Daily Drop (1230)
01-21-26
Wednesday, Jan 21, 2025 // (IG): BB // GITHUB // SN R&D
Londoners Raise Alarm Over China’s 'Super Embassy' and Its Proximity to Key Communications Infrastructure
Bottom Line Up Front (BLUF): Local residents and city officials are voicing national security concerns over China’s proposed “super embassy” in East London, which sits near critical underground communication cables. The £750 million development has been under scrutiny since its proposal, but new objections focus on its potential intelligence collection capabilities due to its location near sensitive telecom routes.
Analyst Comments: Embassies have long been hubs for intelligence collection, and placing one of this scale near major fiber lines makes for an easy SIGINT (signals intelligence) concern. British intelligence agencies are likely less worried about overt surveillance and more about passive collection—think buried antennas, windowless rooms, and diplomatic pouches full of hardware. This reflects a broader trend: urban infrastructure is now a soft target. China denies espionage, of course, but the UK has already blocked the embassy plan once, citing security risks. Expect further pushback and increased scrutiny of diplomatic construction near critical nodes—especially in Five Eyes countries.
READ THE STORY: Metro
Ukraine’s New Defense Minister Faces Battlefield-First Mandate Amid Escalating War Demands
Bottom Line Up Front (BLUF): Rustem Umerov, Ukraine’s newly appointed Defense Minister, has inherited a war that’s both militarily and politically complex. In a recent United24 Media interview, Umerov emphasized a “battlefield-first” approach, distancing his leadership style from bureaucratic tradition. His immediate challenges include shoring up ammunition supplies, accelerating defense procurement, and restoring confidence among frontline units after months of attritional warfare.
Analyst Comments: Umerov stressed that decisions must be driven by the needs of soldiers on the front, not bureaucrats in Kyiv. He highlighted ammunition shortages, broken procurement pipelines, and delayed delivery of Western aid as critical bottlenecks. Umerov also hinted at ongoing efforts to digitize logistics and introduce accountability reforms. His background in business and negotiation is seen as an asset in coordinating international support and managing Ukraine’s expanding defense industry.
READ THE STORY: United24
EU Moves to Phase Out Huawei
Bottom Line Up Front (BLUF): The European Union has announced a formal timeline to remove so-called “high-risk vendors”—primarily Huawei and ZTE—from 5G and other critical infrastructure by 2027. While several member states have already restricted Chinese telecom equipment, this marks the first EU-wide policy push to standardize and accelerate the phase-out.
Analyst Comments: The move signals that Brussels is taking a more centralized stance on supply chain security after years of fragmented national policies. For Huawei and similar vendors, the writing is now officially on the wall in Europe. But the longer tail of this story lies in implementation—some countries still rely heavily on Chinese infrastructure and lack immediate alternatives. Expect lobbying, legal challenges, and pressure on domestic telecoms to fast-track vendor diversification. For defenders, this is a win, but it’s also a reminder: banning tech isn’t the same as securing the stack. Software supply chains, update mechanisms, and insider threats still demand attention.
READ THE STORY: Reuters
Cobalt Launches Two-Way Pentesting Tool for Microsoft Teams
Bottom Line Up Front (BLUF): Cobalt has released a new penetration testing module specifically targeting Microsoft Teams environments, enabling red teamers to simulate real-world collaboration app abuse—both inbound and outbound. The tool is designed to help organizations uncover lateral movement and phishing risks within Teams, a platform increasingly used for internal comms across enterprises.
Analyst Comments: Teams is becoming the new Outlook for attackers—and defenders haven’t caught up. This tool from Cobalt acknowledges that reality. Lateral movement via Teams, malicious file sharing, and spoofed messages are real-world attack paths we’ve seen exploited by APTs and ransomware groups alike. The "two-way" simulation aspect is especially useful: red teams can now test both attacker entry via Teams and internal propagation after compromise. Expect defenders to start integrating Teams-specific detections into SIEM rulesets and tightening policies on external tenant interactions. This is overdue.
READ THE STORY: Security Brief (AU)
DARPA Backs AI-Driven Soaring Tech to Boost Drone Endurance
Bottom Line Up Front (BLUF): DARPA has selected Shearwater Aerospace to deliver AI-powered micro-weather forecasting and mission planning tools under its Albatross program. The goal: enable drones to harness wind currents for extended flight without added hardware. If successful, the approach could redefine endurance limits for existing UAVs through pure software upgrades.
Analyst Comments: Under the Albatross program, Shearwater Aerospace will contribute software that allows drones to forecast and exploit local wind conditions in real time. The system, Smart Flight, uses AI for atmospheric sensing, pathfinding, and in-flight adjustment without the need for new sensors or airframe modifications. Prime contractor PhysicsAI, alongside Applied Aeronautics, will lead flight trials over the next several months. DARPA’s broader unmanned initiative includes VTOL autonomy (via Sikorsky’s MATRIX) and resilient mission execution even under comms loss—part of an ongoing shift toward greater operational independence for drones.
