgotten assets and edge services. Organizations that still lack external attack surface management or baseline scan detection should expect to feel this first. “It’s just scanning” stops being benign when it’s continuous and optimized.
READ THE STORY: CSN
OpenAI Launches “Trusted Access” Program for Cybersecurity Use Cases
Bottom Line Up Front (BLUF): As AI becomes embedded in vulnerability research, threat analysis, and defensive automation, providers are being forced to balance utility against misuse. Trusted Access appears designed to keep advanced features in the hands of known entities while preserving auditability and policy enforcement. The bigger signal is normalization. AI is no longer treated as a general productivity tool—it’s being formally integrated into security workflows with guardrails. That’s positive for defenders, but it also underscores a widening gap between organizations that can access regulated AI capabilities and those left with commodity models. Expect adversaries to respond by leaning harder on local or open-source alternatives where oversight is minimal.
Analyst Comments: OpenAI has introduced a Trusted Access initiative aimed at enabling vetted cybersecurity organizations to use advanced AI capabilities under enhanced security controls. The move reflects growing recognition that high-end AI models are dual-use assets that require tighter governance when applied to sensitive security operations.
READ THE STORY: Cyber Press
BridgePay Ransomware Attack Disrupts Payment Processing Services
Bottom Line Up Front (BLUF): Payment processor BridgePay has suffered a ransomware attack that disrupted transaction processing and impacted downstream merchants. The incident highlights the outsized risk posed by attacks on financial intermediaries, where a single compromise can cascade across multiple businesses and sectors.
Analyst Comments: Ransomware targeting payment processors isn’t about data theft alone—it’s about leverage. When attackers hit the transaction layer, they create immediate operational pain that forces rapid decision-making. Even short outages can translate into lost revenue, reputational damage, and regulatory scrutiny. The broader concern is systemic exposure. Many merchants rely on third-party processors with limited visibility into their security posture. This incident reinforces the need for contingency planning, vendor risk management, and the assumption that upstream providers will eventually fail. Expect ransomware groups to continue probing financial infrastructure where downtime equals pressure.
READ THE STORY: CSN
Infostealer Threats Expand Beyond Windows, Increasingly Target macOS Systems
Bottom Line Up Front (BLUF): MacOS is emerging as a priority target for infostealer operators as attackers shift focus toward environments rich in developer credentials, executive access, and cloud tokens. The long-standing assumption that Apple platforms present lower risk is now actively working against defenders.
Analyst Comments: This shift is about return on investment. macOS users often hold privileged access, cloud credentials, and sensitive data, making successful theft more valuable even if development costs are higher. Attackers are pragmatic: they go where access is richest, not where exploitation is easiest. Defensive complacency is the real enabler. Many organizations still under-protect macOS fleets, with weaker EDR coverage, looser application controls, and lower user vigilance than on Windows. Infostealers don’t need advanced exploits—they rely on social engineering, trojanized software, and permission abuse. As macOS tooling matures, expect this activity to scale.
READ THE STORY: SCMEDIA
Items of interest
Unplugging Beijing: Strategic Push to Reduce Dependence on Chinese Technology and Infrastructure
Bottom Line Up Front (BLUF): Democracies are moving—slowly but decisively—to reduce their exposure to Chinese technology in critical infrastructure, telecom, cloud, and hardware supply chains. “Unplugging Beijing” in practice means diversifying vendors, restricting PRC-linked tech from sensitive networks, and tightening export controls on advanced chips and manufacturing equipment. The transition will be messy and expensive, but the alternative is long-term strategic dependence on an authoritarian rival with a track record of cyber espionage, IP theft, and coercive economic behavior.
Analyst Comments: PRC-linked vendors in 5G, cloud, and backbone equipment can be leveraged for intelligence collection, disruption, or pressure in a crisis. “Unplugging” doesn’t mean instant decoupling; it’s more like a phased emergency migration off a vendor you no longer trust. Expect more supply-chain screening, more bans on specific products (especially in government and critical infrastructure), and quieter but aggressive moves to replace Chinese equipment in telecom cores, data centers, and industrial control environments. Organizations that wait for formal mandates will be doing rushed, expensive rip-and-replace later under worse conditions.
READ THE STORY: FDD
A Full US-China Decoupling Devastate China’s Economy, Weak Domestic Demand Leaves Businesses Bleak (Video)
FROM THE MEDIA: Due to the ongoing economic downturn, major e-commerce platforms are now offering significant subsidies as sellers lower prices in a hurry.
How Export Controls Are Reshaping the Global Chip Industry: US-China Semiconductor Policies (Video)
FROM THE MEDIA: U.S.-led export controls are transforming the global semiconductor landscape — and what it means for chipmakers, investors, and the tech economy. Building on our previous videos “The Great Silicon Divide” and “Rare Earths: China’s Hidden Leverage,” this episode focuses on the latest policy shocks and the growing divide between U.S.-aligned and China-aligned tech ecosystems.
The selected stories cover a broad range of cyber threats and are intended to help readers frame key publicly discussed threats and improve overall situational awareness. InfoDom Securities does not endorse any third-party claims made in its original material or related links on its sites; the opinions expressed by third parties are theirs alone. For further questions, don't hesitate to get in touch with InfoDom Securities at dominanceinformation@gmail.com.