READ THE STORY: The Defense Post
ICE Targeted in Hack-and-Leak Campaign Amid Rising Protests
Bottom Line Up Front (BLUF): Hacktivists leaked sensitive data tied to U.S. Immigration and Customs Enforcement (ICE) as part of a broader protest campaign sparked by recent immigration enforcement actions and growing tensions surrounding ICE operations. The leak includes internal emails, operational details, and personnel data—raising both security and privacy concerns for federal employees.
Analyst Comments: Hacktivism campaigns are evolving from symbolic defacements to coordinated, high-impact data breaches with real-world consequences. Targeting ICE makes strategic sense for actors looking to inflame public sentiment and trigger policy pushback. What’s notable here is the blending of physical protests with digital operations—a hallmark of modern hybrid activism. For defenders, this underscores the need for better insider threat monitoring, email hygiene, and segmentation between operational systems and personnel databases. Expect downstream threats including doxxing, phishing targeting ICE agents, and copycat attacks on other federal entities.
READ THE STORY: AXIOS
ISKP Breached the Red Line: Suicide Bombing in Iran Highlights Intelligence Failures
Bottom Line Up Front (BLUF): The Islamic State Khorasan Province (ISKP) has claimed responsibility for the January 3rd twin suicide bombing in Kerman, Iran, which killed over 90 people during a memorial for Qassem Soleimani. A detailed post-attack investigation confirms ISKP operatives entered Iran via Pakistan, bypassing multiple layers of Iranian security. This marks the most significant breach of Iran’s internal counterterrorism defenses in over a decade.
Analyst Comments: ISKP successfully executed a complex operation deep inside Iranian territory, during a politically sensitive event, with zero prior detection. The fact that attackers crossed from Pakistan and coordinated on Iranian soil suggests gaps in both border surveillance and internal counterterrorism monitoring. For ISKP, it’s a strategic win: they hit a symbolic target while undermining Tehran’s claim to regional control and domestic stability. Expect retaliatory pressure on Pakistan, increased IRGC activity in border provinces, and a likely crackdown on Afghan refugee populations inside Iran—right or wrong, they’ll be a political scapegoat.
READ THE STORY: ISKP
The Quantum Cryptography Cliff: Disconnect Grows Between Research Roadmaps and Real-World Readiness
Bottom Line Up Front (BLUF): Despite a decade of promising roadmaps, large-scale deployment of quantum-safe cryptography is falling behind the pace of quantum computing advances. While governments and academia push post-quantum algorithm standardization, the private sector is lagging in actual implementation—leaving critical infrastructure exposed as the so-called "Q-Day" approaches.
Analyst Comments: Most organizations still haven’t taken inventory of where quantum-vulnerable encryption lives in their environment—let alone started migrating to post-quantum algorithms. The disconnect isn’t just technical; it's strategic. Many CISOs still treat quantum threats as tomorrow’s problem, even as data harvested today could be decrypted later (the “harvest now, decrypt later” threat model). Meanwhile, adversarial states are preparing. The hard truth: the gap between research hype and operational readiness could leave supply chains, government systems, and communications open to retrospective compromise. Post-quantum transition needs to move from academic whitepapers into funded implementation roadmaps—now.
READ THE STORY: SCMEDIA
Hackers Hijack Iran State TV Broadcast in Support of Exiled Prince
Bottom Line Up Front (BLUF): Despite a decade of promising roadmaps, large-scale deployment of quantum-safe cryptography is falling behind the pace of quantum computing advances. While governments and academia push post-quantum algorithm standardization, the private sector is lagging in actual implementation—leaving critical infrastructure exposed as the so-called “Q-Day” approaches.
Analyst Comments: State-controlled media in Iran is a tightly monitored information vector—any successful intrusion is a direct challenge to regime legitimacy. The incident reflects a growing trend of digital resistance targeting high-visibility infrastructure for maximum psychological and political impact. Attribution remains unclear, but past intrusions of this nature have been linked to hacktivist groups like “Edalat-e Ali” or affiliates sympathetic to monarchist or secular opposition movements. Tehran will likely respond with intensified monitoring and arrests tied to suspected cyber dissent. Expect more of these low-impact, high-visibility ops as opposition groups look to exploit the regime’s information choke points.
READ THE STORY: The Canberra Times
Items of interest
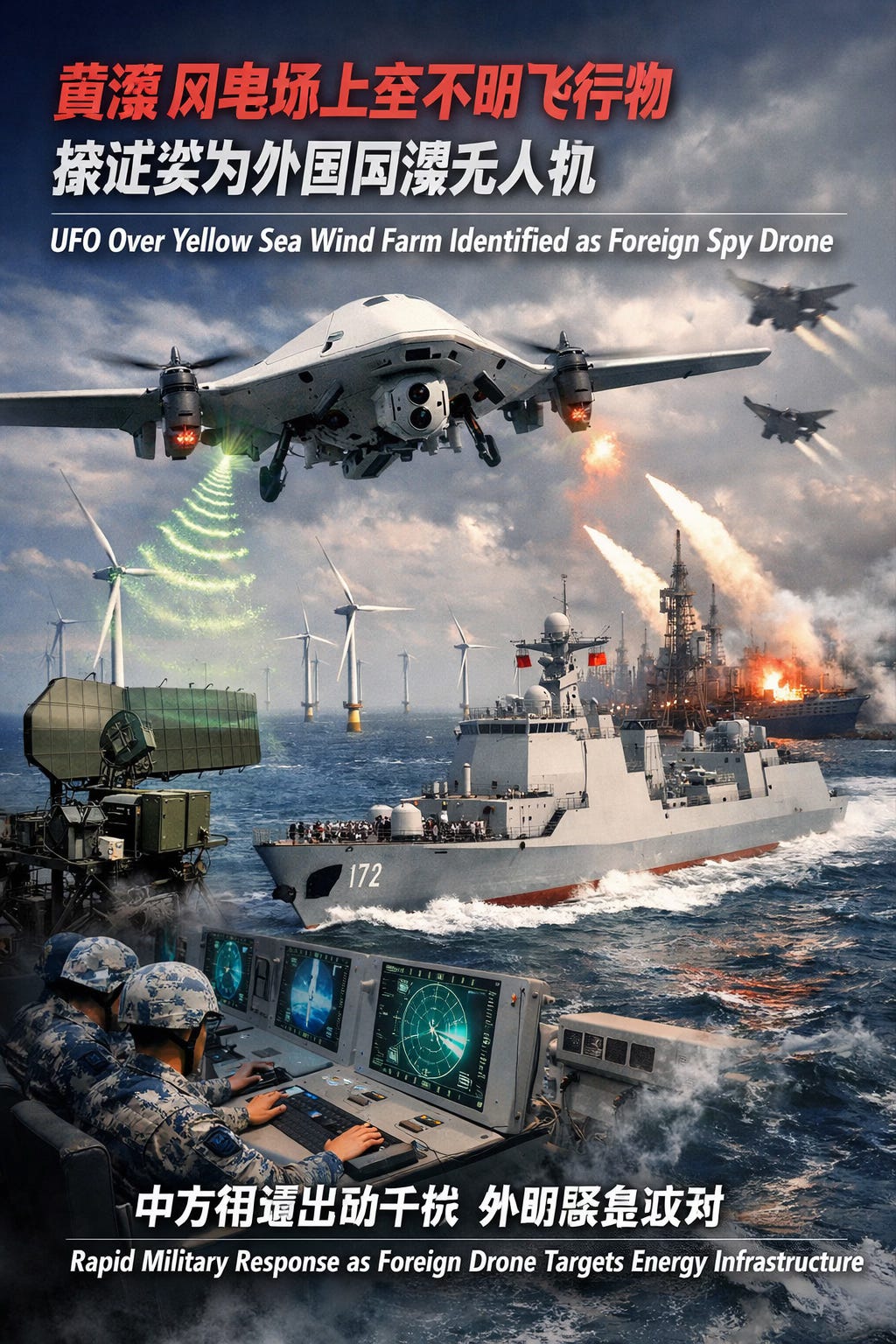
Unidentified Aerial Object Over Chinese Wind Farm Was a Foreign Surveillance Drone
Bottom Line Up Front (BLUF): Chinese state media reports that an unidentified flying object (UFO) spotted over a strategic offshore wind farm in the Yellow Sea has been identified as a foreign surveillance drone. The incident triggered a rapid military response, including radar jamming and naval deployment, with authorities framing it as an act of foreign espionage targeting critical energy infrastructure.
Analyst Comments: This incident fits an emerging pattern: China’s increased sensitivity to perceived surveillance near dual-use infrastructure. Offshore wind farms are not just energy assets—they’re potential platforms for undersea cable routing, radar coverage, and maritime surveillance. Whether the drone belonged to a nation-state remains unconfirmed, but the public framing suggests Beijing is using these events to justify expanded counter-surveillance measures and tighten airspace restrictions. Expect a growing overlap between green energy infrastructure and national defense in both Chinese and Western threat models.
READ THE STORY: CYBERNEWS
Ancient Aliens: China’s Extraterrestrial Legends (Video)
FROM THE MEDIA: "Ancient Aliens" explores the controversial theory that extraterrestrials have visited Earth for millions of years.
UFOs: What Does China Know (Video)
FROM THE MEDIA: Samuel Chong — a lawyer, professional translator, and passionate UFO/UAP researcher originally from China and now based in the United States. Samuel has worked on bringing groundbreaking UFO and extraterrestrial contact books into English, helping to make key information available to a wider global audience.
The selected stories cover a broad range of cyber threats and are intended to help readers frame key publicly discussed threats and improve overall situational awareness. InfoDom Securities does not endorse any third-party claims made in its original material or related links on its sites; the opinions expressed by third parties are theirs alone. For further questions, don't hesitate to get in touch with InfoDom Securities at dominanceinformation@gmail.com.